
@KudelskiSec This is really cool. Thanks for sharing it with the community. Does your sit have an rss feed to keep up with the blogs?
English
Cyber Cyborg
15 posts













F5 Breach #ai-recommendations-54" target="_blank" rel="nofollow noopener">my.f5.com/manage/s/artic…







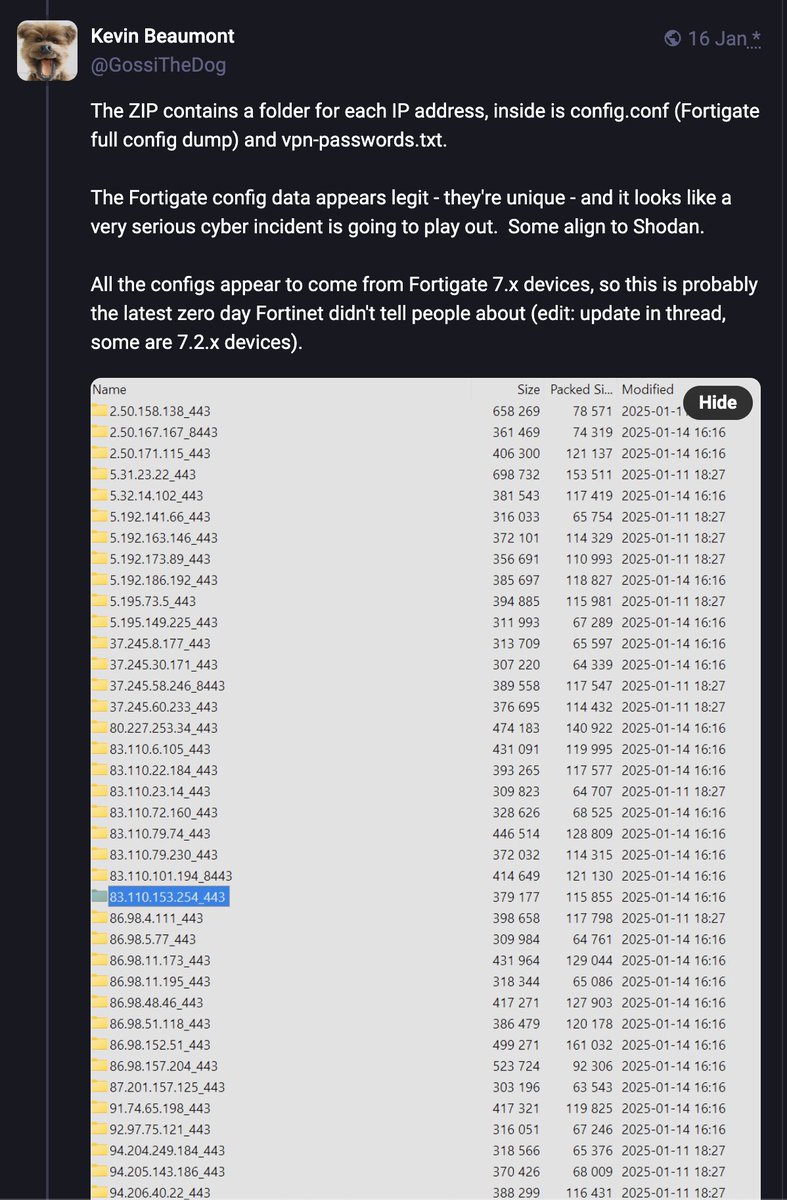
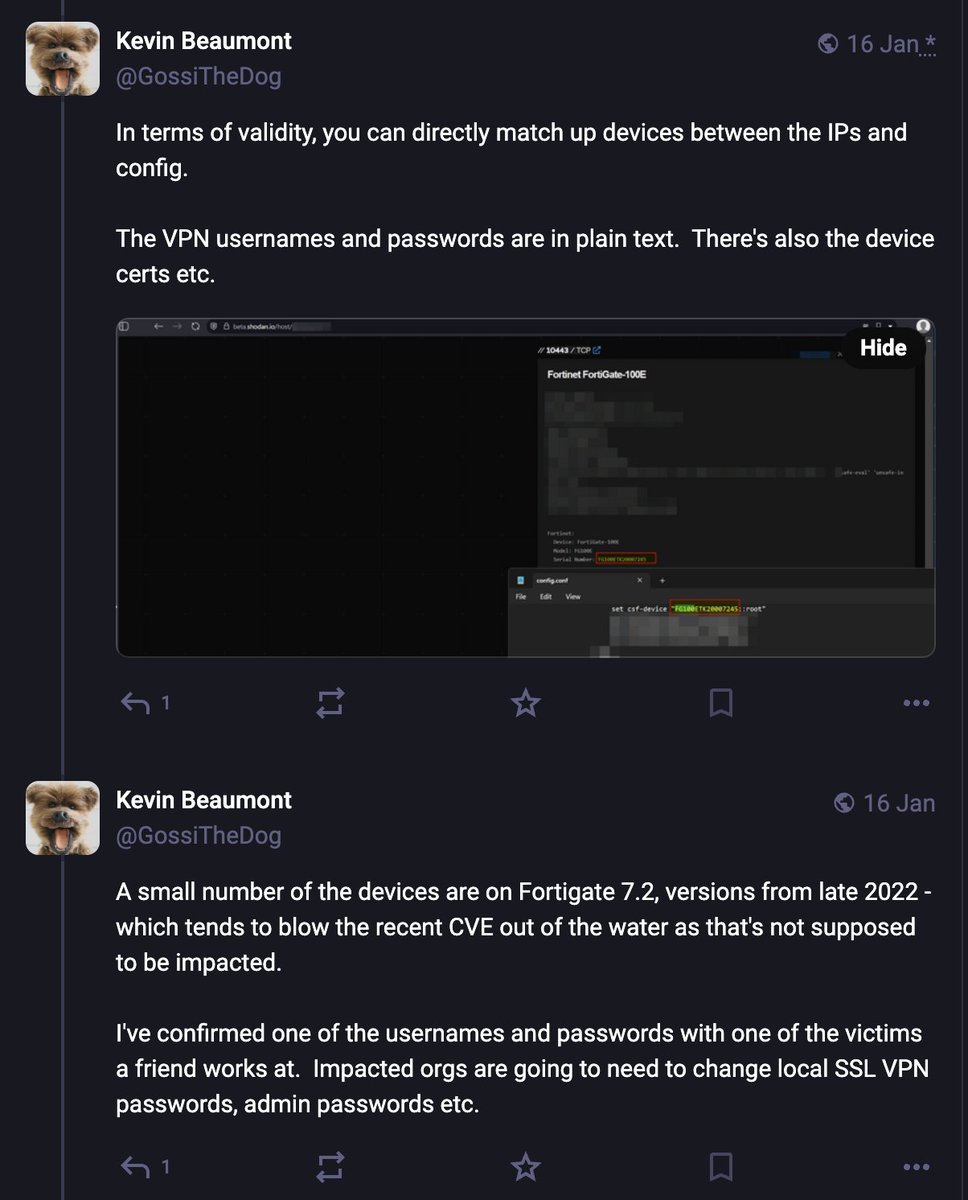
Kevin published the email addresses in the #Fortigate config dump raw.githubusercontent.com/GossiTheDog/Mo…


We're less than an hour away from @JimSycurity's thrilling foray into #ActiveDirectory Security Descriptors! 🥄 Grab a spoon & dig in: The Gooey Guts of Security Descriptors: Securable Objects, All the Way Down TODAY (Oct 24) @ 11a PT / 2p ET Register at bit.ly/DescriptorInna…




