پن کیا گیا ٹویٹ

It's crazy to see the dialogue and justification everyone has been using around the banning of speech, protesting and use of force by the police in Sydney.
None of this should even be happening and people can't see that the more cheer for either side's punishment and demise, the more things are going to get worse for everyone.
To be clear, banning protesting is bad, banning speech is bad, calling for the death of anyone is bad and cheering on state driven violence is abhorrent.
If you want to make a difference, get involved with whatever political party you believe will make the difference you want. Don't go out in public and scream death to whatever.
Also, be consistent. You can't, on one hand, cry genocide for one group but ignore genocide perpetrated elsewhere by the people who fund the terrorist organisations that are central to the reason this all kicked off in the first place.
For example you can't be okay with the jailing or deportation of a neo nazi for online posts but then be fine with calling for the death of Israel. This is hypocritical.
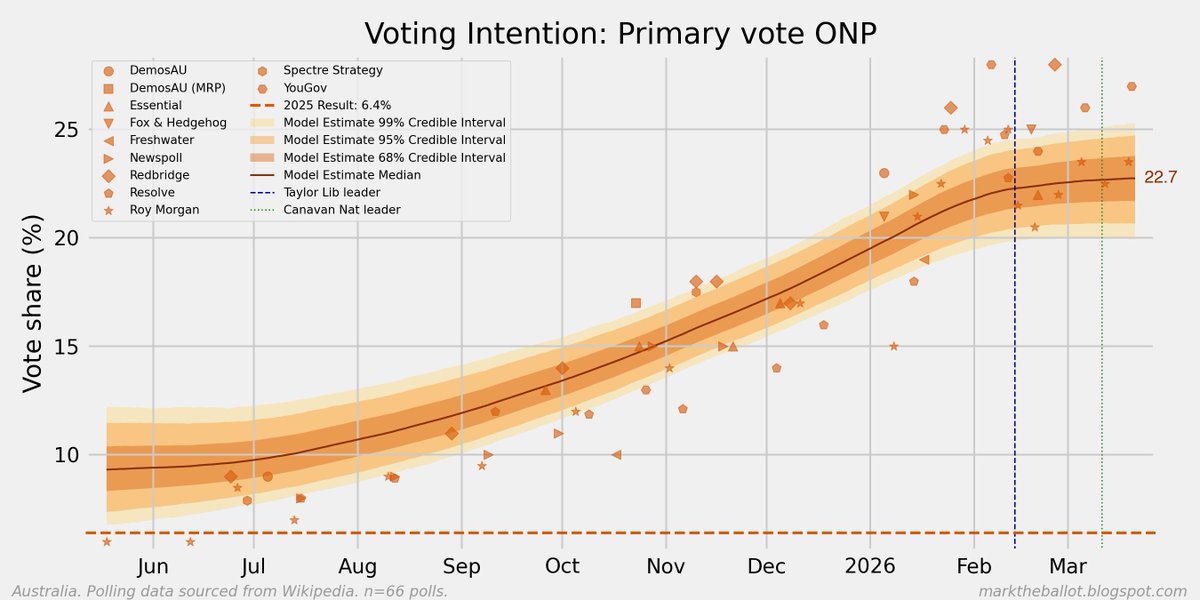
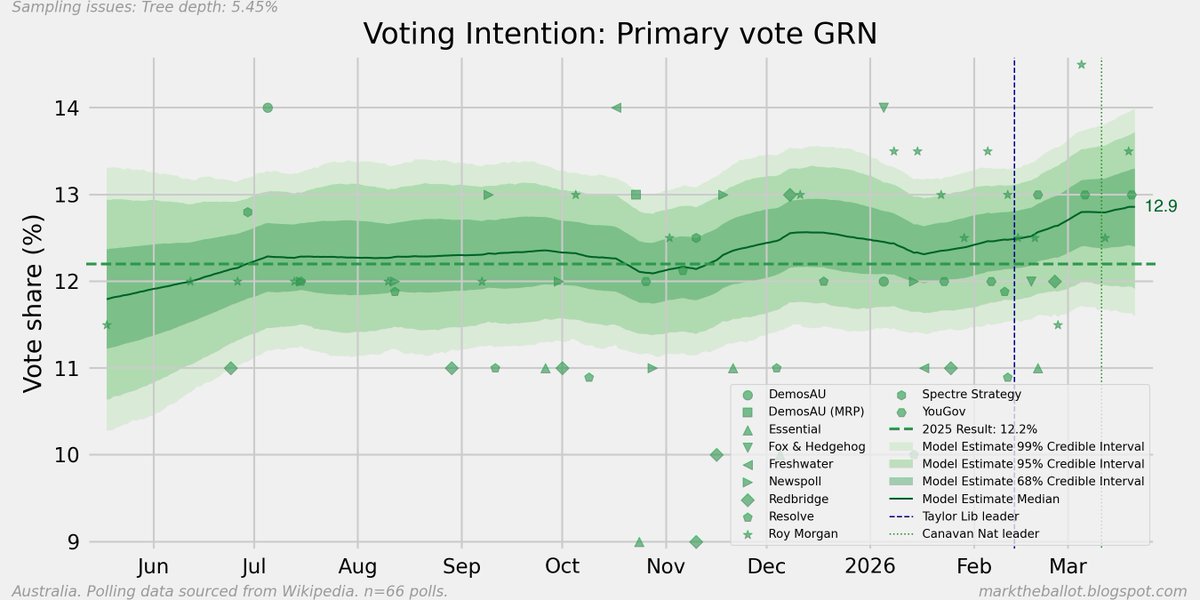
The biggest issues in my opinion are, first and foremost l, Foreign influence in Australian politics. Blatant corruption and lying by politicians, we've been living through the worst reduction in quality of living in decades and they're taking us for a ride. People wailing about problems elsewhere with zero impact on Australians. We've got an ever increasing homeless problem, immigration that is out of control which does nothing except to inflate our housing market and enrich the geronotocracy.
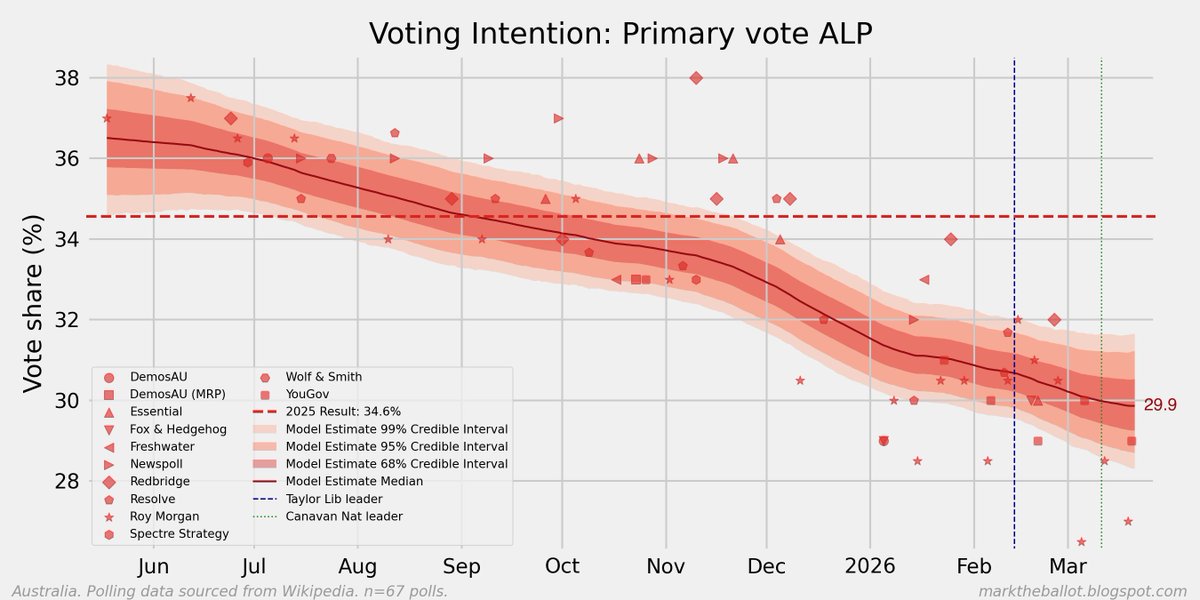
The economic outlook for the short, medium and long term in Australia is the worst it's been for the last 40 years.
Australia's focus needs a reset and redirected to the actual issues that matter for Australians living here. We need a sharp shift back to libertarianism and pluralism. If we don't start to improve things soon we're heading for the same position as the UK is in and much of the EU. We don't have a constitution that embeds individual freedoms like the US does which means it's far easier for us to slide into Authoritarianism. What we are seeing now is not quite there but that's the direction we are heading.
Regan said this in his inaugural address in 1967 and it's as true today as it was then.
"Perhaps you and I have lived too long with this miracle to properly be appreciative. Freedom is a fragile thing and it's never more than one generation away from extinction. It is not ours by way of inheritance; it must be fought for and defended constantly by each generation, for it comes only once to a people. And those in world history who have known freedom and then lost it have never known it again."
Global order is shifting, security isn't a guarantee. We need to look out for Australians first above all, we need to think about how we want to leave this beautiful country of ours for the future generations.
This is all going to take some difficult but honest and pragmatic conversations around what we think we are doing, with a focus on the outcomes because most of the outcomes don't benefit the people we want to help.
Australia first 🇦🇺🐨🦘🪃
English