
s Liberty
13.7K posts


s Liberty
@psyforfreedom
소설가입니다 주로 엑스에 망상기반의. 소설을 씁니다 아 비트코인을 아시나요? 저는 몰라요 ⚡️⚡️⚡️

How bad is the damage to Middle Eastern energy facilities? Experts put a price tag and timeline on it. www3.nhk.or.jp/nhkworld/en/ne…

South Korea's war emergency budget contained Chinese tourist perks. When confronted, Lee responded: "I don't know the details well." At a bipartisan lunch at the presidential office on April 7, People Power Party representative Chang Dong-hyeok raised an inconvenient item buried in the Lee administration's 26 trillion won supplementary budget. Inside South Korea's 26 trillion won emergency war budget: 30.6 billion won for Chinese tourist hospitality, including 500 million won for a luggage-carry service directed specifically at Chinese visitors. Chang asked the obvious question. "Why is Chinese tourist infrastructure in a war-response emergency bill?" President Lee's answer was notable for what it admitted. "I don't know the details well." He then suggested the funds were probably for general tourism promotion, adding: "Surely it wouldn't only be for Chinese people." When Chang pushed back, Lee said: "If it's limited only to Chinese people, cut it. Jeong Cheong-rae of the Democratic Party of Korea, seated beside Lee, interjected that the spending was directed at "Chinese-speaking regions". Lee then questioned whether Chang's characterization was accurate in the first place, suggesting the matter needed to be fact-checked. The Culture, Sports and Tourism Committee subsequently cut approximately 2.5 billion won in related budget items. The cut itself is the tell. If the spending had been genuinely mischaracterized, there would be nothing to remove. A president who doesn't know what's in his own emergency budget, or who does and chose not to defend it, raises the same question either way. What else is in the 26 trillion won bill that no one is asking about yet. Source: biz.chosun.com/en/en-policy/2…
JUST IN: The IRGC Navy just added a second lock to the gate. Hours after the ceasefire was supposed to reopen Hormuz, the IRGC issued an official directive requiring all commercial vessels to use two alternative corridors near Larak Island to avoid sea mines deployed during the war. Inbound traffic north of Larak. Outbound traffic south of Larak. All ships must coordinate with the IRGC Navy before entering. Until further notice. The mines are real. Iran laid them during the February to April campaign as a defensive measure against the US Fifth Fleet. They are in the standard shipping lanes. The alternative routes bypass the minefields but funnel every vessel through a narrow channel inside Iranian territorial waters, past the same Larak Island where the IRGC toll booth already operates and the patrol boats already escort ships one at a time after verifying clearance codes paid for in yuan or cryptocurrency. This is not a safety measure. It is infrastructure. The mines create the problem. The alternative routes create the solution. The solution requires coordination with the IRGC. The coordination requires toll payment. The toll requires yuan. Each layer reinforces the previous one until the Strait of Hormuz is no longer a waterway governed by international maritime law but a managed corridor operated by a theocratic military force collecting revenue in a currency that is not the dollar. The sequence now runs as follows. A vessel operator contacts IRGC-linked intermediaries. Submits IMO number, ownership chain, cargo manifest, crew list, and destination. The IRGC’s Hormozgan Provincial Command screens for sanctions alignment and assigns a friendliness tier. The toll is calculated at approximately one dollar per barrel for oil tankers, paid in yuan through CIPS or in stablecoins through the Qeshm Island crypto exchange window. If approved, the vessel receives a clearance code and route instructions for the Larak corridors. Upon approach, VHF radio hail, AIS verification, and a patrol boat escort through the minefield-free alternative channel. One ship at a time. Fifteen to twenty ships completed this process in the first 24 hours. The pre-war average was 138 per day. Four hundred vessels are reportedly waiting outside the strait. The Gulf states have declared the toll illegal and refuse to pay. Japan’s prime minister called the strait an international public good. Oman’s transport minister said international agreements prohibit fees. None of this has stopped the IRGC from operating the corridor, collecting the revenue, and turning back tankers that attempt passage without a code. Trump claimed a complete opening of the strait. The strait is not completely open. It is completely controlled. The difference between closed and controlled is that a closed strait generates no revenue and invites military intervention. A controlled strait generates reconstruction funding in yuan, establishes a precedent for non-dollar energy settlement, and operates under the legal fiction of a safety directive that blames wartime mines for the necessity of IRGC coordination. The mines will take months to clear. The alternative routes will become permanent. The toll will become normalised. And by the time Islamabad concludes, the infrastructure of a post-dollar energy chokepoint will have been stress-tested, revenue-generating, and operationally embedded for two weeks under the protection of a ceasefire that was supposed to dismantle it. Full analysis open.substack.com/pub/shanakaans…


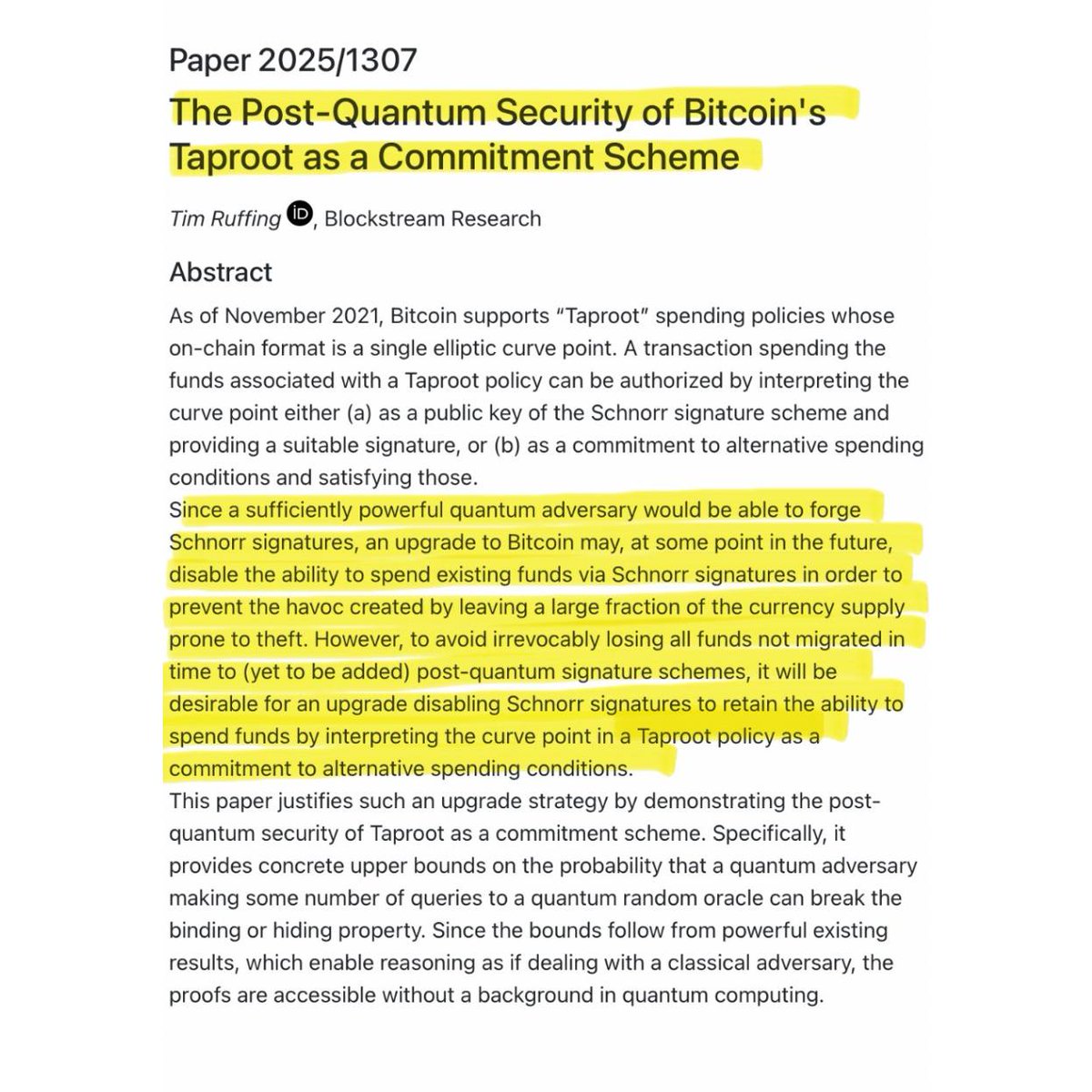
THIS IS BIG. A Bitcoin developer has built a working prototype that protects your wallet from quantum computers. Even if Bitcoin is forced to shut down part of its own security system to protect itself. To understand why this matters you need to understand the problem first. Every Bitcoin wallet is secured by a cryptographic signature scheme built on elliptic curve mathematics. The security assumption behind this system is that deriving a private key from a publicly visible public key requires computational work that classical computers cannot perform within any practical timeframe. Quantum computers running Shor's algorithm can break that assumption. Google researchers published findings last week showing a quantum computer could compromise Bitcoin's core cryptography in as little as nine minutes, using significantly fewer physical qubits than prior estimates required. The threat is not immediate but the timeline is compressing faster than most researchers projected. Now here is where it gets complicated. Bitcoin's Taproot upgrade, activated in 2021, improved transaction efficiency and privacy across the network. But by design it permanently exposes the public key of every Taproot wallet on the blockchain. Because that public key is permanently recorded and publicly visible, a sufficiently powerful quantum computer could use it to derive the corresponding private key and drain the wallet at any point in the future. Approximately 6.9 million Bitcoin across Taproot and older P2PK address formats are already in this exposed state. The developer community has a contingency plan for this scenario. If quantum computers advance to the point where this becomes an active threat, Bitcoin could activate an emergency soft fork that disables the key path spend in Taproot, which is the specific spending mechanism a quantum attacker would exploit. This closes the vulnerability before it can be exploited. But this emergency response introduces a serious secondary problem that nobody had resolved until now. The vast majority of modern Bitcoin wallets, particularly single signature Taproot wallets, rely entirely on that key path spend mechanism and have no alternative spending path configured. If Bitcoin disables that mechanism network wide, those wallets have no remaining method to authorize transactions. The funds inside them become permanently inaccessible, not stolen, but completely unspendable even by their rightful owners. The same upgrade designed to protect users could permanently strand their funds. This is the problem that Olaoluwa Osuntokun, chief technology officer of Lightning Labs, just solved with a working prototype posted to the Bitcoin developer mailing list yesterday. His solution uses a zk-STARK proof, which stands for zero knowledge scalable transparent argument of knowledge. In practical terms this means the following. Every Bitcoin wallet is ultimately derived from a master seed, typically the 12 or 24 word recovery phrase generated when the wallet is first created. All keys in the wallet are mathematically derived from that seed following a deterministic standard called BIP-32. Osuntokun built a system that generates a cryptographic proof demonstrating that a specific public key was derived from a specific master seed via the standard BIP-32 derivation path, without revealing the seed itself or any intermediate private key material. The Bitcoin network can verify the proof and authorize the wallet owner to move their funds, bypassing the disabled signature mechanism entirely. The prototype generates a valid proof in 50 seconds on a standard MacBook using Metal GPU acceleration, consumes approximately 12 gigabytes of RAM during proof generation, and produces a final proof of 1.7 megabytes. Osuntokun acknowledged the codebase is largely unoptimized and that a production implementation built specifically for this statement would run significantly faster and produce smaller proofs. He also noted that multiple proofs could be aggregated into a single compact proof to reduce on-chain verification overhead. Cryptographically relevant quantum computers capable of executing this attack do not exist today. What has changed is that Google's latest research has materially lowered the estimated resource requirements for such an attack, and the practical timeline is now closer than the field previously assumed. What is also new is that the developer community now has a working prototype of one of the critical tools needed to execute an emergency quantum defense without permanently locking legitimate holders out of their own funds. A problem that has existed in theoretical discussions for years has now produced a concrete technical implementation.







Always “restrictions,” “surveillance,” “regulation,” “punishment” … @MichaelGoolsbyV @PCBGConsulting @ShineShadowNews @CarlaHSands @bmarcois @NewshamGrant @MorseHTan @ColonelRETJohn2 @DrTaraO @WillBarclayPCBG @FredFleitz @jinil_official @bmarcois
Pope Leo says the war with Iran is unjust and solves nothing. He likes Islamic dictatorships.

Hillhouse Capital, a firm with strong Chinese ties through its founder Zhang Lei, is on the verge of acquiring IGIS Asset Management, South Korea’s largest real estate fund manager handling $52 billion in assets. IGIS oversees public pension funds and holds sensitive data on major infrastructure and property holdings across the country. The deal has drawn attention after Korean insurers, including Hyeungkuk Life, submitted higher bids but were sidelined following additional bidding rounds conducted by Morgan Stanley and Goldman Sachs. The transaction raises important questions about foreign influence over critical domestic assets. South Korea’s real estate and pension system are vital to national economic stability and retirement security for millions of citizens. When a major fund with links to a geopolitical rival gains control of such assets, it touches on broader concerns regarding economic sovereignty and the protection of public funds. In an era of increasing cross-border investment and geopolitical tension, how nations safeguard strategic domestic assets directly affects public trust and long-term economic independence. Do you believe foreign acquisitions of key financial institutions like IGIS should face stricter national security reviews, or should market principles take priority?

“Virgin female prisoners should be raped before execution so that they do not go to heaven.” -Ayatollah Khomeini (founding leader of the Islamic regime in Iran). I’ll never wrap my head around the fact that this is what Western leftists decided to side with.



