
Daniel Smith | Building ClawQL Agents
2.6K posts


@DanielSmithDev
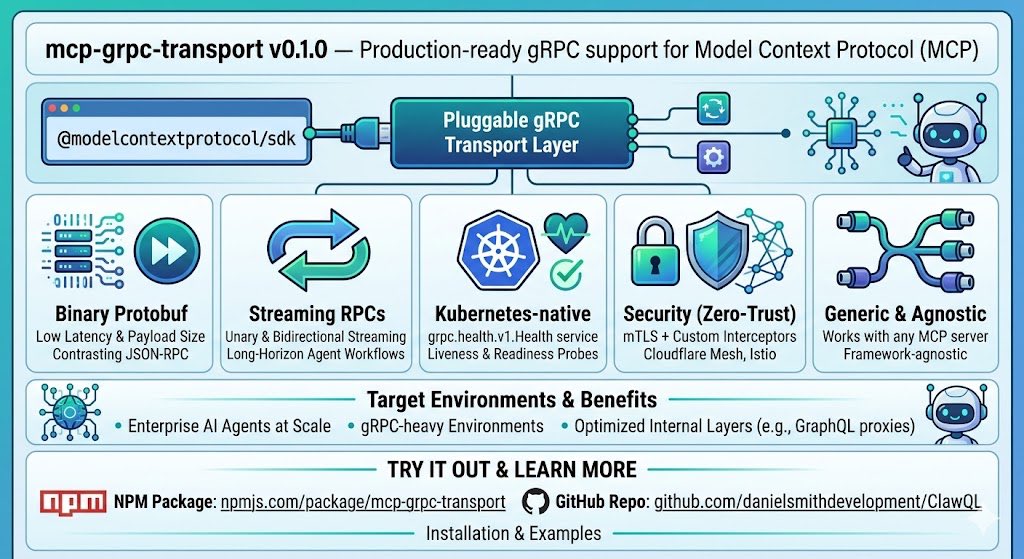
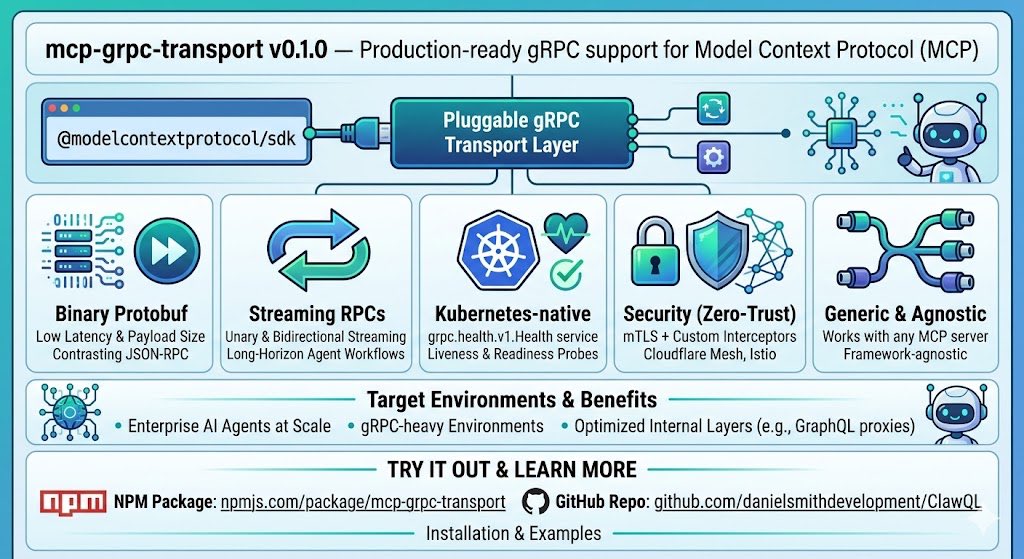
Building @ClawQL Agent/MCP as the API and document intelligence platform for enterprises! PlatformEng/SRE/DevOps in a love-hate relationship with Kubernetes.






software engineers before vs after agents

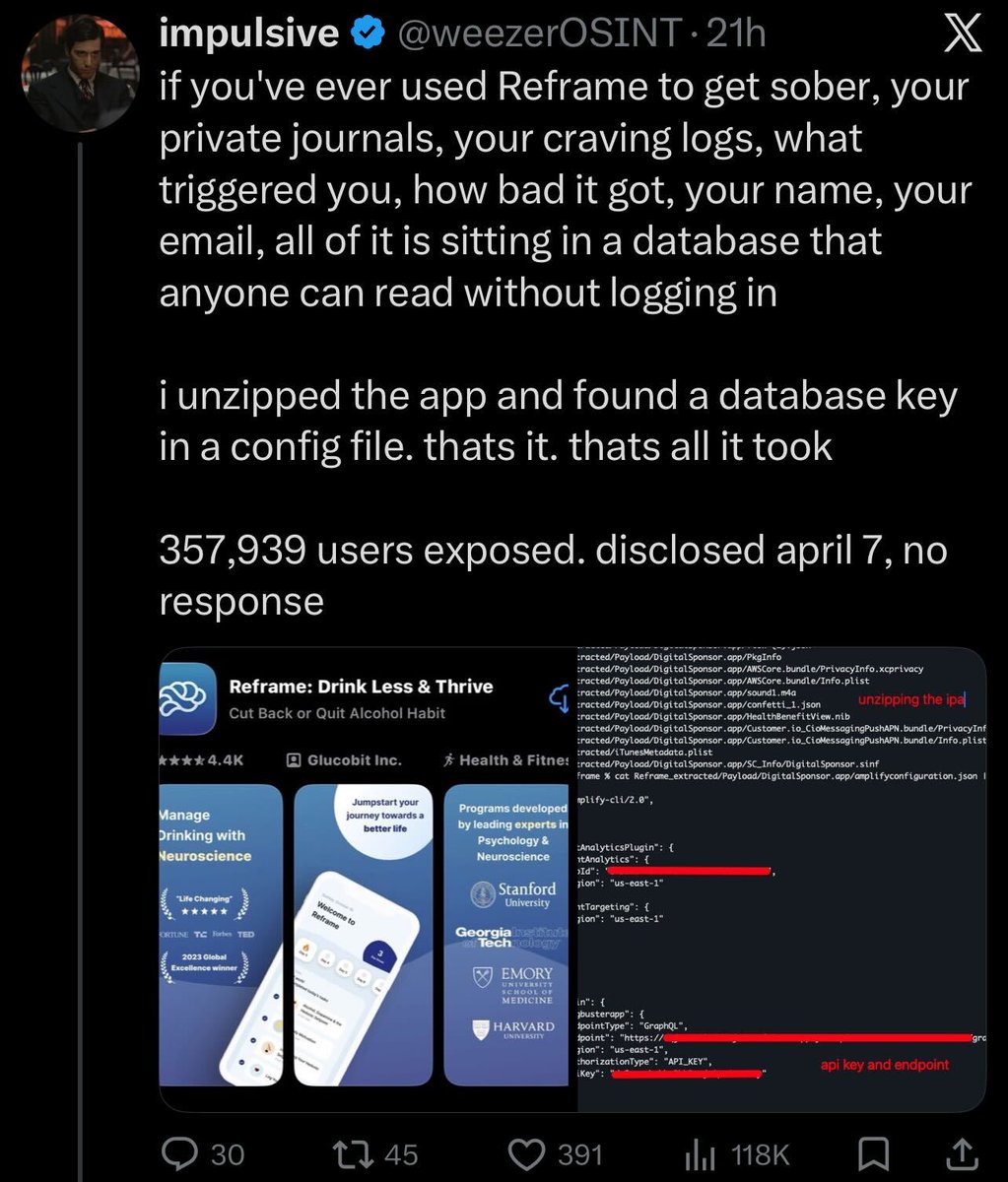
what steps should i have taken? no bug bounty, no security.txt, no security@ email, support@ ignored me for 25 days. the tweet got the founder to rotate the key in hours. and we gotta stop blacklisting researchers over disclosure disagreements thats not how you make the industry better


if you've ever used Reframe to get sober, your private journals, your craving logs, what triggered you, how bad it got, your name, your email, all of it is sitting in a database that anyone can read without logging in i unzipped the app and found a database key in a config file. thats it. thats all it took 357,939 users exposed. disclosed april 7, no response

@weezerOSINT i'd say the same about you - clearly you have the right intent in your work and were immediately responsive. this was a miss on us, and we'll continue to get better

Security people: This behavior is completely unacceptable. I don't care that you sent a few emails and got ignored. You don't get to drop this info publicly and put these users at greater risk. He's been called out by multiple people (@rez0__) and is doubling down. Not cool.
























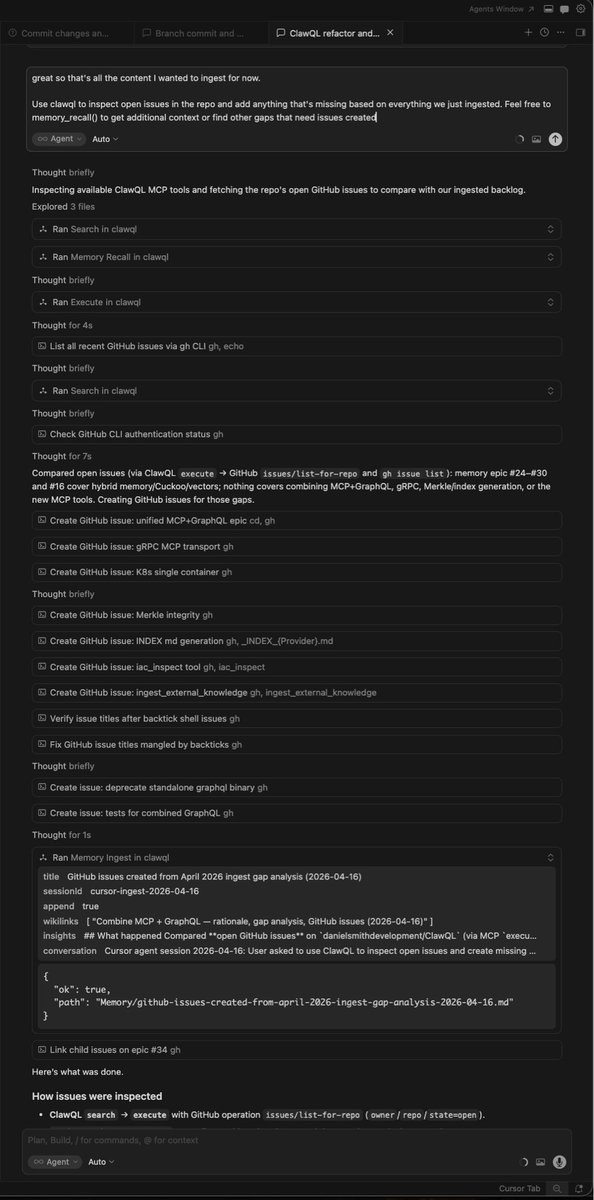
seriously, working with AI is MISERABLE for one and only one reason: having to re-explain the same thing "oh yeah this new session obviously doesn't know what proper case trees are, so let me explain it for the 5000th time in my life" I'm tired AGENTS.md doesn't solve this because it is impossible to fit the entire domain knowledge without nuking the context - it would be 1m+ tokens worth RAGs don't solve this, the agent won't search unknown unknowns SKILLs don't solve this unless I keep like a collection of 1750 skills with specific cuts of domain knowledge for each possible subset of my domain that I might need in a given chat, but that's a lot of manual work recursive LLMs or whatever don't solve this for the same reason, you can't dump a domain book and expect the AGENT will magically guess that it is supposed to search for a specific bit knowledge. unknown unknowns fine tuning doesn't solve this (OSS models suck and OpenAI / Anthropic gave up on user fine tuning) I honestly think a good product around fine tuning on your domain would be a major hit and an underdog lab should take this opportunity