HUNTER
3.3K posts

HUNTER
@OX0DAYS
/Future/Billionaire/Hacker/Web2/Web3/Trader/Crypto/Forex/NFT/Maker/SaaS/AI/IT/Services/Provider/


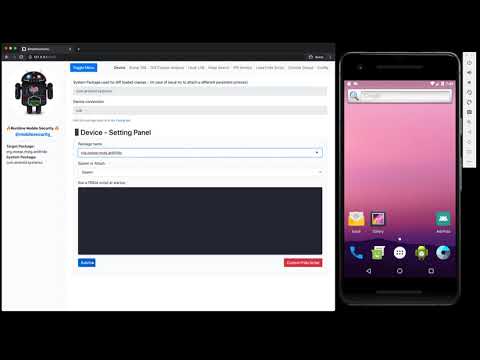









I run Clawdbot on 3 old Android phones. Twitter research. Market monitoring. Telegram chats daily summaries. Private groups signals flashing to my main phone. Running on cheap models like glm-4-flash when ok to save on Claude sub Combined power: same as one Mac Mini. Cost: $0 total. That old phone in your drawer? Turn it into a 24/7 AI server: Download Termux from F-Droid. Run: pkg install nodejs-lts git npm install -g clawdbot clawdbot gateway start Remote access from your computer or main phone. Deploy skills. Cron jobs. Telegram bot. Code. 3-5W per device. Built-in UPS lmao! 🔥 Don't have one? Buy Redmi Note 10 Pro ($60). Pixel 4a ($80). Galaxy A52 ($100). Mac Mini energy. Junk drawer budget. VPS companies hate this setup too.