Kevin Perlow
139 posts


Kevin Perlow
@KevinPerlow
RE and CTI. Feel free to take a gander at my past presentations: https://t.co/iWUyecnxC6







New blog post: Analyzing attacks that exploit the CVE-2021-40444 MSHTML vulnerability msft.it/6011XTGHN




It has launched! ATT&CK v9 is now live with refactored data sources, ATT&CK for Containers, Google Workspace as a platform and more! Read about new data sources and the rest of the update at medium.com/mitre-attack/a… or attack.mitre.org/resources/upda… for new/changed groups/techniques/sw.






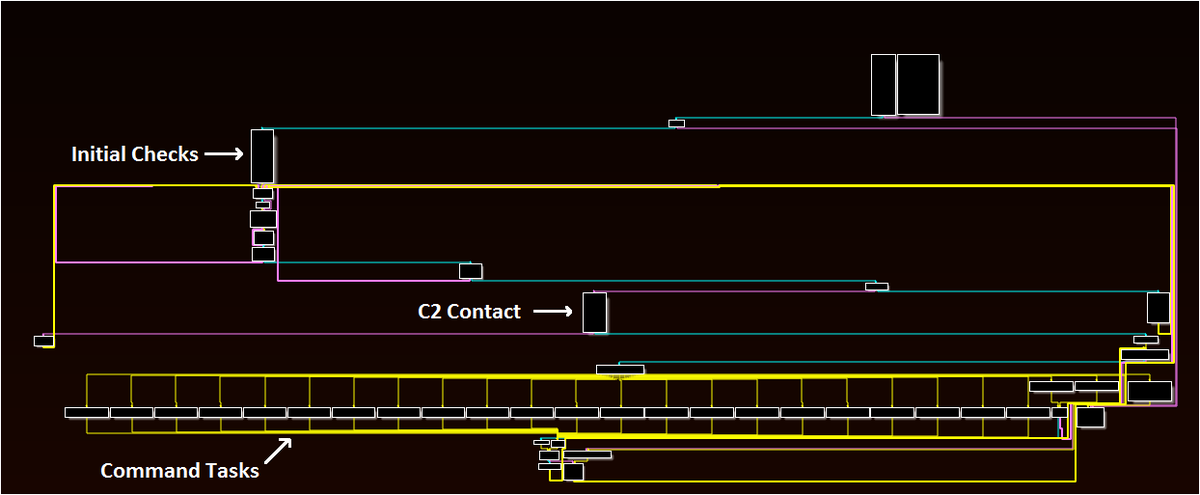
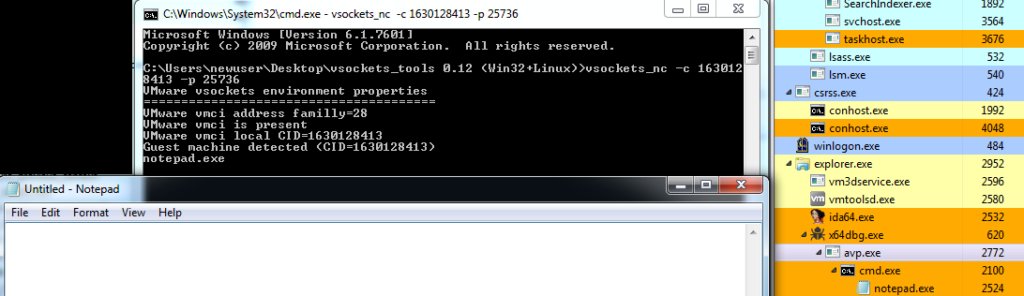
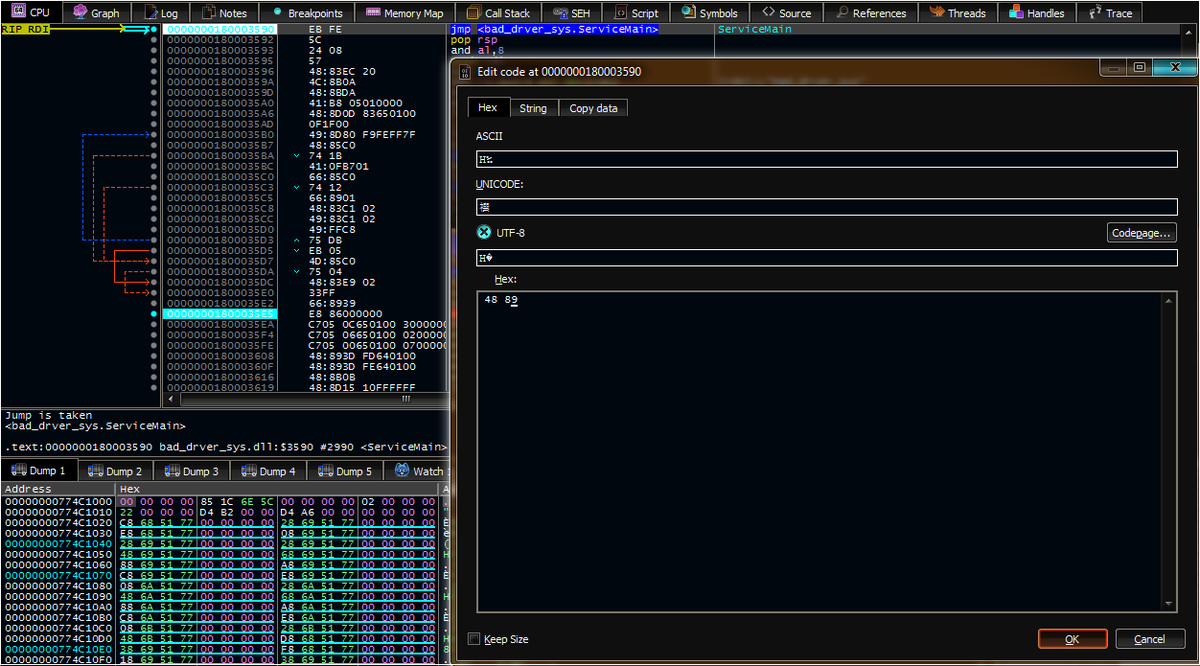
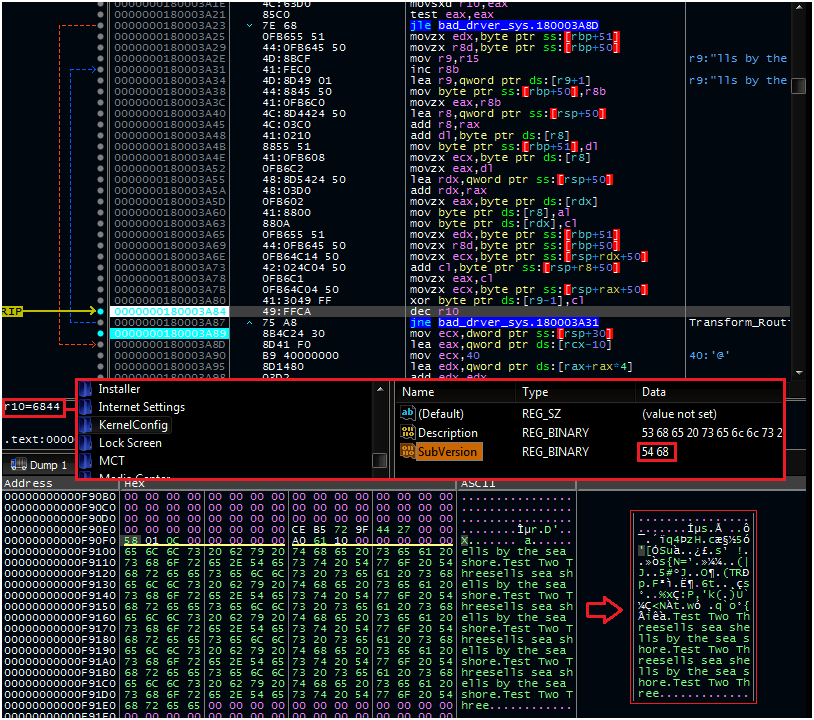
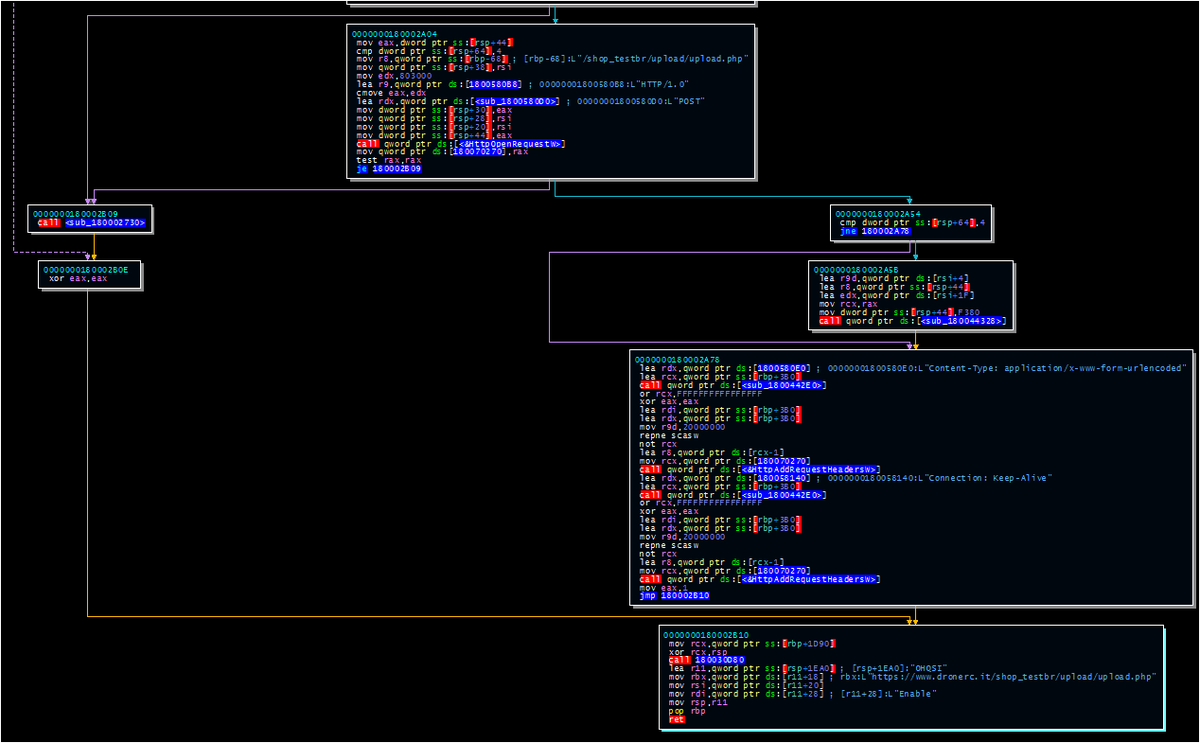
Part II: Looking at the #DPRK /#Lazarus/#ZINC .sys malware targeting security researchers, with a hunt hypothesis as the highlight: norfolkinfosec.com/dprk-targeting… Note that I *don't* have the Stage 2 registry data. Would love to see it if someone has a copy!







New blog post from TAG with details of a North Korean campaign targeting security researchers working on vulnerability research and development. blog.google/threat-analysi… Stay safe out there everyone!

New blog post from TAG with details of a North Korean campaign targeting security researchers working on vulnerability research and development. blog.google/threat-analysi… Stay safe out there everyone!