
Kse Proso
260 posts


@KseProso
#APT groups analyst #ThreatIntel researcher @GroupIB @GroupIB_TI Opinions are my own.









Group-IB’s Threat Intelligence team has investigated the work of the #Lynx #Ransomware group, unveiling multi-architecture builds (Windows, Linux, ESXi). Their affiliate panel centralizes attack orchestration and data-leak scheduling. #RaaS #CyberSecurity


#Lazarus has attempted to evade detection on #macOS systems using a new technique - code smuggling using extended attributes

The #Lazarus Group shows no signs of easing with their campaign targeting #jobseekers extending to the present day. Group-IB researchers found new updates to their tools and tactic - new suite of Python scripts - #CivetQ, a #Windows and #Python version of #BeaverTail


Group-IB researchers noticed a Windows version of #BeaverTail, which was attributed to #Lazarus. We also discovered that the #javascript version of BeaverTail is now being distributed through trojanised games built with ReactJS and distributed as an NPM-based package.

Thanks to #ESET for an in-depth overview of activity in the first half of 2024. In our research, we found that impersonations of Ethiopian, South African, Peruvian and Mexican applications are related to #Gigabud. Check out ESET’s post for more details: x.com/ESETresearch/s…

Discover the latest on #Boolka, a #cyberthreat actor responsible for spreading #malware and stealing data through #webattacks. Learn about Boolka's methods and how we're fighting back. #InfoSec #CyberSecurity Read More : bit.ly/3RDYB2H

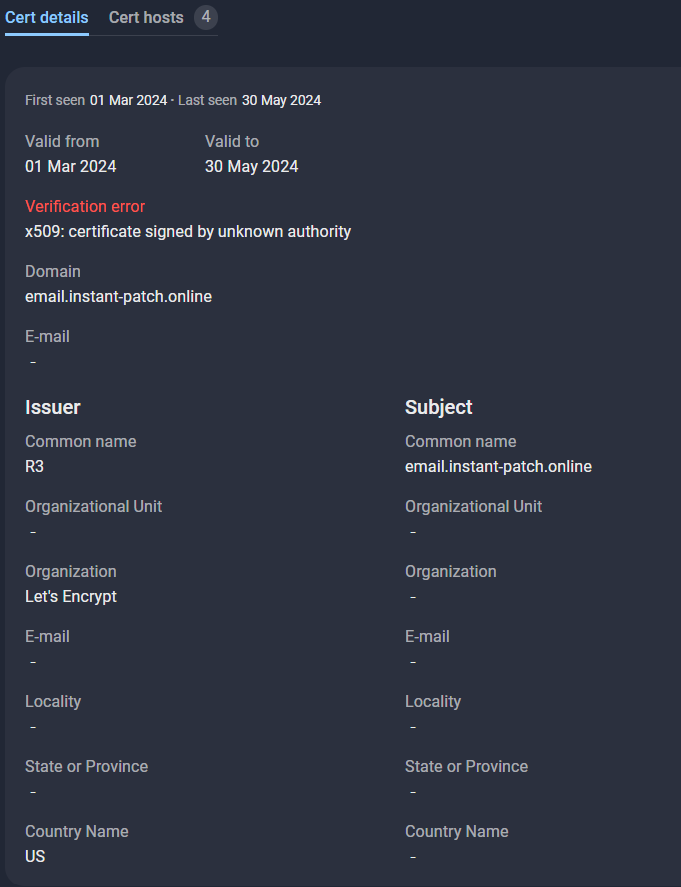

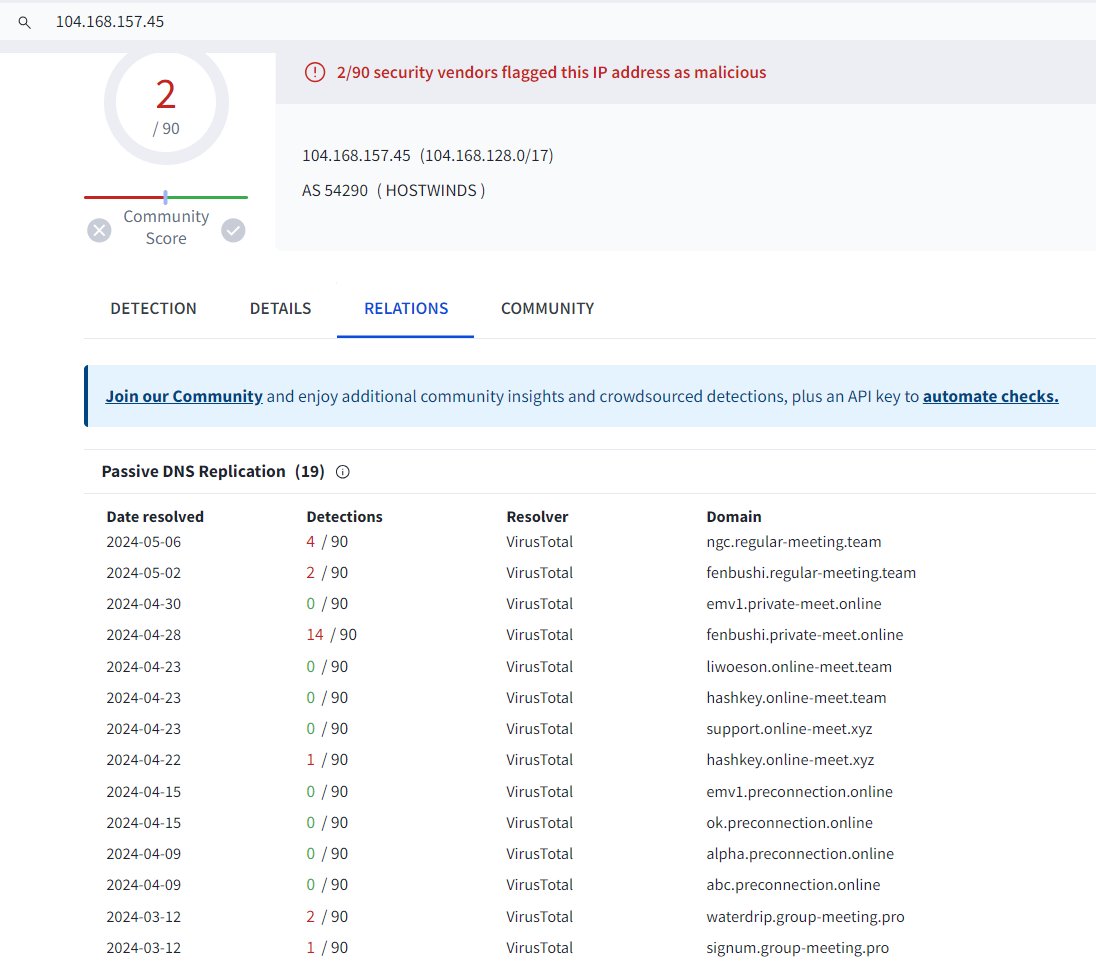

new phishing scam just dropped the scammer impersonates a VC and insists to use a phishing link for the call


Following Group-IB's #GoldFactory report, it is clear that situation of mobile threats in #APAC persists. Though the report shared mainly on the "Gold-prefixed" trojans, the prevalence of #Gigabud in the region is not to be overlooked. There are increased sightings of Gigabud, especially in #Vietnam since late 2023 till present.

🕵️♀️ Exposing the #DarkWeb deception. Since October 2022, the #ThreatActor known as "resetmyname" has been falsely advertising "unique customer databases" from numerous #banks on various Dark Web platforms. Regularly announcing "new bank customer databases" from many countries around the world, this activity has garnered significant media attention over time. @GroupIB's thorough analysis of all data samples that "resetmyname" has ever published or provided reveals that, in fact, TA has been selling data all this time from the publicly available database of the #BidenCash cardshop, which the cardshop itself published for promotional purposes back in June 2022. Detailed reports about "resetmyname" and "BidenCash" are available for Group-IB customers.


🚨 As promised, here's the full disclosure — Group-IB's TI unit uncovers #ResumeLooters, a malicious group targeting primarily #APAC's employment agencies & #retail firms. Read our blog for their tactics, #IoCs, and how to shield against #SQL injection and #XSS attacks: bit.ly/3SvCefp #Cybersecurity