Daniel Púa 已转推

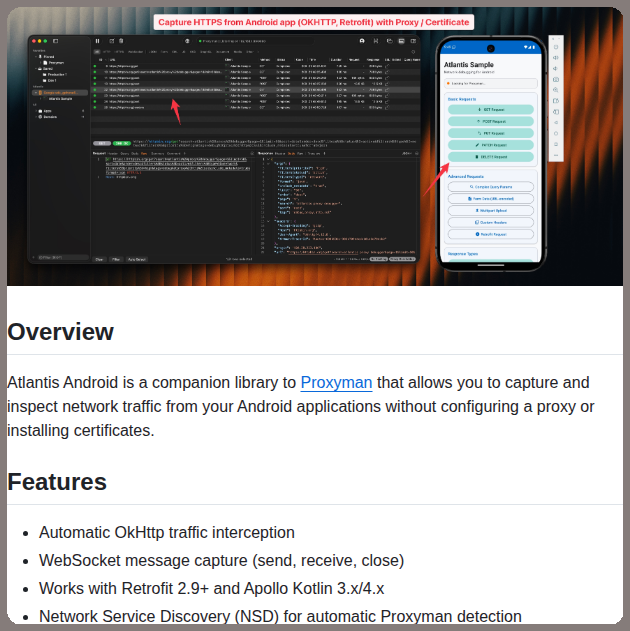
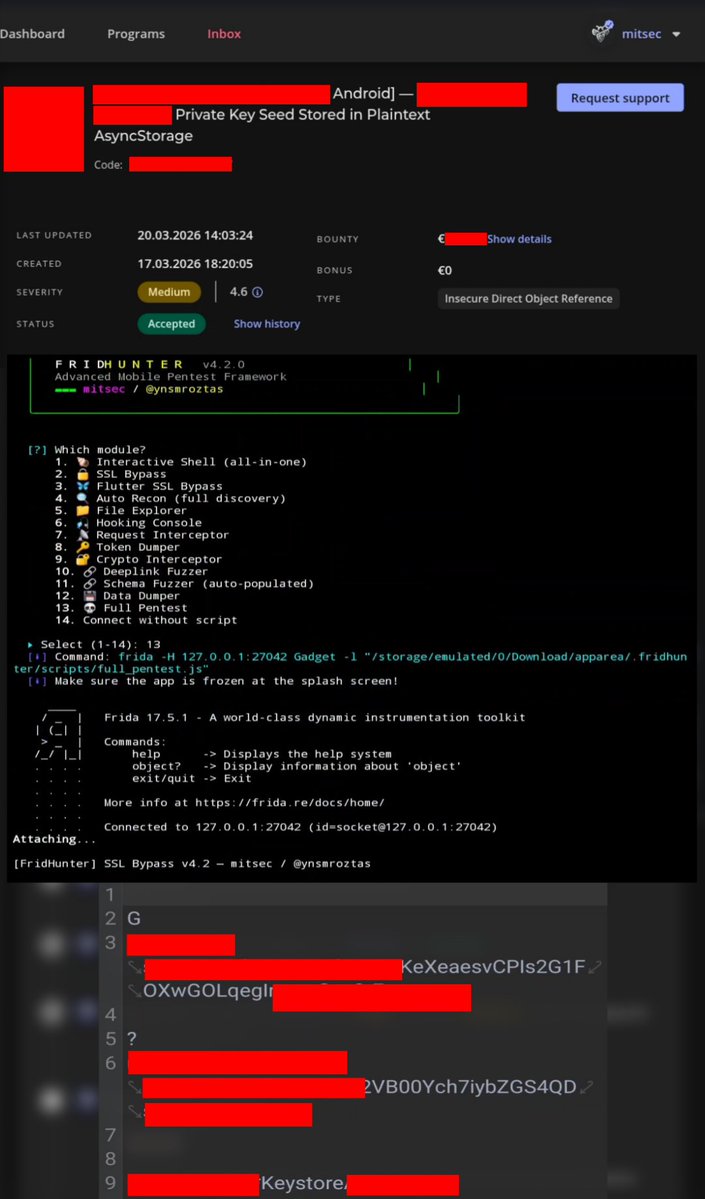
On non-rooted devices, critical data should never be left openly in the `/shared_prefs` file; it should either be moved to a secure area or kept encrypted in a sandbox. Failure to do so can pose serious risks (especially for financial applications). For Android applications, I strongly recommend learning about Frida or hooking techniques.
@intigriti
#bugbountytip #bugbountytips #infosec #recon #android
English