Tur.js
917 posts

@Tur24Tur
Interested in Application Security, Bug Bounty, Reverse Engineering, Frida & Ghidra @NoBugEscapes @BugBountyZip https://t.co/bltifT1jkQ


Hello, the agent found multiple XSS on an open source project on GitHub i deployed it locally on Docker and set up one account. After the agent found the XSS, I told him to write the steps he followed to be shared with everyone. It was an interesting one how he navigated the website step by step and linked the pieces together to achieve an exploit
Whenever I find any interesting results, I'll make sure to share them.
Finding Stored XSS in a CMS — An Automated Agent's Approach
TLDR
- Target: a modern CMS using Vue.js frontend
- Found 2 stored XSS in 22 minutes (157 tool calls)
- Root cause: asset title rendered via v-html without escaping
- Impact: session hijacking (no HttpOnly cookie), admin takeover
How It Went
1. Logged in, checked headers — no CSP, no HttpOnly on session cookie. Vue.js frontend means auto-escaping by default, so I needed to find where the app opts out.
2. Downloaded all JS files and grepped for dangerous sinks: innerHTML, v-html, insertAdjacentHTML. Most were sanitized or safe. One file stood out — the asset field renderer built raw HTML with template literals and fed it into v-html.
3. Tested many surfaces that did NOT work: model names, content fields, WYSIWYG editor, login redirects, API errors, color/tag fields — all escaped or stripped.
4. Found the gap: asset titles go into the render function unsanitized. Uploaded a text file, set the title to `` (29 chars, fits the 30-char truncation limit). Linked it to a content item. Visited the items list — alert fired.
5. Confirmed impact: document.cookie is readable (no HttpOnly), no CSP blocking inline scripts. Any user with asset permissions can plant the payload, and it fires when any admin views the page.
Key Takeaways
1. Source code analysis beats blind fuzzing — reading JS files and finding the exact sink saved hours.
2. v-html is the Vue XSS keyword — every v-html that touches user data is a potential bug.
3. Template literals are just string concatenation — they do not escape HTML.
4. Asset metadata is an overlooked input surface — most testers focus on content fields and URL params.
5. Truncation is not sanitization — 29 characters is plenty for an XSS payload.
#BugBounty #AgenticAI #InfoSec

Spent the last few weeks building an XSS hunting agent using Claude Agent SDK. Custom tools for param discovery, CSP analysis, context detection, and browser-based confirmation. Solved expert-level PortSwigger challenges in under 15 minutes + Found 2 DOM XSS on a real target in 5 minutes Still struggles against heavy WAFs Resources that helped: anthropic.com/engineering/bu… platform.claude.com/cookbook/patte… #BugBounty #AgenticAI #InfoSec










Did @Cloudflare just defeat @Burp_Suite and @CaidoIO? Cloudflare protection is becoming very common. This is the third app I’ve seen using it. Changing the user agent doesn’t help, and Burp TLS-fingerprint bypass plugin didn’t work. The app blocks any request when it detects traffic interception My target mobile app might be using a dynamic certificate based on my friend analysis. Back in Nov 2024, I tested a web app with Burp, but it blocked all traffic. Switching to Caido worked, maybe its signatures weren’t detected at the time. Can anyone share insights? thanks #BugBounty


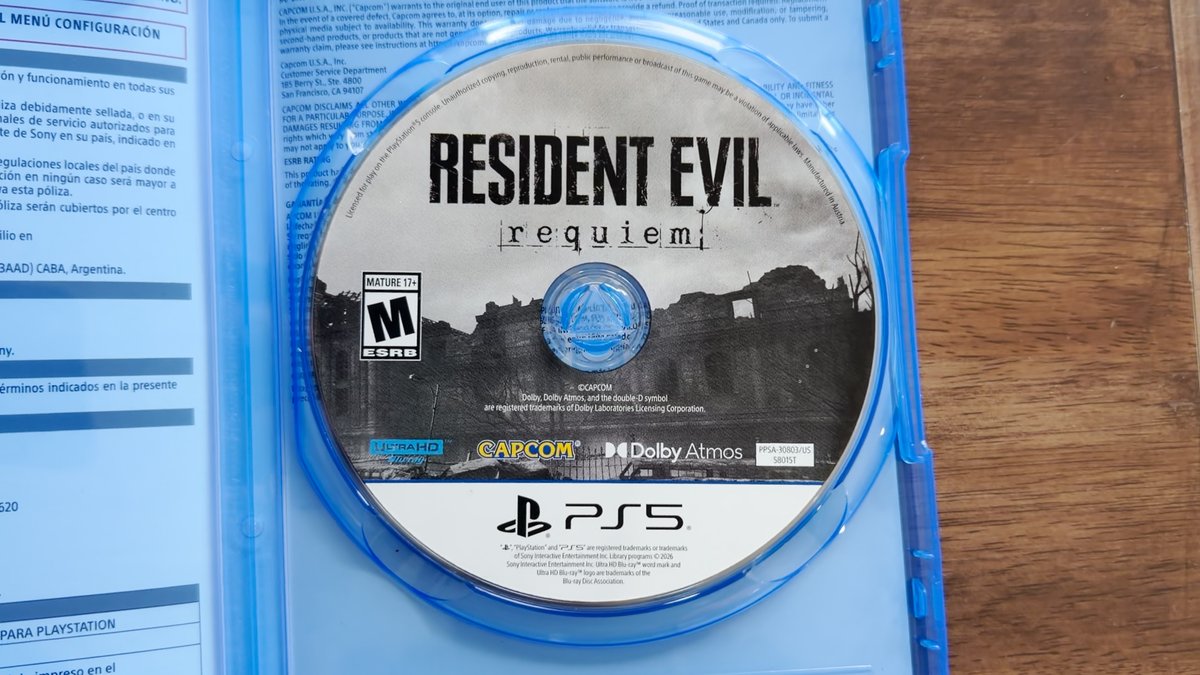
Frida 17.8.0 dropped with frida-strace syscall tracing on Android & iOS, no jailbreak. Thank you @fridadotre #Frida #MobileSecurity #AppSec



For anyone dealing with RASP protected apps, frida-strace is now your first step. Trace the syscalls, find what the app checks, hook those specific functions, bypass. No more guessing. Frida 17.8.0+, kernel 6.1+ required. #Frida #MobileSecurity #AppSec