lexi <img src=x onerror=alert(1)>
41.8K posts


lexi <img src=x onerror=alert(1)>
@1lexxi
not around here anymore lol. previous statements may not represent me correctly anymore
it/its | she/her Katılım Kasım 2018
3.4K Takip Edilen1.6K Takipçiler

@Emmett31539642 @nulllzero @iAnonymous3000 > PGP is the oldest and most secure way of comms on the net today. and it has not wained. that alone speaks volumes.
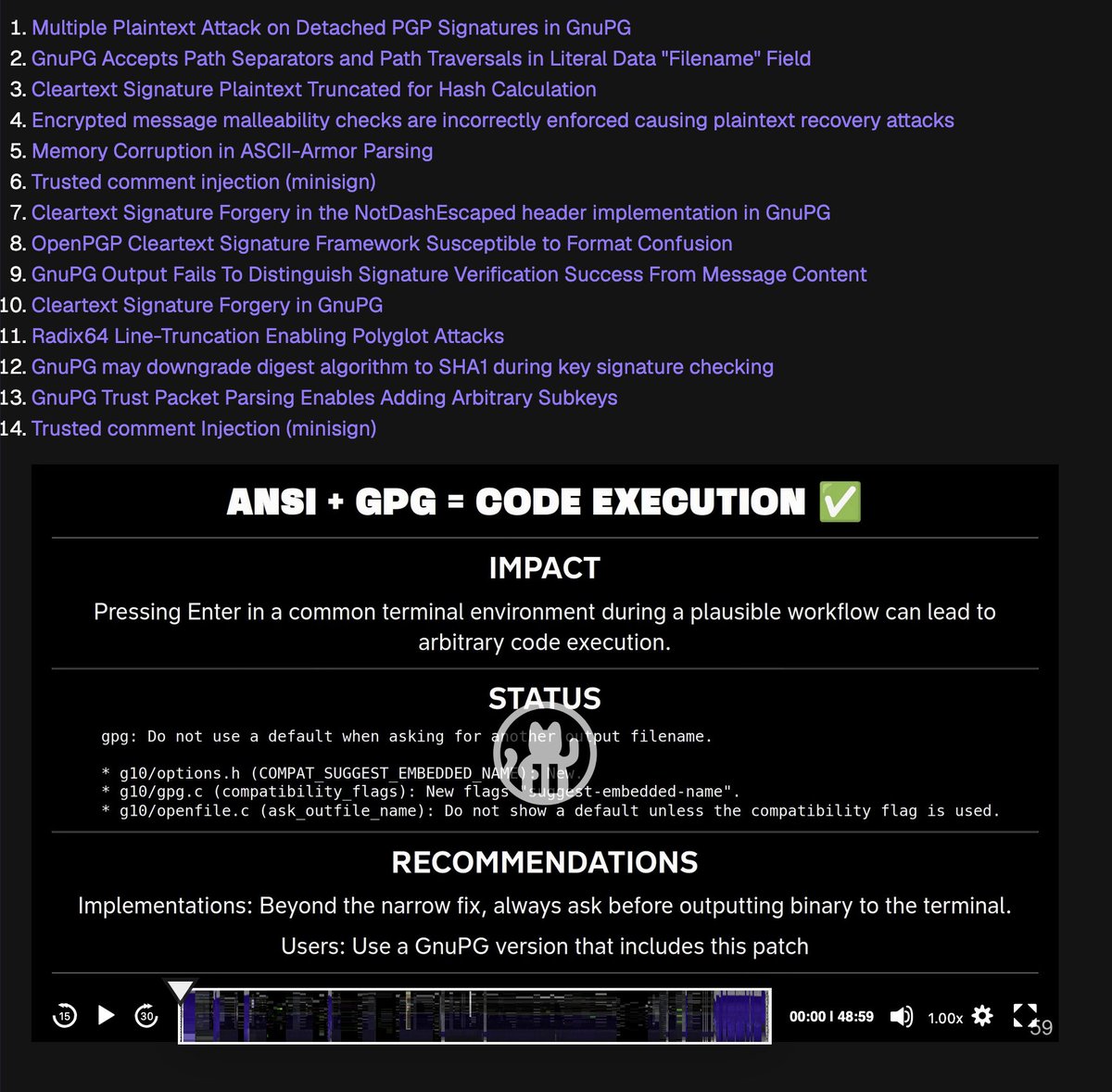
Ironic how you can practically "hack" the most common PGP implementation because PGP, unlike Signal, is dogshit. media.ccc.de/v/39c3-to-sign…
English

I think it has to do more with the encryption as well as being open source. to me, open source is a HUGE mistake. you can have the GPL all you want to but any dev can yank that license at anytime. the simple fact that this huge hack happened on a commercial app speaks volumes and says that even open source w/encryption is not as secure as claimed,
let's take PGP for example, two sides one with the E key, one with the DE key. that method should have been applied to all these damn stupid apps.
Keys are what makes even police comm systems secure with that encryption. People such as @unixpill have no true idea of what secure really means or entails. Plus he doesn't take the time to read EVERYTHING.
PGP is the oldest and most secure way of comms on the net today. and it has not wained. that alone speaks volumes.
English

You don’t need to trust Signal. That’s the whole point.
The protocol is open source. The clients are open source. The server is open source. Independent cryptographers have audited the Signal Protocol repeatedly, and it remains the gold standard for end-to-end encryption.
Signal also supports reproducible builds - meaning you can compile the source code yourself and verify it produces the exact same binary distributed on app stores.
Trust is for closed systems.
English

@RayRedacted held my first big talk at the biggest hacker event in europe on the biggest stage a few days ago (about the gpg dot fail research project) as well. mindblowing experience. can only recommend holding infosec talks, life changing stuff
English
![Ray [REDACTED]](https://pbs.twimg.com/profile_images/2020833070715154432/kaOg1Zon.jpg)
I have literally watched this guy's career rocket from wanting a good infosec job to OMGAreYourFrickingKiddingMe .
I gotta admit that I am extremely proud of my minibar analogy, too. Its at https colon slash slash redact dot link slash minibar
KL4R10N (Previously S4T4N)@KL4R10N
In 2021, I was very skeptical about submitting my first CFP, and @RayRedacted pushed me to just do it. Before that, I didn't know him personally. But from that day onwards, He has been my undeclared mentor.
English

@schwabbler @crackticker ueber die hater wird auf dem private account boese boese woerter gedroppt
Deutsch

vouch btw, 49016 war locker ne woche am stueck bei mir in der crib und hat sich ueber gnupg fuer stunden am stueck den kopf zerbrochen um die mutter aller payloads zu bauen. kein ai gesloppe.
️@crackticker
bra leugnet er die vulns oder spricht er ihnen ihre kritikalitaet ab
Deutsch

@frogmoney420 at gpg dot fail 🤑💸💰🪙💳💱💲🧧💵💴💶💷🫰💹
English

@esoesnulo @awawawhoami important correction: \0 string confusion*s* in the big 2025. in multiple tools 🥀💔
English

i highly recommend watching at least the first few minutes of the talk just to get an idea of the impact
maia arson crimew🐈🐾🏴@awawawhoami
English

@vmfunc @awawawhoami only reachable via c3 dect, ruf mich an aber nur ueber pgp
Deutsch

@1lexxi @awawawhoami !!
do u have signal or a platform where i can message you?
English

@vmfunc @awawawhoami conceptually yes, but different concrete bug. also fun fact we also found a bypass for double-incrementing (and potentially overflowing) the literals_seen counter and that was also a wontfix :D
English

@1lexxi wait correct me if i'm wrong but the detached sig attack is conceptually the same class as the 2007 core security unsigned data injection vuln? gpg "fixed" that by limiting to one message per run but the underlying problem (verification and output are separate codepaths that can desync) was never architecturally solved
17 years later same bug class different packet arrangement??
English
lexi <img src=x onerror=alert(1)> retweetledi

s/o @1lexxi who managed to pay someone to smuggle them from the US as a gift for the gang
️@crackticker
my chud children
English

@RossComputerGuy @grhmc BTW git signing using GnuPG looks fine *for now* (check out git cat-file -p). Basically anything in detached mode (so separate asc sig file) is probably not vulnerable to this particular fresh hell.
FWIW I was able to spoof a clearsign I made a while ago, with a mod to the PoC
English

Ho ho ho merry Christmas. It’s “Don’t use pgp etc.” Santa paste.debian.net/plainh/97923151
English

@HSVSphere you're gonna enjoy that talk lmfao
English

I was right, btw.
==> gpg[dot]fail
Many 0days in GnuPG, very likely.
HSVSphere@HSVSphere
"GnuPG is a C codebase with nearly no tests, no CI pipeline(!!), an architecture that is basically a statemachine with side effects, and over 200 flags. In my experience, only people who haven't experienced the codebase speak positively of it." Stop using GnuPG and use Sequoia.
English

@HSVSphere @dpc_pw hi yes author of the talk here. please for the love of god stop using pgp and if you must use sequoia; i personally have worked on better hardware support (#note_2861549967" target="_blank" rel="nofollow noopener">gitlab.com/sequoia-pgp/se…). you can already use your yubikeys with rust only software today (even though it's still alpha)!
English