Tony Lambert ری ٹویٹ کیا
Tony Lambert
3.9K posts


Tony Lambert
@ForensicITGuy
Recovering sysadmin that now chases adversaries instead of uptime. Sr Malware Analyst @redcanary
Tennessee شامل ہوئے Kasım 2011
1.2K فالونگ6.1K فالوورز

Sometimes adversaries bring in their own tools, and if they leave behind a VM disk, analysis is fair game. In this post we look at some tools an adversary brought during a social engineering campaign. sprou.tt/1tw5BYzWIb1
English
Tony Lambert ری ٹویٹ کیا

In a revealing blog, we detail the #digitaltransformation of cargo theft: a criminal enterprise that leads to $34 billion in annual losses.
Threat actors are combining #socialengineering w/ transportation industry knowledge to steal real physical goods. brnw.ch/21wX9UA
English
Tony Lambert ری ٹویٹ کیا

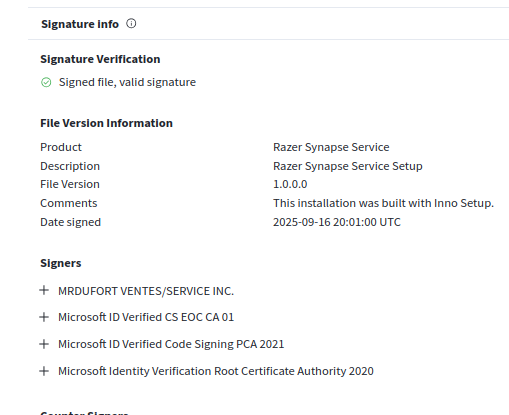
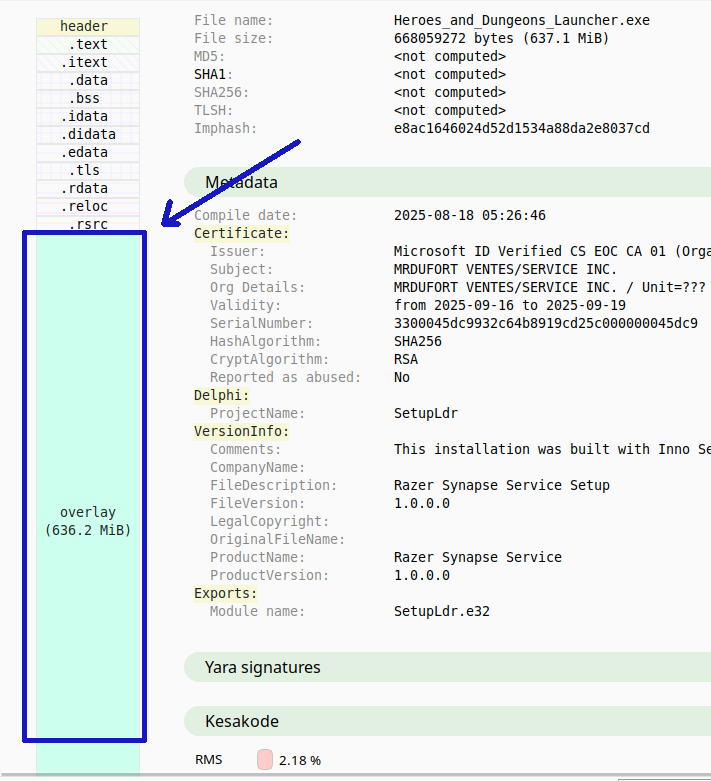
In early October 2025, Microsoft disrupted a Vanilla Tempest campaign by revoking over 200 certificates that the threat actor had fraudulently signed and used in fake Teams setup files to deliver the Oyster backdoor and ultimately deploy Rhysida ransomware.
We identified this Vanilla Tempest campaign in late September 2025, following several months of the threat actor using fraudulently signed binaries in attacks. In addition to revoking certificates, Microsoft Defender Antivirus detects the fake setup files, Oyster backdoor, and Rhysida ransomware, and Microsoft Defender for Endpoint detects Vanilla Tempest TTPs.
Vanilla Tempest, tracked by other security vendors as VICE SPIDER and Vice Society, is a financially motivated actor that focuses on deploying ransomware and exfiltrating data for extortion. The threat actor has used various ransomware payloads, including BlackCat, Quantum Locker, and Zeppelin, but more recently has been primarily deploying Rhysida ransomware.
In this campaign, Vanilla Tempest used fake MSTeamsSetup.exe files hosted on malicious domains mimicking Microsoft Teams, for example, teams-download[.]buzz, teams-install[.]run, or teams-download[.]top. Users are likely directed to malicious download sites using search engine optimization (SEO) poisoning.
Running the fake Microsoft Teams setups delivered a loader, which in turn delivered a fraudulently signed Oyster backdoor. Vanilla Tempest has incorporated Oyster into their attacks as early as June 2025, but they started fraudulently signing these backdoors in early September 2025.
To fraudulently sign the fake installers and post-compromise tools, Vanilla Tempest was observed using Trusted Signing, as well as SSL[.]com, DigiCert, and GlobalSign code signing services.
Fully enabled Microsoft Defender Antivirus blocks this threat. In addition to detections, Microsoft Defender for Endpoint has additional guidance for mitigating and investigating this attack. While these protections help secure our customers, we’re sharing this intelligence broadly to help strengthen defenses and improve resilience across the entire cybersecurity community.

English

It's not just you, most of the macOS stealers look the same nowadays, but there are subtle differences between stealer families to tell them apart. If you're a stickler for detail like us, you might enjoy this post showing differences between the malware. sprou.tt/1cb631gju8p
English
Tony Lambert ری ٹویٹ کیا

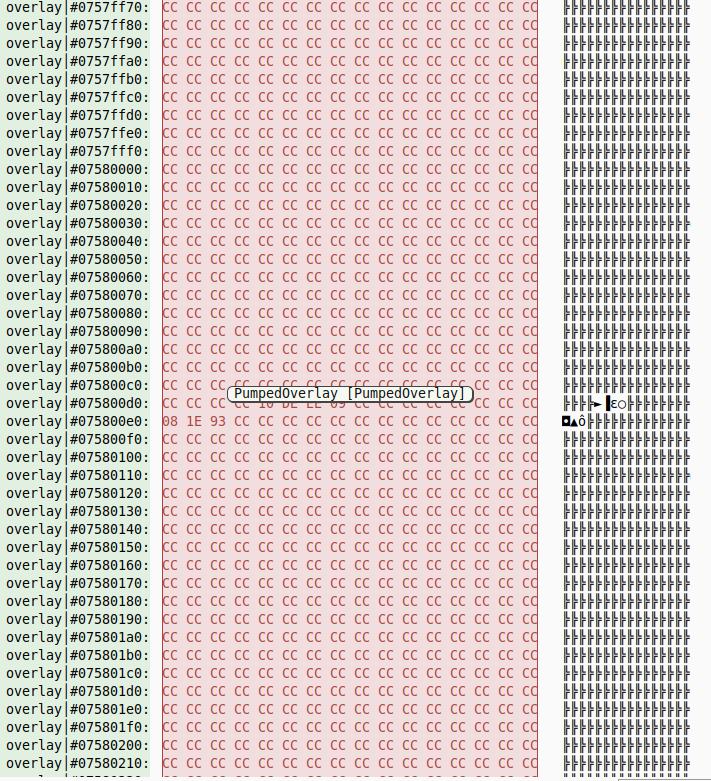
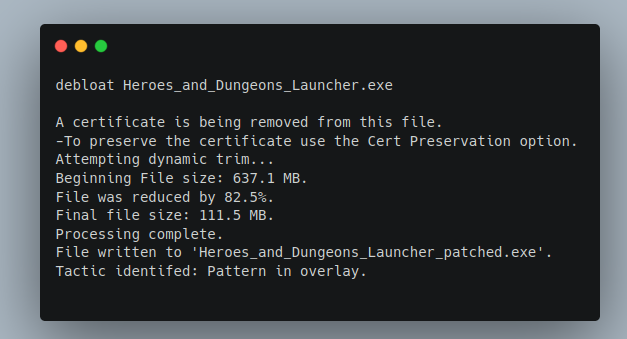
"FUD" from VirusTotal.
Signed, 112 MB file.
Lets analyze.
File is SingleFile .NET; I see this with Malcat:
Debug and Exports indicate it is SingleFile (green arrows in image)
Also, Malcat carved 270 PE out of the overlay (blue arrow), indicative of SingleFile .NET
1/8

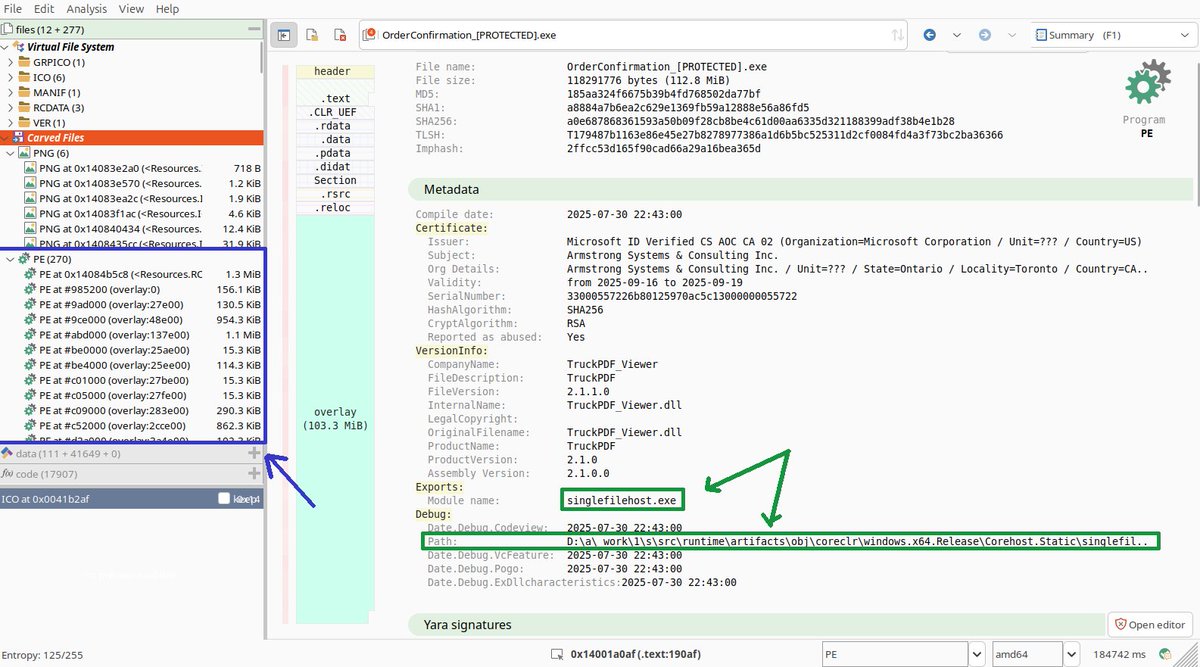
MalwareHunterTeam@malwrhunterteam
"Armstrong Systems & Consulting Inc." (Microsoft given cert) signed "OrderConfirmation_[PROTECTED].exe" sample: a0e687868361593a50b09f28cb8be4c61d00aa6335d321188399adf38b4e1b28
English
Tony Lambert ری ٹویٹ کیا
Tony Lambert ری ٹویٹ کیا
$5 Membership sale is live for the next 24 hours: account.shodan.io/billing/member
English
Tony Lambert ری ٹویٹ کیا
Not only is @HuntressLabs a generous supporter of our Foundation, they also consistently publish top-notch research on emerging macOS threats 🤩
Their latest (by @birchb0y & @stuartjash):
"Feeling Blue(Noroff): Inside a Sophisticated DPRK Web3 Intrusion": huntress.com/blog/inside-bl…
English
Tony Lambert ری ٹویٹ کیا
Tony Lambert ری ٹویٹ کیا

Just 2 days until the next session in our Detection Series!
This time, we’re covering all things initial access — and how to better defend against these evolving tactics.
🎯 This session is a must-attend for blue teams and threat analysts.
➡️ Register now before the last-minute spots fill up: bit.ly/4df8VYx

English
Tony Lambert ری ٹویٹ کیا

✨ Red Canary ➕ @zscaler
Today we are announcing Zscaler’s agreement to acquire Red Canary.
It’s a major milestone in our journey. This is a significant step forward in our mission to improve security operations, not just for our customers, but for the entire cybersecurity community. 🧵⬇️
English

Do you miss @cobaltstrikebot? If so, here's a blog post showing how you can pull Cobalt Strike SpawnTo and watermark info with @shodanhq and some PowerShell: forensicitguy.github.io/squeezing-coba…
English
Tony Lambert ری ٹویٹ کیا
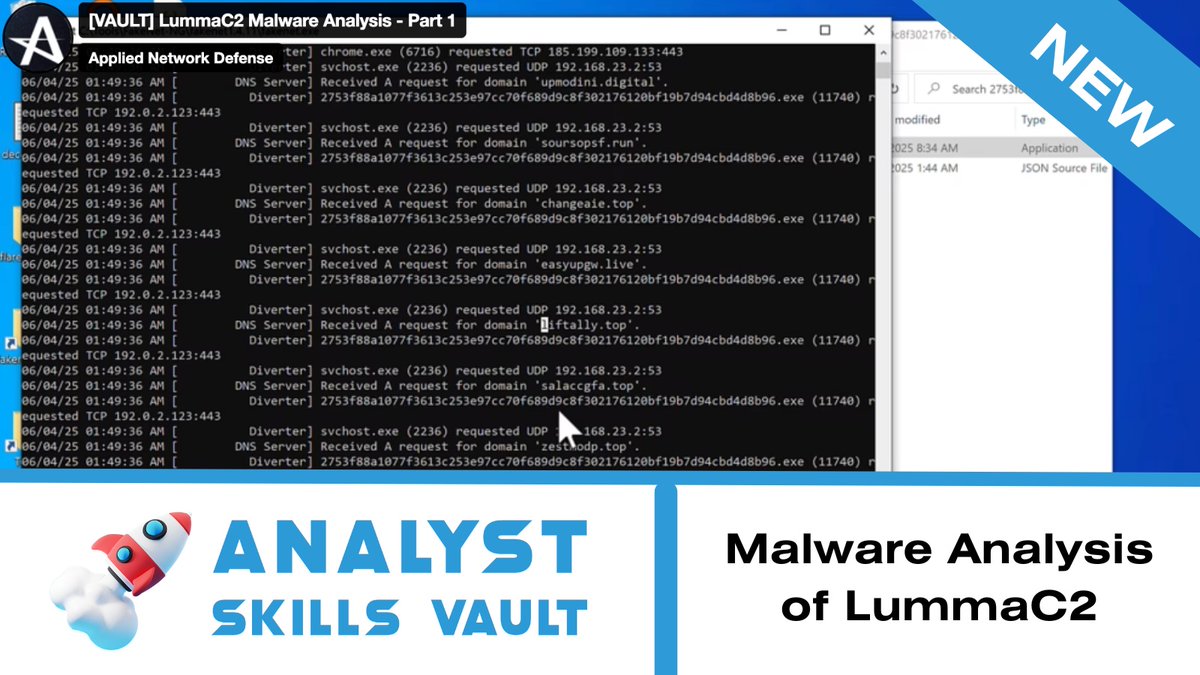
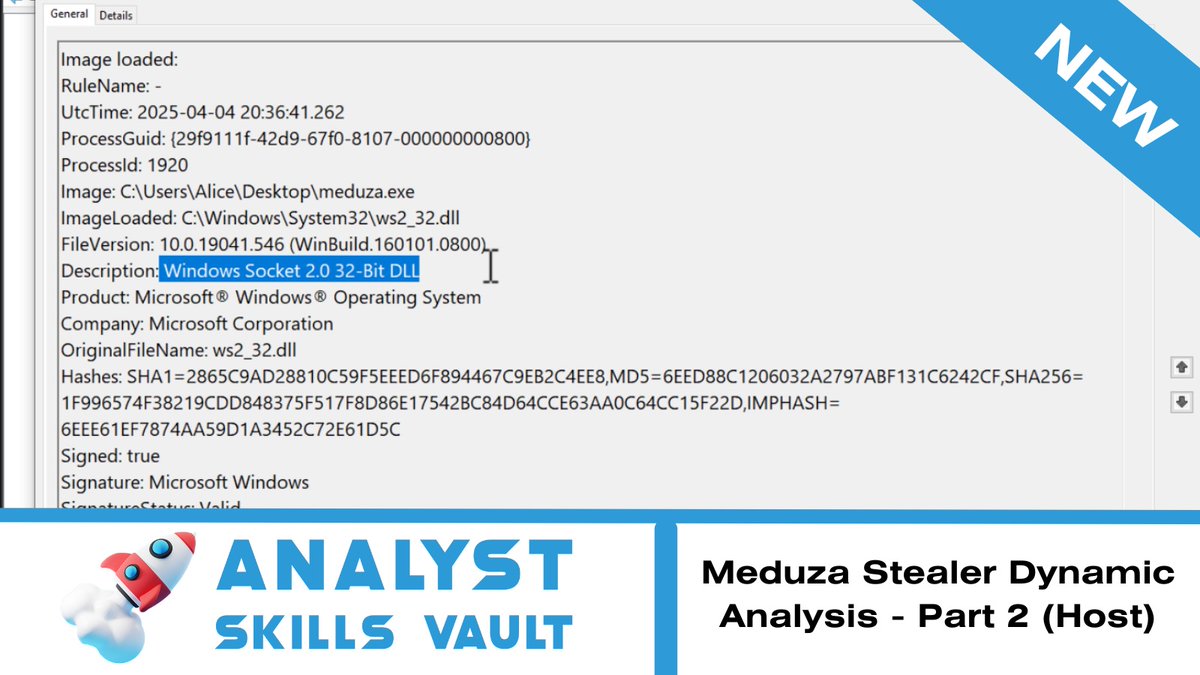
In our latest Analyst Skills Vault lesson, @ForensicITGuy walks through a dynamic analysis of the Meduza Stealer Malware, focusing on host-based artifacts.
English
Tony Lambert ری ٹویٹ کیا

JUST IN: Red Canary Intel has observed activity exploiting a newly-documented unrestricted file upload vulnerability in SAP NetWeaver Visual Composer, software used to develop enterprise applications for business analysts.
🔗 Read our blog for detection opportunities and indicators of compromise: bit.ly/3RF2STl
English
Tony Lambert ری ٹویٹ کیا

Threat Detection Highlights Webinar series – April Edition: This month’s session is extra special. zoom.us/webinar/regist…
We're excited to welcome Tony Lambert @ForensicITGuy , Senior Malware Analyst at @redcanary, known for his sharp research and impactful community contributions.
Joining him is Patrick Staubmann from @vmray Labs, who will bring his researcher’s lens to the latest detection techniques and platform updates.
On the agenda:
🧠 Detecting CPU property queries via registry (new VTI)
🕵️♂️ Anti-sandbox YARA rules: Latrodectus, Hijackloader & "Paste & Run"
💥 Ransomware-focused YARA detection
🐀 RAT config extraction + DNS tunneling
⚡ Quick sandbox demo
🎯 Save your seat now — you won’t want to miss this deep dive into the latest threat detection techniques:
zoom.us/webinar/regist…

English
Tony Lambert ری ٹویٹ کیا

Chrome 136 now has enhanced cookie security 🍪 → goo.gle/3DMf5SS
Changes to remote debugging switches protect your data. Find out how the --remote-debugging-port and --remote-debugging-pipe switches are now being handled.
English
Tony Lambert ری ٹویٹ کیا