Bea Venzon 👾
97 posts


Bea Venzon 👾
@0x0bea
CTI + RE @CrowdStrike // 🐈🐈🐈⬛ // Find me on https://t.co/HiZ5P2nZ27
















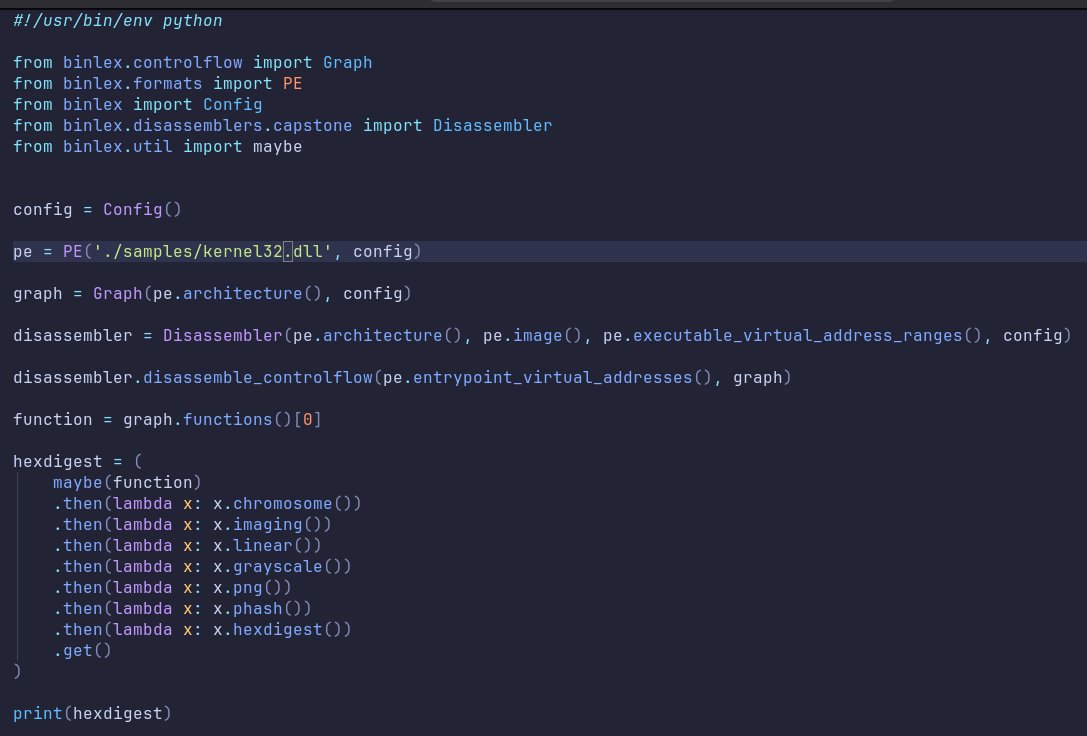
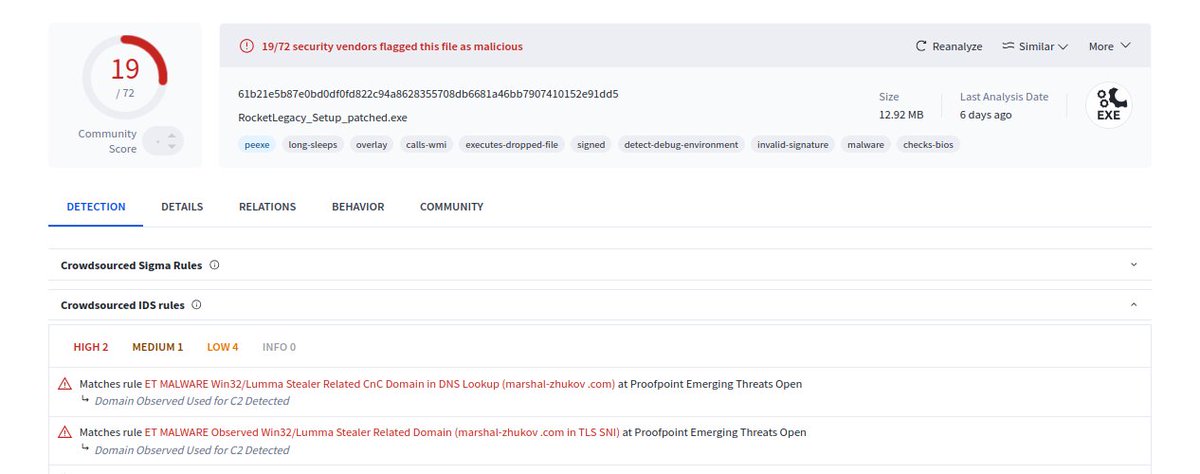
First thoughts about #Lumma Stealer "disruption" (?): There's no need in calling big names on something that (from what I've read and tested) has not happened in the magnitude I'm watching on the media At the moment, Lumma still works, still has working C2s and *apparently* no final major impact has been done to their malware operations despite the big media impact going on. Is true that I saw some malware operations chats in the past hours/days claiming to have issues with the stealer and this is being resolved in a matter of hours like normal issues that previously happened. Here's is proof of a non-crypted build working on a fresh non-seized domain (see photo 1) Detonation: app.any.run/tasks/fb014a66… And more proof on log registers from threat actors using Lumma (meaning the infostealer still is infecting machines) (see photo 2) The efforts in this partial "disruption" operation seems to be focused on the seizure of already known C2 servers (gathered by malware intelligence services), being this domains active in use or not. That's why there's already new domains working, or previous domains that went unnoticed, and this not means the Lumma Stealer infrastructure has been disrupted! Would this events start a "war of attrition" where newly found C2 domains will be quickly seized? We will see, and I don't think is a good idea. This is a questionable approach to Lumma due to the nature of this infostealer, whose C2 servers (that act as a proxy to deliver log from victim computer to a panel) are changed and rotated in a daily basis. And talking about the panels (something that could be more interesting to takedown), seems like the disruption and seizure of the already known panels has been committed partially (see photo 3) and of course this represents the seizure of a domain involved in a malware campaign by a customer, not the whole administration of Lumma Stealer. As said before, efforts to disrupt malware operations are always appreciated and I want to imagine the big work on behalf the operations, but I think events like today ones and claiming things that I don't believe they are true news just harm the reputation of the big companies and LE agencies that everyday tries to keep the world safer. Less drawings, more actions. As said before, I'm commenting the situation after the initial reports. I'll wait for further movements and statements, keeping a close eye. I can't know what is going to happen in the next days.