Sunny
77 posts

BSides Goa Phrase Challenge - Win a T-shirt! 🎉
Hey BSides Goa Community! 👋
Ready for a challenge?
Complete the phrase: 'The first rule of BSides Goa is...........'
In the most creative way and stand a chance to win a BSides Goa T-shirt! 🧠💬
How to Participate:
👍 Follow @bsidesgoa , like and repost the tweet.
🤔 Complete the phrase with your unique twist.
💬 Comment your phrase below or post it on Twitter/Instagram using #BSidesPhraseChallenge.
🏷 Don't forget to tag us!
Prize: 👕 The best phrase will win a BSidesGoa T-shirt! 🎁👏
Deadline: 12/12/2023⏰
Unleash your creativity, and let the phrase magic begin! Good luck! 🚀📜
#Bsidesgoa #Giveaway #tshirt #challenge #CyberSecurity #infosec #BugBounty #Hacking #bsides

English

Some more good reviews on my latest "The Art of Web Reconnaissance Course"♥
If you also want to learn Basics-Advance web recon techniques then get my course for 90% discount
Coupon: 8B5894BFA5BB5CD00C1F
Link: udemy.com/course/the-art…
English

@hack1or0 @ramirezVII @ReconOne_bk example
reaponse json :
{"email":false}
you change it to true in http response ans you may be able more features without verify email
English

Broken Access control trick.
If the server responds with a JSON containing roles and functions expected for the user, try modifying that JSON. You may be able to access unexpected features.
#pentesting #owasp #accessControl
English

My work has sponsored TWO more tickets to tbhmlive.com . Follow @BuddoBot from now until beginning of next week to enter in a 2nd chance for a free ticket!
English
Sunny retuiteado

Ok fam. I’m giving away TWO free tickets to my course which takes place in two/three weeks.
All you have to do to win is like, retweet this tweet, and reply with “tbhmlive.com!”
I’ll pick winners next week!
If you haven’t seen my course, check out the link!
English

@jayesh25 Nice one @jayesh25 !
Bombon has some pretty good blogs about these kinds of bugs here if anyone is interested.
bxmbn.medium.com/how-i-test-for…
bxmbn.medium.com/chaining-cache…
English

🔐 Show & Tell: Uncovering a Simple Web Cache Deception Vulnerability That Paid Off 💰💰
Cache Deception issues might seem complex, but with the right approach, they're straightforward and can lead to generous rewards, ranging from $1,000 to $10,000, depending on the impact.
Today, I'll share how I discovered a basic web cache deception issue that allowed me to access users' PII data through caching, resulting in a "High" payout.
Here's my step-by-step approach:
1️⃣Got Invited to a private program - My first move was to inspect the Request/Response headers for common misconfigurations. I immediately spotted common cache headers like Server-Timing, CF-Cache-Status, X-Cache, X-CDN, etc.
2️⃣Identifying interesting cache headers - Once I pinpointed these headers, the next step involved analyzing the application's behavior. I sent sample endpoints/APIs to Repeater and appended tricky paths to the URIs. For example, if the path "https://target(.)com/api/v1/users" returned sensitive PII, I tried appending variations like "https://target(.)com/api/v1/users/self.css" and "https://target(.)com/api/v1/users/self/.js" to observe if there was a cacheable response.
3️⃣A straightforward cache issue - In my case, it was a simple cache issue as the endpoints returned HTTP 200 with the appended suffix and response with a cache HIT :) The attack scenario involved crafting and sending a malicious link, "https://target(.)com/api/v1/users/self/.js?cachebuster" to a victim. When the victim, already logged in, opened the link, it led to caching the victim's PII data due to the misconfiguration.
4️⃣Exploiting the cache - When navigated to "https://target(.)com/api/v1/users/self/.js?cachebuster" as an attacker using Chrome Incognito, the cached response was found containing the victim's PII data from "/api/v1/users/self/" resulting in a risk of sensitive information disclosure.
While this was a relatively straightforward scenario, more complex techniques can help escalate these Issues to an ATO by chaining CSRF, XSS, etc., potentially requiring parameter mining and/or bypassing limitations. We'll look into these examples in future tweets!
Takeaway: Always keep an eye out for cacheable response headers and ensure this vulnerability class is part of your checklist. If you find a cacheable response but can't exploit it, feel free to drop a message for collaboration. 😊
Thanks for reading! #HackerOne #BugCrowd #SecurityTips #BugBountyTips #Security #WebCache #BugBounty 💻🔒

English

This is a valid P4 in bugcrowd VRT
No cache control for sensitive pages
It's not always about P1/P2 ,
There is no issue with reporting valid P4's
..
I guess there is no such hunter in the BB community who never reported P4 issues in his journey .
x.com/LiveOverflow/s…
LiveOverflow 🔴@LiveOverflow
Do not report this! Stop making up fake issues...
English

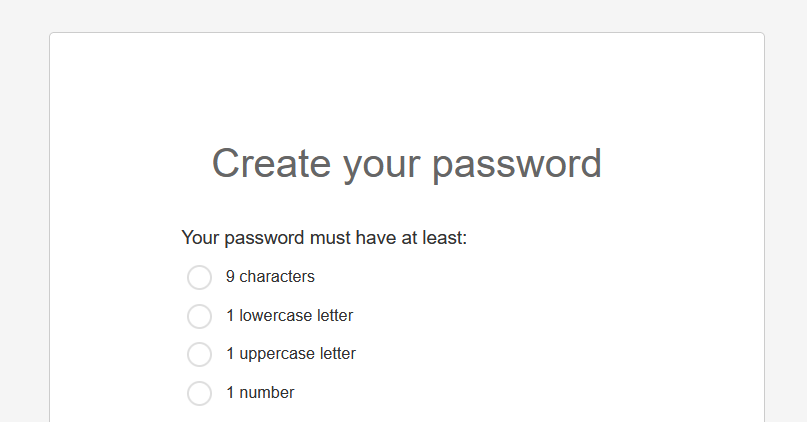
@CristiVlad25 Weak password complexity....
Atleast 12 char with camel case, numbers and special char should be considered as strong password
English

@dirtycoder0124 @Bugcrowd It's back and refresh attack...
Btw congratulations 👏
English

🔒 Question of the day: How to hunt on restricted web applications protected behind a login page? 🤔 Well, guess what? While most folks tend to overlook these targets, I've pocketed over 5 figures $$$$$💰 from such apps. Bounties for findings on these assets often result in generous High/Crit payouts, ranging from $2,000 to $10,000. 💸
Here's a rundown of what you can do to uncover issues with such targets:
1️⃣Response Manipulation: Create a "match and replace" rule in Burp Suite to swap "false" with "true" and 403/401 status codes with 200. After this, try accessing the app and log in with an incorrect password while keeping Burp Suite active. 🛡️ This trick can often reveal whether the app relies on client-side validation for such apps, potentially granting unauthorized access due to lack of server-side authorization checks.
2️⃣Brute Force: Test common username/password combinations. Many such apps use predictable credentials, like admin:admin, admin:password, etc.
3️⃣SQL Injection: Perform SQL Injection on the login for these targets using tools like SQLMAP or Ghauri. It may take some time, but since it's just a single request, it's definitely worth a shot. Prepare to be amazed by the results! 😲
4️⃣JS endpoints: Review all exposed JS files on the page and extract endpoints using JSBeautify/LinkFinder. Often, you'll discover APIs that are vulnerable to IDOR/Information disclosure, even without authentication, potentially leading to nice bounties.
5️⃣Directory Fuzzing: Utilize FFUF or equivalent tools to fuzz for directories. You can find excellent wordlists at wordlists.assetnote.io, tailored to the web application's underlying technology.
6️⃣Breached Credentials Services: Many people employ these services to search for org employees or other credentials linked to the target. If found, they often test them to access the admin page and report the findings (Note - not all programs accept this).
7️⃣Wayback: Always check for archived URLs related to the target, as they may reveal accessible paths without authentication, providing direct access to the dashboard.
There are many more tricks to get around such target apps. We'll talk more in detail with specific examples in future tweets.
🚀Lesson: Do not ignore these types of apps, as they are often a goldmine! 🕵️♂️🌐 #Cybersecurity #BugBounty #WebSecurity #hackerone #bugcrowd #securitytips #questionoftheday #bugbountytips #earn #bounties
English

🔒Sharing more secrets - It's 2023, and CSRF issues are far from extinct. In fact, I've discovered and reported 100+ CSRF vulnerabilities this year, raking in five figures $$$$$!💰
🚀 My top 5 CSRF bypass techniques and their secrets to success:
1️⃣ Swap "POST" with "GET": Instead of using POST requests, switch to GET and move the body parameters into the URI. This simple maneuver often overrides CSRF token implementations, enabling a full-blown CSRF attack.
2️⃣ JSON Requests: Even JSON requests relying on cookies can be vulnerable to CSRF. Here's the trick: send your request with a content-type of text/html and format the body in JSON. In some cases, if the application doesn't rely on the content-type header, CSRF can still work its magic.
3️⃣ Don't Blindly Trust CSRF Tokens: Just because an application has a CSRF token doesn't mean it's foolproof. Sometimes, backend validation for these tokens can be flawed. This means that even with the same token, a CSRF attack may still work on other users' accounts.
4️⃣ Remove the CSRF Token Parameter: Believe it or not, some applications are designed to support legacy versions. If you try removing the CSRF token parameter from the request, it may still work. This is often because apps have dual implementations, and if the parameter is missing, they fall back to the legacy version to support older versions of the app, which can often be vulnerable.
5️⃣ Legacy Endpoints: Hidden in JS files are legacy endpoints that may no longer be actively in use, but they can still be functional and vulnerable to CSRF attacks. These abandoned endpoints are usually not maintained or updated to the latest security standards, making them prime targets for CSRF exploitation.
🎯 Lesson: CSRF issues are not to be underestimated. They are often hiding in plain sight, waiting to be discovered, and they can offer substantial bounties. Happy hunting, and enjoy the rewards! 💎💻 #Cybersecurity #CSRF #BugBounty #InfoSec #hackerone #bugcrowd #cybersecuritytips #securitytips 💰💡
English

🕵️♂️Here's another secret no one will tell you about: A Simple WAF Bypass for Stored XSS that has earned me $$$$💰 so far!
Stored XSS issues can fetch you rewards ranging from $500 to $7500, depending on the program.
WAFs can pose significant challenges when hunting for Stored XSS vulnerabilities, but this simple trick can help you bypass them. By adding 'Content-Encoding: any_random_text' to the request header, you can deceive some WAFs, allowing your payload to slip through undetected. Enjoy the hunt! #bugbounty #securityTips #ethicalhacking #WAFBypass #hackerOne #bugcrowd #bugbountytips

English
Sunny retuiteado

======================
⚡ Exposing Django Debug Panel and Sensitive Infrastructure Information at …vaterelay.nonprod.cloudops.mozgcp.net
👨🏻💻 aliend89 ➟ Mozilla Core Services
🟨 Low
💰 None
🔗 hackerone.com/reports/2078707
======================
#bugbounty #bugbountytips #cybersecurity #infosec

English
Sunny retuiteado

"Ways I followed to Bypass ‘403’ — Your checklist" is a fantastic article written by
Suprajabaskaran where they have discussed in depth about different tricks to bypass 403 in web applications.
Read here: infosecwriteups.com/ways-i-followe…
English
Sunny retuiteado

GraphQL has changed the way developers interact with APIs.
Many apps use GraphQL to source data, so it's a good thing to know as a dev.
In this course, you'll learn everything you need to know to create robust & efficient data-driven applications.
freecodecamp.org/news/graphql-d…
English