Angehefteter Tweet
247CTF
1.5K posts


247CTF
@247CTF
🏆 The 247CTF continuous security competition 📺 YouTube for CTF fundamentals https://t.co/0RP7w5pej2 🏁 https://t.co/FATXT1bqrW for CTF challenges
Australia Beigetreten Nisan 2019
88 Folgt5.4K Follower
247CTF retweetet

During a recent Active Directory intrusion test, @croco_byte was led to devise a new versatile attack vector targeting Group Policy Objects, allowing their exploitation through NTLM relaying.
synacktiv.com/publications/g…
English
247CTF retweetet

Bypassing Windows Defender and PPL Protection to Dump LSASS tacticaladversary.io/adversary-tact… #redteam
English
247CTF retweetet

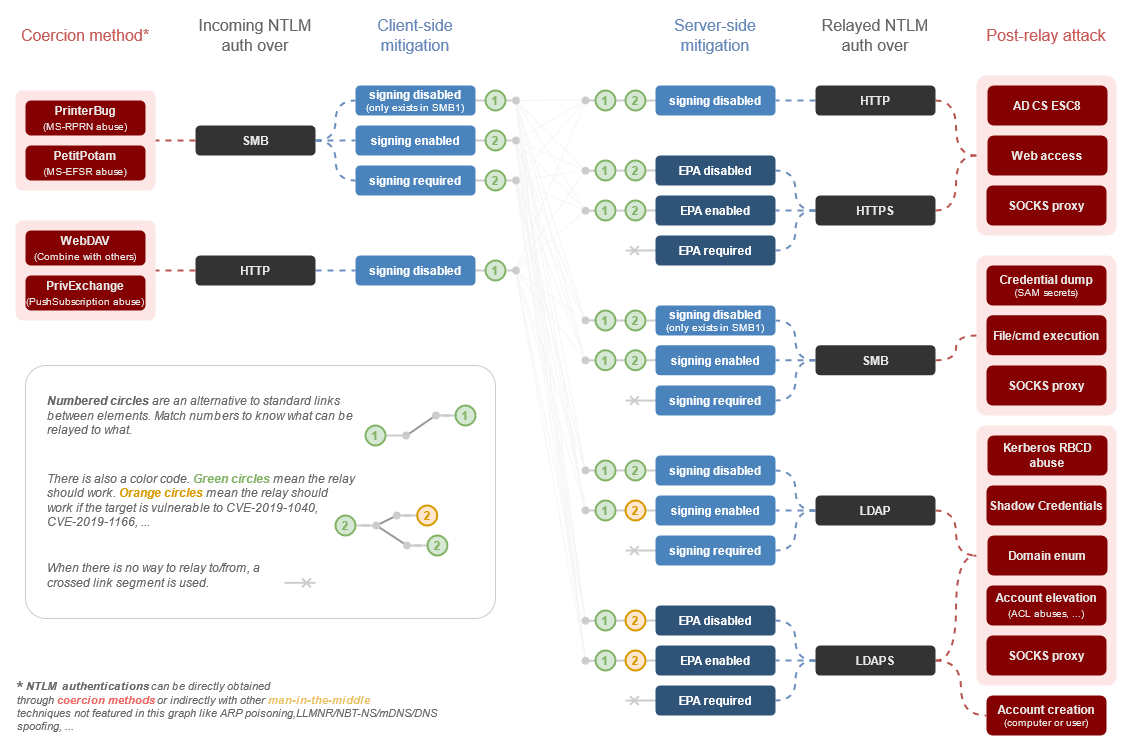
Here is a first draft on an NTLM relay mindmap 🙂 from authentication coercion to post-relay exploitation. I'll gladly update/correct it if you think there are things wrong or missing.
➡️Featured on The Hacker Recipes thehacker.recipes/ad-ds/movement…
English
247CTF retweetet

[BLOG]
Ok, I've written about my experience of battling with both managed and unmanaged memory allocations to try and improve @FuzzySec's Melkor POC.
rastamouse.me/building-a-sli…
Rasta Mouse@_RastaMouse
@domchell 💯 I thought of doing a blog post showing ways to minimise or clear heap memory allocations in your C# tooling, kinda like programming OPSEC tips that don’t rely of the GC. Not sure how useful it would be though.
English
247CTF retweetet

EDRSandblast-GodFault: a tool written in C that weaponize a vulnerable signed driver to bypass EDR detections (Notify Routine callbacks, Object Callbacks and ETW TI provider) and LSASS protections github.com/gabriellandau/…
English
247CTF retweetet

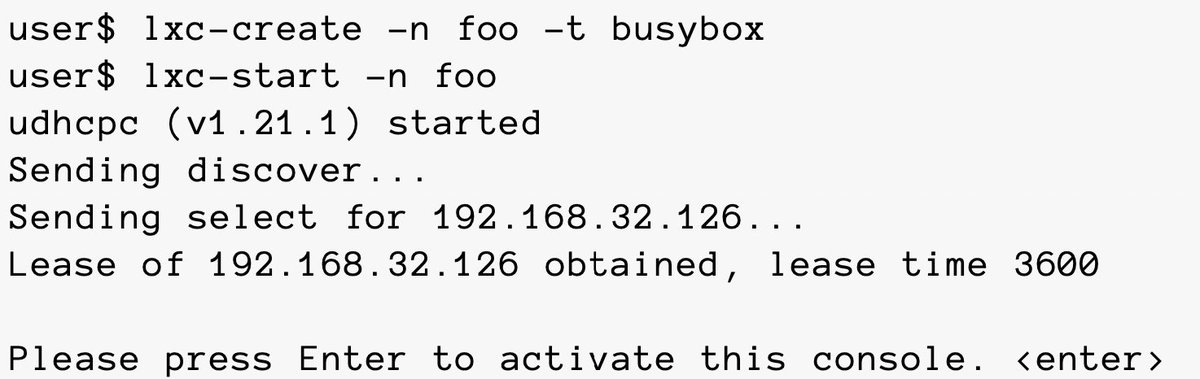
A few years old but a very well written white paper on Linux containers
Credits @NCCGroupplc
research.nccgroup.com/wp-content/upl…
#Linux #containers #infosec


English
247CTF retweetet
I just published Home Grown Red Team: SMB Pivots With Havoc C2 link.medium.com/Ap3Xk0HKjCb
An updated article for lateral movement with Havoc.
English
247CTF retweetet

SUCH a good read. I love the section where they explicitly explain the process used to write custom shellcode for OpenBSD. Even for a noob to Binary Exploitation that was so easy to follow and really emboldening to go after these sort of bugs.
Bravo!
blog.assetnote.io/2023/08/09/exp…
English
247CTF retweetet

Excited to share my new research: a POC of a new “threadless” process injection technique that works by utilizing the concept of DLL Notification Callbacks in local/remote processes.
github.com/ShorSec/DllNot…
An accompanying blog post with more details:
shorsec.io/blog/dll-notif…
ShorSec Cyber Security@ShorSecLtd
We are excited to share a new "threadless" process injection technique by @dec0ne. This new technique utilizes DLL Notification Callbacks in the remote process to trigger the shellcode github.com/ShorSec/DllNot… Detailed blog post: shorsec.io/blog/dll-notif… Demo video in next tweet
English
247CTF retweetet

@tifkin_ , @0xdab0 , and I are very proud to announce that the alpha release of Nemesis is now public! The code is at github.com/SpecterOps/Nem… and we have a post explaining details at posts.specterops.io/hacking-with-y… 1/3
English
247CTF retweetet

. @samwcyo's write ups not only contain a 👌 amount of technical details, but also tell a story and describe the mentality required to find these internet breaking bugs.
Also, note the verbiage surrounding "interesting" or "curious". Essential.
Must read:
samcurry.net/points-com/
English
247CTF retweetet

When making the vulnerable #AWS environment CloudFoxable, @sethsec drew inspo from #security tools like #CloudGoat, flaws.cloud, and #Metasploitable. CloudFoxable provides flags and #attackpaths in a CTF format.
Check out the #challenges! bfx.social/3X6diwX

English
247CTF retweetet

It's only a service principal. cyberdom.blog/2023/07/29/per…
English
247CTF retweetet

Abusing DLLs with RWX sections to fulfill memory allocation primitive and achieve code injection in a local and remote process.
Post by Thiago Peixoto, Felipe Duarte and Ido Naor of @SecurityJoes.
#redteam
securityjoes.com/post/process-m…
English
247CTF retweetet

Continuing their journey through offensive data, @harmj0y, @tifkin_, and @0xdab0 break down some common challenges in post-exploitation work flows. ghst.ly/45d5oF3
English
247CTF retweetet

Me and @Her0_IT did a fair bit of research against one of the leading EDRs in the sector. This first post will hopefully be the start of a long saga, documenting all of our findings.
This first part was dated back in 2020:
riccardoancarani.github.io/2023-08-03-att…
English
247CTF retweetet

Published a write-up on successfully phishing a target using AD FS with MFA. Covers some of the challenges and how I finally got it working 🎣
research.aurainfosec.io/pentest/hook-l…
English
247CTF retweetet

Backdooring ClickOnce .NET for Initial Access: A Practical Example by @an0n_r0 infosecwriteups.com/backdooring-cl…
English
247CTF retweetet

New DLL hijacking opportunities, triggered using DCOM for lateral movement: github.com/WKL-Sec/dcomhi…
English