Human
5.5K posts

Human
@BadaMasigi
AI will not replace you. A person using AI will
Katılım Ocak 2020
640 Takip Edilen46 Takipçiler
Human retweetledi

Best YouTube Channels To Crack Tech Interviews (2026)
1. DSA – NeetCode
2. LeetCode Patterns – Abdul Bari
3. System Design – Gaurav Sen
4. Mock Interviews – Pramp
5. FAANG Prep – Tech Dummies
6. Coding Rounds – Nick White
7. Behavioral – Jeff H Sipe
8. Problem Solving – Back To Back SWE
9. Deep DSA – Errichto
10. Interview Strategy – Exponent
11. Resume + Career – Self Made Millennial
12. Real Interview Qs – Clément Mihailescu
13. Advanced DSA – William Lin
14. CS Basics – MIT OpenCourseWare


English
Human retweetledi

OAuth consent phishing is the #M365 attack most orgs still aren’t watching.
No password stolen.
No MFA bypassed.
Just one “Sign in with Microsoft → Approve” click.
Malicious app gets a refresh token with persistent access to mail, files & calendar. Bypasses Conditional Access. Logs look normal. Default detections miss it.
Fix: Monitor Entra audit logs for “Consent to application”. Alert on risky scopes (Mail.Read, Files.ReadWrite.All, offline_access) from unverified publishers.
Better: Disable user consent entirely. Force admin approval only, where practical.
This is the gap between “we have MFA” and real security. M365/SecOps pros: auditing your consents right now!

English
Human retweetledi

OWASP just dropped APTS
A governance standard for autonomous pentesting platforms.
Not a methodology.
A control layer.
Focus: scope enforcement, safe autonomy, manipulation resistance, accountability.
As AI-driven testing scales, this is the guardrail the industry needed.
github.com/OWASP/APTS

English
Human retweetledi

Schedule these exams ASAP
Microsoft Learn@MicrosoftLearn
New AI Certification exams are now in beta. Build real‑world AI & agentic skills from fundamentals to enterprise‑ready solutions: 🔗 AI‑901 – Implement AI solutions using Microsoft Foundry. msft.it/6017vDw7h 🔗 AI‑103 – Build scalable AI apps & agents on Azure. msft.it/6019vDwCB 🔗 AB‑620 – Design enterprise‑ready agents in Copilot Studio. msft.it/6010vDwC8
English
Human retweetledi

🛡️ 𝗛𝗮𝗰𝗸𝗲𝗿 𝗦𝗲𝗮𝗿𝗰𝗵 𝗘𝗻𝗴𝗶𝗻𝗲𝘀 (𝗢𝗦𝗜𝗡𝗧)
🌐 Infra
• Shodan — Find exposed devices
shodan.io
• Censys — Internet-wide asset view
censys.io
• FOFA — Asset discovery
fofa.info
• ZoomEye — Attack surface mapping
zoomeye.org
📧 Identity
• Hunter — Find emails
hunter.io
• HaveIBeenPwned — Breach check
haveibeenpwned.com
• Dehashed — Leaked credentials
dehashed.com
💻 Web / Code
• URLScan — Analyze websites
urlscan.io
• Grep.app — Search code
grep.app
• crt.sh — SSL cert lookup
crt.sh
🔐 Vulns
• Vulners — Vulnerability DB
vulners.com
• GreyNoise — Filter attack noise
viz.greynoise.io
• FullHunt — Attack surface
fullhunt.io
📡 OSINT
• WiGLE — WiFi mapping
wigle.net
• IntelX — Deep data search
intelx.io
• LeakIX — Exposed data
leakix.net
• SecurityTrails — DNS/IP data
securitytrails.com
💡 Tip: SpiderFoot — automate recon
spiderfoot.net
#OSINT #CyberSecurity
English
Human retweetledi

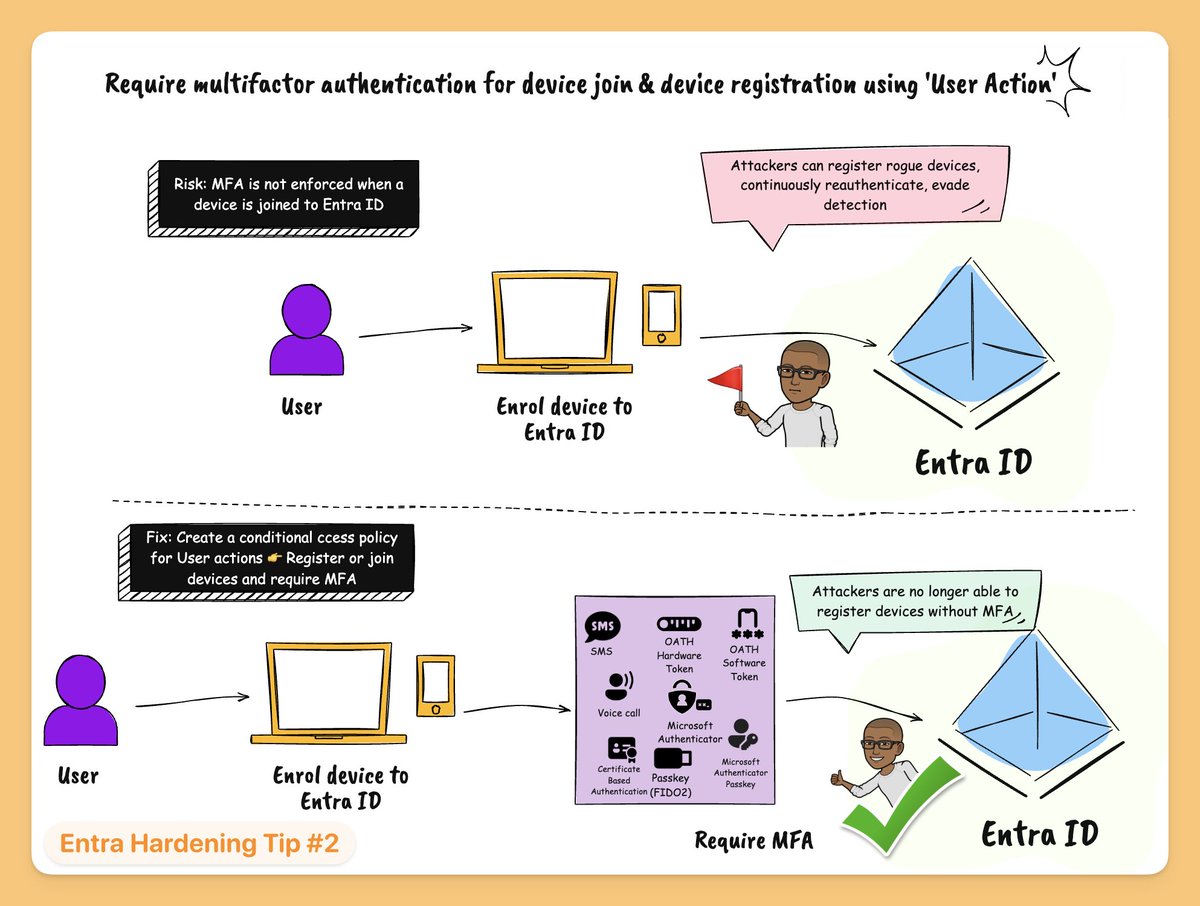
Entra Hardening Tip #2: Require MFA for device join & device registration using 'User Action'
If you don’t enforce a Conditional Access policy for “Register or join devices”, you’re leaving a gap.
Attackers can take advantage of this and register new devices without MFA.
Once they’re in, they can:
🚩 Stay persistent
🚩 Bypass controls that rely on trusted devices
From there, it opens the door to:
🚩 Data exfiltration
🚩Dropping malicious apps
🚩 Moving laterally across your environment
🚩Recon of your device configuration and compliance policies
The fix:
Create a CA policy
→ Include: All users
→ Target: User Action = Register or join devices
→ Grant access: Require authentication strength - MFA
English
Human retweetledi

Just dropped a new EntraChat episode with @PyroTek3 from @TrustedSec and honestly my brain is full 🤯
Sean has been doing Microsoft identity security since Azure AD was barely a thing and he still sees the same misconfigs in enterprise environments every. single. day.
legacy auth left on. app permissions nobody's auditing. shadow tenants nobody knows exist.
the fundamentals aren't boring, they're just not done 🎙️👇
English
Human retweetledi

TeamViewer charges $50.90/month.
AnyDesk starts at $22.90/month.
And every single connection goes through their servers.
Your screen. Your passwords. Your files. Your private conversations. All routed through someone else's computer.
TeamViewer was breached in June 2024. An APT group got into their internal corporate IT environment.
There is a free alternative. You host it yourself. Your data never touches a third party.
It is called RustDesk. 102,000+ stars on GitHub.
You download it. Share your ID. Connect. That is it. Works instantly. No account needed.
Here is what it does:
- Full remote desktop control across Windows, Mac, Linux, Android, and iOS
- File transfer between devices. Drag and drop.
- Clipboard sync. Copy on one machine, paste on the other.
- Direct P2P connections through TCP hole punching. Faster than any relay.
- End-to-end encryption on every connection. NaCl cryptography.
- Works out of the box with zero configuration
Here's the wildest part:
You do not need to self-host to use it. Public relay servers are built in. Download and connect in seconds.
But if you self-host on a $5 VPS, you get something no paid tool offers:
Complete data sovereignty. Your screen. Your files. Your logs. All on YOUR server. Nobody else sees them. Ever. Unlimited users. Unlimited devices.
TeamViewer Business: $50.90/month. $610/year.
AnyDesk Solo: $22.90/month. $274/year.
RustDesk: $0. Forever.
Built in Rust. 356 contributors. 14,900+ forks. Translated into 39 languages.
AGPL-3.0 licensed. Self-hosted. Community-driven.
100% Open Source.
(Link in the comments)

English
Human retweetledi
Human retweetledi
Human retweetledi
Human retweetledi

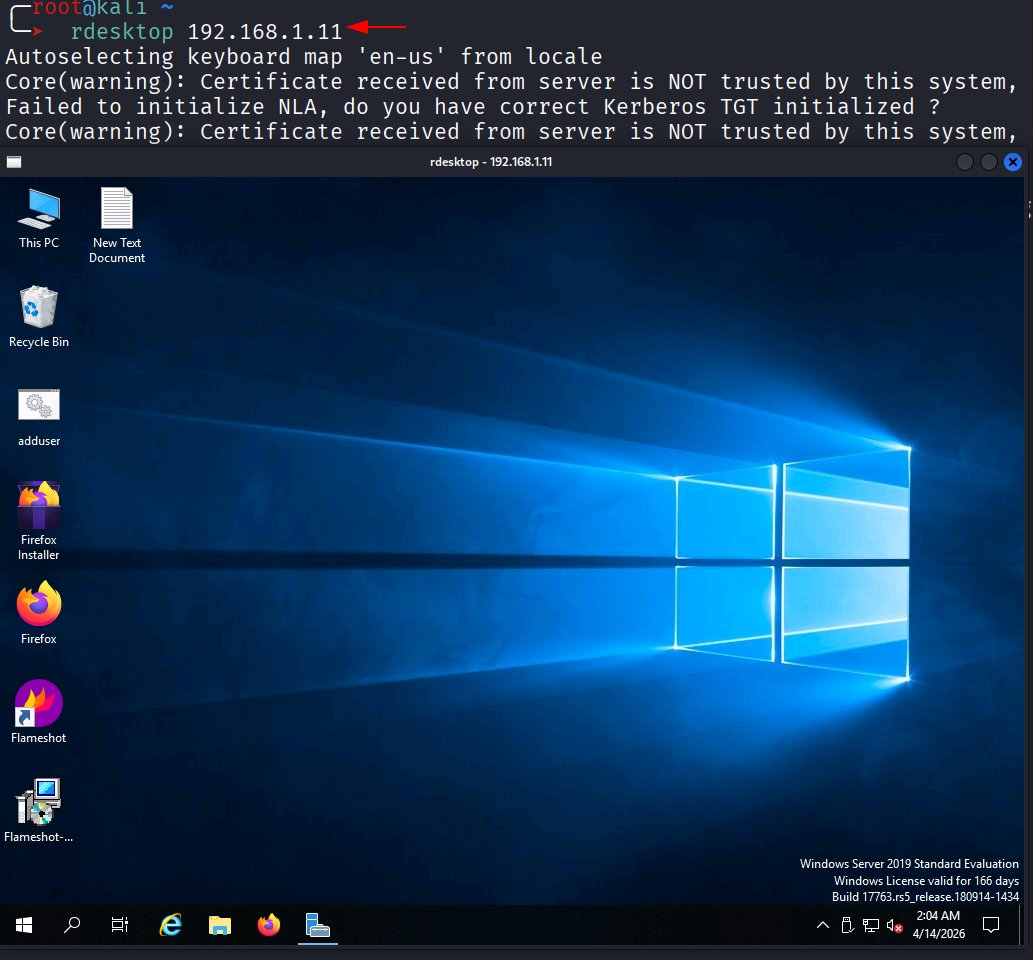
🚨 Lateral Movement: Enabling RDP Remotely 🚨
🔥 Telegram: t.me/hackinarticles
✴ Twitter: x.com/hackinarticles
Attackers can remotely enable Remote Desktop (RDP) on compromised systems to gain persistent access and move laterally across the network without needing physical interaction.
⚡ Attack Highlights
💻 Enable RDP via registry modification
🔐 Change fDenyTSConnections to allow access
🔥 Open firewall port 3389 for connectivity
🌐 Authenticate remotely using valid credentials
🛠️ Techniques & Methods
📡 Remote Registry manipulation
⚙️ PowerShell / CMD execution
🧩 Group Policy (GPO) abuse
🛡️ Firewall rule modification
💡 RDP uses port 3389 and requires proper firewall rules and permissions—once enabled, attackers can fully control the system remotely.
📖 Article: hackingarticles.in/lateral-moveme…
#CyberSecurity #EthicalHacking #Pentesting #RedTeam #LateralMovement #RDP #ActiveDirectory



English
Human retweetledi
Human retweetledi
Human retweetledi

Ok, I just used Claude to pentest a very simple Active Directory in the LAB!
round one it basically end to end did a pentest with very little handholding, it walked me through a wizard of test style and rules, when it got stuck at the black box stage it then asked me for a course of action, we went to assume breach. the account I gave it was in the 'administrators' group so it had ADMIN rights and then it ran bloodhound, DCSYC, found kerberoastable accounts, enumerated ADCS vulnerabilities etc. then it checked the hashes of accounts and then wrote a report (the report is pretty good)
I am now making it go back and go again but this time the user is LOW priv (a bit of a fuck up on my part this was the wrong way round)

English

Major Predictions for UAE 🇦🇪 -
Great period till 2041
2026, 2027 - Buy property
2028, 2033, 2035, 2036 - Sell property
#UAE #Dubai #uaerealestate
English
Human retweetledi