Sabitlenmiş Tweet
Eduardo Chavarro
21.4K posts


Eduardo Chavarro
@EChavarro
MSc Infosec, #DFIRMA, Telecommunications | DFIR Group Manager | GCIH/GRID/GCFA/CHFI/CISM/CPTE/SFCP/ITIL | #Kaspersky #GERT
Closer Katılım Ocak 2010
1.4K Takip Edilen2.3K Takipçiler
Eduardo Chavarro retweetledi

Better understand agentic AI systems and mitigate the cybersecurity risks using a new guide we authored with @ASDGovAu and others. View the joint report. #Cybersecurity #AgenticAI
media.defense.gov/2026/Apr/30/20…
English
Eduardo Chavarro retweetledi

🚨 Cybersecurity firm Trellix confirms a breach.
Attackers accessed part of its source code repository; no exploitation or release impact found. Investigation ongoing with forensic experts and law enforcement.
Details ➜ thehackernews.com/2026/05/trelli…
English
Eduardo Chavarro retweetledi

Gained initial access to a company network… but what next?
In this real pentest project our colleague @irabva shows how Kubernetes misconfigurations led to full cluster access and exposed S3 data.
If you work with K8s, read this
purpleshift.io/purple/2026-03…
English
Eduardo Chavarro retweetledi

⚠️ Kaspersky found a new wiper targeting Venezuela’s energy sector.
Lotus Wiper fully destroys systems—no ransom, no recovery. It uses scripts to disable defenses, then wipes drives, deletes backups, and erases files using native Windows tools.
🔗 Details → thehackernews.com/2026/04/lotus-…
English
Eduardo Chavarro retweetledi

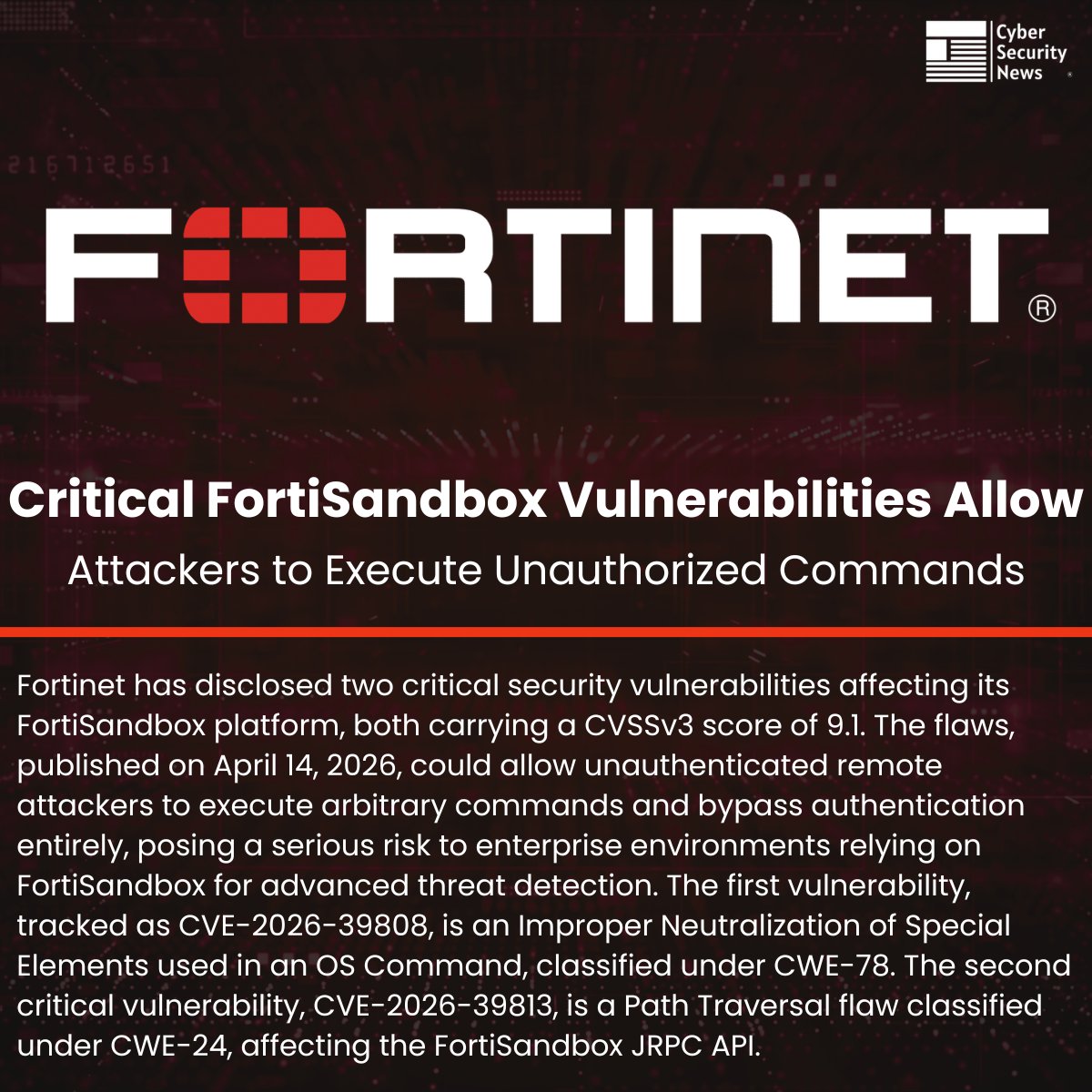
🚨 Critical FortiSandbox Vulnerabilities Allow Attackers to Execute Unauthorized Commands
Source: cybersecuritynews.com/fortisandbox-v…
Fortinet has disclosed two critical security vulnerabilities affecting its FortiSandbox platform, both carrying a CVSSv3 score of 9.1.
The flaws, published on April 14, 2026, could allow unauthenticated remote attackers to execute arbitrary commands and bypass authentication entirely, posing a serious risk to enterprise environments relying on FortiSandbox for advanced threat detection.
The first vulnerability, tracked as CVE-2026-39808, is an Improper Neutralization of Special Elements used in an OS Command, classified under CWE-78.
The second critical vulnerability, CVE-2026-39813, is a Path Traversal flaw classified under CWE-24, affecting the FortiSandbox JRPC API.
#cybersecuritynews
English
Eduardo Chavarro retweetledi

Attackers replacing legitimate download links for (i) CPU-Z, (ii) HWMonitor (HWMonitor Pro), and (iii) Perfmonitor 2 sysadmin software on the cpuid[.]com website -> visitors downloading trojanized distributions from malicious pages. It occurred April 9-10. Details: kas.pr/gj1y

English
Eduardo Chavarro retweetledi

Here's a report from our Security Services (MDR, Incident Response, Compromise Assessment, and SOC Consulting) for 2025: fewer high-severity incidents; CVEs in Microsoft products were most popular among attackers; and public-facing applications, valid accounts, and trusted relationships were the most popular initial vectors(>80% of attacks). For more on these and other expert insights, here’s the full report: kas.pr/16q2

English
Eduardo Chavarro retweetledi

Heads up FortiClient EMS users! CVE-2026-35616 (new) & CVE-2026-21643 - both unauthenticated RCE observed to be exploited in the wild! We fingerprint about 2000 instances globally, see public Dashboard: dashboard.shadowserver.org/statistics/iot…
Top affected: US & Germany dashboard.shadowserver.org/statistics/iot…

English
Eduardo Chavarro retweetledi

⚠️ We are observing heavy reconnaissance activity targeting Cisco IOS XE - specifically IOx application hosting APIs following recent CVE disclosures in the March 2026 Cisco bundle.
A China-based actor is hitting /iox/api/v2/hosting/platform/* endpoints, which are IOx REST API interfaces used to retrieve system diagnostics, log configurations, and tech support bundles.
Track live Cisco IOS XE exploitation on Defused 👉 console.defusedcyber.com/intel

English
Eduardo Chavarro retweetledi

🚨 Critical Fortinet FortiClient EMS 0-Day Vulnerability Actively Exploited in the Wild
Source: cybersecuritynews.com/fortinet-forti…
Fortinet has issued an emergency hotfix after security researchers disclosed a critical zero-day vulnerability in FortiClient EMS that is already being actively exploited by threat actors.
Tracked as CVE-2026-35616 and carrying a CVSSv3 score of 9.1 (Critical), the flaw enables unauthenticated attackers to bypass API authentication and authorization controls entirely, allowing them to execute arbitrary code or commands on vulnerable systems.
Successful exploitation does not require any prior authentication, user interaction, or elevated privileges, making it particularly dangerous for organizations with internet-exposed EMS deployments.
#cybersecuritynews #vulnerability

English
Eduardo Chavarro retweetledi

🚨 New Fortinet vulnerability being exploited as an 0-day
CVE-2026-35616 - FortiClient EMS pre-authentication API access bypass - CVSS 9.1 Critical
After observing in-the-wild exploitation of this vulnerability earlier this week, Defused reported it to Fortinet under responsible disclosure.
Fortinet has released an emergency hotfix - plus a scheduled patch - for FortiClient EMS 7.4.5 and 7.4.6.
The vulnerability allows an unauthenticated attacker to bypass API authentication and authorization entirely, unauthorized code or commands via crafted requests.
This discovery was made through our upcoming Radar feature launching next week 😇
Advisory: fortiguard.com/psirt/FG-IR-26…
Track exploitation of this and other Fortinet vulns in real time and get updates on the new Defused Radar 👉 console.defusedcyber.com/signup
Credit also to @heckintosh_ for independently discovering this vulnerability 💪

English
Eduardo Chavarro retweetledi

Cisco source code stolen in Trivy-linked dev environment breach
bleepingcomputer.com/news/security/…
bleepingcomputer.com/news/security/…
English
Eduardo Chavarro retweetledi

We know it’s been a while since our last post.
But we’re back, with great news!
We’re launching our blog, “Purpleshift,” featuring interesting articles, talks, and research for both blue and red teams.
Yeah that’s why it’s purple :)
purpleshift.io
English
Eduardo Chavarro retweetledi

🚨‼️ MAJOR SUPPLY CHAIN ATTACK: npm package axios is compromised after the maintainer's npm account was hijacked.
Malicious versions contain a Remote Access Trojan. axios has 100M+ weekly downloads — it's in practically everything.
If you have installed axios@1.14.1 or axios@0.30.4, assume compromise.

English
Eduardo Chavarro retweetledi

Critical Fortinet Forticlient EMS flaw now exploited in attacks
bleepingcomputer.com/news/security/…
bleepingcomputer.com/news/security/…
English
Eduardo Chavarro retweetledi
Eduardo Chavarro retweetledi

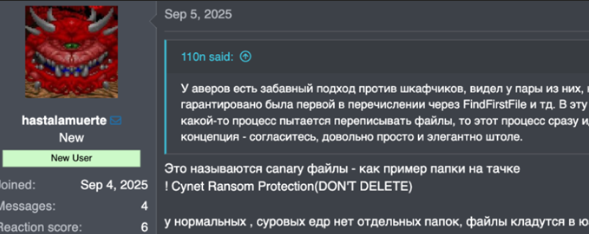
Afiliado “hastalamuerte” reveló TTP de Gentleman y disputas internas. Explotan RDWeb, SSL VPN y CVE-2024-55591 en Fortinet para omitir autenticación y comprometer redes.
Mas información: ecucert.gob.ec/wp-content/upl…
#PorUnEcuadorCiberseguro
@Arcotel_ec
@CsirtCEDIA
@CsirtEPN
Español
Eduardo Chavarro retweetledi

Here’s a report about a campaign targeting Mexico that our MDR team hunted down. It features Horabot – a bundle of a banking Trojan, email spreader, and complex attack-chain: kas.pr/kok6

English

Apresentamos o Kaspersky Threat Attribution Engine (KTAE), a nossa ferramenta usada para fazer uma estimativa sobre qual grupo APT específico pertence uma amostra de malware. bit.ly/3OVgU5d
Português

Inicialmente, los ciberdelincuentes se dirigieron principalmente a empresas privadas, empresas que valoraban sus datos lo suficiente como para justificar un pago considerable. Las escuelas y universidades, por lo general, no eran atacadas. bit.ly/3Pc8uX1
Español