himanshumonu
97 posts



Controversial take: AI is making bug bounty both better AND worse at the same time.
Better: faster recon, pattern recognition, report writing
Worse: noise from script kiddies running AI-generated scans, more dupes, lower signal-to-noise
Where do you stand? Is AI net positive or negative for the industry?
English

@EvanKlein338226 keep sharing your thoughts. these are very helpful.
English

@EvanKlein338226 rate limit bug not accept by programme, password change doesnt invalidate session.
English

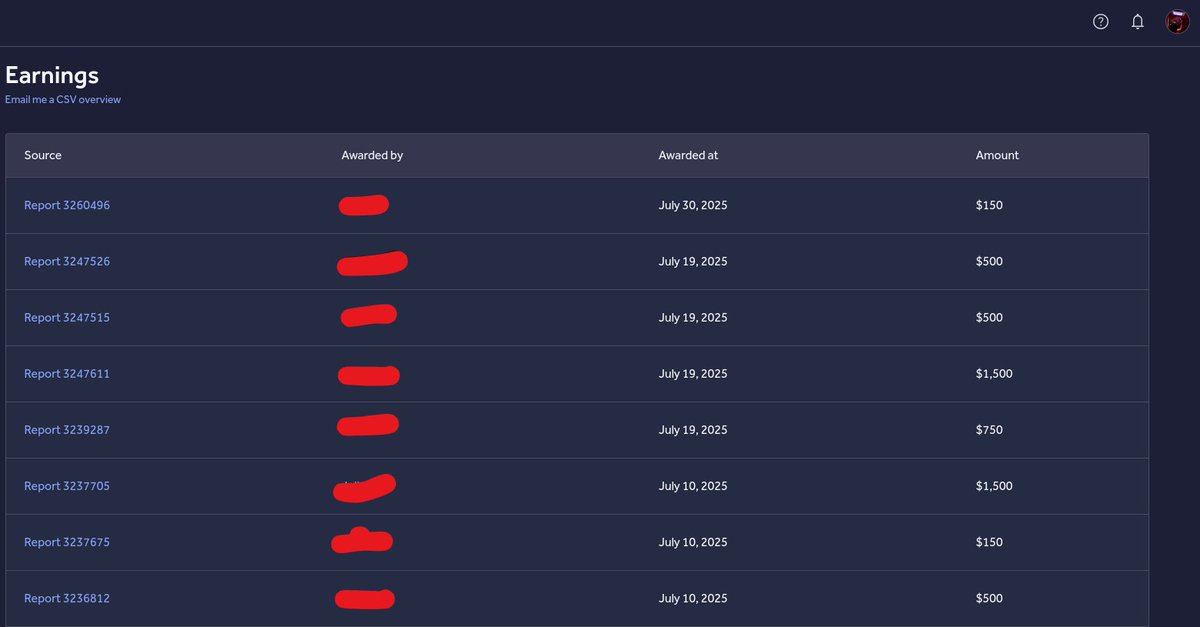
Several reports submitted this month were paid out today, with more still under review and pending bounty.
#BugBounty #CyberSecurity #InfoSec #SecurityResearch

English

@suslu7616 bro you work for vieh group ? your payload is using by vieh group
English

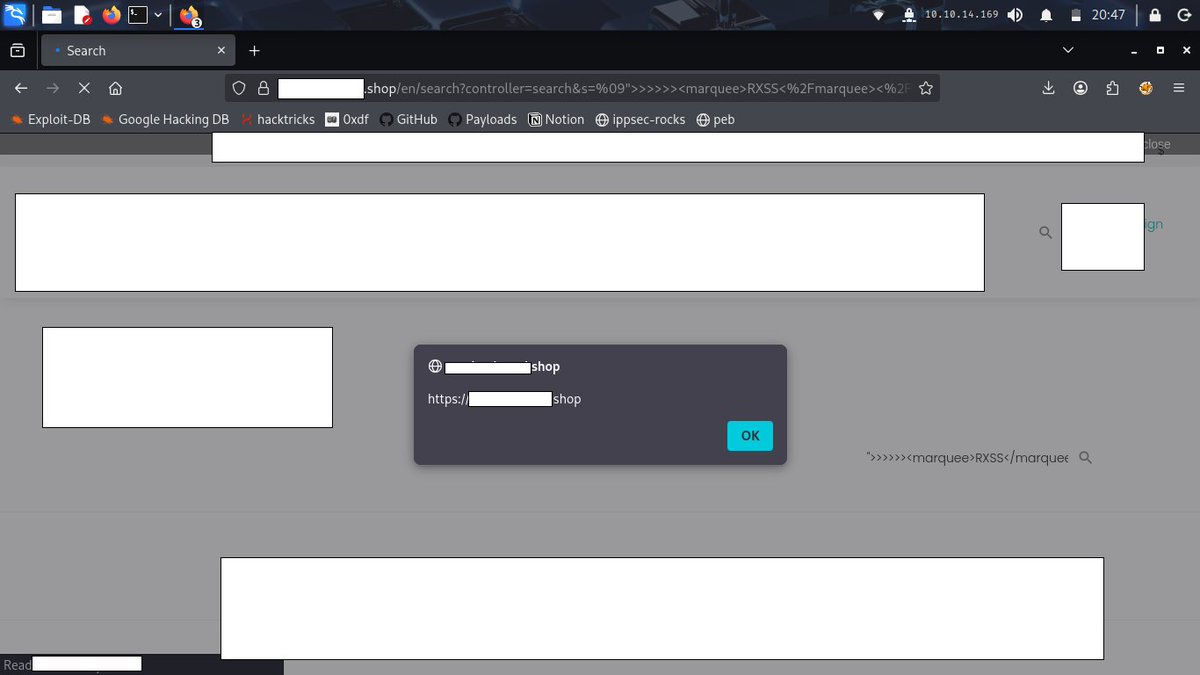
I found #xss on #ecommerce site.
Payload; ">>>>>><marquee>RXSS</marquee></head><abc></script><script>alert(origin)</script><meta
How do you increase the impact?
#bugbounty #xss #cybersecurity #websecurity #infosec #redteam #AppSec #hacking #cybersecuritytips #bugbountytips
English

@Atomsmade @Behi_Sec this is my github dork { AWS_SECRET_ACCESS_KEY org:organization name
"target" "password/email":
"api/v1/users" "example.com" }
English

@Behi_Sec I choose target, i run katana and start finding endpoint,api keys leakage in js files, 2nd step fuzzing using ffuf, 3rd step waybackurls. after this i change my target and repeat these steps. what is your approach when you hunt on a target ?
English

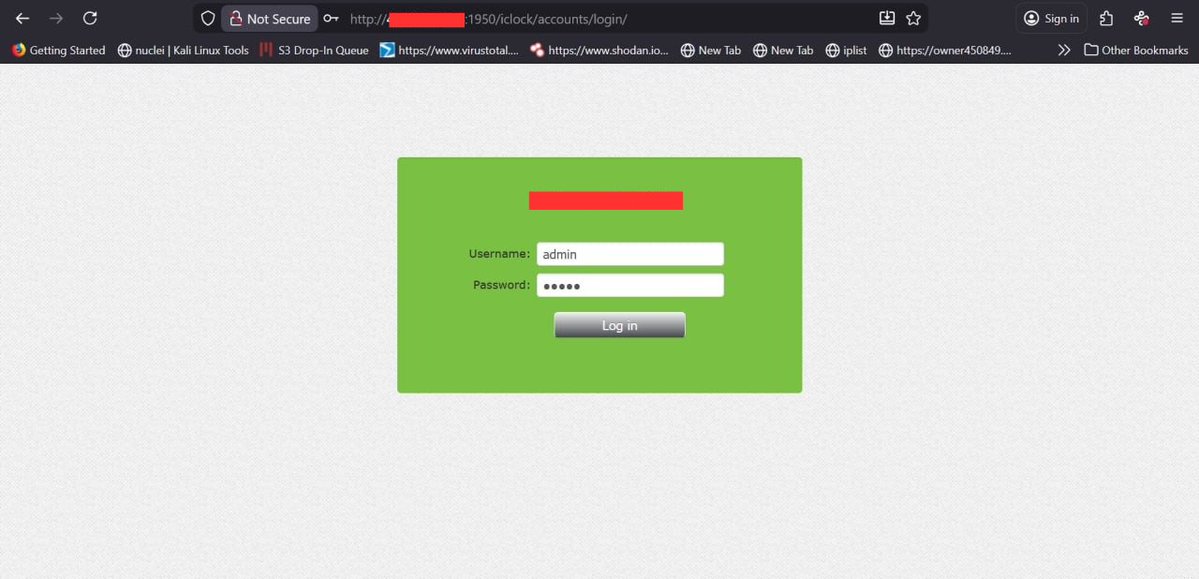
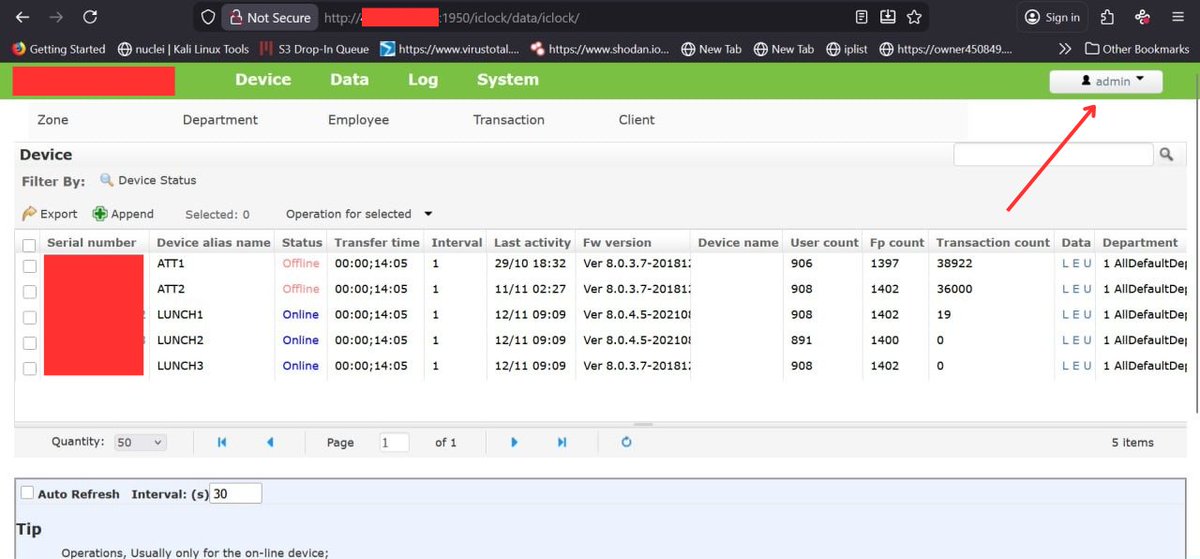
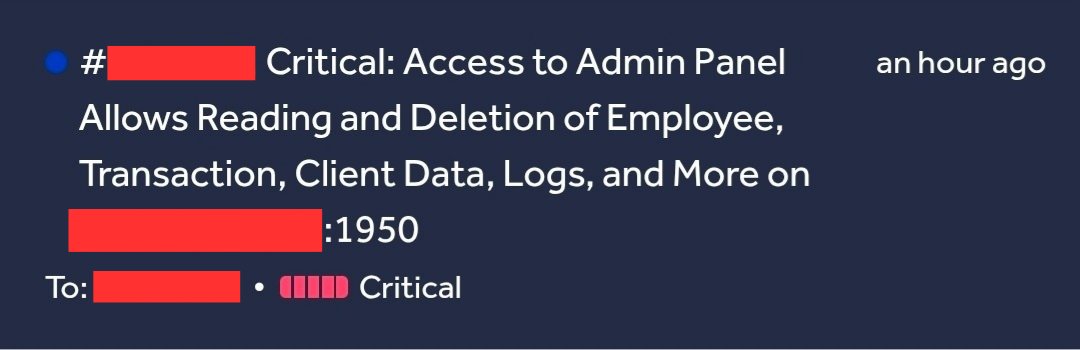
Admin Panel Access Scenario I Found
• During recon I found a domain with an empty main page
• Port scan showed 1950 open
• Visiting example.com:1950 revealed an admin login
• Default creds worked and gave full admin access
#CyberSecurity #BugBounty #bugbountytips
English

@Behi_Sec tell about user registeration asking phone number and verify code on that number. we dont want to share our phone number. what you do in that case
English

@ghost__man01 @AxosBank Bhai tum self hosted program pe hunting karte ho ya phir h1,bugcrowd.
English

Hey @AxosBank, I want to report a vulnerability on your website. Please guide me how can I report it so that your customers remain safe and trustworthy of their data.
Thanks.
#BugBounty
English

@Behi_Sec Just share all important things related to access control
English

In July, I submitted 40 vulnerabilities to 5 programs on @Hacker0x01. #TogetherWeHitHarder hackerone.com/last-month
English

In July, I submitted 10 vulnerabilities to 1 program on @Hacker0x01 and get paid 5,550$ in bounties for 8 reports #TogetherWeHitHarder hackerone.com/last-month
English

