Sabitlenmiş Tweet
Al-Pharaday
1.2K posts

Al-Pharaday retweetledi
Al-Pharaday retweetledi
Al-Pharaday retweetledi
@vxunderground "This is a Chromium thing"
Check it with @brave, it is based on the Chromium open-source project. It is technically a "fork" of Chromium.
But only 'technically'.
English

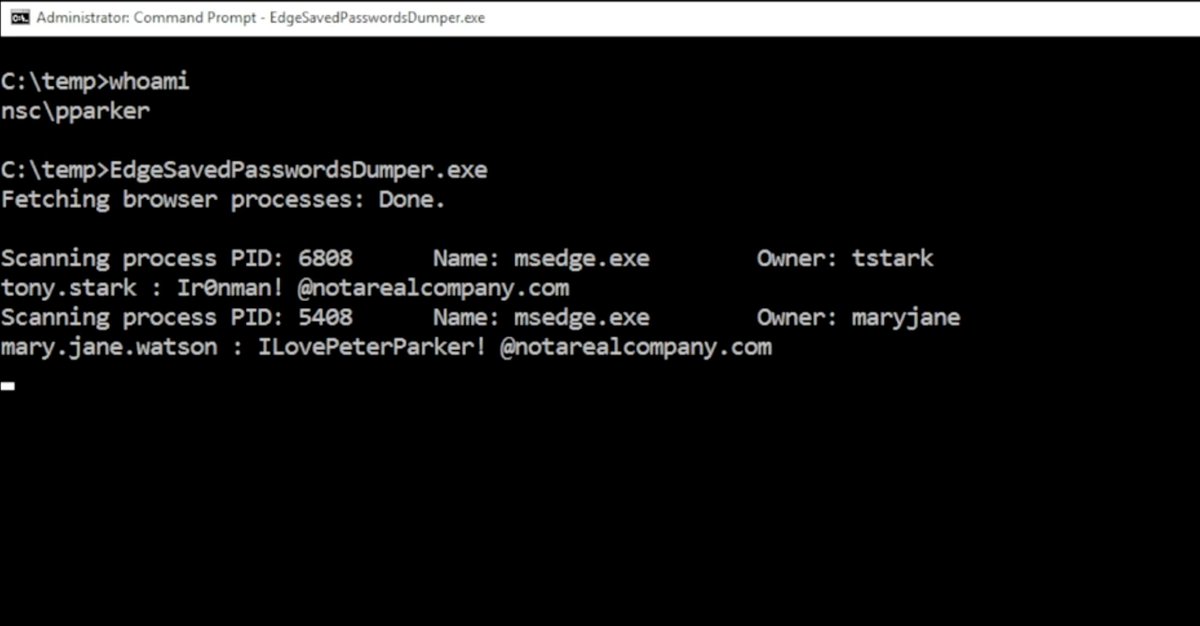
The initial proof-of-concept was released in C-sharp.
Using this method to dump credentials is iffy because it requires administrative access and some security access tokens which can raise some flags.
First, Edge is Chromium based. This is a Chromium thing but (if my memory serves me correctly) a unique attribute to Edge exclusively. However, because it is Chromium based this may impact other Chromium bases. It requires more investigation. Edge is a primary target because it's the default Windows browser and used in enterprise environments.
Secondly, as far as malware goes, this is yet another method to potentially dump credentials on a home users machine. There are a few different ways. This method doesn't surprise me. However, successfully using this method is an enterprise environment would be difficult to use. It would require administrative access and some security access tokens which would immediately raise some flags.
In other words, this method is interesting, I like the research performed, however it isn't something super super critical. If you're using this method in an enterprise environment then that company has been completely compromised down to the bone and they've got much larger issues.
The code and research is really cool though. I just wish it wasn't written in C-sharp (I have an irrational disdain to .NET, especially lately).
International Cyber Digest@IntCyberDigest
‼️🚨 Microsoft calls this "intended behaviour," so here we go. How to dump the credentials of every user stored in Microsoft Edge: 1. Open Edge. Don't browse anywhere, just open it. 2. Flip to Task Manager, find Edge, expand the task. 3. Highlight the "browser" sub-task, right-click, and choose "Create Memory Dump." 4. Open the dump file and look for credentials. The logged-in Windows user can dump every stored Edge credential with no additional rights. Which means any malware that user executes has those credentials for the asking. Thanks to Rob VandenBrink at SANS: isc.sans.edu/diary/32954
English
@LundukeJournal @Cloudflare @ubuntu And what isues do the islamists have with Ubuntu? Age verification and sh't?
English
The Islamic terrorist group, 313 Team, has announced that they have ended their “5-day attack” on Ubuntu Linux infrastructure.
The Iran & Palestine aligned Islamists have also announced that they intend to target @Cloudflare servers in retaliation for assisting @Ubuntu.
“Cloudflare intervened and prevented our attack. Therefore, Cloudflare servers should expect a devastating attack that will target their servers.”

English
@GunloverClub1 Could be helpful against Big Boys in bullet-proof vests travelling in armoured vehicles. Right through the windshield.
English
@IntCyberDigest @L1v1ng0ffTh3L4N My Windows distro has never had Edge by default, and therefore requires a usb stick to load browser installers. Only @brave or Zen or nothing.
English

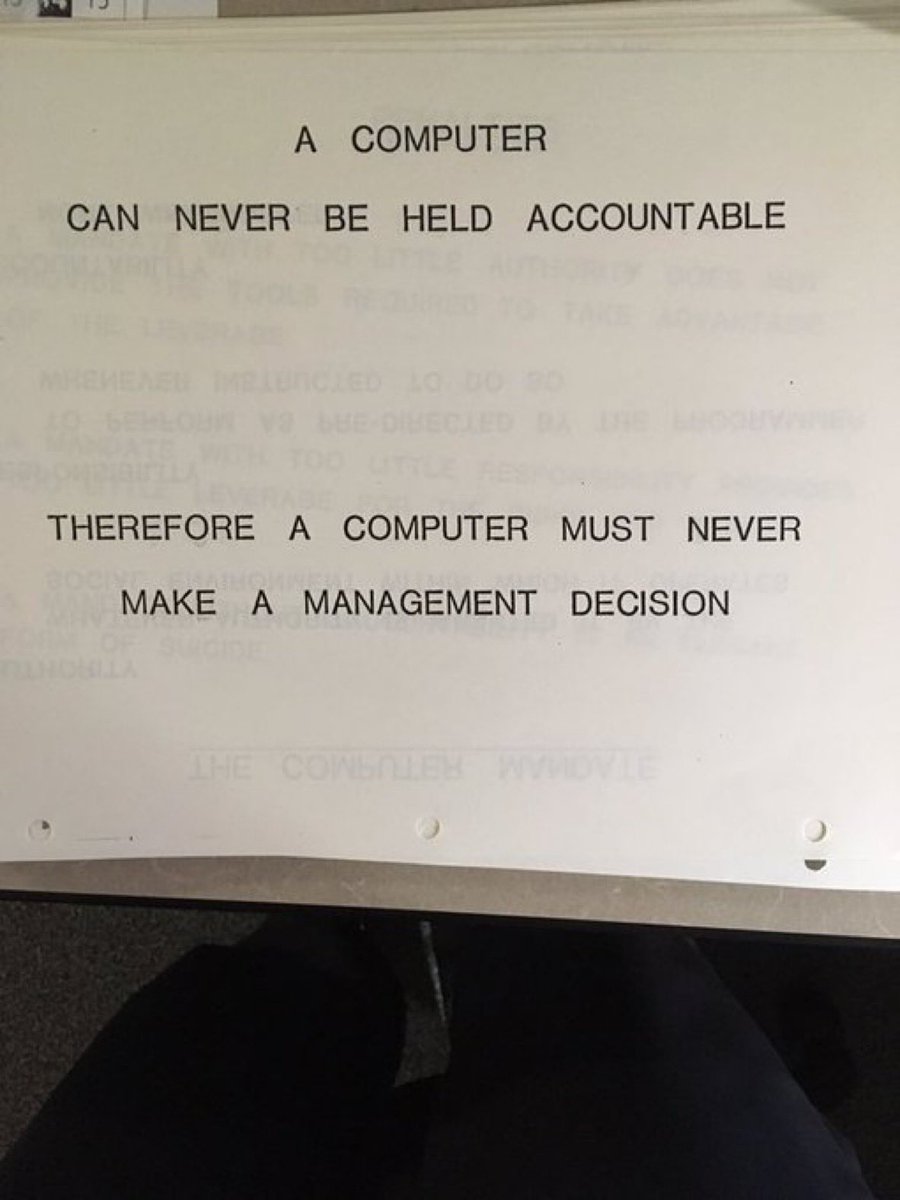
❗️🚨 Microsoft Edge keeps every saved password in process memory as cleartext from the moment it launches. Microsoft's responsed when reported: "by design."
All of them. Including credentials for sites you won't open this session.
Researcher @L1v1ng0ffTh3L4N tested every major Chromium browser. Edge is the only one that behaves this way.
Chrome decrypts credentials on demand, and App-Bound Encryption locks the keys to an authenticated Chrome process so other processes can't reuse them.
In Chrome, plaintext surfaces only during autofill or when a password is viewed, making memory scraping far less useful.
What makes this extra weird is that Edge still demands re-authentication before revealing those passwords in its Password Manager UI, while the same browser process already holds every one of them in plaintext.
In shared environments, this turns into a credential harvest. On a terminal server, an attacker with admin rights can read the memory of every logged-on user process. In the published PoC video, a compromised admin account lifts stored credentials from two other logged-on (and even disconnected) users with Edge running.
Microsoft's official response when notified: "by design."
The finding was disclosed April 29 at BigBiteOfTech by PaloAltoNtwks Norway, alongside a small educational tool that lets anyone verify the cleartext storage for themselves.

English
Al-Pharaday retweetledi

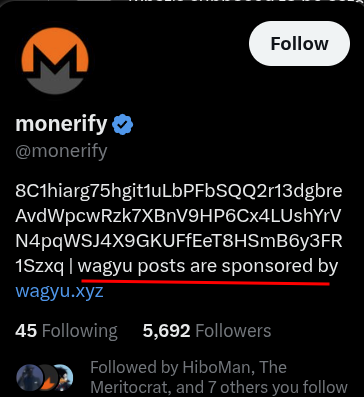
I had a friend who tried secretly using Monero.
It was discovered he had embedded his “stealth” address inside a CPU mining malware binary that ended up being decompiled.
The same “stealth” address he used to accept normal payments thinking it was adequately private.
Seth For Privacy@sethforprivacy
If you only knew how many of your favorite maxis are secretly using Monero, running nodes, etc 🫣
English
@senatorshoshana If a third of kids know how to bypass the restriction, the other two thirds will learn from them. A perfect way to raise a generation of rebels. It'sfascinating to watch the System cutting its own head in real time. 🏴☠️
English
@DoingFedTime @Sovereign_Matt @Kushed_Crypto A behavioral pattern that could be predicted by any profiler.

English
@DoingFedTime @Sovereign_Matt @Kushed_Crypto The dude has said enough to expose himself to any rookie profiler,l bickering with you here.
English
@CollinRugg Step 2: he will need an army in case another king decides to seize his land; it can be conscripts (if there're any) or mercenaries (requires lots of money). If nobody is to attack him since he's under the protection of an outside force like the government, then he is not A King.
English

Self-depicted King of Switzerland is steadily growing his own ‘empire’ thanks to a legal loophole.
Jonas Lauwiner has acquired more than 110,000 square meters of land for free.
According to The Times, Lauwiner has acquired 148 bits of land and 83 sections of road in Switzerland thanks to the loophole.
“I am fair. I don’t shut the roads and I do not charge much for them. [I make money] by selling the right to construct near my road and I sell the right of passage if there is a new house,” he said.
The 31 year old calls his “conquests” a “military campaign,” that are carried out digitally and “without bloodshed,” according to the outlet.
The loophole, under Swiss law, allows anyone to acquire land for free if it is registered as ownerless, by making a claim to the local council.
Video: The Times.
English
Al-Pharaday retweetledi

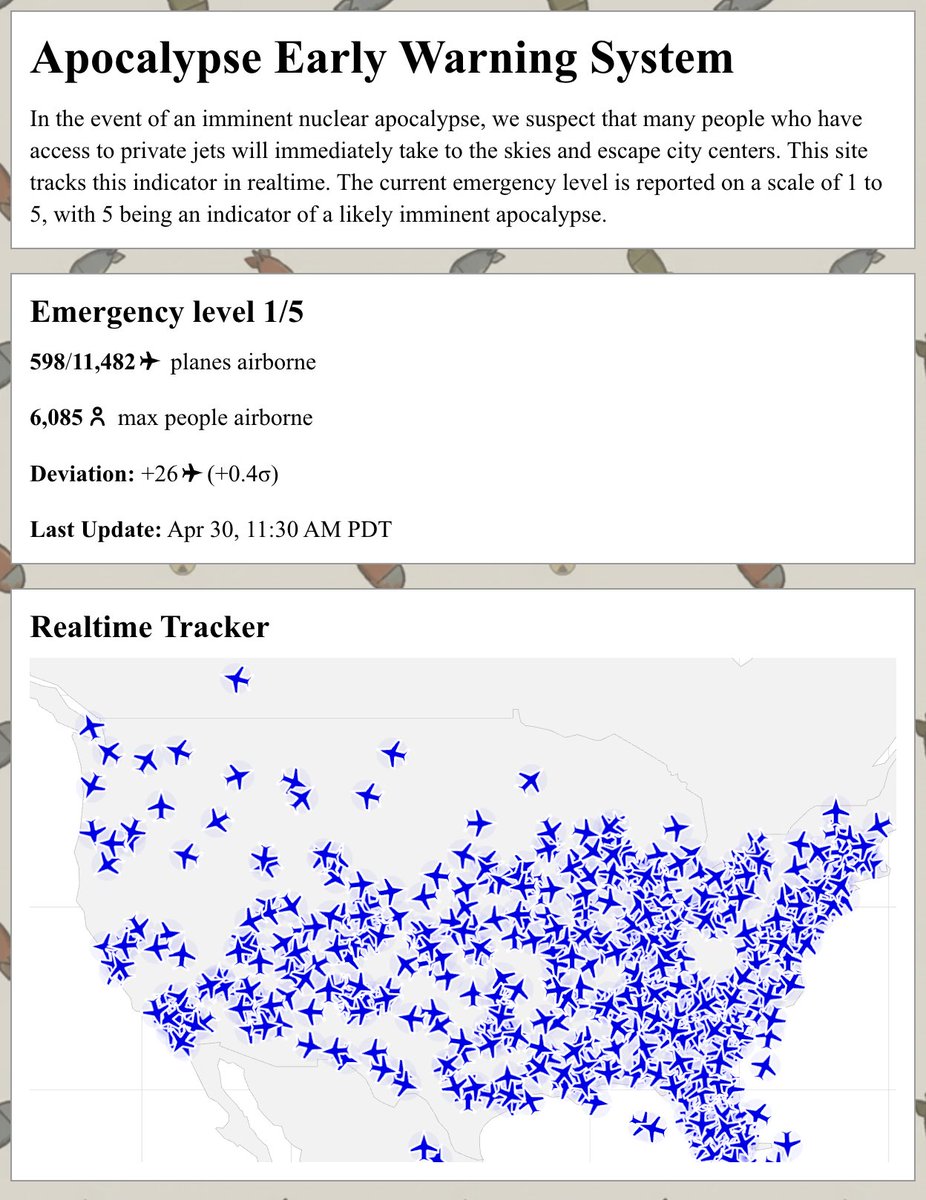
i made an app for tracking whether the oligarchs are actually fleeing city centers ews.kylemcdonald.net
English
@kcimc If you have access to flights data of this sort, you actually can track figures of authority irt, right?
Btw, during a massive thermonuclear strike critical systems on board of an aircraft are supposed to stop operating. Why would they choose to meet their end while on high?
English