
James D
388 posts


James D
@FranticTyping
Threat Hunting | Detection Engineering | Defensive Automation (ex @Countercept, @mwrlabs)




My talk "Scaling Detection and Response Teams - Enabling Efficient Investigations" is at 3:45pm today at #BSidesLDN2023 on track 2! Come down and say hi if you're around 😀 pretalx.com/bsides-london-…





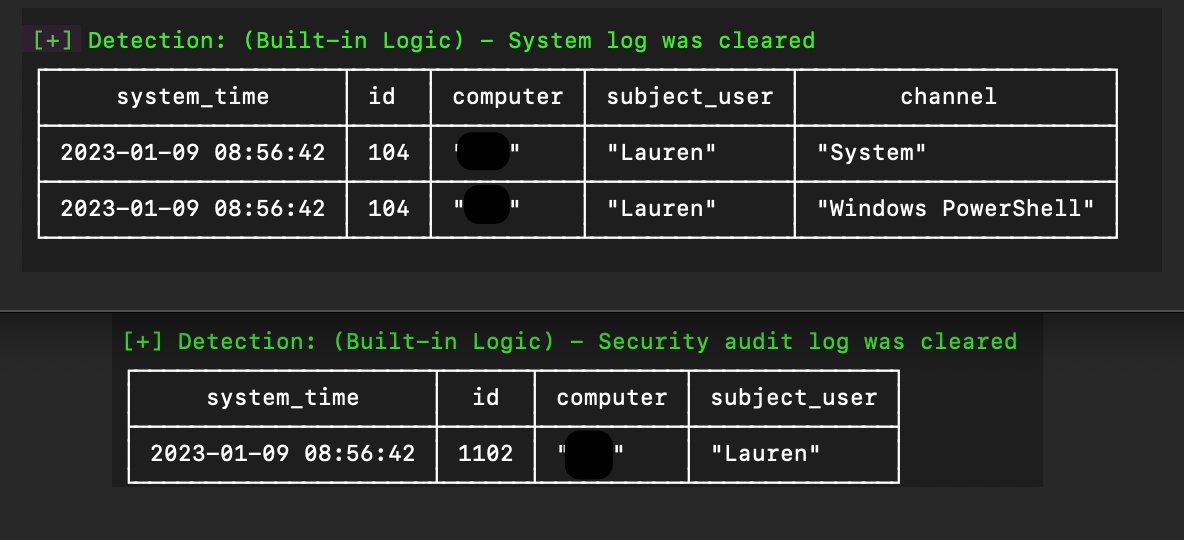
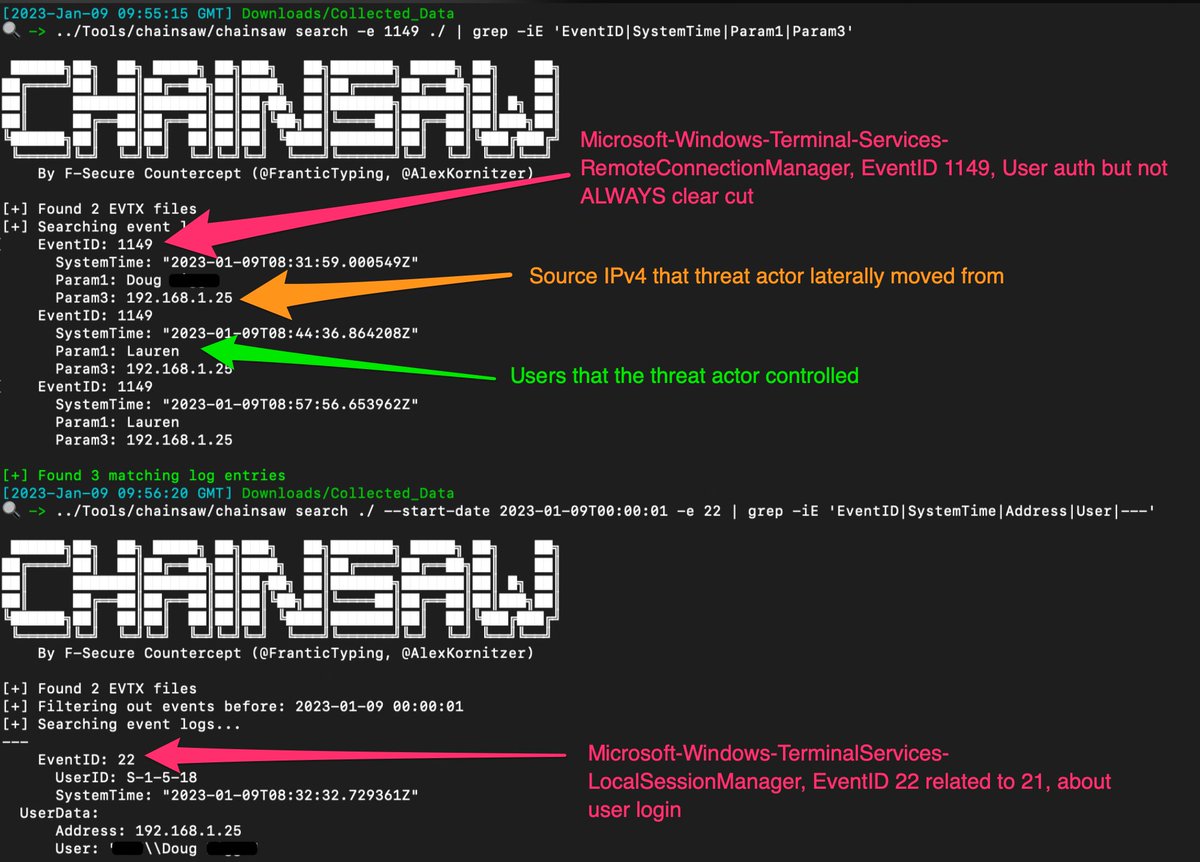
Our incident responders recently battled TheDukes/CozyBear/APT29 out of a customer environment. We also developed tooling to help investigate the timeline of the breach. We added 3 techniques for the analysis & timestamp enrichment of Shimcache entries withsecure.smh.re/19H


Elastic Security makes our ransomware protection artifact open! Learn more here about our commitment to openness and transparency and how detection capabilities need to evolve to keep pace with ransomware threats: go.es.io/3IiBFkd











Happy to drop this new open-source tool that connects the dots during a cyber attack to help blue teams cut down response times, avoid alert fatigue, and communicate during an incident. More info here >> labs.withsecure.com/tools/detectree #cybersecurity #incidents #infosec




