Ali Azam
581 posts


Ali Azam
@Ali2251
Founder and CEO @ Canary / ex Vp of eng @ Ondo https://t.co/aFxuQ6Hcaf

LayerZero is being used to launder proceeds from the Layerzero/KelpDAO hack. $500K was just moved via LZ. Address: 0x4D5A08A96D644d7CA7F4541E1512a53D55aA5842 Destination: TLTCf565jGgSeCsUhBpWuPhrrHcGGX9ekT 🚶🚶




Out of an abundance of caution we are temporarily pausing our LayerZero OFT bridges until the root cause of the rsETH incident has been identified. We will provide updates on this temporary pause as we receive them.







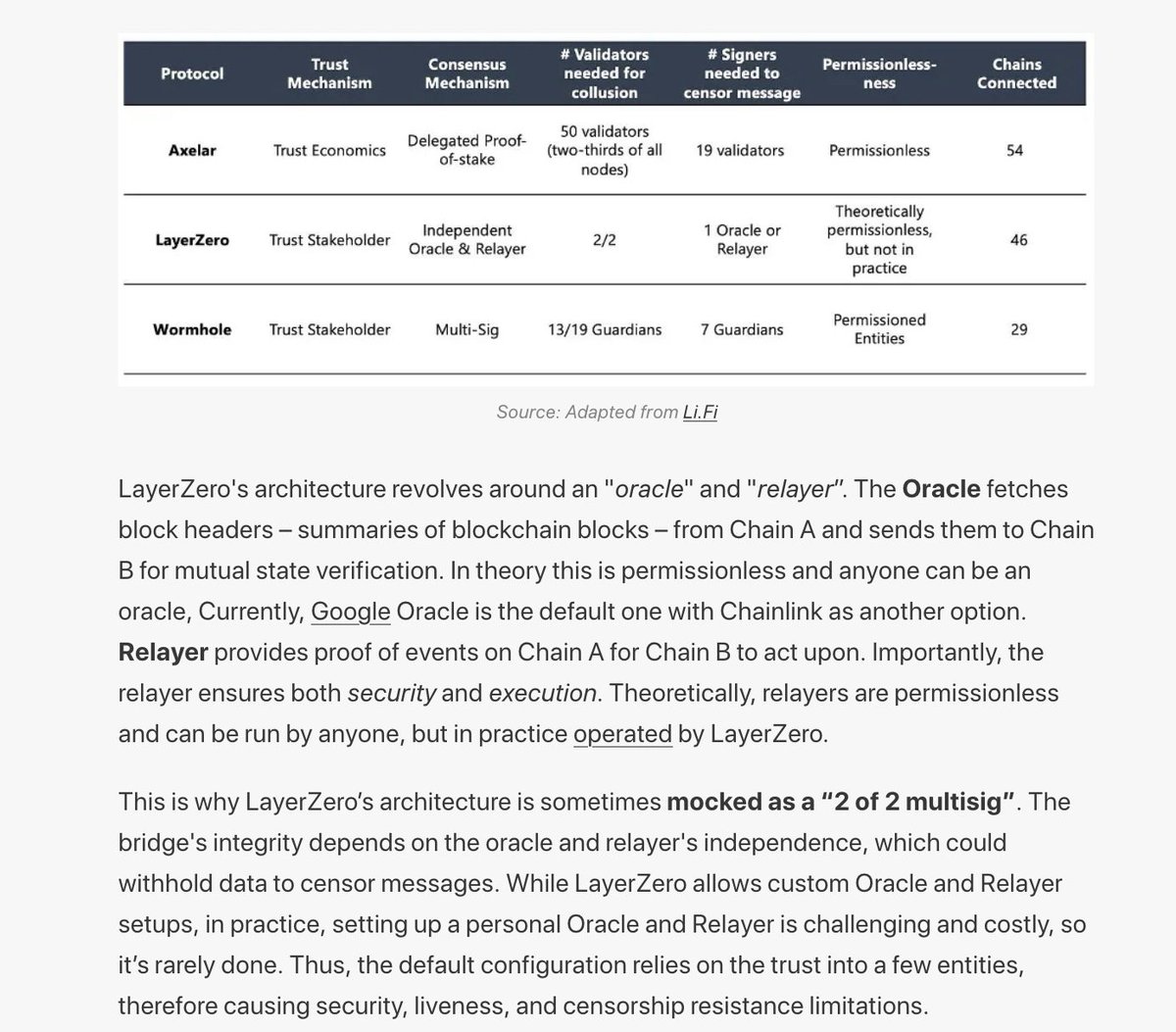
@syvxbt USDT0 is not running on a glorified multisig. We run a 2/2 DVN set up with custom code built to withstand exactly this incident. Also: until you know the root cause of this, its totally stupid to even reccommend other solutions that may be exposed to a similar exploit path.




Agree with this and would also encourage all asset issuers to consider rate limits at the mint & redemption level, as well as a custom rate limit configuration on top of LZ OFTs. We built a solution on top of the standard OFT to throttle cross chain transfers at $10m per hour for every DVN, in addition to the $10m per block rate limit on the mint contract. The former would have prevented Kelp, the latter Resolv. In a disaster scenario where the LZ DVN is compromised you can at least contain the damage to $10m per chain per hour before stepping in to shut down transfers entirely. Yes it’s a slightly annoying inconvenience for users 99% of the time, but a worthwhile trade off to avoid going to zero. If you would like support on adding the same custom OFT configuration please reach out directly to myself or the team.
Feels like pooled lending protocols would benefit from a rate limit on the supply of an asset being deposited for collateral Like, if the current supply is 100m and the supply cap is 300m, the supply should only be allowed to go to 110m in the next 10 minutes. Nobody needs to deposit all 200m in one shot This matters because if/when an exotic asset is hacked, the impact of the hack is constrained by the size of the exit paths for that asset. Especially when you consider that many hacks are infinite mint bugs… there the size of the exits literally determines the size of the hack. Lending protocols are often the largest exits (DEX liquidity is usually pretty small). Having a “smart cap” that is a bit above current supply, which can adjust over a few hours to the true cap, would make a huge difference. It would have saved rsETH depositors $200m today This also raises an interesting point: asset issuers should want this too. If you are an asset issuer who issues receipt tokens which have a redemption delay, then you actually aren’t worried about a hacker redeeming with you. But you need possible exits to be as small as possible while not impeding normal users. High supply caps need to be seen as a liability, rather than a sign of stature.