Squiblydoo
1.8K posts


Squiblydoo
@SquiblydooBlog
Malware Analysis Creator of Debloat, certReport, and https://t.co/hEJGt0jzIq Want to chat? Join the Debloat discord: https://t.co/ZcWIqa6ZA9












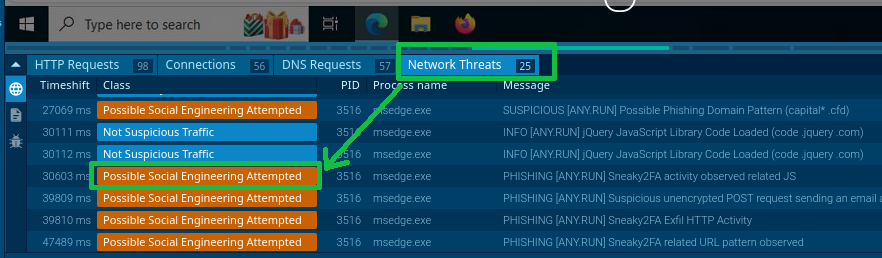





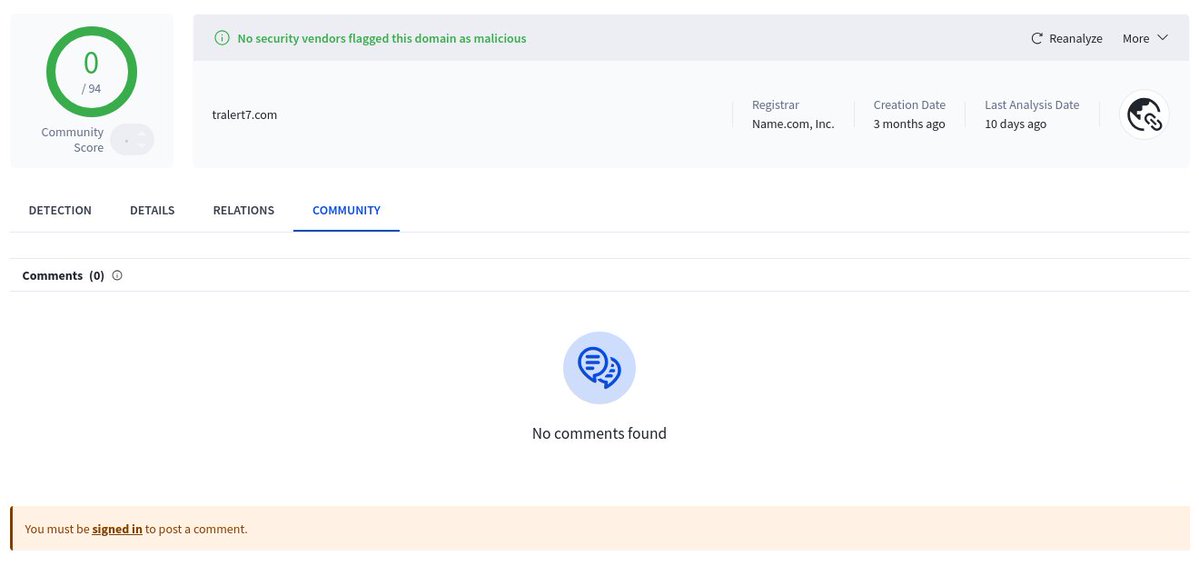
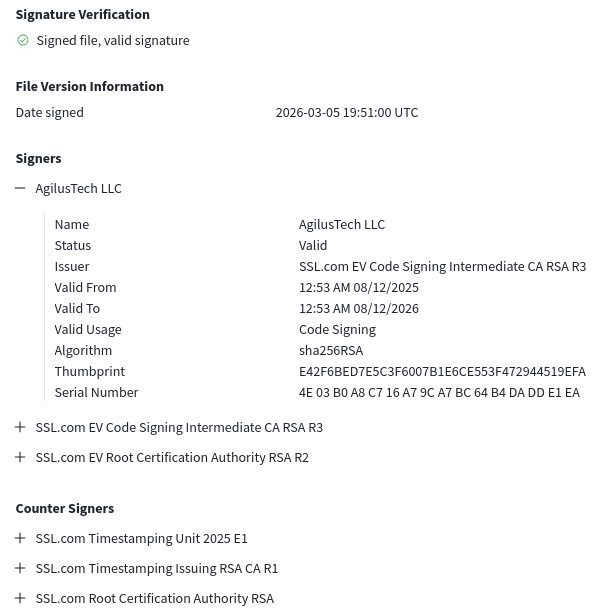




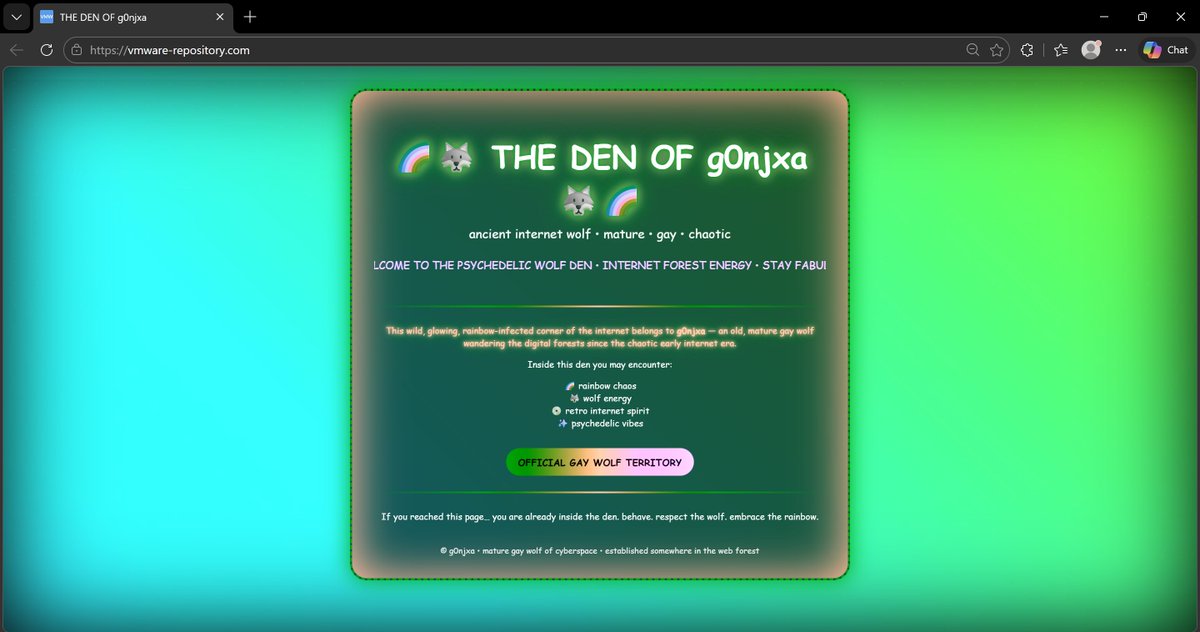
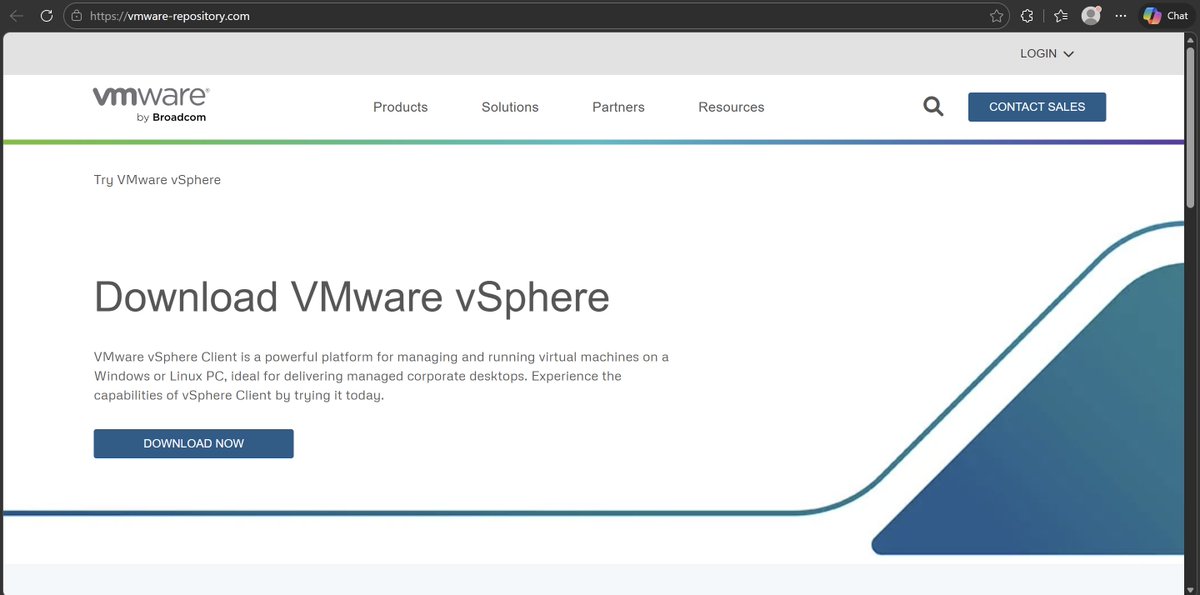
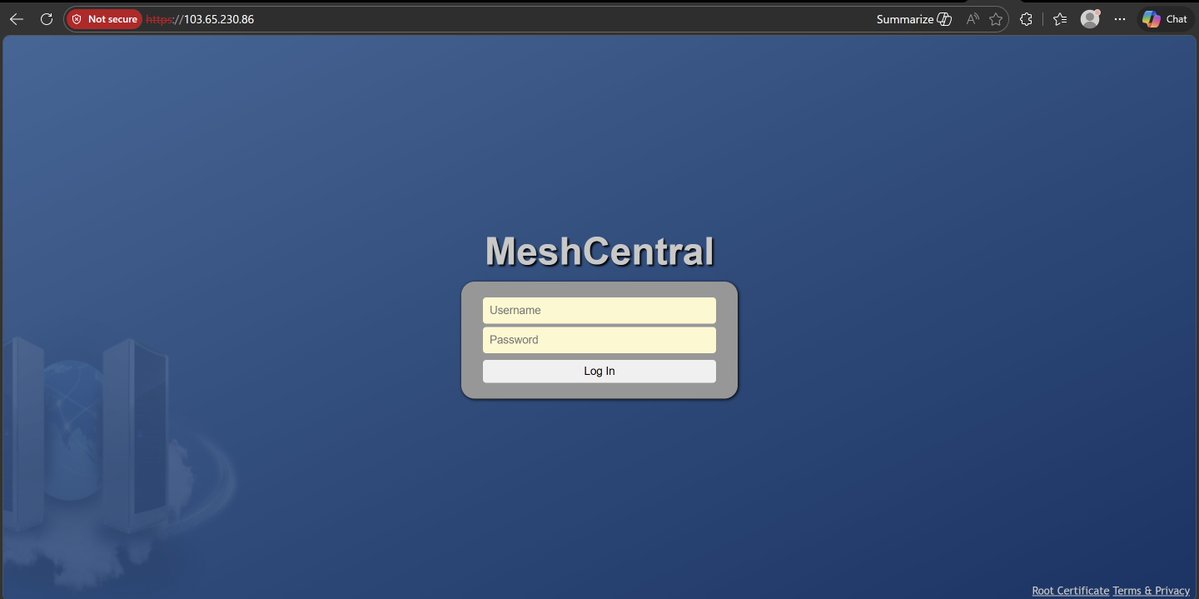
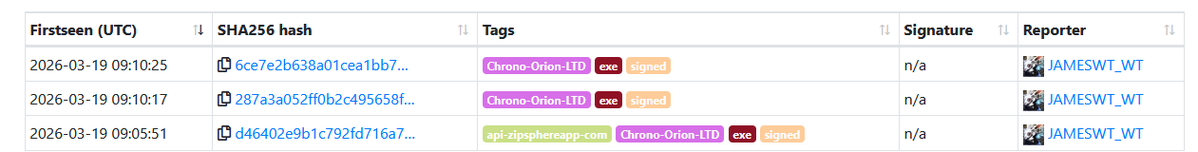
⚠️Watch out for a SEO poisoning campaign impersonating VMware vSphere downloads leveraging MeshCentral RMM tool bundled into fake installers targeting enterprise environments. Sample: dbfe1f915f40122a336cd5d0de802a6f3ec0204ab75321934a06dafbc1964446 Detonation: app.any.run/tasks/e0937ead… From malicious search results -> vmware-vsphere[.]com (associates, vmwarevsphere[.]com, vmware-remote-console[.]com, remote-console-vmware[.]com, vsphere-client[.]com, vsphere-client[.]org ) leading to vmware-repository[.]com A malicious build with EV signature issued to malicious signer "Pacex Learning Private Limited" (Globalsign) is delivered from Dropbox. The build connects to 103.65.230.86 (MeshCentral RMM C2) and installs legit VMware product as decoy

We're happy to announce that #malcat 0.9.13 is out! You'll find a new Apple-silicon MacOS port, two integrated MCP servers (in-GUI +headless) for automated triage and an improved interface: malcat.fr/blog/0913-is-o…