Wang Security
2.1K posts


Wang Security
@WangSecurity_
Head of Judging @sherlockdefi
Contact via DMs or → Katılım Mart 2023
636 Takip Edilen798 Takipçiler
Wang Security retweetledi

Major Announcement: The XRP Ledger roadmap is getting a $550K audit contest!
In collaboration with @RippleXDev, we’re putting upcoming XRPL features under a two-week, feature-unlock security review.
Contest starts Monday. Prepare yourselves!
English
Wang Security retweetledi

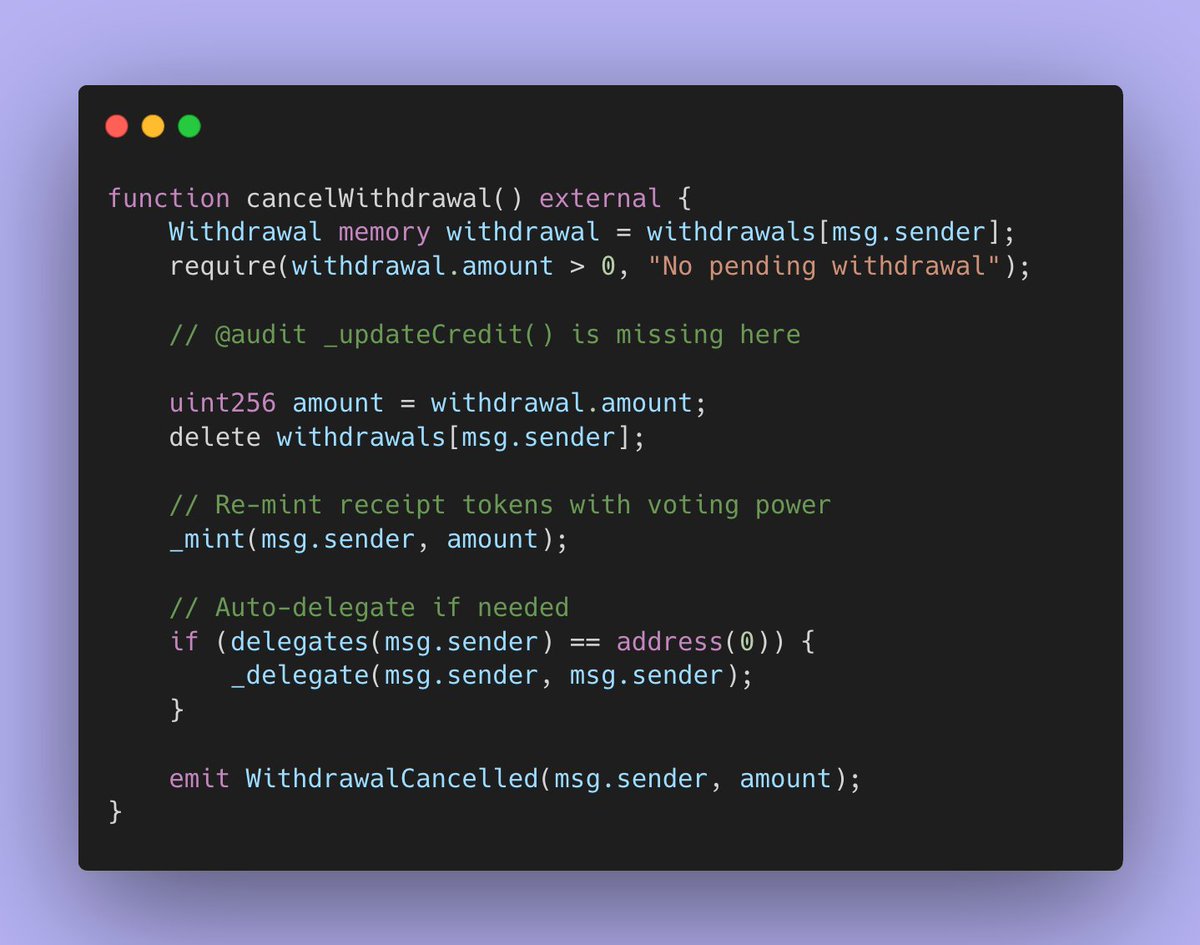
Security is a top priority at @ZentraFinance. Before their formal audit phase ahead of launch, the team also ran Sherlock AI across the staking and rewards contracts to catch issues early. It surfaced a High-severity bug in the rewards accounting. Zentra gave us permission to share it publicly so other teams can learn from the pattern.
Here’s how the vulnerability worked.
Zentra is a decentralized, non-custodial, over-collateralized money market with staking mechanics. The issue lives in StakedZNTDistributor, where rewards are tracked using a global shareIndex and a per-user lastShareIndex so users only accrue rewards for periods when they actually hold shares.
The invariant is simple: only outstanding shares should earn rewards.
The failure point is cancelWithdrawal(). On requestWithdrawal(), the contract syncs accounting (updates lastShareIndex to the current shareIndex) and then burns the user’s receipt tokens, leaving them with zero shares during the pending window. Rewards can still be added during that window via addReward, increasing shareIndex.
If the user then calls cancelWithdrawal(), the contract remints the burned shares — but does not sync lastShareIndex at the moment of remint. The next time rewards are accounted (e.g., claimAllRewards(), stake(), or another requestWithdrawal()), _updateCredit computes (shareIndex - lastShareIndex) * remintedBalance, which incorrectly credits rewards for the entire pending-withdrawal interval when the user’s balance was actually zero.
In practice, it becomes a timing loop around reward events: stake → request withdrawal (burn) → wait for addReward → cancel withdrawal (remint, no sync) → claim. Repeating that cycle around meaningful reward additions siphons rewards from honest stakers.
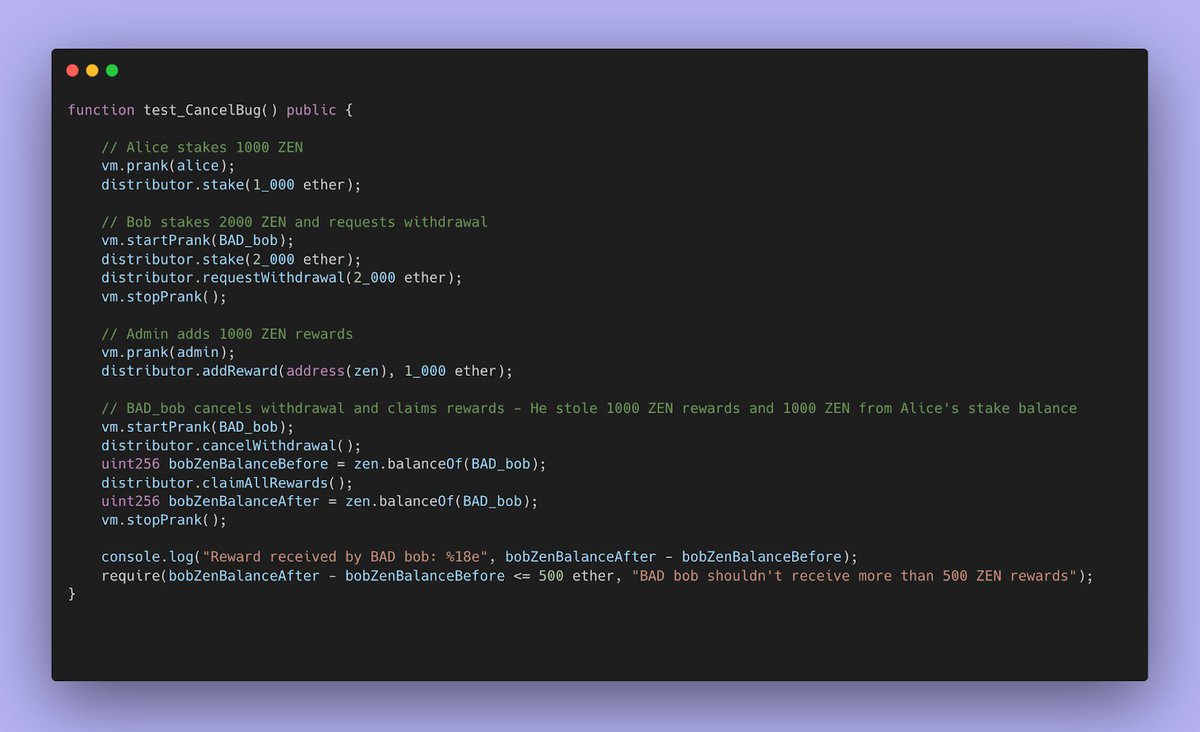
The PoC demonstrates this by setting up an honest staker (Alice) and an attacker (Bob). Bob requests withdrawal, rewards are added during the pending period, Bob cancels, then claims and ends up receiving all the reward for a time that Bob didn’t hold any shares.
Impact is reward dilution and value leakage from the reward pool, because users can claim rewards for time they did not have shares outstanding, breaking the core reward-accounting invariant. Impact is not only limited by rewards dilution. The vulnerability allows the attacker to drain staking tokens too since staked token is also used as reward token. Therefore, insolvency is yet another impact of the vulnerability.
Fix direction is straightforward: treat cancelWithdrawal() as an accounting sync point. When shares are reminted, lastShareIndex must be brought current (or an equivalent sync performed) so the burn interval never gets included in later _updateCredit calculations.
Special thanks to @demorextess for helping triage the issue and assisting with the PoC.
Zentra caught and fixed this during development by running Sherlock AI early. That’s where AI auditing is most helpful: it finds edge cases before reward logic gets locked in, so the formal audit phase starts from a cleaner baseline and incentives go live on math that’s already been pressure tested.
Note: Sherlock completed a security audit of Zentra’s minimal deployment (launch) contracts at branch main, commit 4be344d6f47355063dcf758359ac5682d87a370e. This statement applies only to the contracts and versions referenced by that commit. Security reviews reduce risk, but do not eliminate it.
English
Wang Security retweetledi

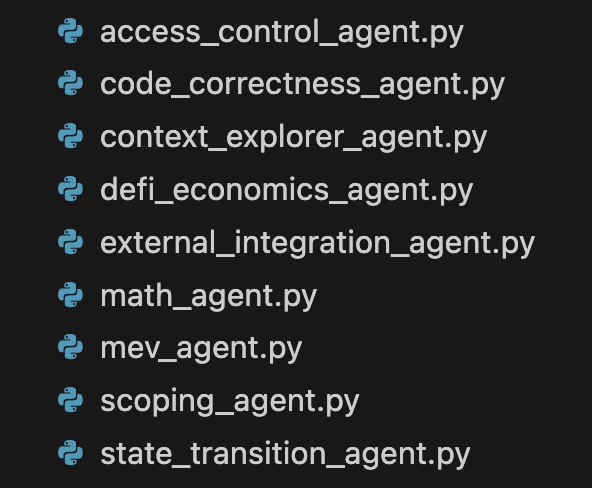
Running @sherlockdefi AI is like hiring an army of top-tier web3 auditors, each of which uses custom methodologies and tools derived from real contest-winning workflows. It’s only getting better from here.
English
Wang Security retweetledi

It was a random Tuesday morning in late 2023, and I was pulling yet another shift at this little coffee shop in Baixa, Lisbon. Crypto winter was dragging on, payouts from auditing contests were nice when they hit but way too irregular, so I was still slinging espressos and steaming milk to pay rent. Headphones in, probably listening to some Bankless episode or a deep dive on EVM quirks, just trying to get through the rush.
I finish making a cappuccino, call out the order, and the guy who picks it up — mid-20s, hoodie, laptop bag, total crypto-native vibe — takes a sip and then does a double-take. He stares at me for a solid three seconds like he’s trying to match a face to a profile pic.
“No way… are you @0xSimao?”
I literally freeze with the milk pitcher in one hand and a rag in the other. In Portugal? At my random neighborhood café? Nobody here knows what a reentrancy bug even is, let alone recognizes my X handle.
I pull out one earbud and go, “Uh… yeah, that’s me.”
He breaks into this huge grin. “Bro, your thread on that Sherlock contest last month was insane — the way you explained the precision loss in the price oracle? Saved me hours debugging my own contract. Huge respect.”
I’m standing there in my slightly stained apron, face probably red as hell, mumbling something like “Thanks man, glad it helped.” Meanwhile the line behind him is growing and my boss is giving me the side-eye.
We chat for like thirty seconds — he’s a dev building on Arbitrum, follows a bunch of the same auditors I do — then he snaps a quick selfie (with permission) and says he’s gonna tweet it with “finally met the legend pouring my coffee.” I’m begging him not to, but he does it anyway.
By the time my shift ends that evening, my notifications are blowing up. People tagging me like “0xSimao moonlighting as a barista is the most relatable CT thing ever” and “king of grinding in every sense.” A couple OGs even tossed me small tips in ETH “for the next coffee run.”
That was the first time the online world properly crashed into real life for me. Still kinda surreal thinking about it. Now whenever I’m behind the counter I half-expect someone else to walk up and go “hey, aren’t you the guy who found that flash loan bug…?”
Anyway, that’s my “recognized in the wild” story. Still makes me laugh.
English

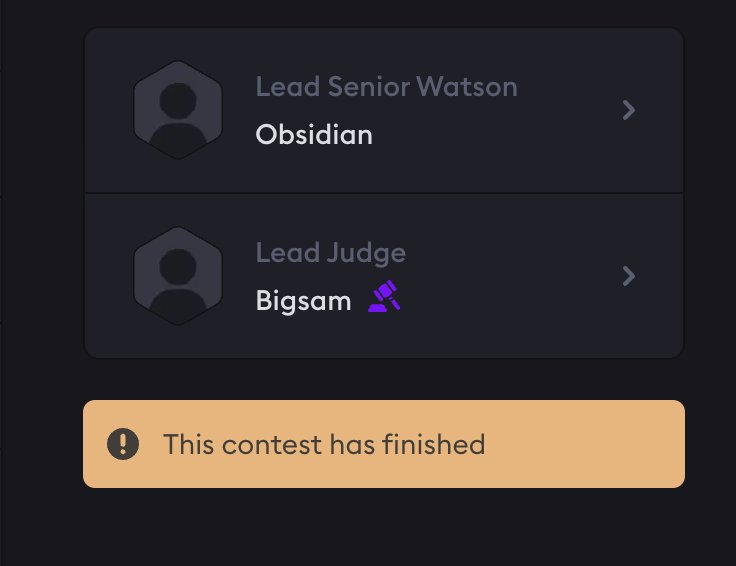
@AmolegbeSamuelT @3janexyz @sherlockdefi Thank you for the job, it was great having you as a Judge on 3Jane contest
English

Recently wrapped up my role as Lead Judge for the @3janexyz contest hosted by @sherlockdefi, and I must say it was quite an experience.
📌 Reviewed the codebase 24 hours before kickoff,
📌 Stayed in close touch with the protocol team,
English
Wang Security retweetledi
Wang Security retweetledi

Based on the engagement that my previous post got, and taking into account some of the comments, I will elaborate on why I said @sherlockdefi is the best competitive audit platform out there (for me at least).
To some people, this choice seems controversial, but hear me out.

English
Wang Security retweetledi

Sherlock AI reported a Critical vulnerability in the @40acresFinance protocol.
The 40acres team generously allowed us to share the details publicly so others can learn from the finding.
Here’s how the vulnerability worked:
First, veNFTs are a special type of vote-escrowed ERC721 tokens that earn weekly rewards.
40acres gives veNFT holders instant access to loans based on their veNFT’s future revenue.
Each borrower’s veNFT sits inside a personal PortfolioAccount that routes functionality through modular “facets” using the diamond proxy pattern.
The exploit allows an attacker to reclaim their collateral (veNFT) from their PortfolioAccount without repaying the loan.
Check out the aerodromeVote() function below. 40acres has a very cool feature that allows borrowers to vote with their veNFTs held as collateral in 40acres.
The function has the following problem: The loanContract address is not validated, allowing a malicious user to specify an arbitrary contract. This contract could be approved to control the veNFT in the PortfolioAccount, enabling its transfer during the vote() call in the malicious loanContract.
Attack Steps
1) Attacker deploys a malicious contract that implements ILoan.vote(uint256) to call transferFrom/safeTransferFrom to transfer the approved veNFT.
2) Attacker calls portfolioAccount.aerodromeVote(maliciousContract, tokenId). The portfolio fallback delegates to the facet, which lacks input validation and calls maliciousContract.vote(tokenId) and transfers the veNFT back to the attacker, even though the loan has not been repaid.
Note: The repetition of the bug causes the lending pool to be drained - doing it once is just taking a loan & stealing your veNFT back.
Impact
Unbacked loans across the system. Any borrower can reclaim their own collateral mid-loan, leading to full insolvency of the lending pool.
Acknowledgements
Thank you to @defsec_, @vinica_boy, and @onthehunt11_ for helping with this writeup.
Important to know: The 40acres team discovered the bug and applied a fix prior to launch
Detected by Sherlock AI
You can see the original issue as generated by Sherlock AI in the next tweet.
The run took 3 hours 59 minutes from start to finish.
Sherlock AI brings security to the development process, scanning commits and call paths early, surfacing high-impact flaws fast, and giving auditors clearer visibility into complex systems. In practice, that means issues like this can be caught and resolved long before audits, bounties, or deployment.
Try Sherlock AI for your protocol today.



English
Wang Security retweetledi

Episode 7 of The Web3 Security Podcast is now live!
This week, @offerijns, the CTO at @centrifuge, joins @jack__sanford to discuss Centrifuge's controversial security methodology, their co-authorship of the ERC-7540 standard, and more!
Full episode below 👇
English
Wang Security retweetledi

Top teams are already starting to feel the impact Sherlock AI can have.
Don't believe us? Ask @offerijns, CTO of @centrifuge

English
Wang Security retweetledi
Wang Security retweetledi
Wang Security retweetledi

If you are interested in understanding how Sui enables executing transactions in parallel, and when sequential execution is necessary and how it is processed, take a look at my article below.
x.com/WangSecurity_/…
Wang Security@WangSecurity_
English

I just got my first top 5 win in my first Immunefi contest 🎉 Thank you to everyone who believed in me.
@spearbit @mikeleffer I’d love a shot at the internship role — I’m ready to learn, work hard and add value.
this is just the beginning 💪
Immunefi@immunefi
The $30K @FolksFinance Audit Competition is a wrap! 🎉 100% of the reward pool has been paid out! 💰 🏆 Top Winners: 1. @pks_eth – $7,308 2. @4mj3x – $4,413 3. danvinci_20 – $2,613 4. @_uhudo – $2,313 5. @0xenzo_eth – $1,308 Congrats to all participants & winners! Your valuable contributions helped strengthen and secure the platform. Check the complete results of the Audit Competition: 👉 #top" target="_blank" rel="nofollow noopener">immunefi.com/audit-competit…
English
Wang Security retweetledi

Contest is already live and I will be the lead judge.
Looking forward to seeing your submissions!
SHERLOCK@sherlockdefi
Stop scrolling, auditors. The next big audit contest is here. 92,000 USDC up for grabs to help us secure @brevis_zk's Pico ZKVM. Starting on Monday, September 1st at 15:00 UTC. Show us what you got.
English
Wang Security retweetledi

ZK Bootcamp Prep: Building a Math Tower
In the following months I will be posting daily updates on my math journey with a clear goal to start @RareSkills_io ZK Bootcamp near the end of the year.
Why?
I believe Zero-Knowledge Proofs are the endgame of web3, the final piece of technology that will allow us to fully transform a web2 world in to a web3 world. The broad application of ZK is become closer and closer as technological advances are made with increasing speed.
Unfortunately, I do not understand ZK. I've read articles, done courses and watched video's, but the mathematical complexity is simply beyond me. This does not mean that I am incapable of learning it, but, as @justinskycak put it so eloquently in his famous article, I currently do not have the right prerequisites to begin learning.
So since last November I have been studying on @_MathAcademy_ I've completed Mathematical Foundations I and currently I'm on 70% MFII. Combined with the math puzzles I encounter in my work as security researcher, I do feel I have advanced enough to start making sense of it all.
But in order to do it correctly, to build a mental tower of math where the ZK concepts can comfortably fit, I still have a lot of work to do.
What?
Mathematical Foundations II (70%)
Mathematical Foundations III
Linear Algebra
This is roughly 10.000 xp. 1 xp takes about 1.2-1.5 minutes, so between 200-250 hours of focused study.
When?
Ideal : 25 Nov ➡️ 107 xp/day
Realistic : 25 Dec ➡️ 80 xp/day
Life happened: 25 Jan ➡️ 65 xp/day
I'll keep you all updated! 😁👊
English
Wang Security retweetledi

Introducing The Web3 Security Podcast hosted by our CEO @jack__sanford!
Each episode will feature leaders from the most prominent organizations in the industry offering insights on security, Web3, and more.
Our first episode with @fredrik0x from @ethereumfndn premieres today!
English