Sean Hoyt retweetledi
Sean Hoyt
605 posts

Sean Hoyt
@Deadman_Android
I'm an Android Systems Developer, with a passion for finding new and weird stuff.
St Paul, MN Katılım Haziran 2011
236 Takip Edilen566 Takipçiler
Sean Hoyt retweetledi
Sean Hoyt retweetledi
Sean Hoyt retweetledi
Sean Hoyt retweetledi

@AdamAllevato I bought one of these as well, it will be delivered soon. Would love to collaborate I have android os dev experience. Along with some work done on similar rk3288 devices.
English
Sean Hoyt retweetledi

Sean Hoyt retweetledi

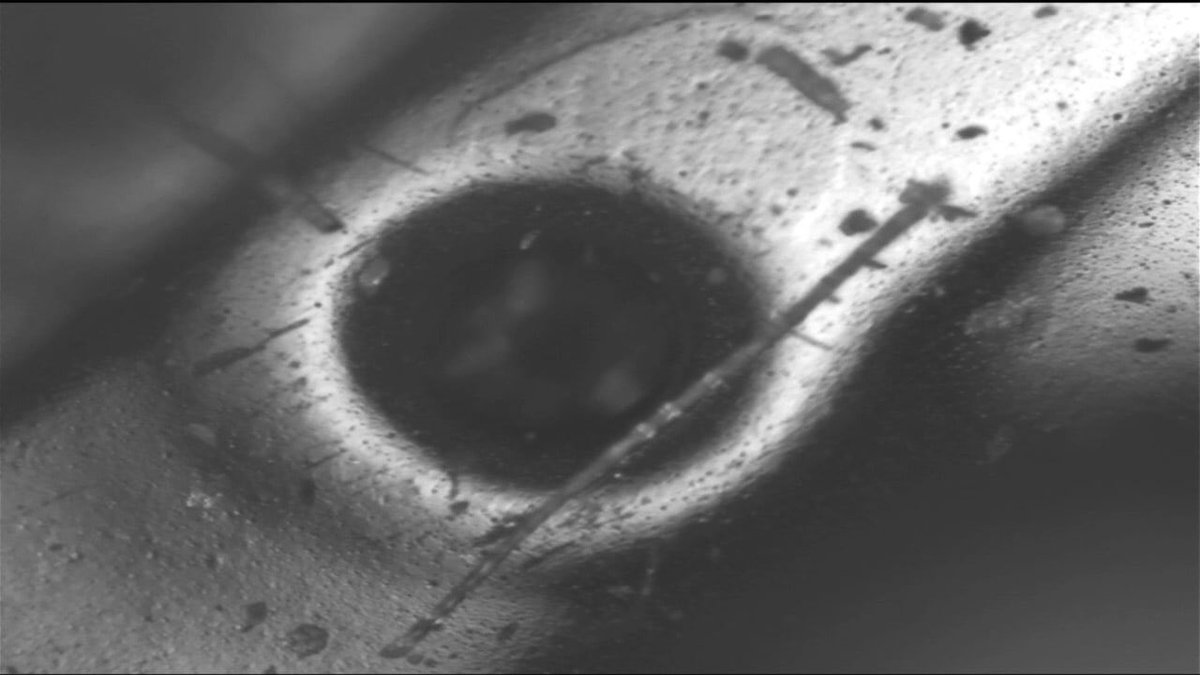
(1/9) A very rare original Xbox “Duke” controller prototype, built approximately a year before the Xbox launched. Below, I’ll document all of the differences between this and a retail unit. #Xbox #Microsoft

English

🚨 @DonjonLedger has struck again discovering a MediaTek vulnerability potentially impacting millions of Android phones. Another reminder that smartphones aren’t built for security. Even when powered off, user data - including pins & seeds - can be extracted in under a minute.
English

As always, the Ledger Donjon followed a strict responsible disclosure process with the relevant vendors, which allowed security fixes to be released. MediaTek confirmed providing a fix to OEMs on Jan 5, 2026. The vulnerability is now public (CVE-2025-20435) nvd.nist.gov/vuln/detail/CV…
English

github.com/orgs/Amazon-OS…
19 different soc's across their 1st party and partner FireTV devices. Next steps will be splitting/cleaning up the version imports to make it easier to see changes.
English

@Deadman_Android this is actually really good but not really what im doing, im getting the "online" multiplayer not splitscreen
English
Sean Hoyt retweetledi

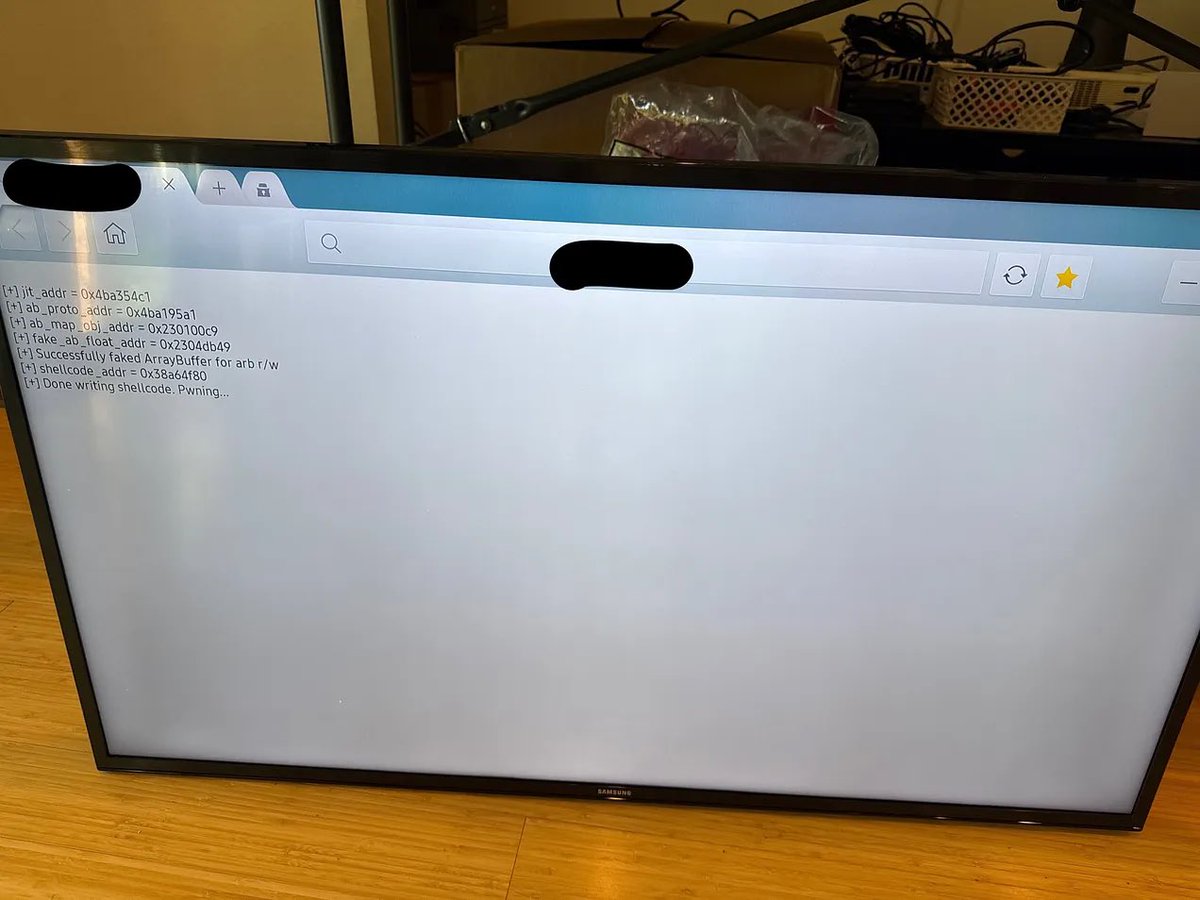
After weeks of reverse engineering MediaTek's DA2 with @shomykohai, we finally figured out how the V6 exploit works. We decided to call it heapb8 ("heapbait")!
Technical writeup: blog.r0rt1z2.com/posts/exploiti…
PoC: github.com/shomykohai/pen…
English
Sean Hoyt retweetledi

apk.sh makes reverse engineering Android apps easier, automating repetitive tasks like pulling, decoding, rebuilding and patching an APK. It supports direct bytecode manipulation with no decompilation, this avoids decompilation/recompilation errors. reddit.com/r/ReverseEngin…
English

@Deadman_Android @konrad_it These are the ones we busted up over the summer... linkedin.com/posts/kevin-fi…
English

@d0tslash I wonder if they use the DJI CDN again.
tomshardware.com/tech-industry/…
English