Deepak Maram
122 posts

Deepak Maram
@mskd96
Researcher @mysten_labs | CS PhD @cornell_tech @cornell | Ex- @oracle, @cloudflare, @offchainlabs, @chainlinklabs | Bachelor's @iitbombay.









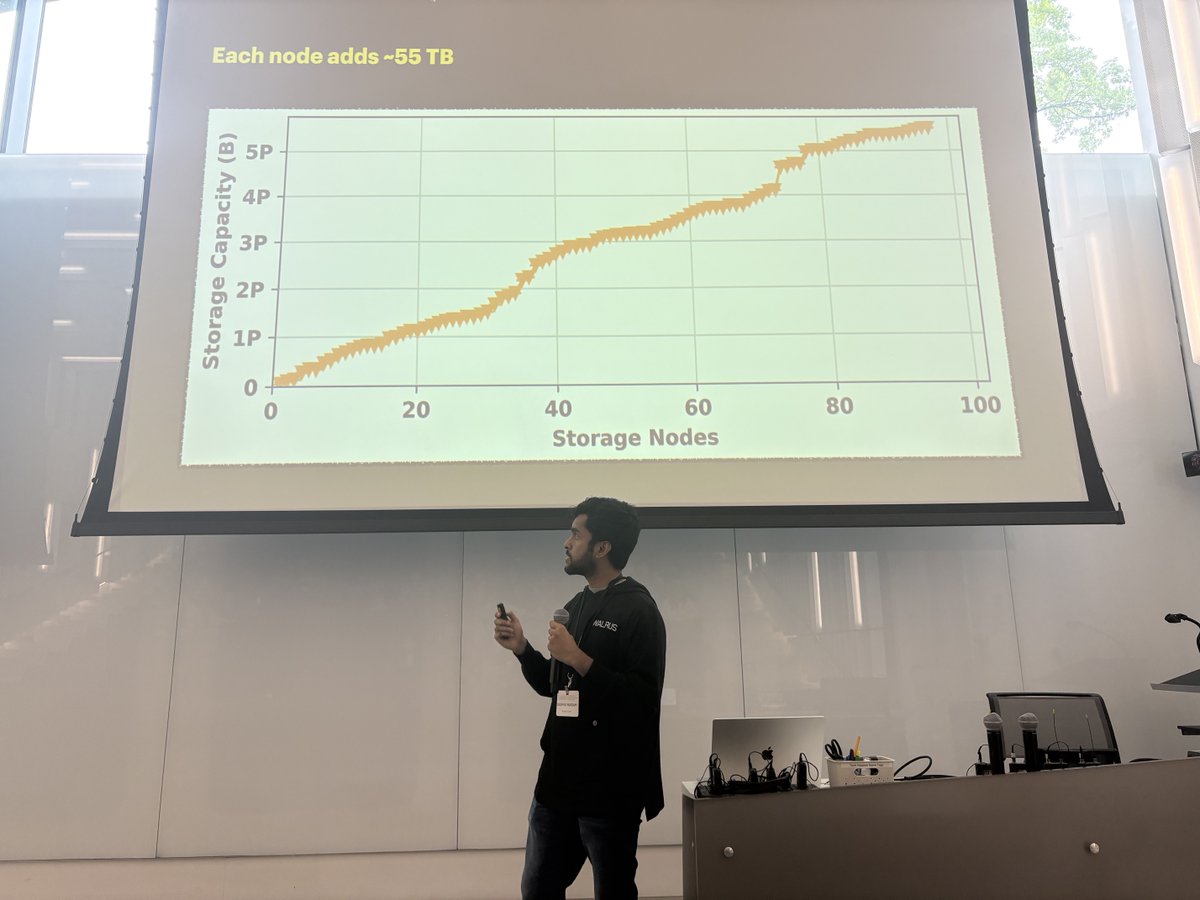

Privacy. Storage. Identity. Sui’s Suite, Unpacked The latest SNARK CHOCOLATE is out! 🍫 We sat down with Deepak Maram (@mskd96) from @Mysten_Labs to dive into @SuiNetwork's cryptography-driven roadmap and products: 🔹 ZKLogin, a privacy-preserving login system using OpenID and ZKPs, now powering millions of transactions 🔹 How Sui integrates ZK features at the protocol level for UX, scalability, and performance 🔹 Walrus (@WalrusProtocol) and Seal, new infrastructure for decentralized storage and programmable secret management 🔹 ZK light clients & scalable off-chain state verification 🔹 How Sui’s research team brings applied cryptography to real-world products 🎧 Listen now: 🔽 Spotify (next post) ⏬ Apple Podcasts (following post)



1 Million Verifications on Reclaim Protocol! To every client who trusted us, every investor who backed us, and every believer who cheered us on - thank you.






NEW IC3 research examines interactive authentication mechanisms that could enhance wallet security, helping crypto users transact more safely.