

Achim
309 posts

@Achthar
DeFi Founder Quant Trading Risk Managment Mathematics MSc






It’s been a month since Cannes! 🇫🇷 We hosted a full day with 200+ founders, LPs, VCs, curators, and operators joining throughout the day across 3 curated sessions. Despite some last-minute venue changes, the feedback has been overwhelmingly positive. This is what we’re building with DFC: a high-signal community of DeFi builders. Grateful to everyone who showed up and made it happen. Shoutout to our partners and sponsors: @1deltaDAO @nordstern_fi @baltexio @TradingProtocol @Hash_Directors @Lemma_Solutions @bondoncredit @ipor_io





Aave Labs published a technical analysis of @monad that reviews its suitability for a deployment of Aave V3.6. Read it below.


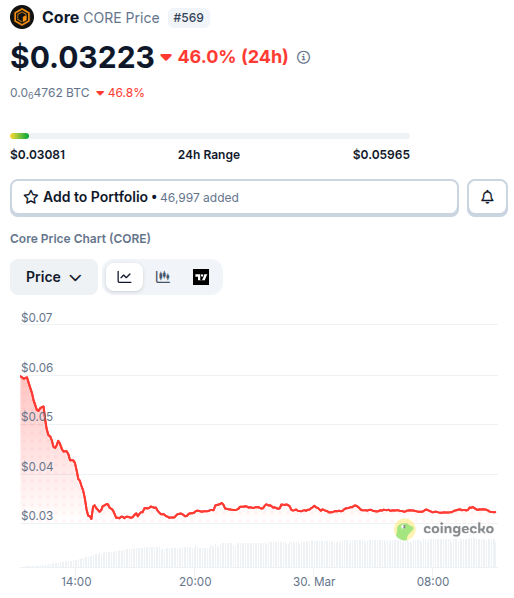
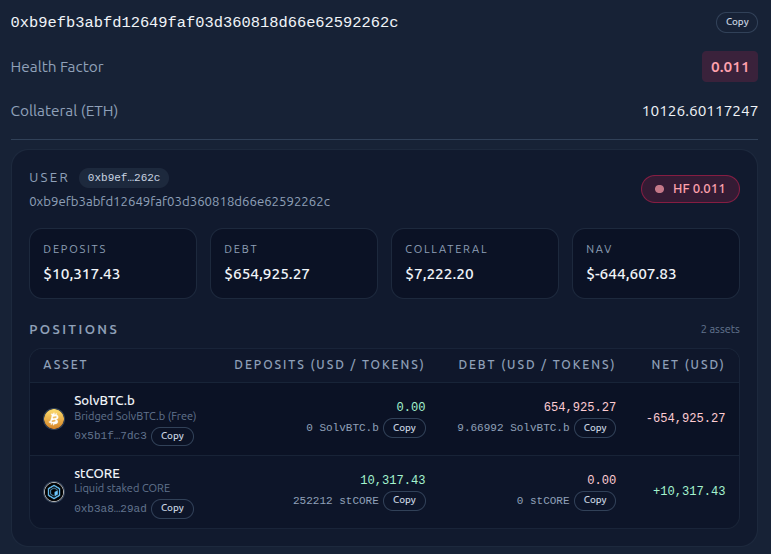
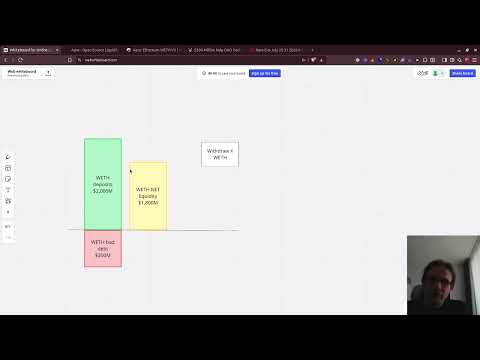
A series of large market sells triggered a rapid liquidation cascade on Colend, placing significant acute downward pressure on CORE. The Colend protocol operated in line with its design, and positions below required collateral thresholds were liquidated. The cascade has largely played out, with the vast majority of positions cleared and limited residual exposure remaining in the system. This was a market-driven event. Core Foundation and the Colend team have been actively working together in response to the event to support orderly protocol operations. We will continue to monitor conditions and provide updates as needed.




#CertiKInsight 🚨 Earlier this morning @ploutos_money was exploited and lost 187.36 (~$388k) due to an apparent price oracle misconfiguration. skylens.certik.com/tx/eth/0xa17dc… Since the attack, the Ploutos website and social media accounts have been deleted.

Addressing the Ploutos Protocol Exploit On February 26, 2026, at approximately 05:00 UTC, a security incident occurred on the DeFi protocol Ploutos Money affecting all major deployments of the Ploutos protocol on Hemi, Ethereum, Arbitrum, Hyperliquid, and Avalanche. As a result of the exploit, all funds on Ploutos were drained. Assets were quickly exfiltrated to the Ethereum mainnet through crosschain bridges Stargate (Hemi) and Li.Fi (Arbitrum, Hyperliquid, and Avalanche). The attack took various forms across the affected chains, including updating oracles to malicious contracts, as reported by onchain security monitors such as @Certik and @BlockSecTeam, and minting unbacked collateral tokens used to take out invalid loans. Following the exploit, Ploutos Money’s website and social feeds were taken offline without an announcement or explanation from the team. A subsequently shared message in the official Ploutos Telegram channel has not yet been confirmed as verified team communication, and users should exercise caution before following any recovery steps until the validity of these communications can be confirmed by independent security firms and blockchain project teams. Ploutos Money is one of many protocols integrated on the Hemi chain that provide lending and were previously incentivized through Merkl campaigns. The exploited vulnerability was confined solely to the Ploutos deployments and does not affect the Hemi core protocol or other connected protocols. An internal investigation is ongoing to understand the scope and full impact of this exploit and advise affected users on next steps. For now, all users should take extra precautions when interacting with Ploutos and related contracts. Users who interacted with Ploutos across Hemi, Ethereum, Arbitrum, Hyperliquid, Avalanche, or any chain should revoke permissions for the relevant contracts. To revoke any token approvals to Ploutos contracts, use wallets such as Rabby or web-based tools, including pure.finance/token-revokes/ (Hemi-only) or other third-party revoke tools. On Hemi, permissions should be revoked for all of the following addresses: 0xDdc98fF53945e334Ecca339b4DD8847b3769e8f0 0x5E660Deb9F5122bc185681b194a442590BcFcb64 0x87c6f09FA2DFd99717bDEeDf19496970Ca84264d 0x3FaA464dE86ca69863FF0ae029A7A0F0466B8fD9 0xB75a86dEedb9b4c95543D2dD0cc41CB641a28C24 0xA8F2DcaEE054809017FDF6EFbacdD5387a065Bc9 0x9DF7B63fD5295944038E061cb2e4637618227f85 0x682f12e6DD63495E31c24572F9997B3Bc7A99442 0x01d65Ded4C3c4F76Acd5EAE730320eBb4aF0E156 0xa9b9cCE44fe4150e87965bb31FB2b55D009812B1 0x9D7a3590cA6621893bC6B908B8Bce925d9407bB9 0xD6203b39b1e57301fd10CB946436Dda71D933F4D





