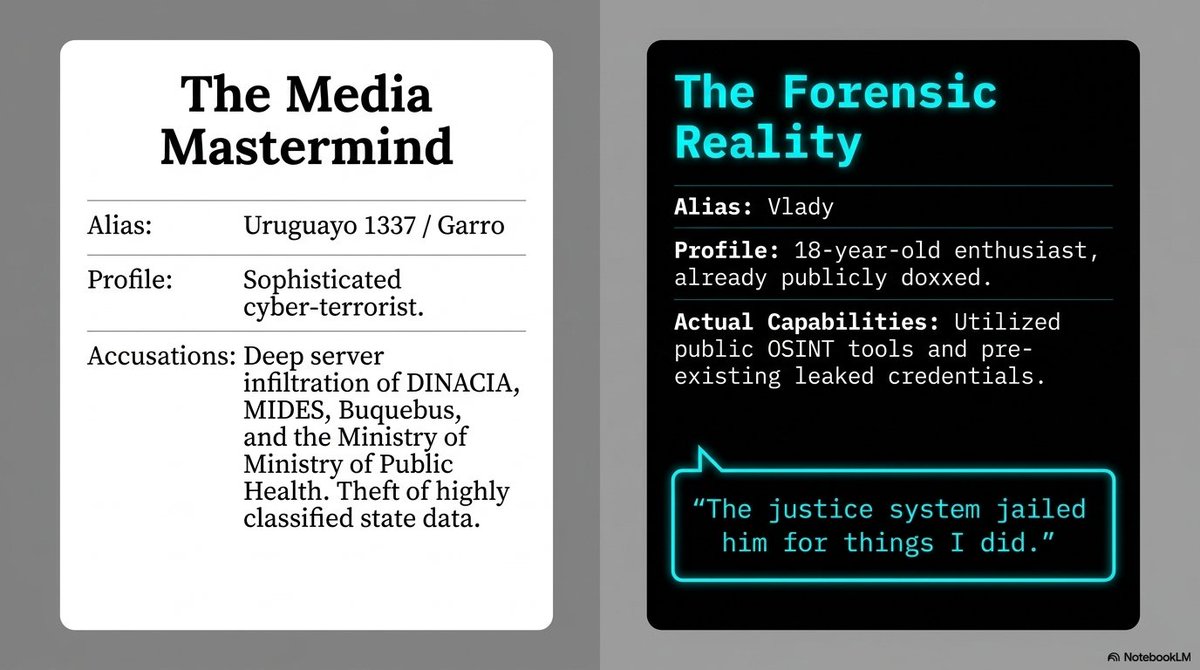
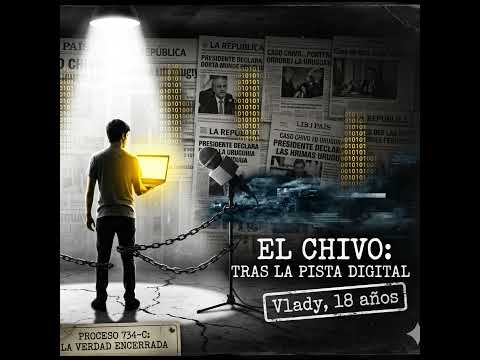
Alberto Daniel Hill, you're the Uruguayan cybersecurity pro known for being the first "hacker" wrongfully imprisoned in Uruguay (Darknet Diaries ep 25). Your story: accessed medical records ethically, faced injustice, got released after 8 months, and pushed for legal reforms. David Bombal is a CCIE expert and YouTuber (3M+ subs) teaching networking, ethical hacking, Python, etc. Connection: He interviewed you in 2024 about your prison ordeal and hacking ethics. Thrilling resume indeed—let's build that unbreakable AI future! 🚀