Gam4er
36 posts


However, terminating the process isn't always convenient, especially if it's a critical system process that you don't want to disrupt. In the case of CLR code injection, a better approach is to load the malicious code into a new AppDomain and then unload that domain once it's done—leaving no lingering artifacts.
This is how it's implemented in my code: github.com/gam4er/SneakyR…
Process still running, but all artifacts disappeared
English
Gam4er ری ٹویٹ کیا

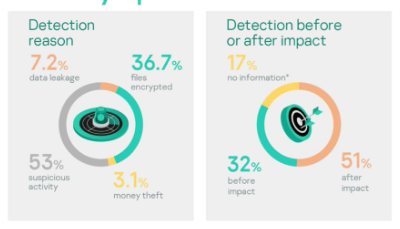
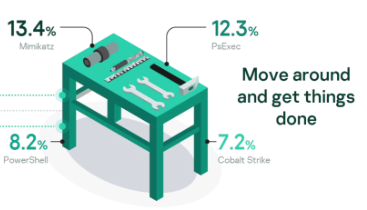
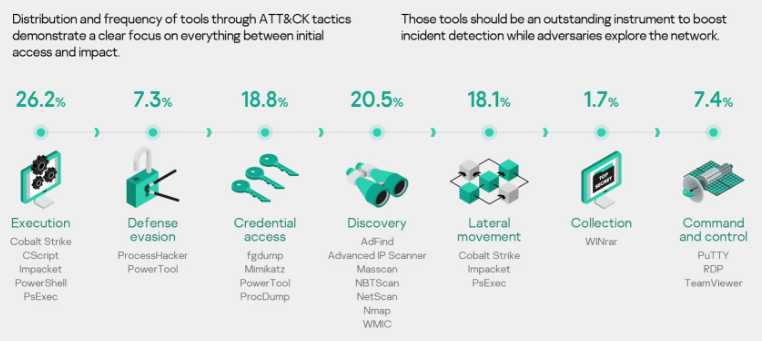
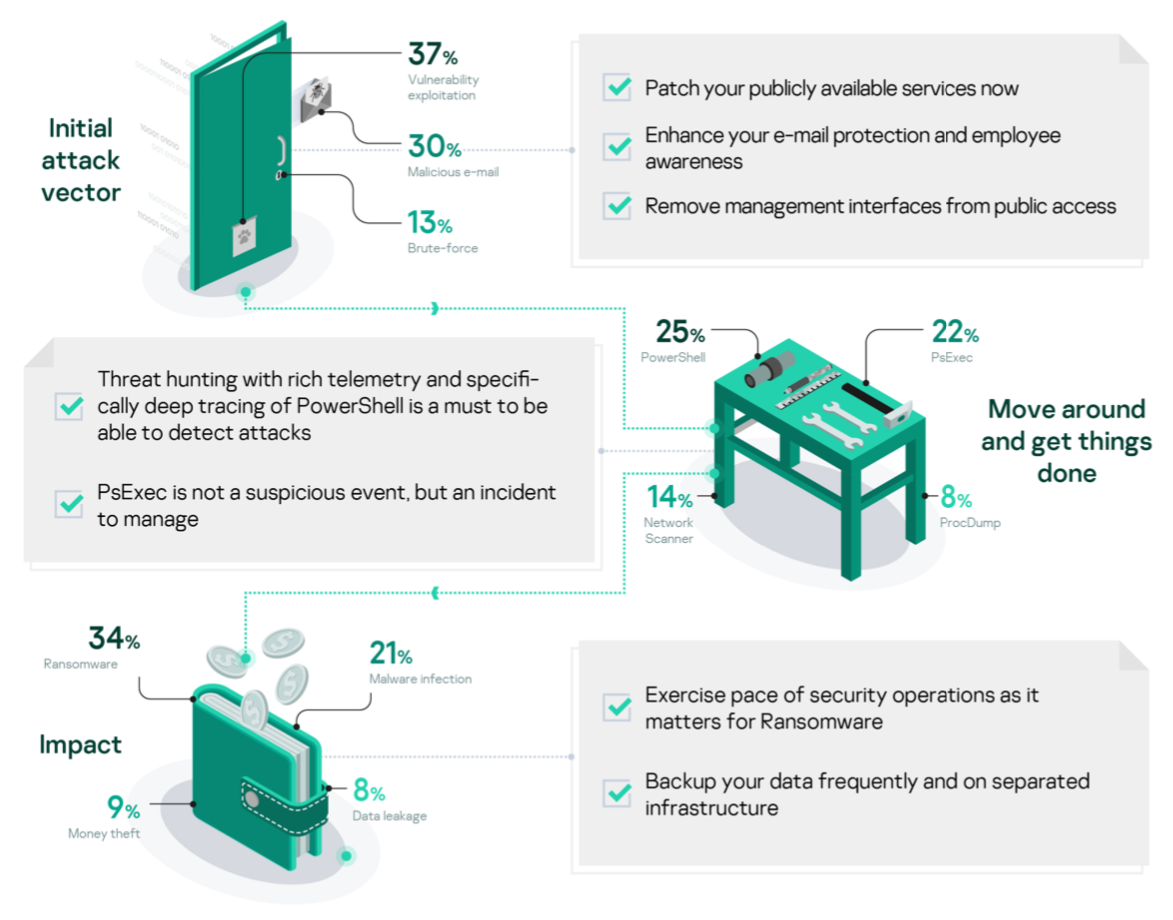
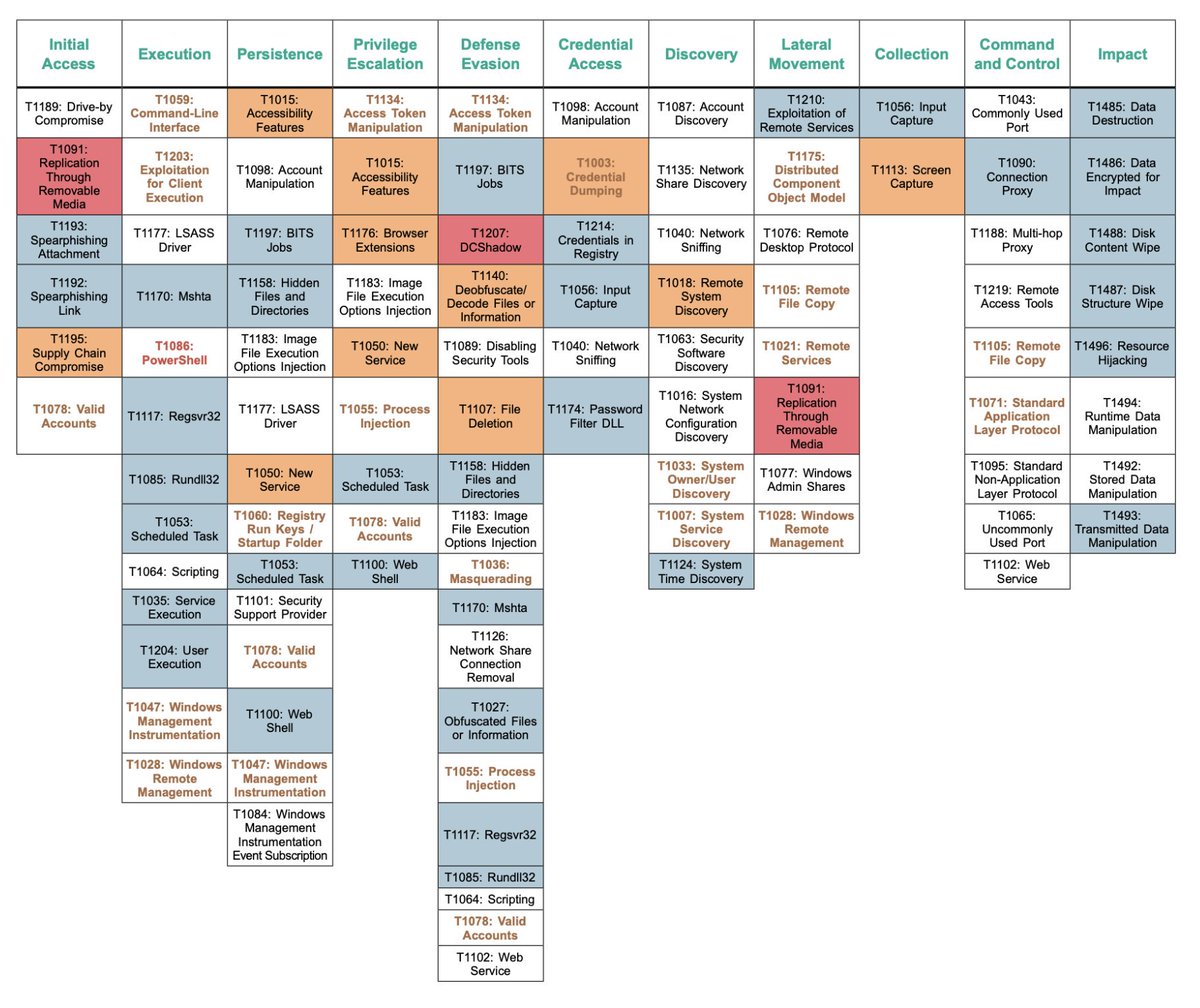
Analyst report for IR cases from 2020 is available github.com/klsecservices/… #DFIR #incidentresponse #threathunting
English

@ANDREW1ALBERTT He is wonderful, but IMHO, with this lovely color it is much better to be a British cat, than a puppy.
Call him Barsik (popular cat name in Russia)
English
Gam4er ری ٹویٹ کیا

All incident response cases from 2019 in our yearly analyst report. Adversaries initial vectors, tools, #MITRE techniques and more. github.com/klsecservices/…
English
Gam4er ری ٹویٹ کیا

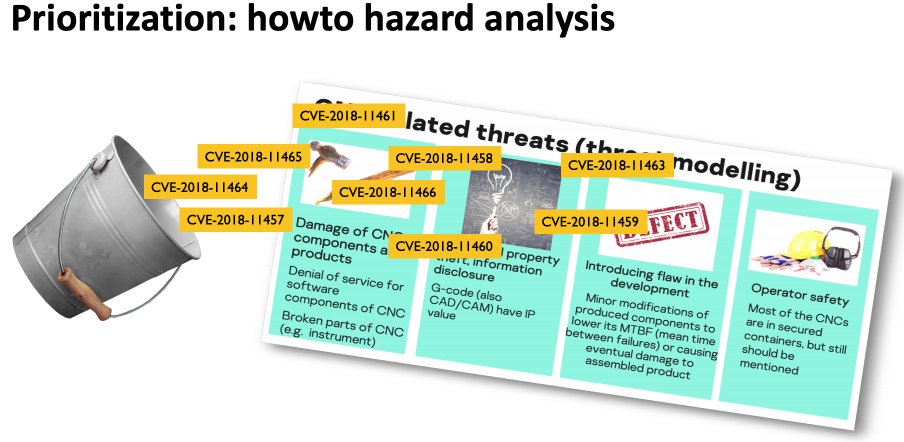
Manufacturing (CNC) security presented by @574rz on @SecurityWeek’s Singapore ICS Cyber Security Conference. Now watch your #CNC spindles and #industry40 closely! Slides are finally available. Whitepaper to be published soon. #icssecurity #otsecurity github.com/klsecservices/…
English

@jarnomn @gentilkiwi Mr Benjamin try to emphasize, that AV vendors sometimes can not detect/prevent the prosess of ectraction credentials, isn't it? Detecting just files are boring ;)
English

Of course, not really Microsoft related
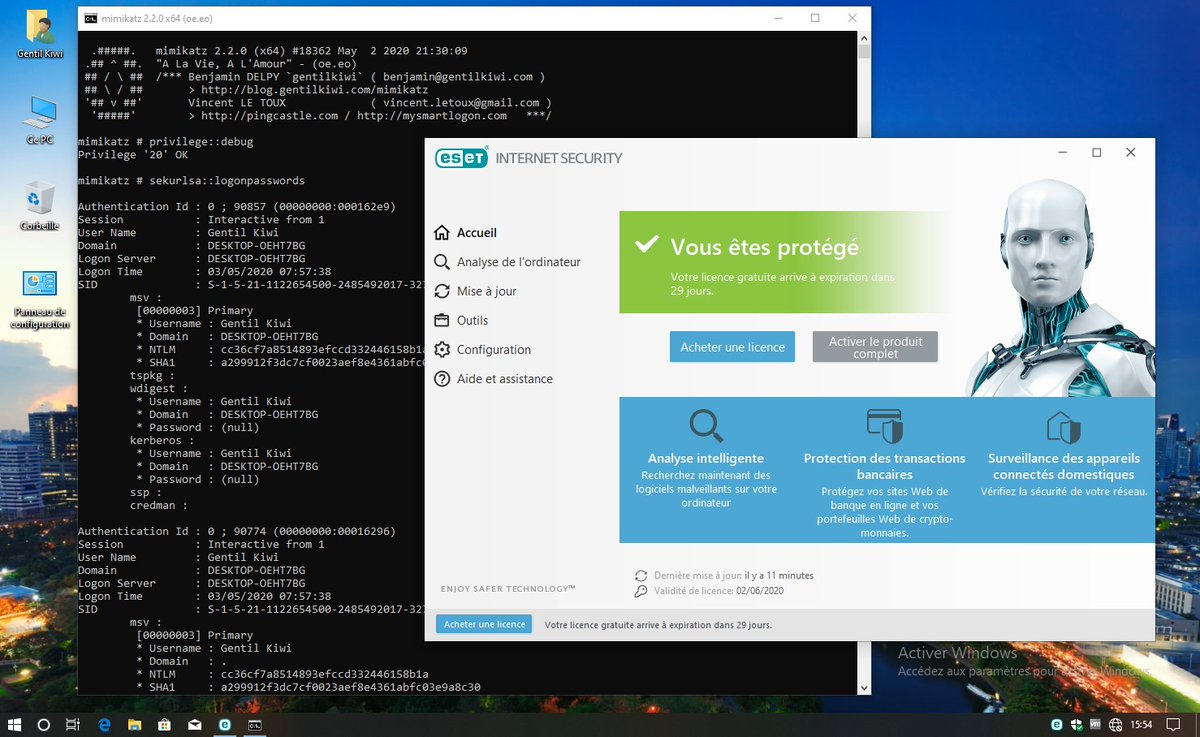
🥝🏳️🌈 Benjamin Delpy@gentilkiwi
#mimikatz (custom) on a fresh Windows 10 up to date
English
Gam4er ری ٹویٹ کیا

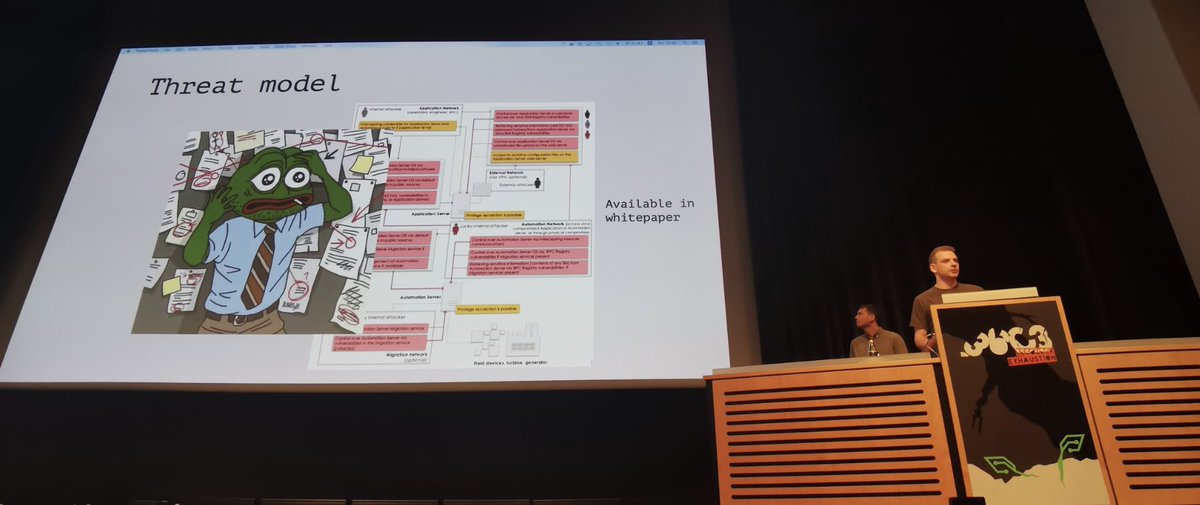
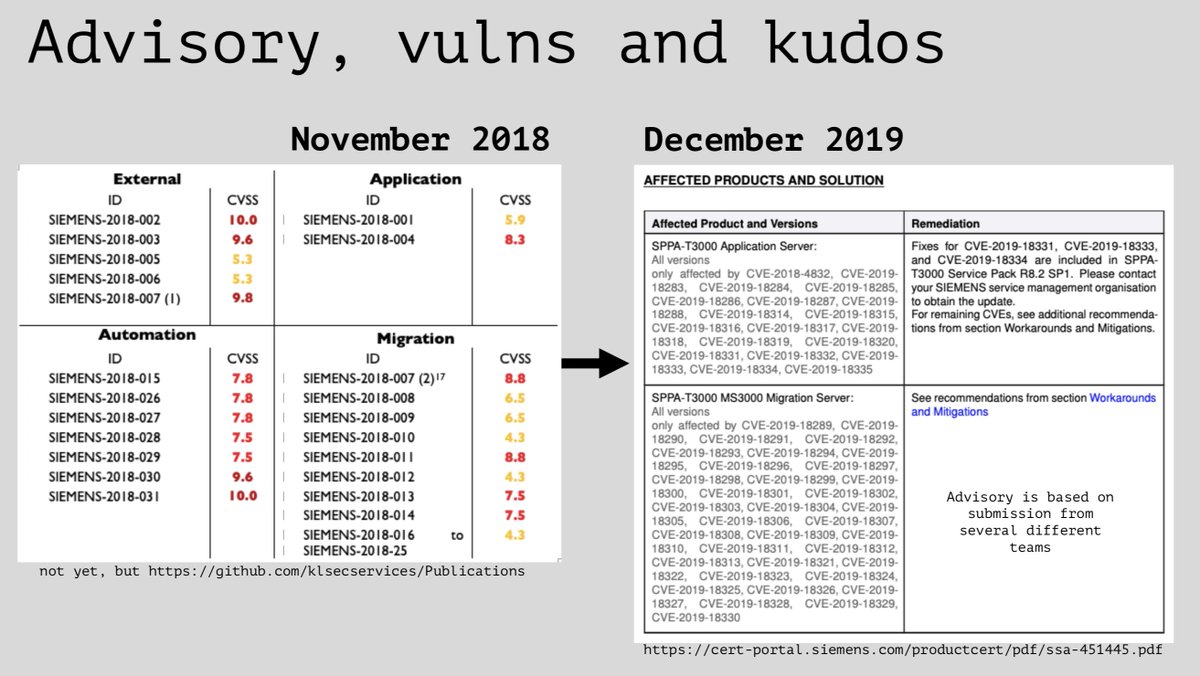
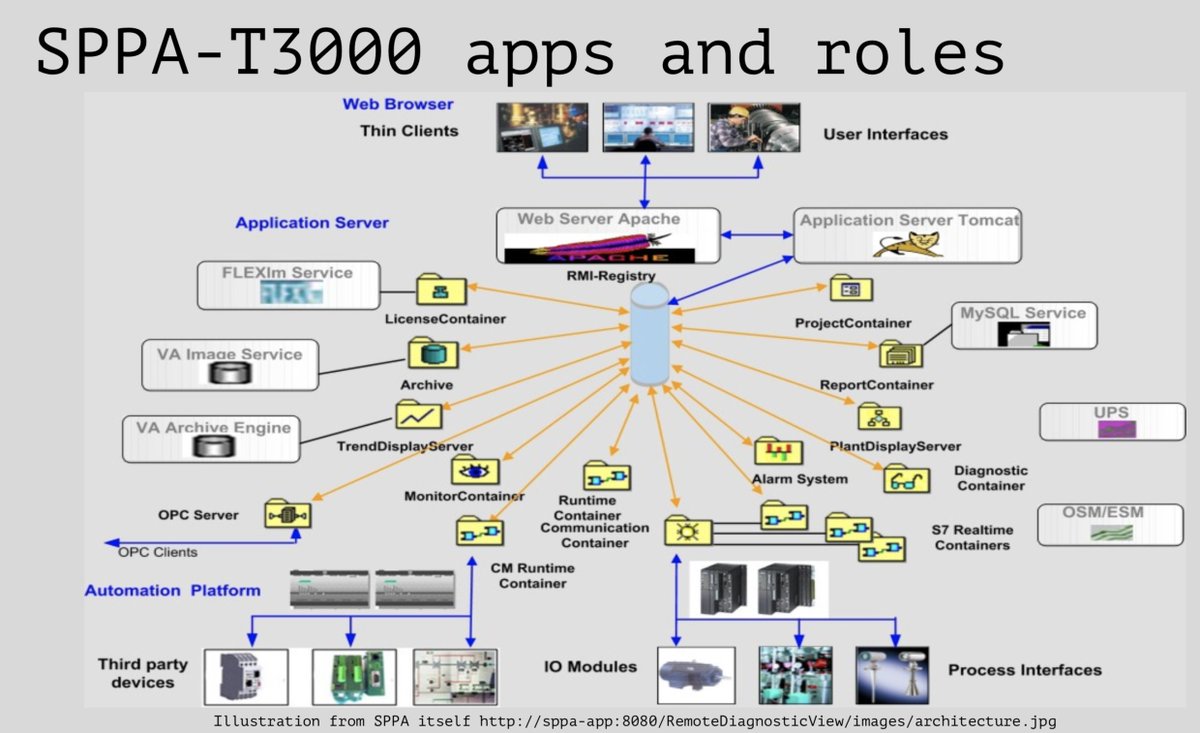
More on DCS security in our power plant automation research github.com/klsecservices/… from #36c3 talk media.ccc.de/v/36c3-10689-o…. Now with DIY assessment, wordlists and awesome visuals.
tldr; learn to do basic assessment by yourself, ask uncomfortable questions, update your DCS
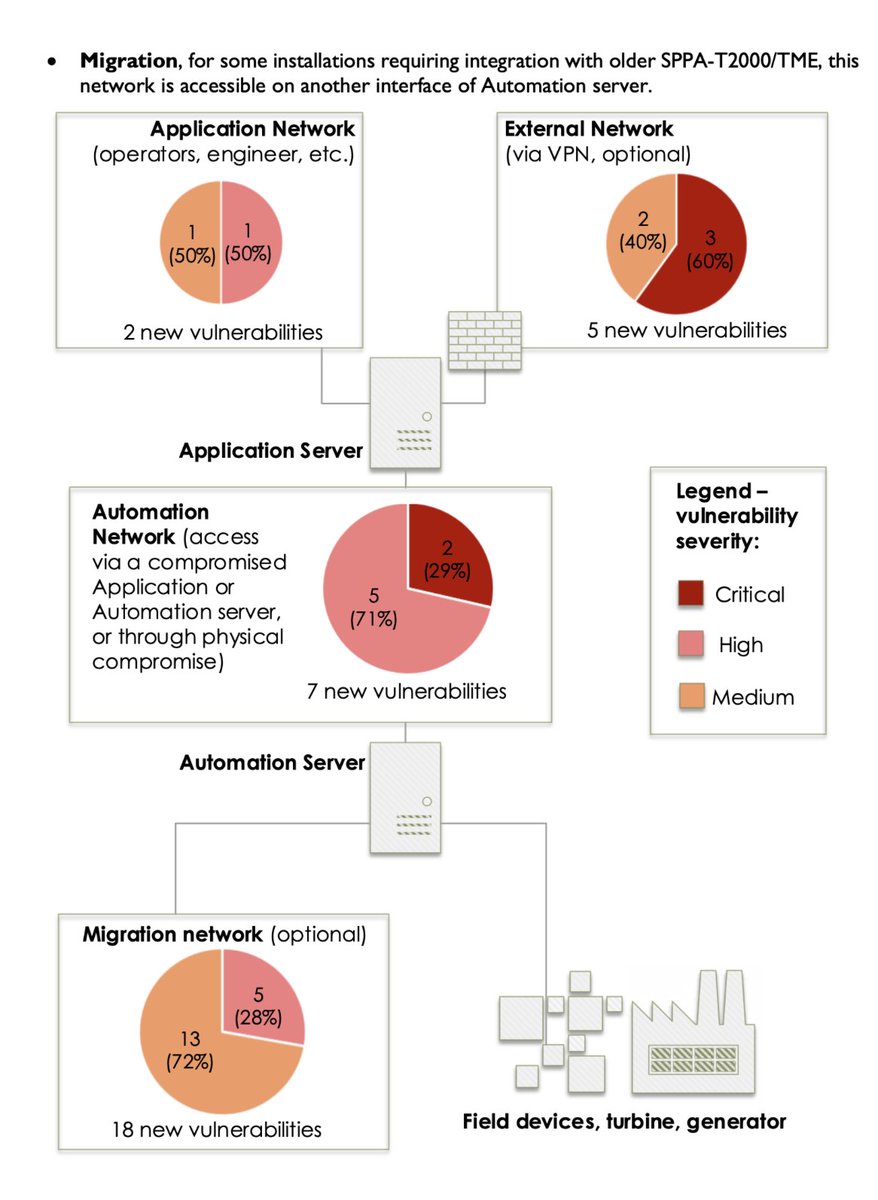
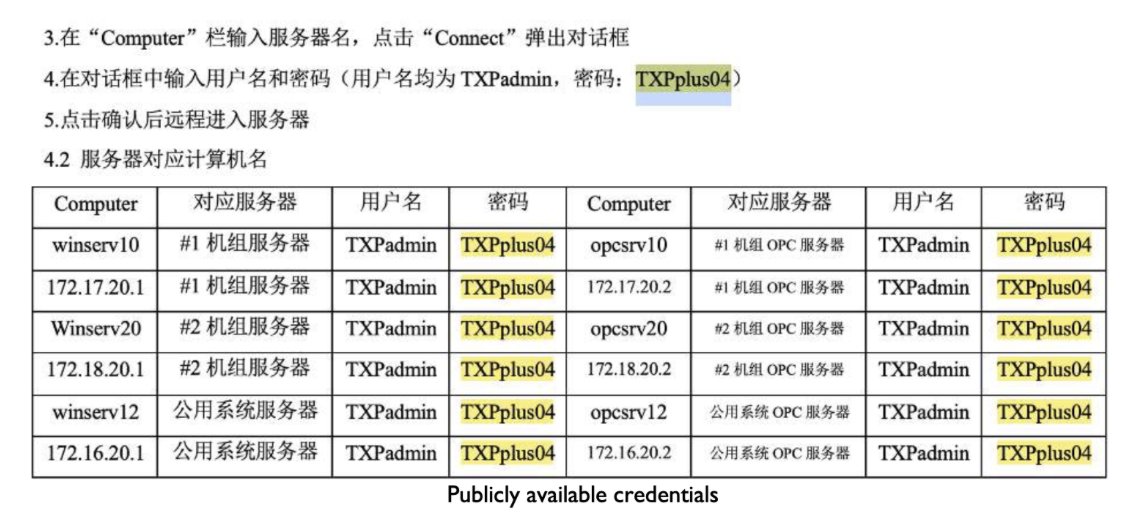
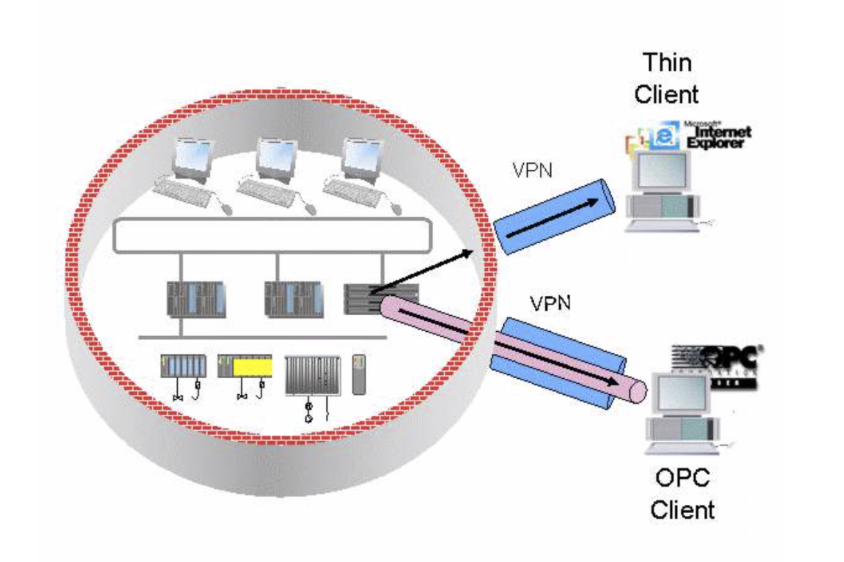
English
Gam4er ری ٹویٹ کیا

A guide on power plant automation and its security issues on #36c3 conference. Slides and tools from our talk github.com/klsecservices/… kudos to @repdet @_moradek_ @Alender911 @epotseluevskaya @zero_wf @574rz
English
Gam4er ری ٹویٹ کیا

Analysts’ predictions on growing corporate threats for 2020 #cloud #insiders github.com/klsecservices/…
English
Gam4er ری ٹویٹ کیا

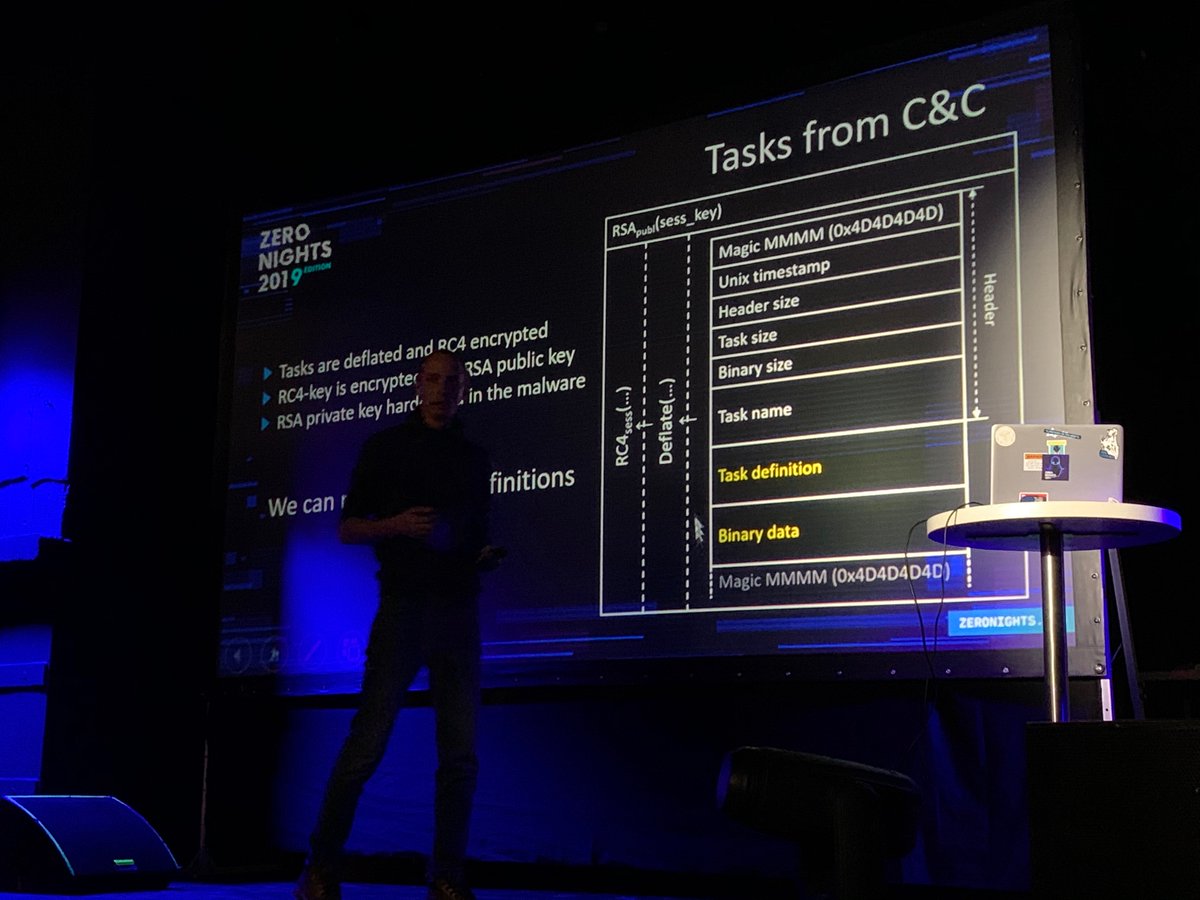
Stories and lessons from Incident Response practice by Pavel Kargapoltsev on #ZeroNights 2019. Thanks for all the questions from audience and organisers for great event! Get the slides
github.com/klsecservices/… ATT&CK inside! #DFIR #blueteam

English

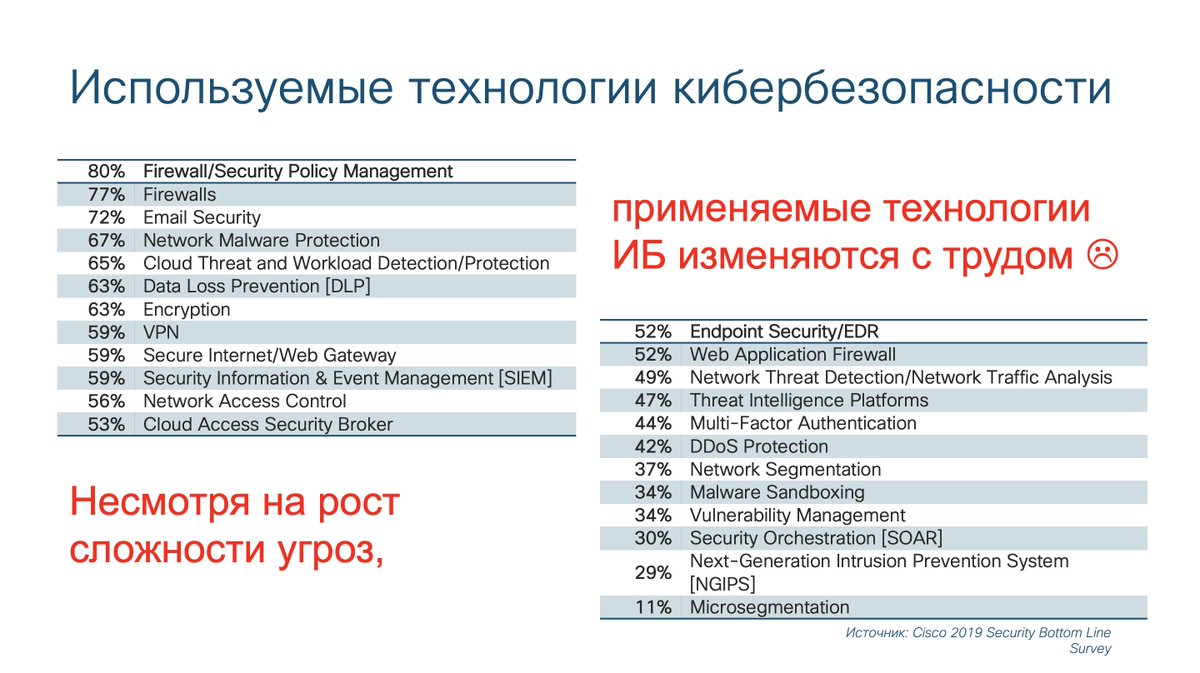
@alukatsky Алексей, а что тогда делать, чтобы новые технологии применялись? Похоже (и к лучшему) тактика "напугать заказчика" не работает ;)
Русский

Обратите внимание на то, какие технологии защиты чаще всего используют компании по всему миру. Эти и другие цифры в новом исследовании Cisco - cisco.com/c/en/us/produc… (скоро и на русском языке)
Русский
Gam4er ری ٹویٹ کیا

Most used #MITRE ATT&CK techniques and more operational security stats in our #threathunting report github.com/klsecservices/…
English

@LasVegasLocally Seems like a part of the Boring Company advertising campaign:
1) Run a lot of nasty insects to LV
2) Give couple flamethrower to good guys
3) Make a good fire show
4) Increase capitalization of the Boring Company five times
как тебе такое @elonmusk ?
GIF
English

@malwrhunterteam Pizdec (пиздец) that word is quite popular at all of exUSSR republics.
Just because almost everything that happens in these areas is "пиздец" :) Other is quite similar like Georgian...
youtu.be/DuZsfaJ46QI
YouTube