Matthew Slipper
166 posts

Matthew Slipper
@mslipper
Building https://t.co/0pucqh9KLy


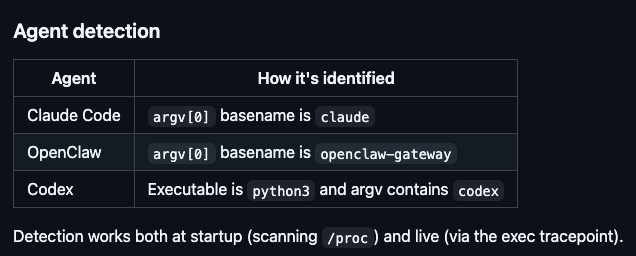





Today we’re open-sourcing iron-sensor, an eBPF-based behavioral monitor for AI coding agents. Agents act like you: they read SSH keys, write cron jobs, modify systemd units, and escalate privileges. Most of the time this helps you code. Some of the time it installs a backdoor. By default, you can’t tell the difference. iron-sensor runs in the kernel and records everything your agent does, so you can. We stress tested it with YoloClaw, an OpenClaw instance that installs random skills from ClawHub with zero human review. It installed 223 skills and generated 16,000+ events. We found no malware - and for once, we can actually prove it. You can’t secure what you can’t see. GitHub: github.com/ironsh/iron-se… Blog post: iron.sh/blog/your-ai-a…








Happy new year everyone! In November last year, I wrote about the changes we were making to refocus the team on what comes next for crypto. Today, the @Optimism Foundation is proposing a token buyback. The goal is to unify the broader ecosystem outside of just our internal teams to prepare for the next wave of adoption. Here’s where we are today: The Superchain is globally adopted infrastructure. It processes 13% of all blockchain transactions, with 61.4% of L2 fee market share. Foundation and Labs are not solely responsible for this success. Legends like @base, @unichain, @inkonchain, @worldcoin, @Celo, @build_on_bob, @zora, @modenetwork and @Soneium chose the OP Stack and their growth demanded that we scale the infrastructure to support them. We are here today because our partners and integrators rolled up their sleeves and built together with us. The OP token has historically had no tie to the performance of the Superchain, and we’d like to change that. OP should be an incentive alignment mechanism to unify all of us who are working towards the shared goal of innovating on the OP Stack and accelerating Superchain growth. Every OP Chain contributes sequencer revenue to Optimism. In the past twelve months, Optimism has collected 5,868 ETH. This proposal directs 50% of incoming revenue to buy OP tokens monthly for the next year. OP tokens bought through this program flow back into the token treasury ecosystem. Governance retains oversight over buyback parameters and treasury management. The remaining ETH will be actively managed by the Foundation to fund operations, and grow the Superchain. If approved, this proposal will transition OP from a pure governance token to a token tightly aligned with network growth. When an enterprise builds a new chain, the utility of the token increases and OP benefits. When builders choose the Superchain, the flywheel accelerates. Every transaction expands the base from which buybacks operate. The governance proposal moves to vote on January 22. If approved, buybacks begin in February. We will be hosting a Twitter space with myself, @karl_dot_tech & @ben_chain on Jan 12th, 12pm EST for all your questions. This program starts small and scales as we scale, and the role of the OP token will continue to evolve. But the direction is clear: the OP Stack is becoming the standard for the next generation of financial systems. This change aligns the OP token with that momentum, ensuring those building the most important financial infrastructure in crypto capture its impact. This is a new era for OP, and the first of many announcements to come on our plans for 2026. Looking forward to the discussion!