NETERN
12.6K posts


NETERN
@0xnetern
Product Developer || Cyber Security Expert || UI UX Designer || Blockchain Security Expert || NFT collector







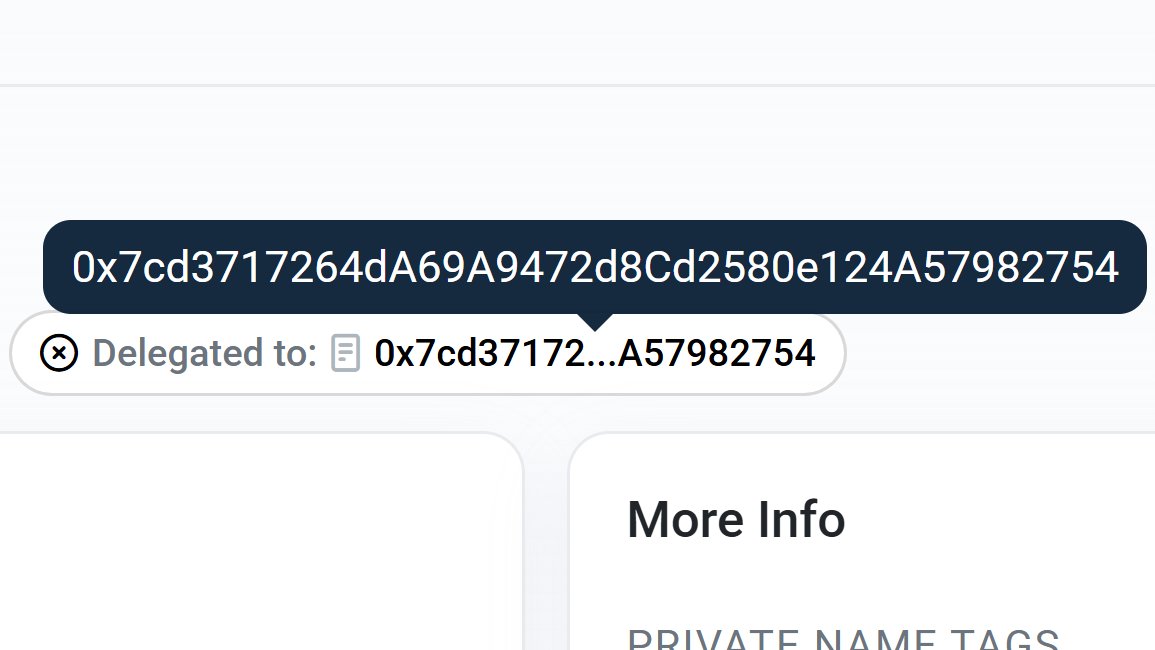
BUILD4 Security Disclosure: ERC-7702 Delegation Attack on Developer Wallet To our BUILD4 community, We believe in full transparency, which is why we are sharing the findings of an independent security investigation conducted by @MetaFinancialAI (MEFAI). What happened: A BUILD4 developer wallet was compromised through an ERC-7702 delegation attack, a new class of exploit known as "CrimeEnjoyor" that has affected over 450,000 wallets globally across Ethereum and BNB Chain since the Pectra upgrade. The attack works by disguising a malicious authorization signature as a normal wallet interaction. Once signed, the attacker's contract gains full control of the wallet, including the ability to auto-forward any incoming funds. MetaFinance confirmed on-chain that the wallet's bytecode was overwritten with a delegation pointer to a malicious contract controlled by a serial drainer address with nearly 4,000 transactions — an organized, industrial-scale operation that has hit thousands of wallets across the ecosystem. User funds are completely safe. This attack targeted only an individual developer wallet. No user wallets, no treasury funds, no platform contracts, and no private keys were affected. BUILD4's infrastructure, smart contracts, and all user-facing systems remained fully secure throughout. The compromised wallet has been permanently retired and was never connected to user funds or platform operations. What we did immediately: Identified and isolated the compromised wallet within hours Engaged MetaFinance for an independent on-chain forensic analysis Rotated all operational keys and deployed fresh secure wallets Verified the integrity of all platform contracts, treasury, and user wallets Confirmed zero impact on any user funds or platform operations A warning to fellow AI and Web3 projects: ERC-7702 delegation attacks are a serious and emerging threat that the industry is not yet fully prepared for. Wallet interfaces including MetaMask did not properly flag these authorization payloads when BNB Chain first enabled support. Research by Wintermute confirmed that over 80% of ERC-7702 delegations in the wild were linked to malicious drainer scripts. We urge every project, developer, and user in the space to: Audit all operational wallets by checking bytecode (any address returning code starting with 0xef01 is compromised) Never reuse wallets that show delegation signatures Use dedicated hardware wallets with updated firmware for all operational keys Treat any unfamiliar transaction confirmation with extreme caution Our commitment: Security is not an afterthought at BUILD4 — it is foundational. We are taking additional steps to harden our operational security, including multi-signature requirements for all platform wallets and enhanced monitoring for emerging attack vectors. We will continue to operate with full transparency and share findings that can help protect the broader community. Your funds are safe. Your trust matters to us. — The BUILD4 Team






Last Wednesday (March 25), my crypto wallet was drained for ~79k. I have had people assist me during the investigation period and while I am not certain, I believe is the attack may have originated from a phishing link in the bio of a profile currently leading @Kalshi's weekly leaderboard for total predictions. I had clicked into a profile (“Miss.Cleo”) while browsing and saw what looked like a normal Vercel link. It was actually vvwv.vercel.app — two v’s made to look like a “w.” In hindsight, the account looks suspicious: created in January 2026, zero posts, no public profit or volume, but 160k+ predictions in roughly three months. It doesn’t seem like normal trading activity. It looks more like someone synthetically climbing the leaderboard to gain visibility, and drive traffic through the bio link. The link has since been removed. Including all the nerdy details of the crypto theft below on the off chance anyone cares to read : Within 27 minutes of clicking the link, an automated script drained my entire Exodus wallet — BTC, USDC, and USDT — across two blockchains. At 11:59 AM EST, $28,039 in USDC was sent to: 0x7dc0cbf8c92b819652d577cae53fb021cfadaf72 Within 36 seconds, dust deposits started arriving from lookalike addresses — address poisoning designed to confuse any future copy-paste transactions. At 12:16 PM EST, the BTC sweep started. 10 transactions fired in 10 seconds — one per second — each draining a UTXO to a different Bitcoin address. Five minutes later, a second burst: 7 more transactions in 7 seconds. 17 total BTC transactions. This cadence is not possible manually At 12:26 PM EST, the remaining $527 in USDT was drained to: 0x785c5f491fa058f6b2149b9ff2b186869bd1c969 Total stolen: ~0.7017 BTC (~$49,700), 28,039 USDC, 527 USDT. Approximately $79,853 in under 30 minutes. USDC ($28,039): Moved within 3.5 hours through an intermediary, then forwarded in 48 seconds to a high-volume aggregator: 0x2CfF890f0378a11913B6129B2E97417a2c302680 As of today that aggregator holds over $21.5 million — 838 ETH, 10.3M USDC, 2.5M USDT, 56 WBTC, and 213 other tokens. This was premeditated. The USDC theft address is not a normal wallet — it's an EIP-7702 proxy contract that was deployed and pre-funded with ETH from multiple addresses starting March 22 It processes transfers from hundreds of addresses every few minutes. This is not a personal wallet. It's either an exchange hot wallet, an OTC desk, or a professional laundering operation. BTC (~$49,700): Was scattered across 11 addresses, cycled through a self-mixing pattern, and consolidated. That consolidation address has since been swept — the BTC was batched into a 70+ BTC transaction alongside what appears to be funds from other victims. All 11 theft addresses are now zeroed out. The BTC is gone. USDT ($527): Still sitting untouched at 0x785c5f491fa058f6b2149b9ff2b186869bd1c969



CLAUDE POWERED BOT TURNED $1 INTO $3.3M BY ARBITRAGING POLYMARKET FASTER THAN ANY HUMAN CAN REACT








gm, if u have been in this space for more than 2 years and have never lost funds to any hack, be it a protocol exploit or ur own wallet getting compromised, u are either lying, u have nothing to lose or u are the most disciplined human being alive, there is no in between respect to all three


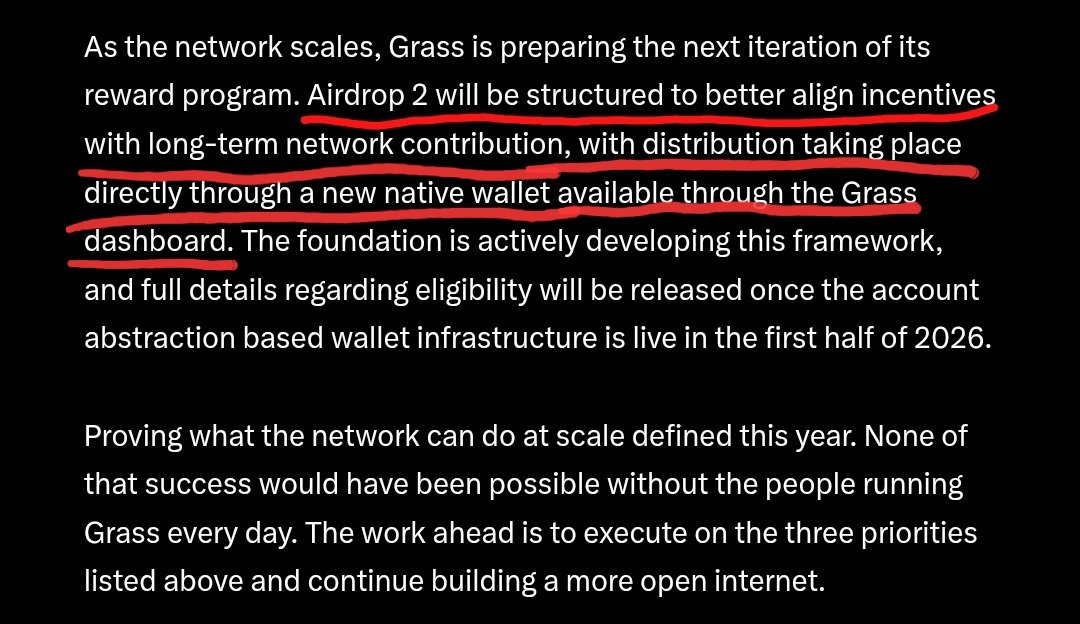

Am I fhe only one who will farm $GRASS points this Q2?