Todorov
691 posts


I made $500 and am donating it to a random person who retweets this and comments below✌️
Found an issue related to using `ERC20::approve` - it always reverts with USDT on Ethereum mainnet (no `bool` returned). Use `SafeERC20`'s `forceApprove` method by OpenZeppelin instead🫡
pashov@pashov
I’m betting $500 that I will find at least a single Medium/High severity issue in your Solidity protocol’s code in 24hrs Try me, weak devs, this will be the easiest cash ever😈
English

It was pleasure for me to work together with Pashov and such an amazing experts to provide a great security service. Check the latest report from @PashovAuditGrp 👇💯
Pashov Audit Group@PashovAuditGrp
Arcadia audit report published, this one is exciting as it comes after 2 other great team audits and before a Sherlock contest. Quote from one of our auditors: "This was the most extensive and intensive fuzzing test suite i have ever seen"🫡 Read here: github.com/pashov/audits/…
English

If you wonder what actually is the pre-audit phase and what kind of mistakes can be fixed before the actual security audit…👇
pashov@pashov
4 quick tips I give to my security clients pre-audit: 1. Enforce a concrete compiler version that has no reported bugs 2. All state-changing methods should emit events 3. Use `safeTransfer` as opposed to `transfer` 4. Add complete NatSpec docs to all external methods
English

Well maintained list of Smart contract vulnerabilities.👇🏻
github.com/sirhashalot/SC…
English

@0xTodorov Another point I would add here is to write a clean code.
Panoptic, which holds a contest on C4 now, has drawn schemes in their code, and it's far easier to understand how they use functions and store variables.
English

@Saedeh57 At overall, the standard is fine-tuned a lot in the last 2 years, but it has complex nature as every upgradable project, which increases the chance for potential bugs.
I can recommend you this short article, there you can find some security advices:
eip2535diamonds.substack.com/p/diamond-upgr…
English

@0xTodorov Interesting that I was working on Diamond contracts in the past few days.
How do you see them from the security aspect?
English

MEV has become a significant topic of discussion and concern in the Web3 community due to its impact on the decentralized systems.
Because of that it's highly for every researcher to master it. Link below can help you for that👇🏻
github.com/0xalpharush/aw…
English

@WangAudit To be validated, one problem should be explained clear, if someone cannot explain the issue in most cases that’s because he didn’t understand the root cause.
English

@0xTodorov Knowing this issues and actually understanding them can lead to finding good bugs.
I've recently read a bug from 0x52 who reported the problem with USDC in a real case with a solution, and it was a unique.
Hope no one submits bugs like "using USDC and USDT can cause problems".
English

Tokens with non-standard decimal values can pose risks to smart contracts. For instance, tokens like YAM-V2 with 24 decimals may trigger unexpected reverts due to overflow, introducing a liveness risk to the contract. On the other hand, tokens with low decimals, such as USDC (6 decimals) or Gemini USD (2 decimals), can result in more significant precision loss than anticipated when handling these tokens, adding another layer of complexity to contract interactions. Developers should carefully account for these decimal variations to ensure the robustness of their smart contracts.
English

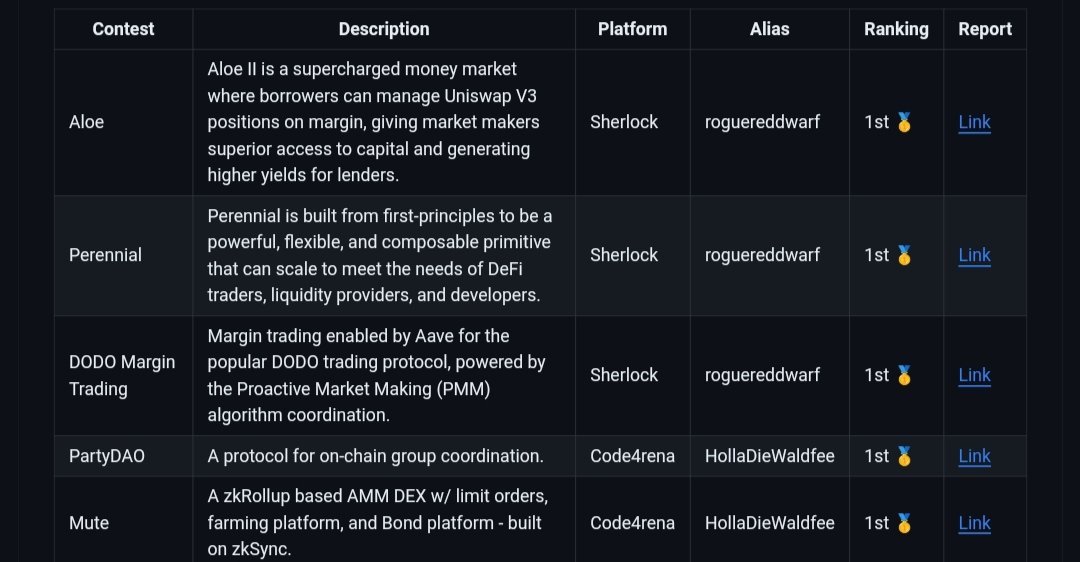
@HollaWaldfee100 Inspirational, congrats👏🏻, if I may ask, how much time you put in Aloe to achieve the 1st place there?
English


Staking protocols have a wide range of vulnerable spots, including but not limited to withdrawal mechanisms and the duration of the stake. In this article, you can find more information and to use it as a checklist when reviewing such protocols.👇🏻
blog.quillaudits.com/2023/03/10/gui…
English