Ember
1.2K posts


Ember
@embrron
A moment of pain is worth a lifetime of glory. Growing @pyronfi



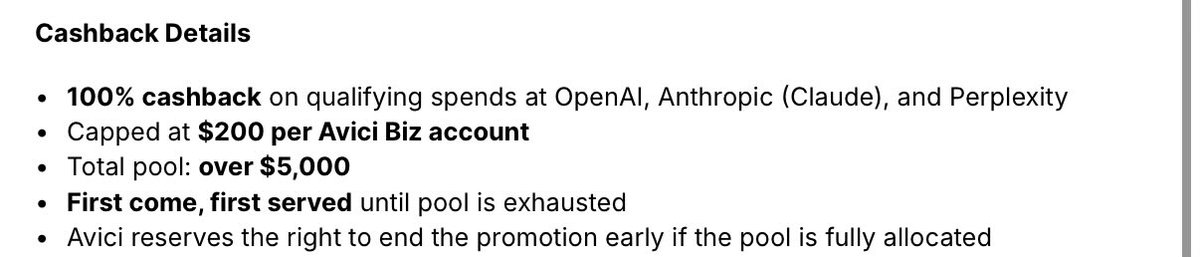
Avici card → spend on claude → earn claude credits back Should we ship it? show us you need it Comment “want”👇









Earlier today, a malicious actor gained unauthorized access to Drift Protocol through a novel attack involving durable nonces, resulting in a rapid takeover of Drift’s Security Council administrative powers. This was a highly sophisticated operation that appears to have involved multi-week preparation and staged execution, including the use of durable nonce accounts to pre-sign transactions that delayed execution.


in light of recent events, chief puppeteer @0x_febo and I wrote a solana program and a library that allow applications to BAN the use of durable nonces within their program there are two options for you to use: 1. you can use the ensure_never_nonce function from the p-never-nonce crate that we just published within your program 2. you can cpi into the p-never-nonce program that will be deployed shortly github.com/febo/pinocchio…


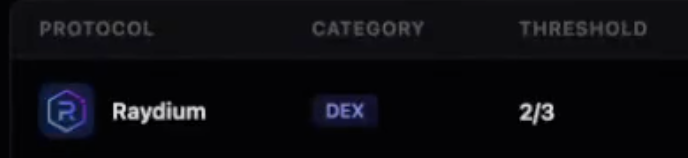
1/ Drift's admin key was compromised. $213M+ drained from @solana's largest DEX in under 10 seconds. Unfortunately, we've seen similar patterns before: - fake collateral market - a manipulated oracle - disabled circuit breakers Let's break it down 👇 written w/ Chaos AI







@DriftProtocol tldr: we were managing a $500m+ protocol like a bunch of 4 year old kids. everything around admin key protection was wired, and you can’t seriously expect people to believe this was a 100% external attack why? 👇🏻


@DriftProtocol tldr: we were managing a $500m+ protocol like a bunch of 4 year old kids. everything around admin key protection was wired, and you can’t seriously expect people to believe this was a 100% external attack why? 👇🏻

Earlier today, a malicious actor gained unauthorized access to Drift Protocol through a novel attack involving durable nonces, resulting in a rapid takeover of Drift’s Security Council administrative powers. This was a highly sophisticated operation that appears to have involved multi-week preparation and staged execution, including the use of durable nonce accounts to pre-sign transactions that delayed execution.


Drift Protocol is experiencing an active attack. Deposits and withdrawals have been suspended. We are coordinating with multiple security firms, bridges, and exchanges to contain the incident. This is not an April Fools joke. We’ll provide additional updates from this account as more information is available to share.