Pinned Tweet

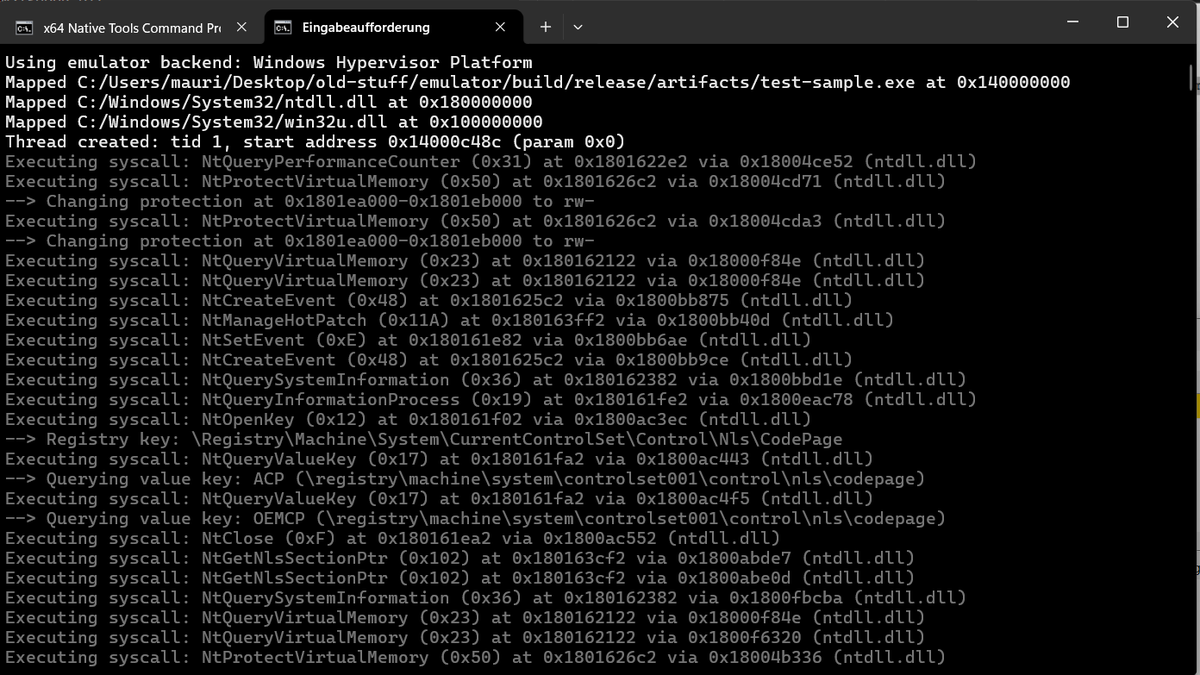
While researching @kaspersky's components, I've decided to write a fun project that makes possible hooking system calls from your own driver by interfacing with its hypervisor: github.com/iPower/Kaspers…
English
iPower
547 posts


@iPowerPower
Just a guy who likes anime, fighting games, hypervisors and reverse engineering. Member of @the_secret_club. Do not DM me about game cheats.









Intel VT-rp community.intel.com/t5/Blogs/Tech-…