@Byttno Bygd av våre forfedres blod, svette og tårer. Så kommer de skamløse fittan å skal bestemme... sku hatt ørfik heil gjengen
Morten Larsen
13.7K posts


@CyberLarsen
Technical Manager helping companies deliver successful Dynamics 365, Power Platform & SharePoint solutions in Norway & Sweden | Microsoft specialist

@Byttno Bygd av våre forfedres blod, svette og tårer. Så kommer de skamløse fittan å skal bestemme... sku hatt ørfik heil gjengen





Jordskjelvet kl 0930 ble kjent av mange i Oslo. Oslo ligger i det vi kaller en graben, en innsynking mellom to forkastninger i jordskorpen, og dette øker sannsynligheten for at det oppstår jordskjelv (NORSAR). jordskjelv.no/om-jordskjelv/

Anthropic pays engineers $750,000+ a year to understand how LLMs work. Stanford just put a 2 hour lecture that covers 80% of it for FREE. Bookmark this. Give it 2 hours today. It might be the highest ROI thing you do this month:





Artificial Intelligence in Cybersecurity: Using AI for Port Scanning - hackers-arise.com/artificial-int… | github.com/peter-hackerta… By @_aircorridor at @three_cube Nmap has been the gold standard of network scanning for decades, and over this time, it has obtained hundreds of command-line options and NSE scripts. It’s great from one side, you can tailor the command for your needs, but on the other side, it requires expertise. What if you could simply tell an AI in plain English what you want to discover, and have it automatically select the right Nmap commands, parse the results, and identify security issues? That’s exactly what the LLM-Tools-Nmap utility does. Basically, it bridges the gap between Large Language Models (LLMs) and Nmap.

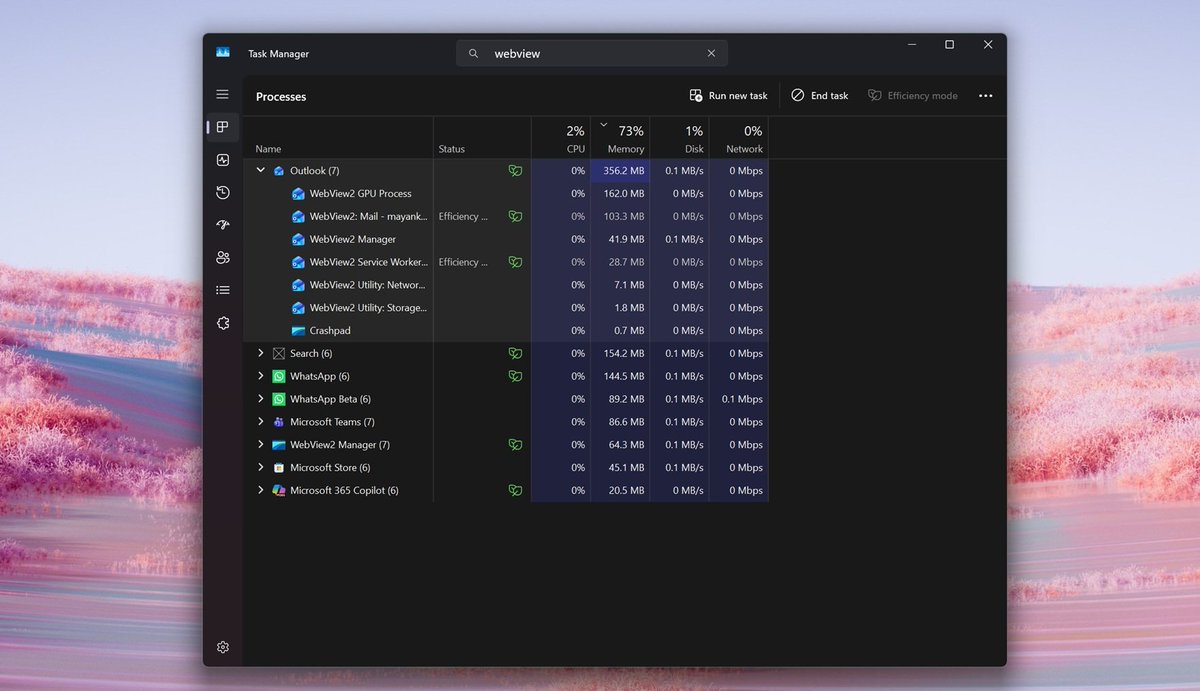
By Usama Jawad - From lunar flyby to IT support, Artemis II astronauts report Outlook failures, proving even deep space isn't safe from Microsoft's software bugs. #Outlook #ArtemisII #Microsoft neowin.net/news/project-h…


Yesterday, Isar Aerospace was set to launch its qualification flight for Mission ‘Onward and Upward’ from Andøya Space during a 15 minute launch window. While all operations and check-outs were nominal throughout the countdown, Isar Aerospace was informed about an unauthorized vessel intruding the designated danger zone at sea. Shortly before the launch system entered final autosequence, the launch was placed on hold for 15 minutes. The range could only be declared clear at 21:18, and the countdown resumed. As a result of the delay, the vehicle encountered an increase in engine fuel temperature, which could not be addressed within the shortened countdown and hence forced the abort of the mission. Daniel Metzler, CEO and Co-Founder of Isar Aerospace: “Rocket launches are highly complex operations – from safe ground infrastructure to more than 100,000 parts, structures, and systems working together seamlessly. While we're working to return to the pad as quickly as possible, we will not compromise on mission assurance.”