David Etim
449 posts


David Etim
@DavidEtim2654
Upcoming SOC Analyst | Cybersecurity Fundamentals SIEM • Networking • Incident Detection Building skills daily 🚀















I look at my life and I know I’ve lived well


Cybersecurity is not easy ooo Make dem no whine you ooo.

If I tell you I’m tired, please believe 😪


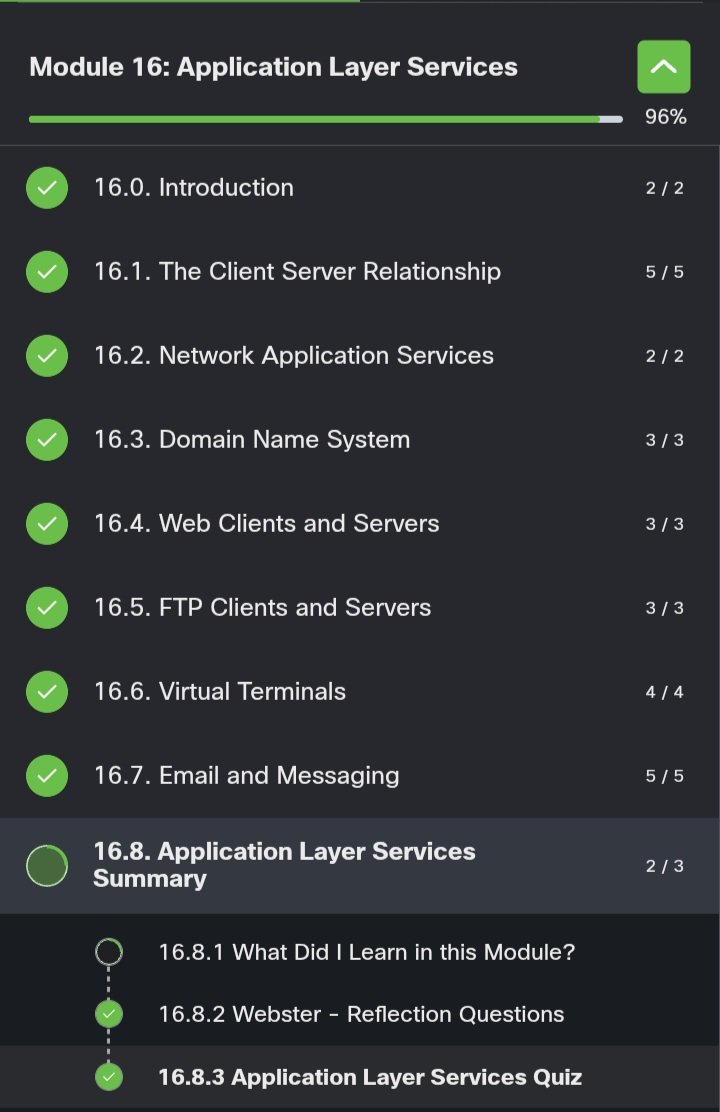
DAY 22-24 of becoming a soc anslyst Module 15:tcp and udp Learnt about Tcp and udp Port numbers Types of Port ans their uses #SOCAnalyst #BlueTeam #CyberDefense #SIEM #SecurityOperations #ThreatDetection #CyberSecurity #EntryLevelSOC


DAY 37-38 of becoming a soc anslyst Cybersecurity landscape. This is teaching about,how to: Understand the cost and impact of security events. Identify some historic high profile security events. Security concepts about surrounding information assurance. #BlueTeam #SOCAnalyst