Sabitlenmiş Tweet

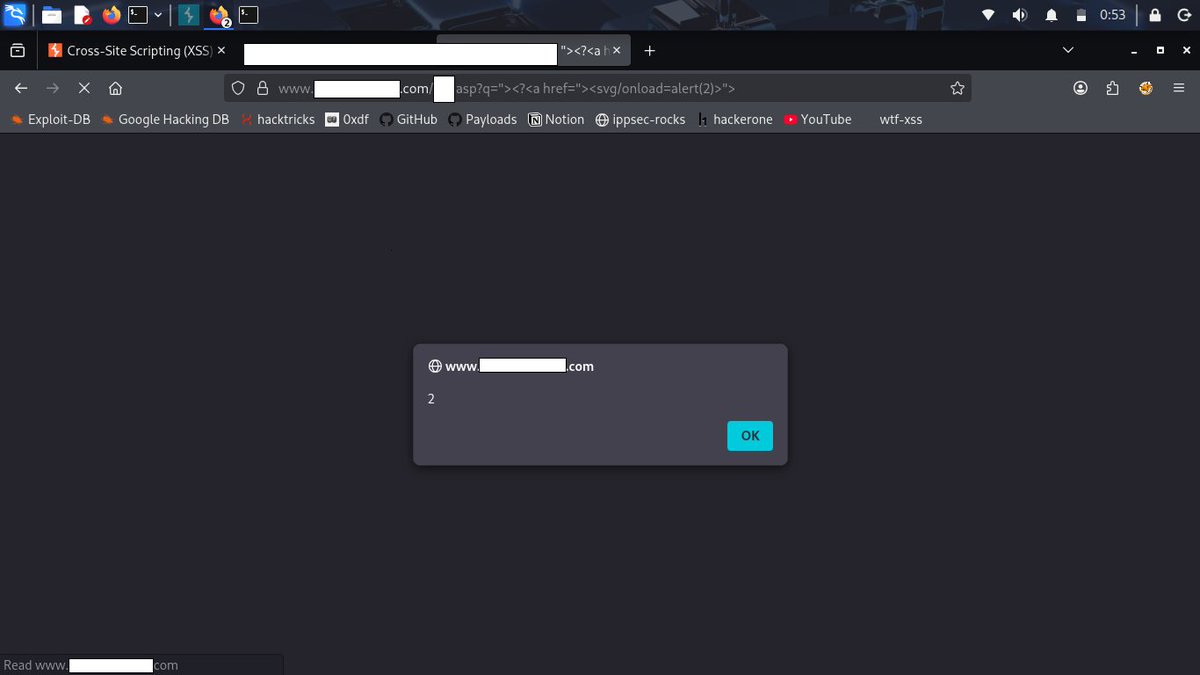
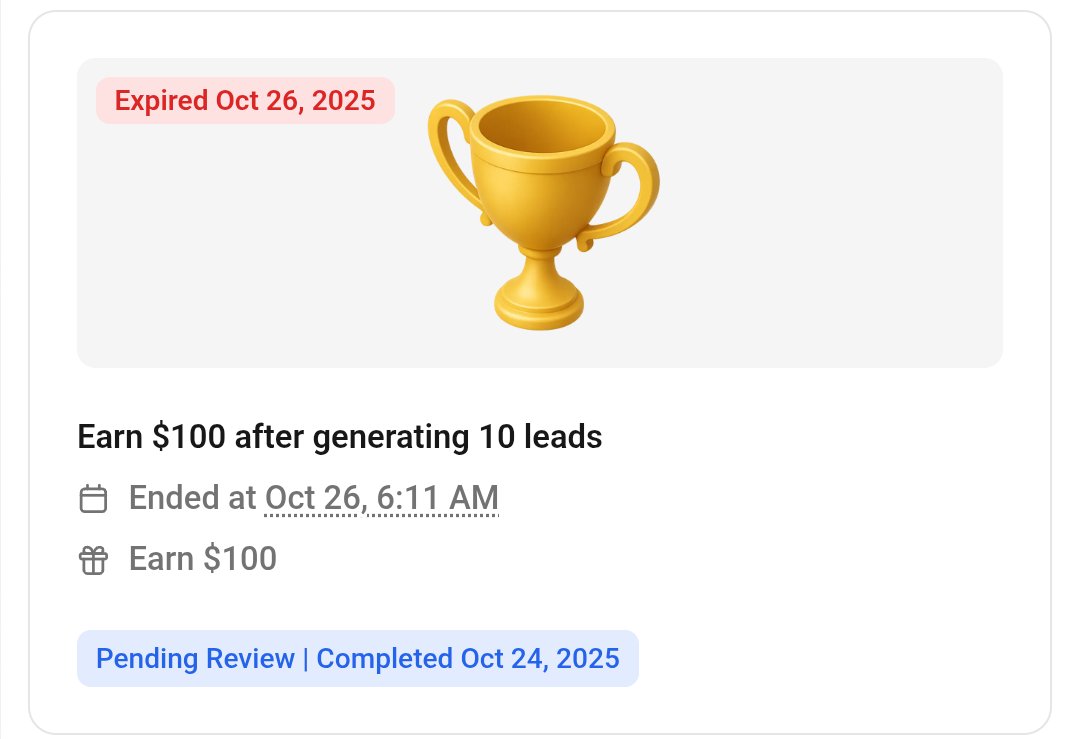
Happy to be listed on @Flipkart Hall of Fame. Write-up will be👇
ghostman01.medium.com
flipkart.com/pages/security
#bugbountytips #bugbountytip #BugBounty #BugHunter #appsec #vapt #pentesting #cybersecurity #cybersecurityresearcher #securityresearcher #hacking #PenetrationTesting
English