ian
9 posts

ian
@adversarialy
threat research @BlackLotusLabs



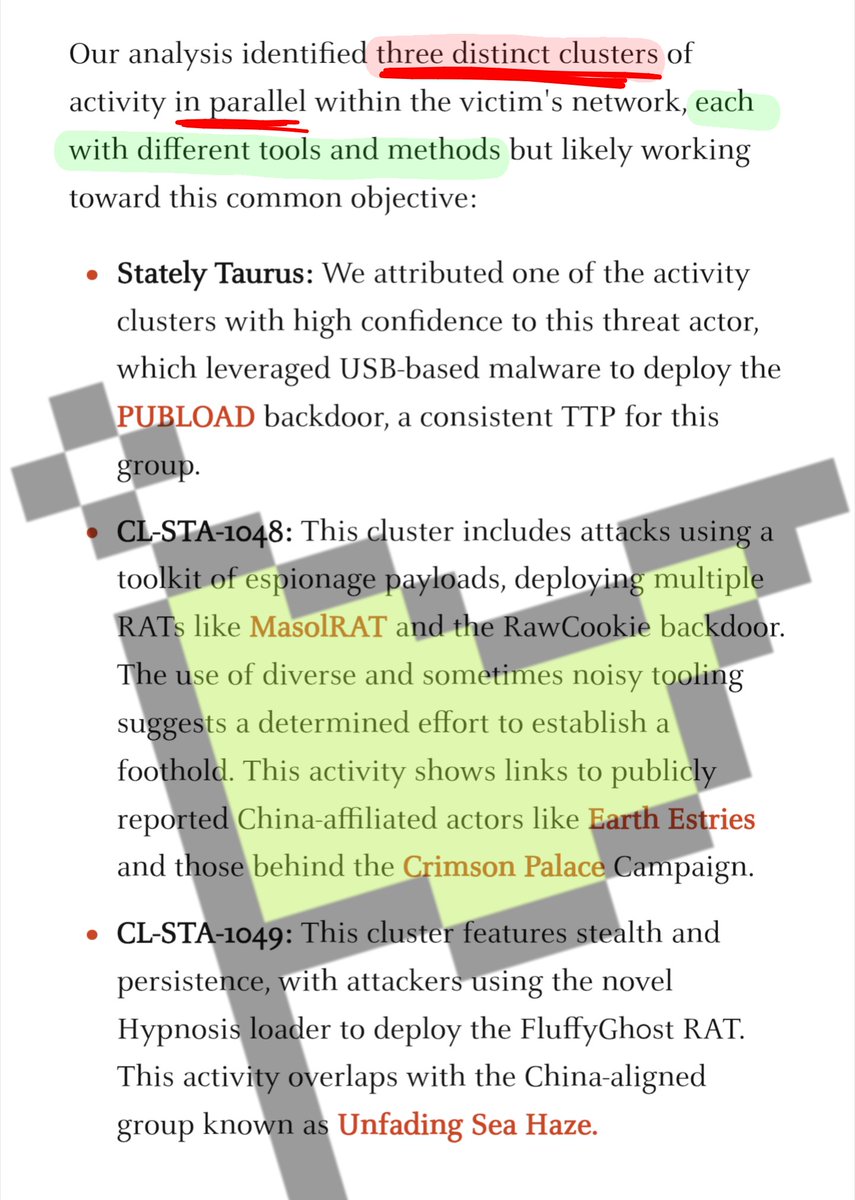
Unit 42 reported that multiple cyberespionage clusters targeting a Southeast Asian government organization used USBFect, RATs, and loaders. unit42.paloaltonetworks.com/espionage-camp…

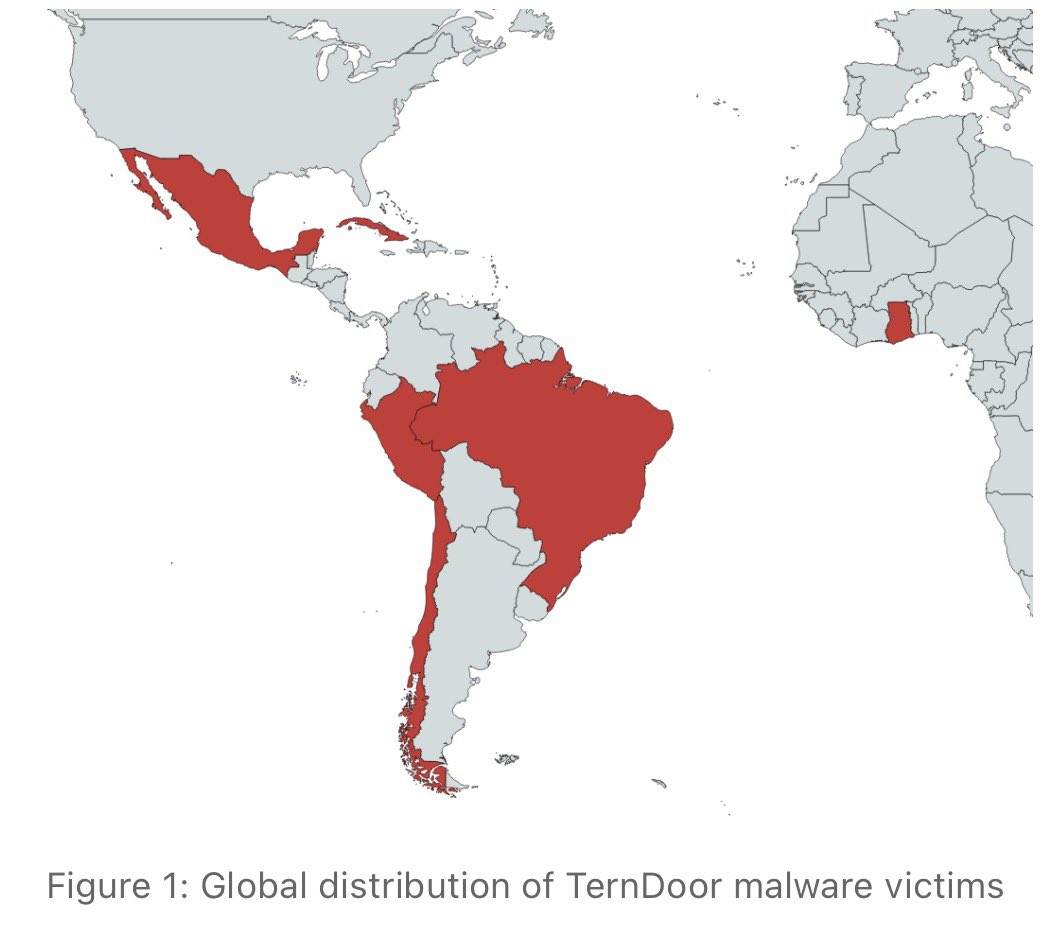
Elastic Security Labs exposes BRUSHWORM backdoor and BRUSHLOGGER keylogger targeting South Asian financial institution. Custom malware pair features USB worm spreading, broad file theft, and system-wide keystroke capture via DLL side-loading.
Key technical details:
• BRUSHWORM (paint.exe): Modular backdoor with AES-CBC encrypted config, scheduled task persistence (MSGraphics), anti-analysis checks (screen resolution, hypervisor detection), and C2 communication to resources.dawnnewsisl[.]com/updtdll
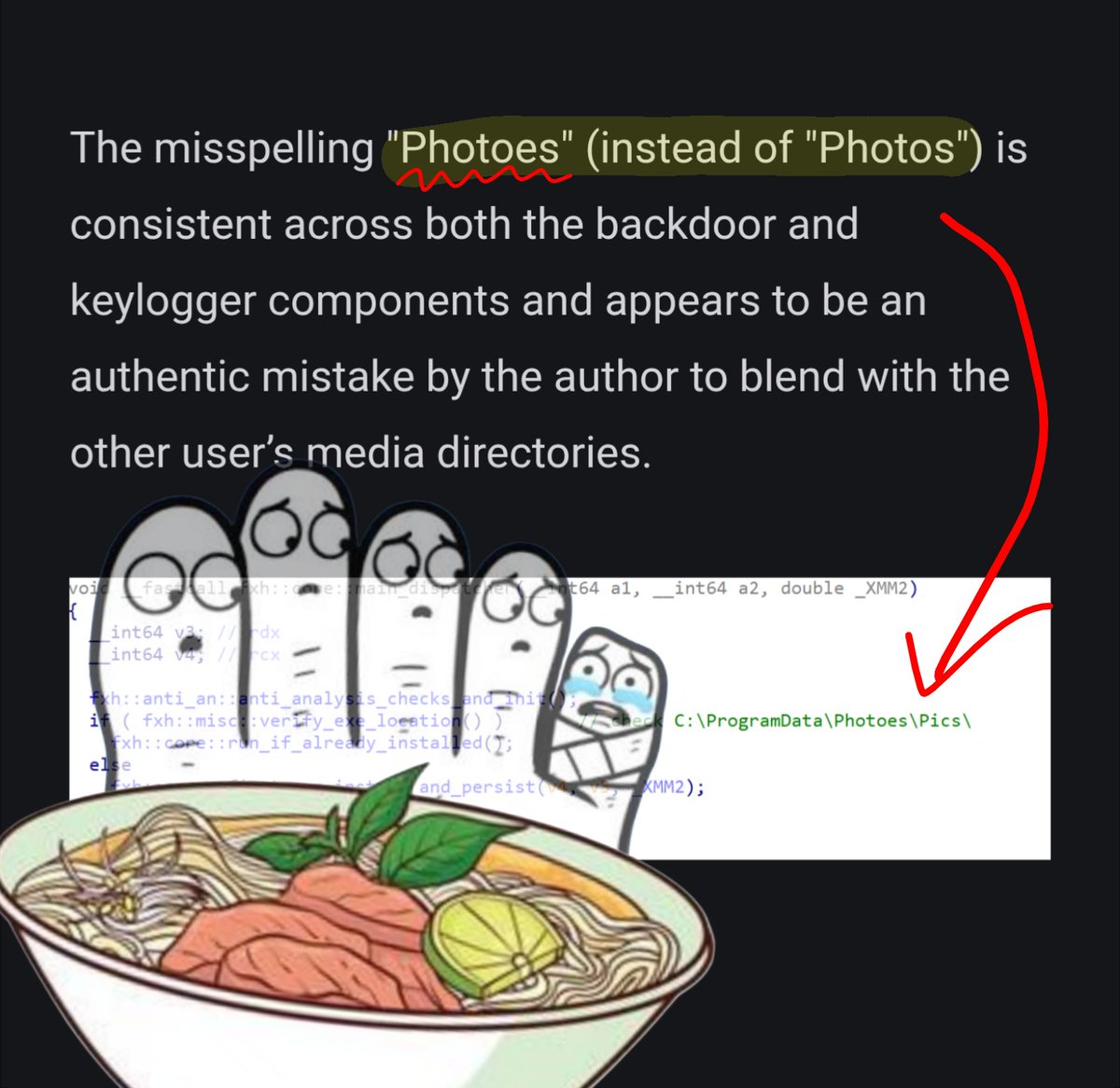
• Creates hidden directories: C:\ProgramData\Photoes\Pics\, C:\Users\Public\Libraries\, stages stolen files in C:\Users\Public\Systeminfo\
• USB spreading uses social engineering filenames (Salary Slips.exe, Documents.exe) and exfiltrates 40+ file extensions including .doc, .pdf, .pst, .py
• BRUSHLOGGER (libcurl.dll): DLL side-loading keylogger with WH_KEYBOARD_LL hook, XOR encryption (key 0x43), logs to C:\programdata\Photoes\

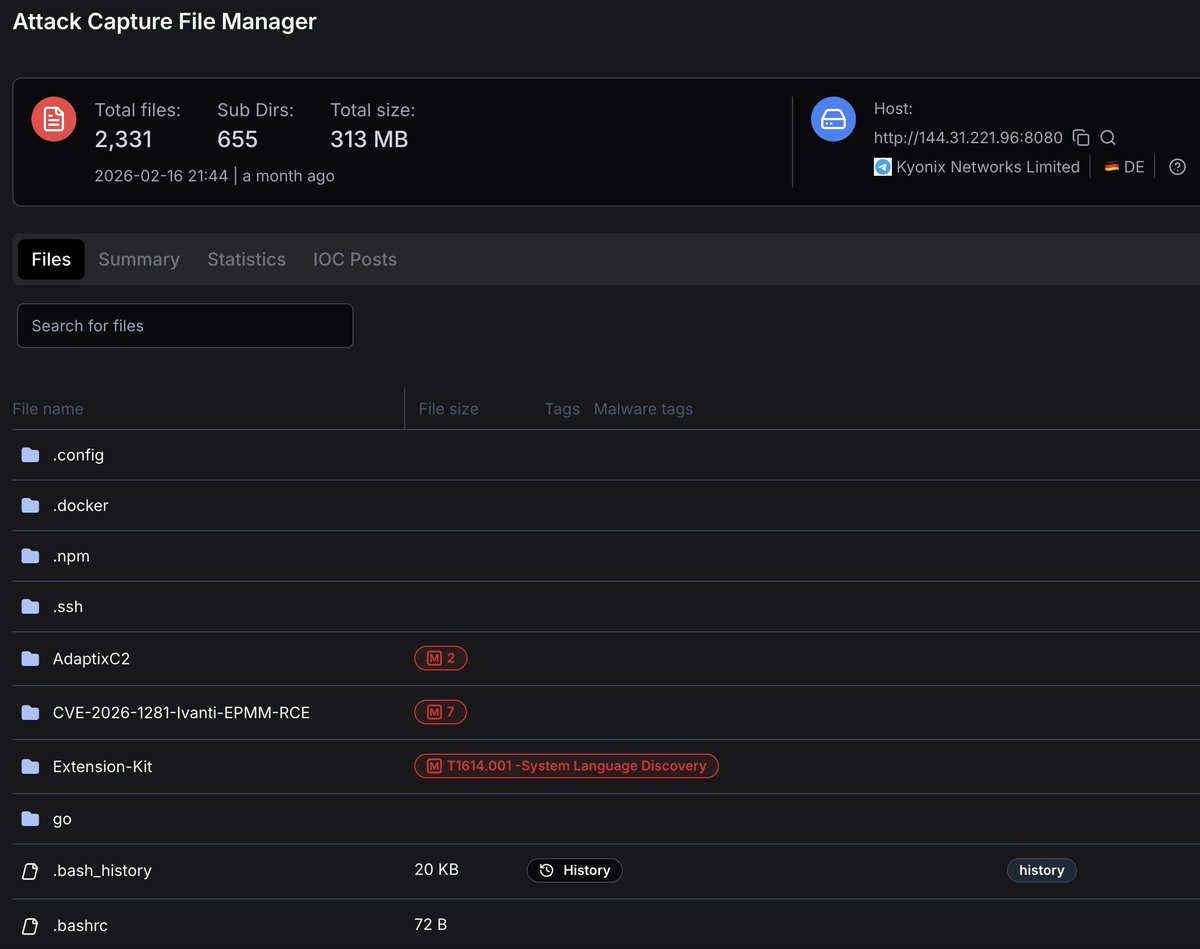
Catched in the wild 😉 cc @DefusedCyber