CodeX
962 posts


CodeX
@codex_tf2
advanced persistent clown 🤡 📕 redteam blog: https://t.co/ihAv2kFvUj 🛠️ github: https://t.co/VhmOUAVF3R opinions are my own
explorer.exe Beigetreten Şubat 2022
216 Folgt2K Follower
Angehefteter Tweet

[Pin] My maldev link dump if anyone else wants to read :D (Will be updated)
raw.githubusercontent.com/CodeXTF2/malde…
English


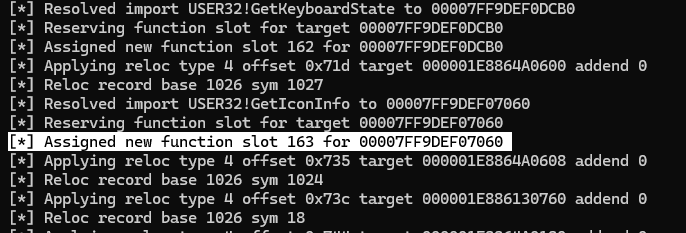
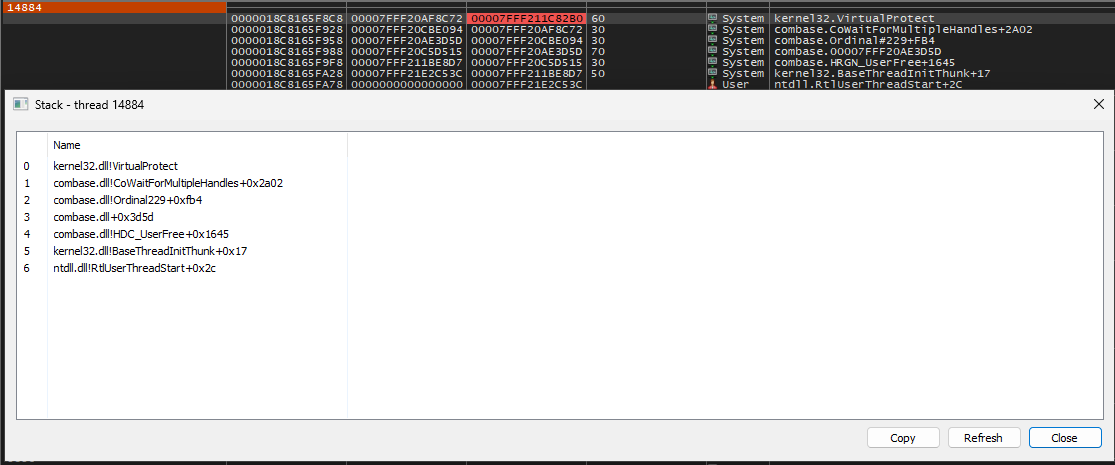
@vxunderground But here is a VirtualProtect call that was made via timer call / fiber switch shown in both x64dbg and and process hacker. After the call completes this all unwinds through gadgets to ultimately switch fiber back to the original timer fiber which will unwind + pick up next task
English

I am now the proud owner of a version of Ekko that:
- Uses threadpool timers
- Conceals use of timers from the call stack
- Does not use NtContinue/Ex
I've learned that if you believe hard enough and use a shitload of ROP anything is possible.
Octoberfest7@Octoberfest73
@jamieantisocial This is finally motivating me to take a look at fibers again. I could be wrong, haven’t explored fully yet, but I’m pretty sure I see a path forward to use fibers with Ekko and eliminate its use of NtContinue
English

Open source port/reimplementation of the Cobalt Strike BOF Loader as is. This includes issues not present in other open source COFF loaders. The goal of this project is to make an analog of the specific implementation in Cobalt Strike for debugging
github.com/CodeXTF2/Cobal…
English
CodeX retweetet

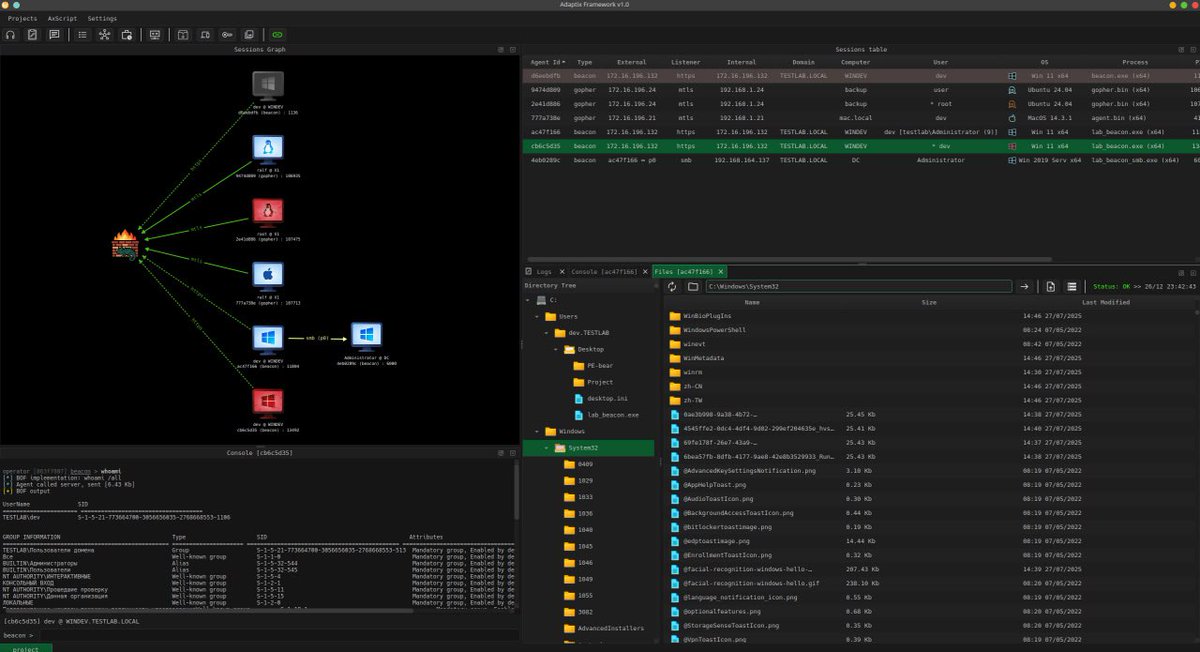
AdaptixC2 v1.1 is out!
* New DNS/DoH beacon listener
* New extenders type - service
* New BOFs in Extension-Kit
* Added Events/Hooks manager
Full update info: #login-subscriptions" target="_blank" rel="nofollow noopener">adaptix-framework.gitbook.io/adaptix-framew…
English

apparently the windows exe stats page echotrail.io now points to some coworking space service using the same logo as the original - wtf?
English

Made an open source library to implement Malleable C2 profile support for HTTP based C2s. Its not perfect code 😭 but hopefully more C2s start supporting more HTTP traffic customization depth.
All malleable transforms in http block supported :D
github.com/CodeXTF2/OpenM…
English
CodeX retweetet

Because “stare at Burp responses until something looks weird” isn’t a strategy 👀 @hoodoer introduces Colonel Clustered, a new Burp Suite extension that automatically groups responses by content to surface subtle outliers during web app testing. Read now! hubs.la/Q03_v-r30
English
CodeX retweetet

Weakpass version 4 was released sometime the last months, best for your password cracking needs:
weakpass.com
🔥
English
CodeX retweetet

Learn how BHIS identified a highly stealthy and persistent intrusion technique enabling a threat actor to sustain command-and-control (C2) within a client’s environment.
Read more: blackhillsinfosec.com/the-curious-ca…
The Curious Case of the Comburglar
by: @wojeblaze
Published: 12/18/2025
English
CodeX retweetet

New MSSQLHound updates from @_Mayyhem 🔥
Now includes EPA-based NTLM relay scanning, CVE-2025-49758 patch detection, and BloodHound Cypher queries to map + remediate MSSQL attack paths.
Check it out! ghst.ly/4pKTgVI
English
CodeX retweetet

[New @originhq blog+POC]
No PPL? No problem!
SecurityTrace, an undocumented ETW feature, restricts some AutoLogger traces to PPL only — yet we found this current design still allows non-PPL processes to consume from Threat-Intelligence as admin only!
originhq.com/blog/securityt…
English
CodeX retweetet
CodeX retweetet

I've been receiving messages from both Lockbit ransomware group and ALPHV ransomware group for months.
I've been so preoccupied with my newborn son I thought it was an imposter.
They've been trying to tell me stuff, and I just kept sending cat pictures. They eventually gave up and started replying with pictures of cats too.
¯\_(ツ)_/¯
English
CodeX retweetet

Use the known vulnerable but not blocklisted Topaz Antifraud kernel driver to kill EDR.
By sharing this am I contributing to getting the driver blocklisted?
From @DharaniSanjaiy
github.com/ThanniKudam/To…
English
Last week we acquired UK-based DeceptIQ.
DeceptIQ (@deceptiq_) is built by red-teamers with a deep desire to turn the tables on attackers. In our ten years of doing Canary, we’ve never seen such a strong natural alignment.
We are super excited to help defenders win, together.
GIF
English
CodeX retweetet
CodeX retweetet

there is also this list i have saved a while ago where the diff between wininet and winhttp is explained:
wininet + proxy -> needs a valid domain user’s token.
wininet + SYSTEM -> Bad
wininet + service -> bad
wininet -> harder to implement verification
wininet -> socks4
winhttp + service -> good
winhttp + system -> good
winhttp + proxy -> HTTP/1.0 proxy issues
winhttp -> impersonation support
winhttp -> supports kerberos ?
Sources:
- learn.microsoft.com/en-us/windows/…
- cobaltstrike.com/blog/talk-to-y…
- docs.metasploit.com/docs/using-met…
- learn.microsoft.com/en-us/windows/…
- learn.microsoft.com/en-us/windows/…
English