ทวีตที่ปักหมุด
Tyson Benson
2.5K posts


Tyson Benson
@tysonbenson
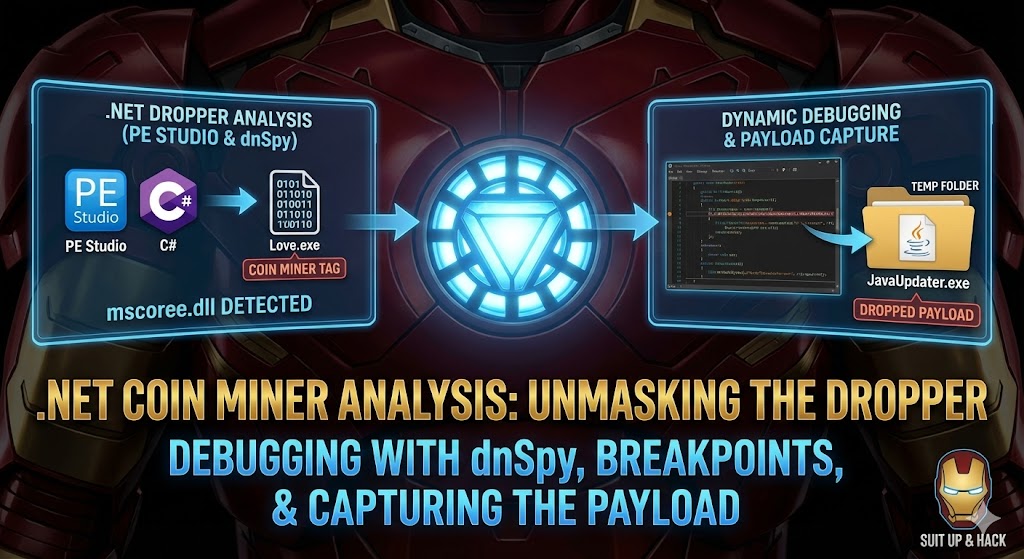
Patent Law → Product Cybersecurity | Suit Up & Hack 📺 | Malware Analysis • Exploit Dev • Windows Internals
Detroit, Michigan เข้าร่วม Eylül 2010
2K กำลังติดตาม1.7K ผู้ติดตาม
Tyson Benson รีทวีตแล้ว

Tyson Benson รีทวีตแล้ว
Tyson Benson รีทวีตแล้ว

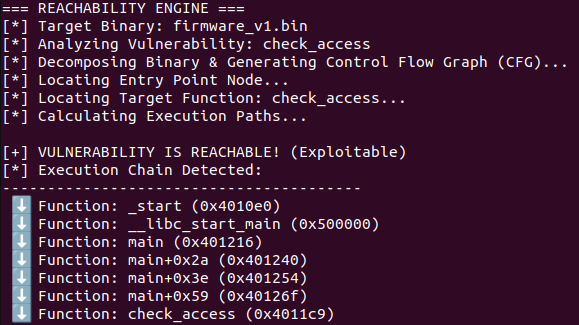
Compliance is checking a box. Security is checking the execution path.
I don't care if the library version is vulnerable. I care if the function is reachable.
Built a prototype today to trace the "Red Line" of execution from the kernel handoff straight to the vulnerability.
Proof of Reachability > CVSS Score
English
Tyson Benson รีทวีตแล้ว

💀 Using EMBA from @securefirmware to find CVEs in IoT camera firmware! youtu.be/wmDa4WxLnLs

YouTube
English
Tyson Benson รีทวีตแล้ว

From chip to code! 💻 I'm dumping router firmware with a CH341A and letting EMBA hunt for vulns. This is how you start reverse engineering hardware. #HardwareHacking #EMBA #Flashrom #SecurityResearch youtu.be/-YlEaXoWhWY

YouTube
English
Tyson Benson รีทวีตแล้ว

Tyson Benson รีทวีตแล้ว

New Video! Part 1 of Build Your Own AI Agent: Static IoT Firmware Analysis with Python & LLMs! youtu.be/P6Izjw98vYc?si…

YouTube
English
Tyson Benson รีทวีตแล้ว
Tyson Benson รีทวีตแล้ว
Tyson Benson รีทวีตแล้ว
Tyson Benson รีทวีตแล้ว

🚨 Big news: New TH Book 🏹
After years in Threat Hunting, I wrote the book I always wanted when I started.
The Art of Threat Hunting, practical, technical, no fluff.
⚡Hypothesis generation, queries & adaptation stuff, CTI-driven programs, documentation, team alignment. The full lifecycle.
🦖Full breakdown on the blog: rexorvc0.com
🔗Available on Amazon: amazon.com/Art-Threat-Hun…
#ThreatHunting #BlueTeam #Cybersecurity #Research #CTI #Malware #threat

English
Tyson Benson รีทวีตแล้ว

Like everything in life - begin with the basics in Reverse Engineering - revers.engineering/applied-re-bas…
English
Tyson Benson รีทวีตแล้ว
Tyson Benson รีทวีตแล้ว
Tyson Benson รีทวีตแล้ว

Oh you've compiled a kernel? Yeah, yeah, yeah but have you compiled a BROWSER. In this next video we continue the series of going through @ret2systems browser exploitation course. I would consider this another beginner friendly tutorial so don't be intimidated!
Join me and check out the latest video below!
youtu.be/f3okm258ZiE
YouTube
English
Tyson Benson รีทวีตแล้ว

Thread: How real adversaries are using C2 in 2026 (From building @scythe_io + watching nation-state/red team playbooks)
Spoiler: It's not just fancy Cobalt Strike beacons anymore. 🦄 1/10
English
Tyson Benson รีทวีตแล้ว

Interested in exploiting browsers? Join me as I go over the free section of @ret2wargames "Fundamentals of Browser Exploitation" course. This is a course delivered by real #Pwn2Own winners! So, you're learning from the best! This first video is very beginner friendly so check it out even if you're just curios🧐.
Video link below:
youtu.be/5ArMYqwCmD4

YouTube
English
Tyson Benson รีทวีตแล้ว

A lot of malware analysts, myself included, are building something similar, so it’s amazing to see a Docker environment already bundled with the tools, MCP backend, and skills. Definitely gonna try this. Thanks for sharing!!
Tim Blazytko@mr_phrazer
New blog post: Building a Pipeline for Agentic Malware Analysis Agentic RE + malware analysis with custom skills, MCP tooling, and persistent case state to automate intial triage Link: synthesis.to/2026/03/18/age… Github: github.com/mrphrazer/agen…
English

@Steph3nSims Welcome these chances - strive to become an expert in the field(s). These are the times to differentiate yourself.
English
Tyson Benson รีทวีตแล้ว

I want to share a quick thought for people in cyber security. This will be my longest tweet ever.
I’ve spoken to many lately who are having an existential crisis from the constant posts about “the end of cybersecurity jobs.”
Yes, things are changing quickly. This is a significant moment for the tech industry. Change can be uncomfortable. But we’ve seen cycles like this before.
• When GitHub and open source took off, people said software engineers would disappear because code was free.
• When AWS and cloud computing emerged, people said infrastructure jobs would vanish.
• When fuzzing and SAST tools improved, people said vulnerability research would disappear.
• Virtualization would eliminate infrastructure jobs.
• Mobile computing was going to end desktop dev.
• Exploit mitigations would end exploitability. It didn't.
Each time automation improved, the amount of software grew faster than the automation. It does feel "different" this time as it's explosive.
Some roles will shrink:
• repetitive pentesting
• basic vulnerability scanning
• tier-1 SOC monitoring
But other areas are expanding rapidly:
• AI system security
• supply chain security
• identity architecture
• autonomous agent security
• critical infrastructure protection
Historically, every time we eliminate one class of bugs, new classes emerge. Right now people are vibe-coding entire systems, giving AI access to their machines, crossing trust boundaries, and deploying autonomous agents with excessive permissions. The legal and regulatory world is nowhere close to ready.
There will absolutely be new failure modes. Humans are amazing and always adapt, finding new ways to do things.
The worst thing you can do right now is fall into a doom loop.
...and I’ll be honest, I too have felt the "psychological paralysis" a few times thinking, “Is this time different?” It's especially impactful when it comes from someone I respect in the community. There are certainly unknowns, in an industry where we've become accustomed to predictability.
But... the majority of those reactions are usually driven by social media, not reality. Platforms like X reward engagement, and sensational doom posts spread faster than measured thinking.
If you see something like:
“Holy #$%^! Opus 66.6 just found every bug in Chrome and replaced 50 startups!”
…mute it and move on.
Instead:
Stay curious.
Learn the new technology.
Adapt your skillsets.
Build things.
We’ll get through this transition the same way we always have. If I'm wrong then Sam Altman better be right about UBI! :) I'm sure that if this tweet gets any engagement that I'll get some heat for it, but a good friend of mine reminds me often to focus on what you have control over. I'll revisit this tweet at DEF CON 40!
English