Jack
1.1K posts







🚨ALERT: Potential ZERO-DAY, Attackers Use Corrupted Files to Evade Detection 🧵 (1/3) ⚠️ The ongoing attack evades #antivirus software, prevents uploads to sandboxes, and bypasses Outlook's spam filters, allowing the malicious emails to reach your inbox The #ANYRUN team discovered that as part of this #zeroday attack, threat actors attempt to conceal the file type by deliberately corrupting it, making it difficult for certain security tools to detect 📌 Our sandbox solves this problem thanks to interactivity. It launches these broken files in their corresponding programs, which allows it to identify #malicious behavior See example: app.any.run/tasks/6839e806… 🚫 Although these files operate successfully within the OS, they remain undetected by most security solutions due to the failure to apply proper procedures for their file types They were uploaded to VirusTotal, but all antivirus solutions returned "clean" or “Item Not Found” as they couldn't analyze the file properly
i’m legit amped about aligning with all of the “tip of the spear” teams under the CISO this part of the public “secure futures” update is a pretty nice acknowledgment of threat intel impact let’s go! come join us: aka.ms/msticjobs 🕵️ aka.ms/ghostjobs 👻

🚨We’re seeing reports of a large-scale #spearphishing campaign targeting multiple sectors, including government and IT. A foreign threat actor is sending phishing emails with malicious RDP files to gain network access. Take proactive measures. More info: bit.ly/4fp9aQB

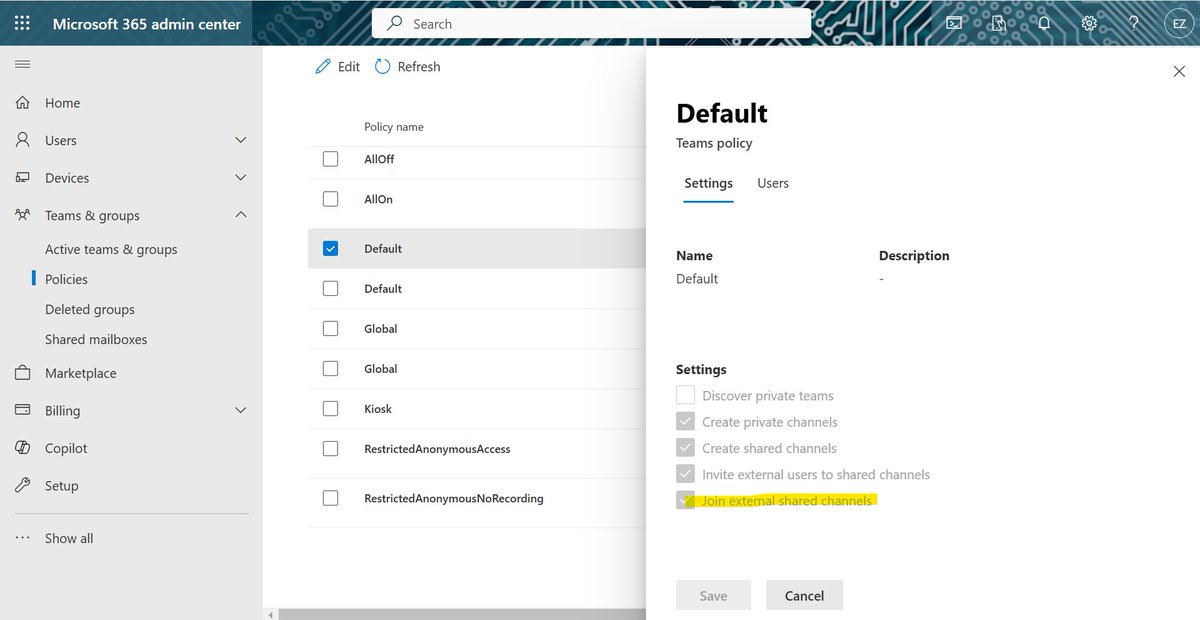
I'm not 100% sure if this will help thwart the current initial access attacks through Teams, but here are some things I would do: 1. Go admin.teams.microsoft.com/company-wide-s… and ensure the following box is unchecked: learn.microsoft.com/en-us/microsof…