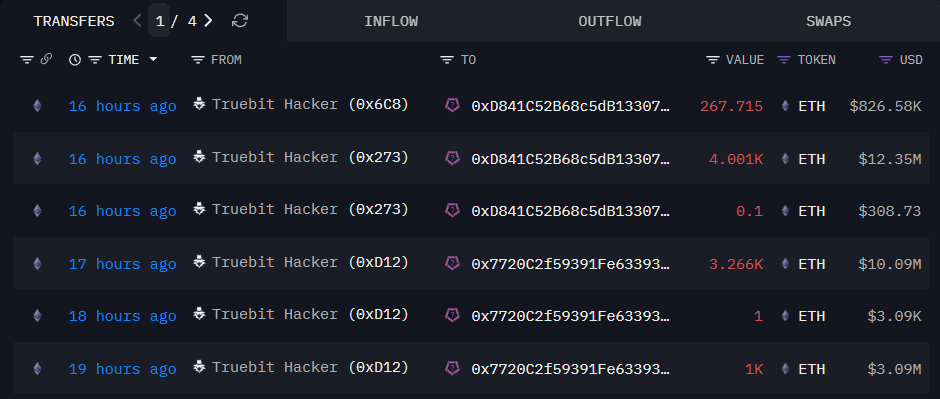
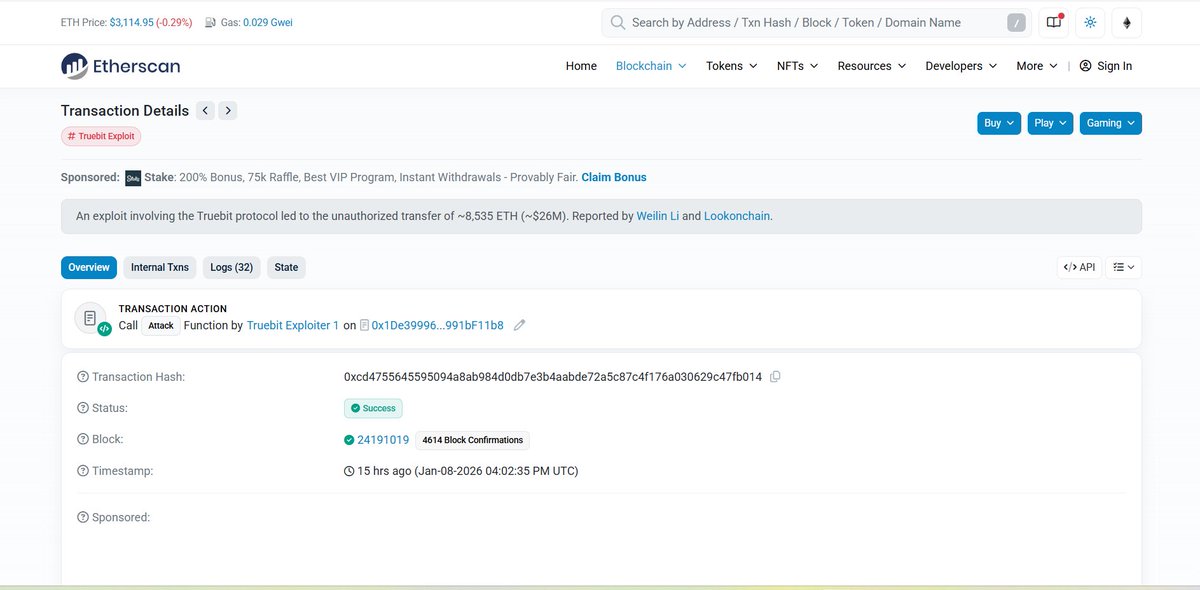
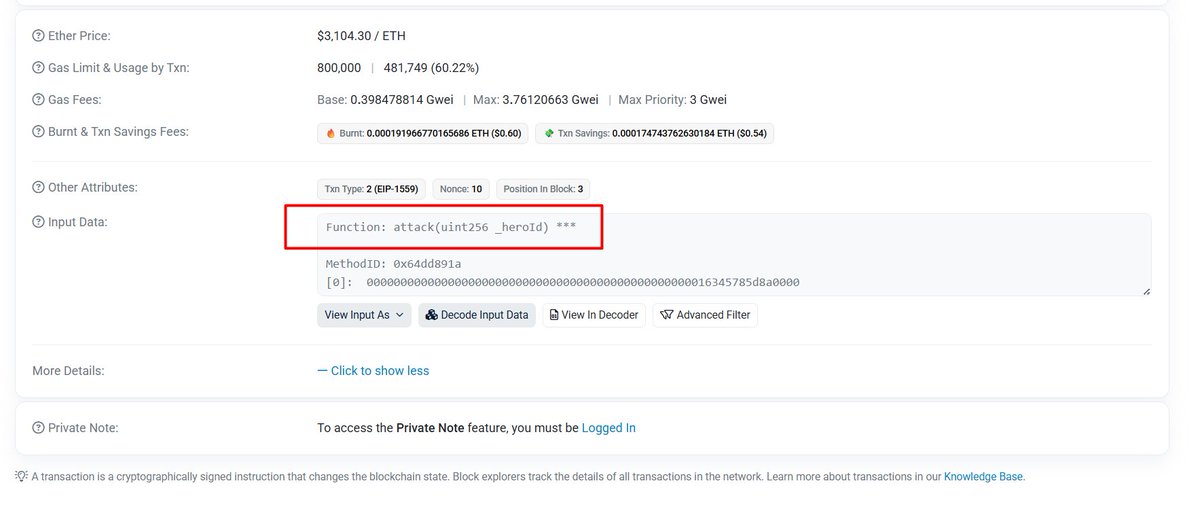
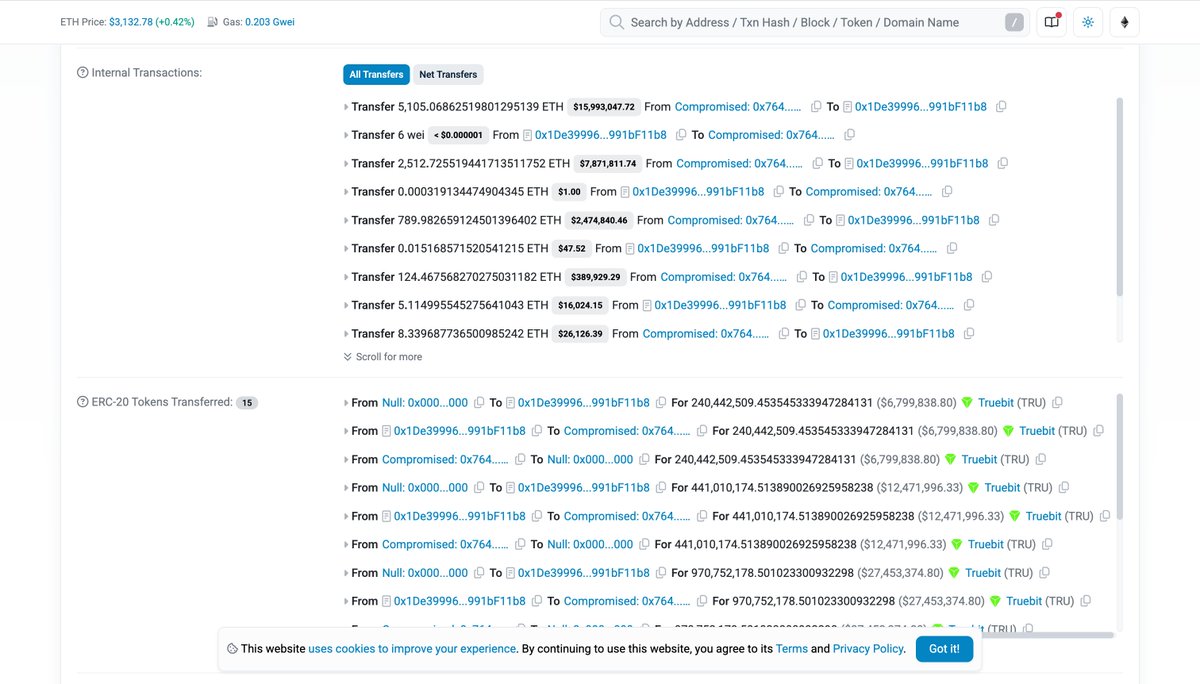
Today, we became aware of a security incident involving one or more malicious actors. The affected smart contract is 0x764C64b2A09b09Acb100B80d8c505Aa6a0302EF2 and we strongly advise the public not to interact with this contract until further notice. We are in contact with law enforcement and taking all available measures to address the situation. We will share updates through our official channels as they become available.