
Streamr Network
13.2K posts

@Streamr
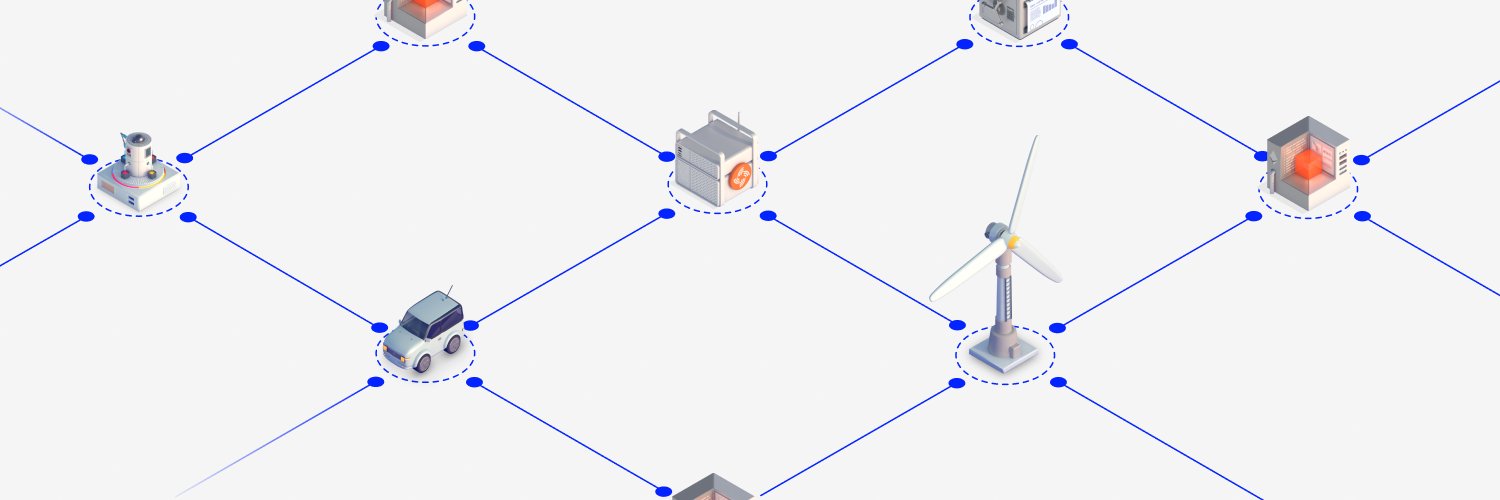
Real-time data & media broadcasting. Global, peer-to-peer, serverless. $DATA. Powered by @0xPolygon. Powering @Streamr_app → https://t.co/0j9kNBgu5O








Sweden Breach Shows the Security Risks of National Digital ID Systems reclaimthenet.org/bankid-breach-…




In Texas, we’re standing together to protect our children from online harm. The Senate’s Kids Online Safety Act (KOSA, S. 1748) sets a strong, bipartisan standard by requiring Big Tech to exercise a “duty of care” in designing social media and gaming platforms — putting child safety first without limiting free speech. Unfortunately, the House’s KIDS Act (HR 7757) falls short. It removes this crucial duty of care, limits state powers to protect kids, and lets tech companies police themselves with minimal accountability. This letter to Senators Cornyn and Cruz urges them to respond to the strong bipartisan support of the Texas Senate for the language in the US Senate’s KOSA — a bill that balances federal standards with states’ rights to enact stronger protections as technology evolves. Kids deserve real guardrails online. We must hold Big Tech accountable and keep states empowered to protect our children. #ProtectKidsOnline #DutyOfCare #KOSA #BipartisanAction





JUST IN: Reddit CEO says the company is considering requiring Face ID to ensure humanity in order to crack down on AI bots.



The Senate's Kids Online Safety Act is the gold standard for protecting kids online. ✅ 76 bipartisan cosponsors ✅ Includes a duty of care ✅ Passed the Senate 91–3 in 2024 @LeaderJohnThune: Families cannot wait. It's time for the Senate to #PassKOSA without delay.




The FBI has confirmed it is buying commercially available location data from private companies. This lets the agency track people's movements using smartphone data without needing a warrant.


🚨America's newest Digital ID proposal just dropped in the US Senate. Republican Senator Marsha Blackburn has introduced a new AI bill that bundles 17 different policies into one massive, 291 page bill. This is just like all these other tech bills we've been seeing - a massive Digital ID framework - with universal age verification being the key to access to the tools. The bill includes mandatory age verification for every existing account and freezing accounts until users verify their age.



In December, President Trump signed an Executive Order tasking us with the development of a national framework for AI, what he called “One Rulebook.” This was in response to a growing patchwork of 50 different state regulatory regimes that threaten to stifle innovation and jeopardize America’s lead in the AI race. Today we are releasing that framework. It will help parents safeguard their children from online harm, shield communities from higher electric bills, protect our First Amendment rights from AI censorship, and ensure that all Americans benefit from this transformative technology. We look forward to working with our colleagues in Congress to turn the principles we are announcing today into legislation. whitehouse.gov/articles/2026/…

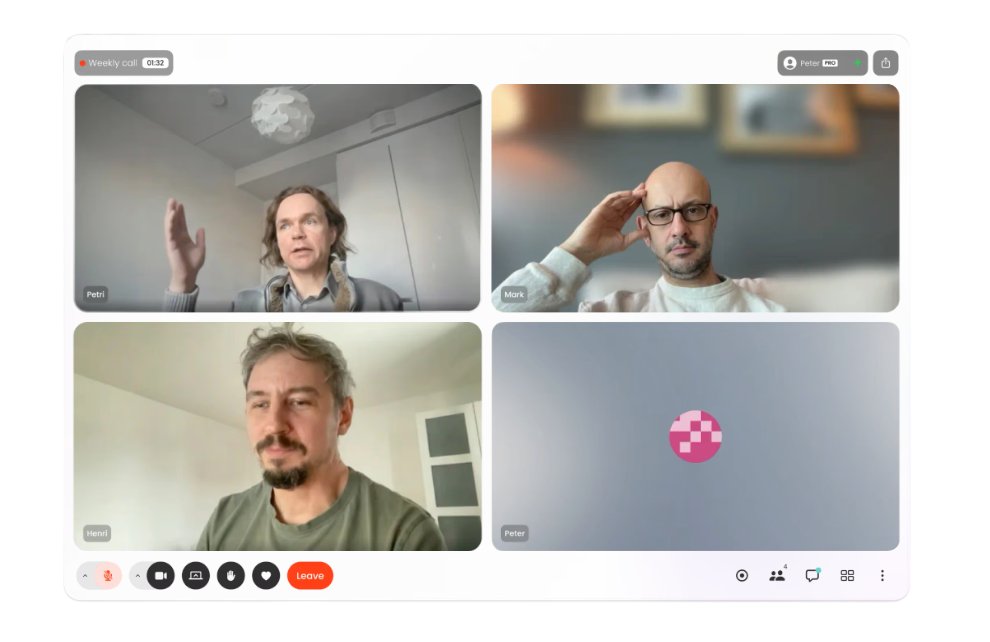
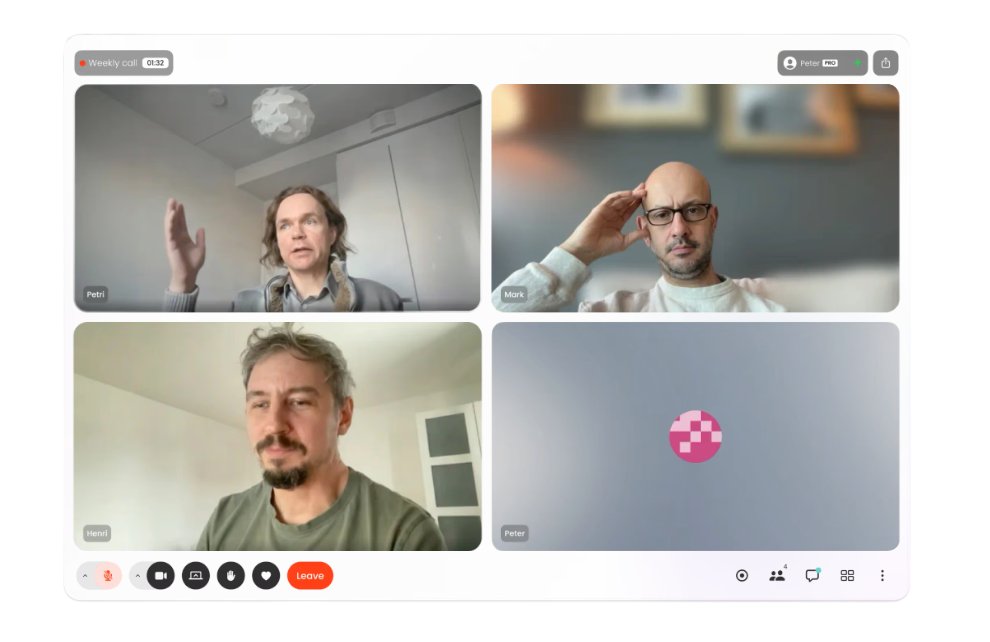
🔶We spent a long time asking ourselves a simple question: Why do video calls still need central servers at all? Once you look closely, most of the privacy and reliability issues start right there. 1/🧵




The FBI is buying your location data. Read that again.