Maik Morgenstern
1.3K posts


Maik Morgenstern
@TriggerMeHappy
Doing fun stuff at @reversinglabs now. Reverse Engineer. Former CTO @avtestorg
Germany 加入时间 Nisan 2009
950 关注734 粉丝



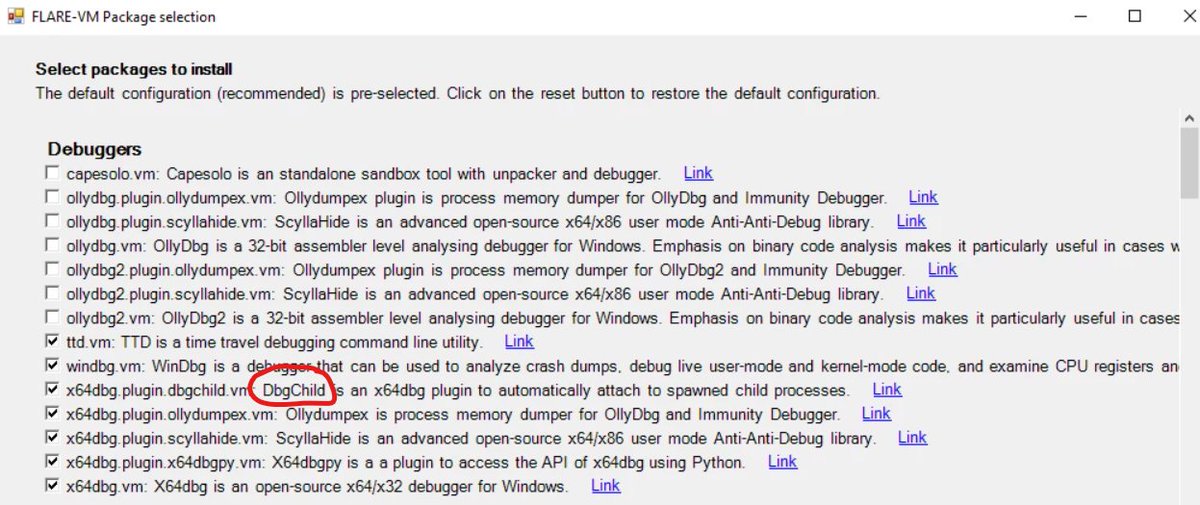
They’ve included my DbgChild in Mandiant’s FLARE-VM security.googlecloudcommunity.com/community-blog…
English

@m_r_tz I just focused on the API call's and ignored most of the actual instructions. That worked surprisingly well
English

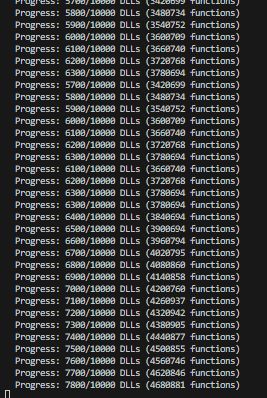
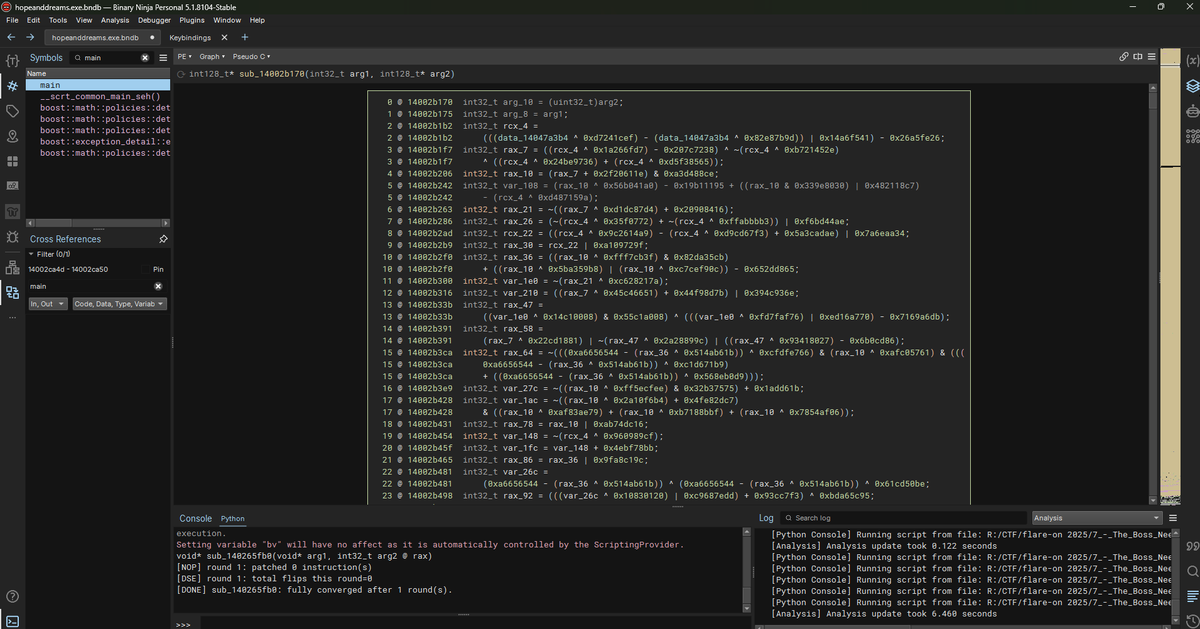
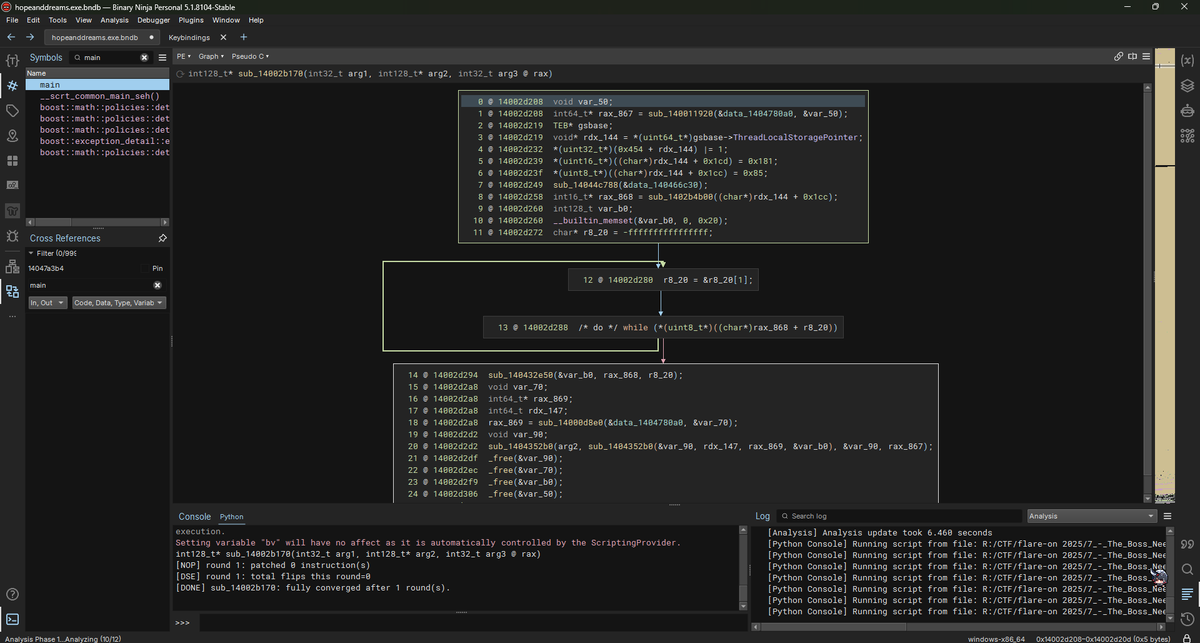
Here's how the obfuscation in #flareon12 challenge 7 looks like in source - all just junk code 🗑️



English

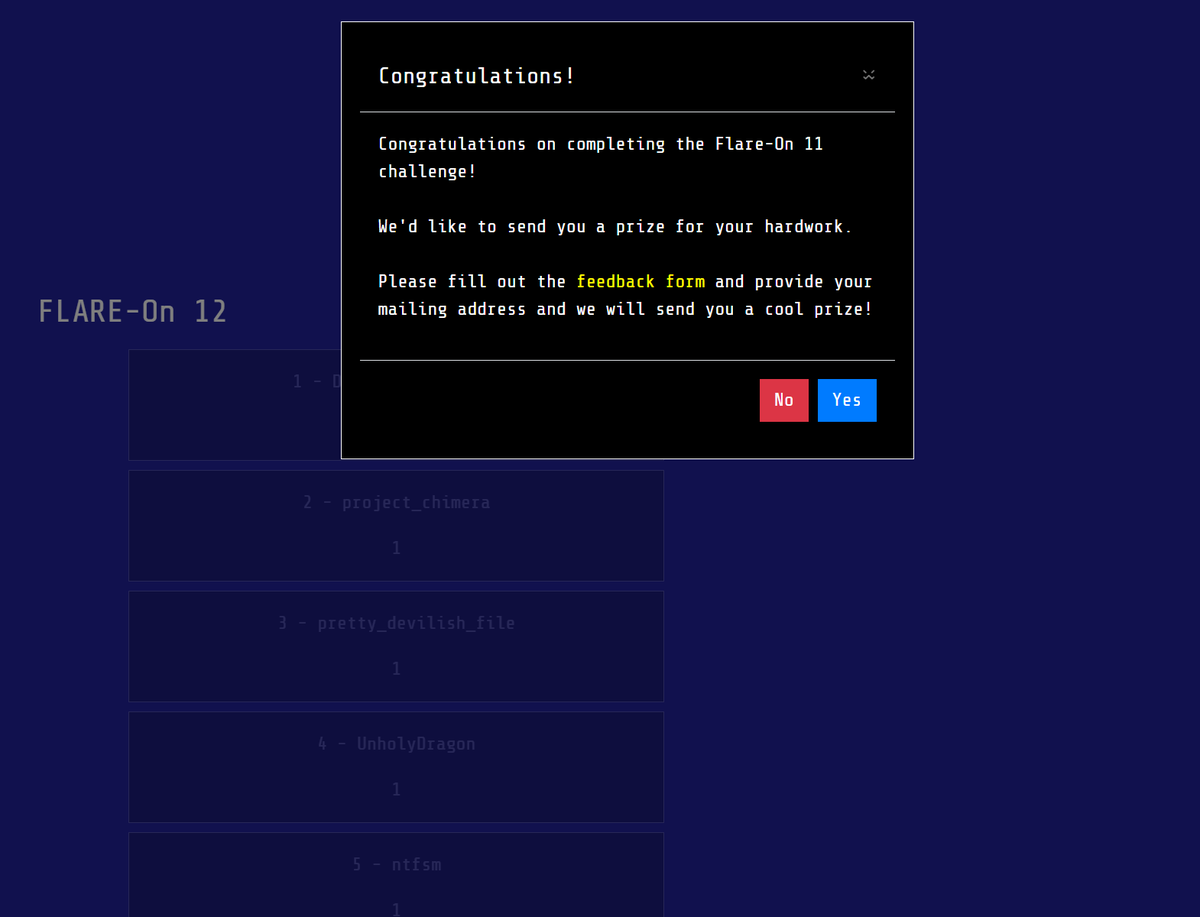
Finally done with #flareon12. The 9th task was quite a ride. I need some tips from those who did the whole thing in less than a week.

English

@ReverseThatApp @Mandiant Grats for finishing so quick 💪
English
Really enjoyed #flareon12 — especially challenges 7, 8, and the brutal but fun final challenge (9). 🧠🔥
Thanks to @Mandiant for another amazing RE CTF.
#CTF #ReverseEngineering #CyberSecurity

English

@TriggerMeHappy @vector35 @x64dbg I still use x64dbg for interactive debugging most of the time but I'm trying to use windbg and the built-in Binja debugger more but when it comes to static analysis I think Binja is king. The API is fantastic.
English

In case you haven't tried it yet: Time-Travel Debugging + @vector35 Binary Ninja integration is such a ridiculously powerful reverse engineering method.
English

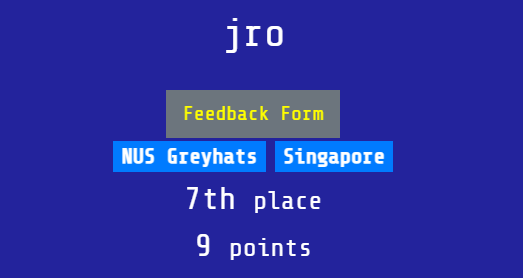
Done with #FlareOn12
An improvement from last year, proud to be representing @HarfangLab.
The maths in #9 really threw me (most people it seems) off. More malware like #7!
Big thanks to @googlecloud, @Mandiant this competition is a great opportunity to improve every year.

English

@x86matthew Good job, pretty fast on 9! Which was really painful 😁
English
finished for 2025! the final challenge was very painful but happy with the result overall 🙃 #flareon12

English

@malware_owl That's what I said as well, I was close to crying once I discovered another layer after having thought I am done 🤣
English
Challenge 7 of #flareon12 has so many junks that I almost cried. Managed to write a deobfuscator for that. Time to solve it for real ...
English

Challenge accepted. Challenge completed. 💪 #FlareOn12
The last one, #9 was brutal, but I made it — 30th out of 2,500+ players! Proud to have represented @ReversingLabs for the first time and placed it high on the scoreboard.
Thanks @Mandiant & @googlecloud for Flare-On 12!

English

@willington1337 Grats, still wondering about ch9 and whether there is a shortcut or not 😁
English

@junr0n Nice, grats! Still struggling with 9 and looking for the shortcut 😁
English

@m_r_tz Open the first four challenges for everyone now, and then open the rest at the scheduled start time =)
English

Timezones are hard, FLARE-On is harder!
Apologies, challengers – #flareon12 had an unintentional early start. To keep things fair for everyone, we are pausing the competition. We're evaluating the situation and will provide an update around 10 AM ET.
English
Maik Morgenstern 已转推

#flareon12 is coming in hot and fast this year and will only run for 4 weeks this year instead of the usual 6. Don't miss it! flare-on.com
English

I don't retweet much but this is big. One of the best RE tools on Windows got even better.
x64dbg@x64dbg
We're excited to announce a major new release of x64dbg! The main new feature is support for bitfields, enums and anonymous types, which allows all types in the Windows SDK to be represented and displayed 🔥
English

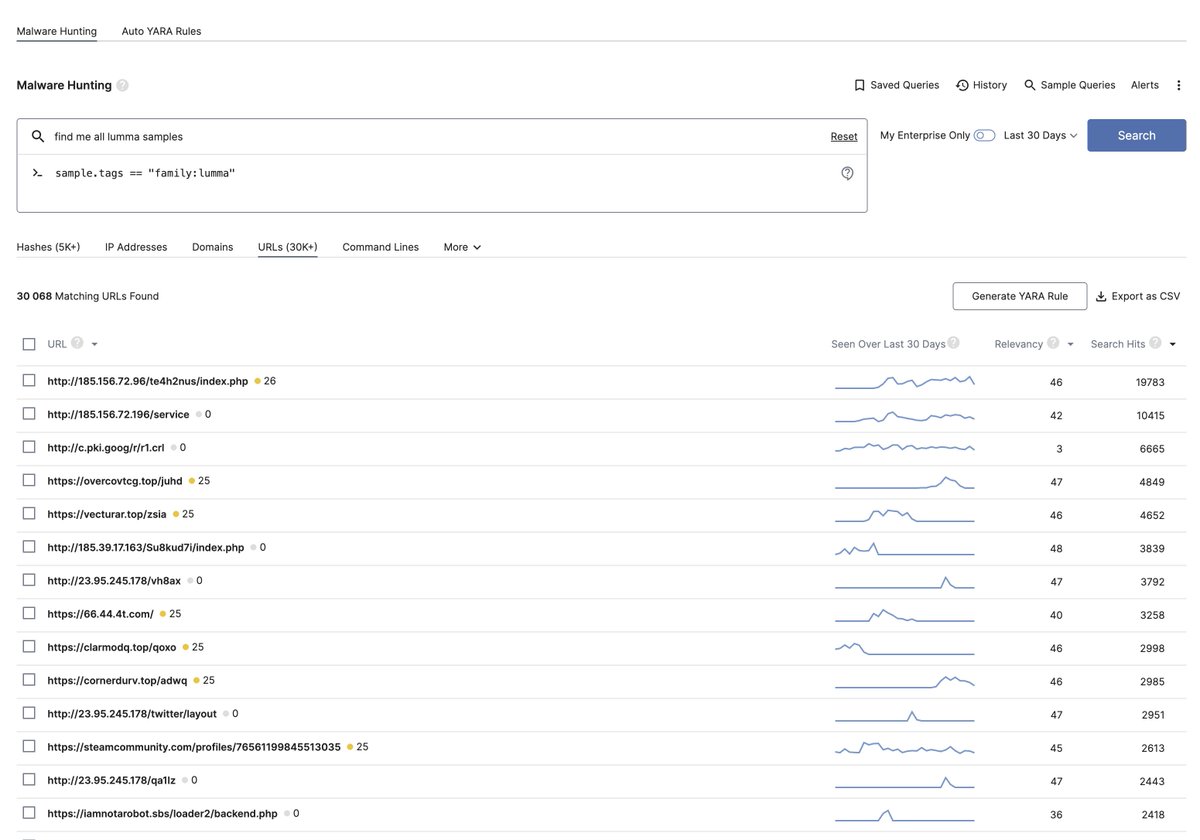
@ddd1ms c.pki.goog ? How did you check for false positives in that list?
English

@cyb3rops Plus a huge clean file repo in the cloud to deal with all the false positives 😁
English