stdnoerr
57 posts

stdnoerr
@stdnoerr
Tech enthusiast | pwner | CTFs with @ARESxCyber
Area 51 加入时间 Haziran 2020
212 关注220 粉丝
stdnoerr 已转推

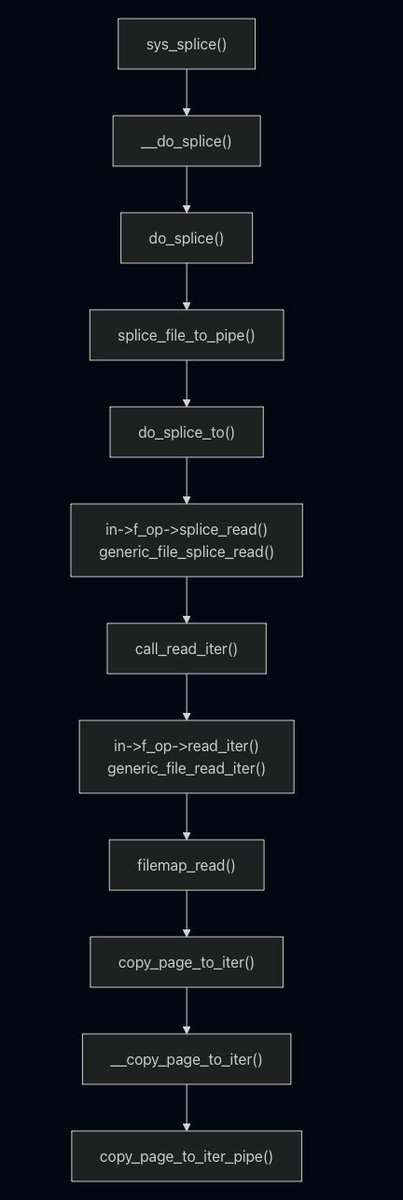
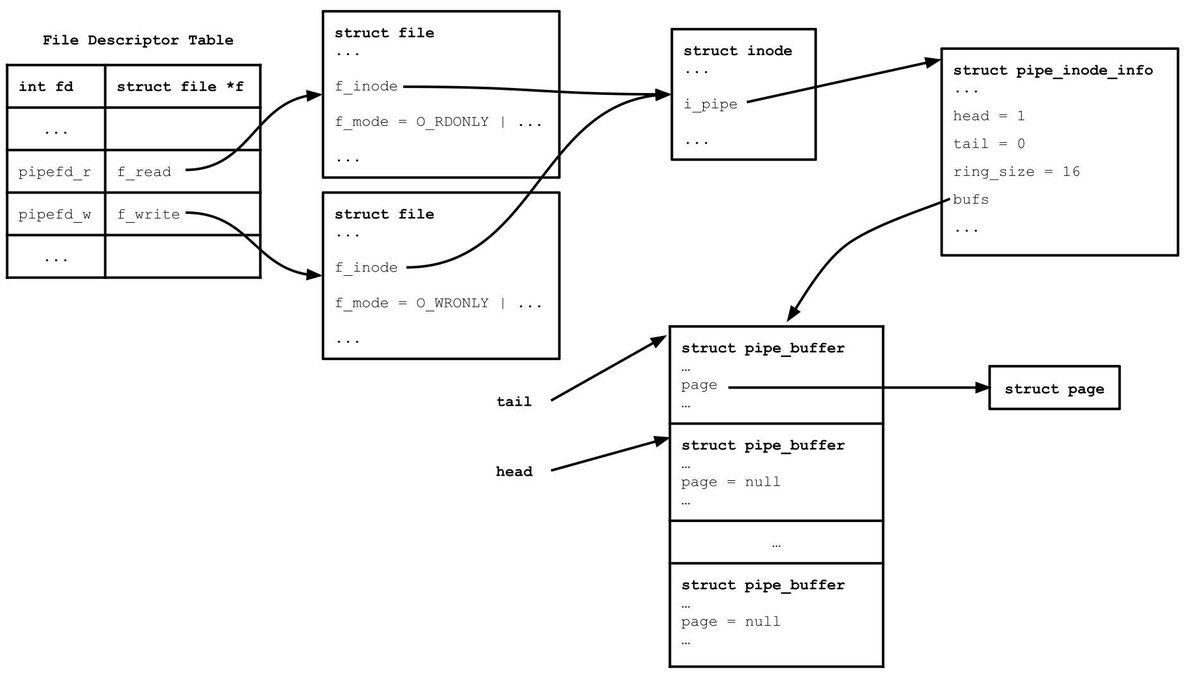
Learning how to exploit DirtyPipe vulnerability in Linux kernel (@0xnull007 and @stdnoerr)
0xnull007.github.io/posts/dirtypip…
stdnoerr.blog/blog/DirtyPipe…
#infosec #Linux
English

In our new article, Maxime Desbrus examines a technique for easily creating a Rust “Two-Face” binary for #Linux:
➡️ in most environments it runs a benign program;
➡️ but on a specific host it launches an entirely different, much more discreet payload.
Read it here 🔗 synacktiv.com/en/publication…
English

@stdnoerr long time no see stdnoerr :)
seeing you here brings back old memories from the discord server lmao
English

@h0mbre_ I don't know if someone mentioned this or not but this blog by @benhawkes addresses this problem by comparing the vulnerability with other similar vulnerabilities and proving them to be members of an "equivalence" class.
blog.isosceles.com/exploit-equiva…
English

played BlackHat 2024 Qualifiers with AirOverflow. Didn't get much time but managed to solve one challenge. Here's the writeup for the one I solved.
P.S. I'm in Riyadh for the Finals. If you're there as well, feel free to hit me up
stdnoerr.github.io/writeup/2023/1…
#BHMEA24
English

Managed third place :) Two months of hard work any many fun challenges !
CSCG@C_S_C_G
The Cyber Security Challenge Germany has concluded! 🥳 Congratulations to all the participants for their hard work and dedication. Special thanks to @equinixmetal for sponsoring the infrastructure. Without further ado, here's the final scoreboard! #CSCG24
English
stdnoerr 已转推
corCTF 2023 has ended🥳- thanks to all the players and our wonderful sponsors! We hope everyone had a great time!
Congrats to the top 5 teams:
1. @Water_Paddler
2. @CyberTeamItaly
3. cat🇰🇷
4. @0rganizers
5. @r3kapig
See you all next year!

English

A quick method to bypass an EDR. Even aggressive EDR's can be bypassed. Allocate your shellcode, overwrite a WNF subscription callback in a userland process, and trigger the WNF state change.. Old but relevant example github.com/ustayready/wnf… follow for more fun soon to come!
English
stdnoerr 已转推

CVE-2022-22629: From WebKit Patch Diffing to PoC github.com/parsdefense/CV…
English

@mistymntncop I need to read it again ig. Sorry if It turns out to be nothing
English

@mistymntncop I found the document.
It is about JSC and I may or may not remember the exact contents I mentioned above since I read this document some time ago (~8-9 months). But the gist is same.
And yeah it is utterly fascinating
iokit.racing/jsctales.pdf
English