Sabitlenmiş Tweet

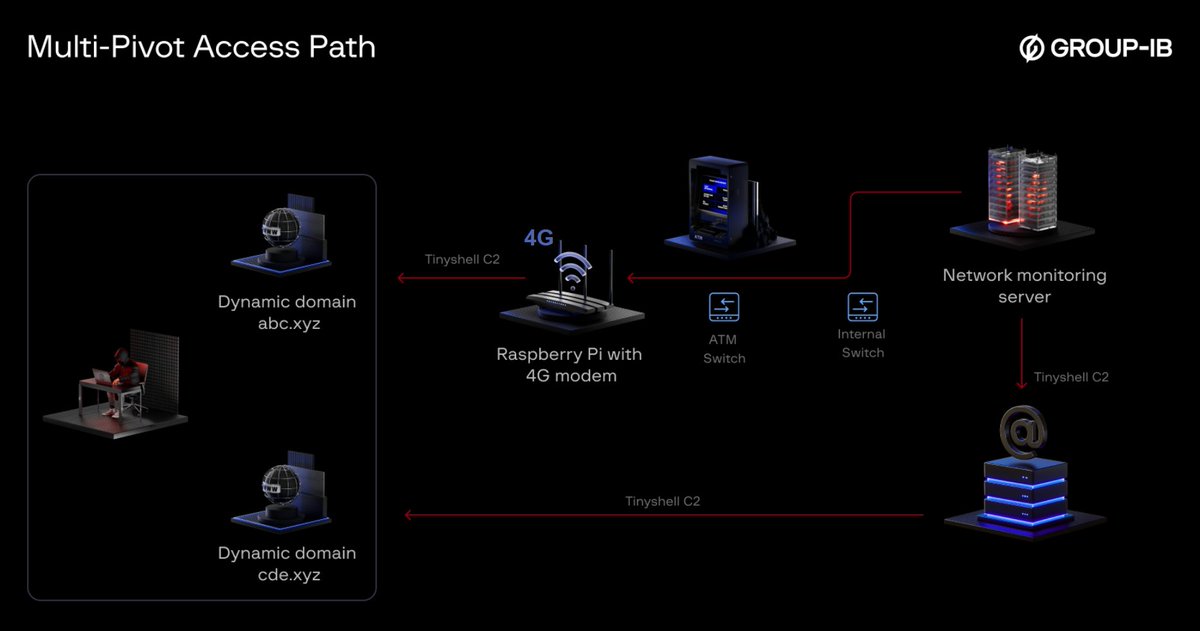
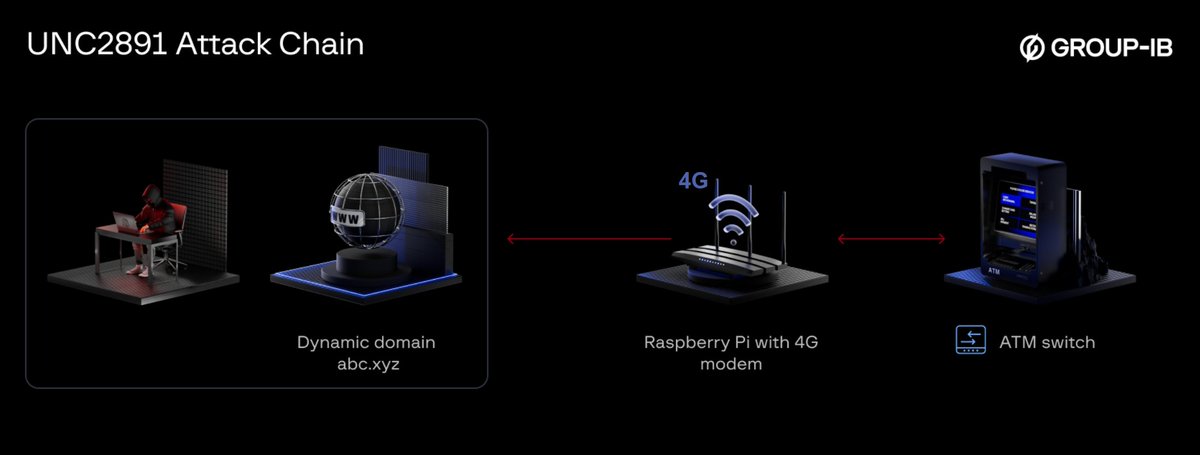
Group-IB is the first to uncover a real-world bank heist where threat actor #UNC2891 used a 4G-enabled Raspberry Pi to create physical access to breach the bank’s ATM infrastructure, evading defenses with stealth #Linux backdoors. #ThreatIntel
English